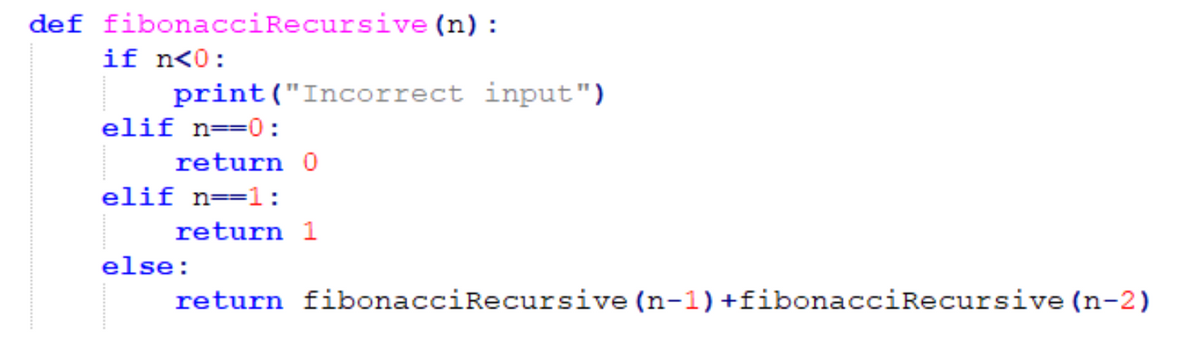
What is the big O notation for this function?
Q: Just what is the function of the StreamWriter object?
A: Stream Writer instance: The Append Text function produces a Stream Writer object.
Q: This question should be answered with OCaml. All functions must be implemented with the Continuation…
A: The answer for the above question is given in the following step for your reference
Q: Do operating systems serve just one purpose, or are there really three?
A: The operating system manages all the software and hardware in the computer. It performs basic tasks…
Q: Since computers are becoming so advanced, this is a plausible outcome. How did computers become so…
A: Introduction: Data can be defined as a set of raw facts, figures, or information that can be used to…
Q: Please explain the pros and cons of symmetric encryption. When deciding on an encryption method,…
A: Symmetric encryption is a method of encryption where a single key is used for both encryption and…
Q: How do I Evaluate and assist company decision makers in understanding the importance of database…
A: Database administration and data governance are important components of building scalable and robust…
Q: B1. Identify your favorite word processor. In what ways does it differ from Nano and Nano's output?…
A: Word Processor: A word processor is the type of software used for creating, editing, and formatting…
Q: Ethernet detects errors but does not correct them. Therefore, Ethernet is reliable. (T/F)
A: False. Ethernet detects errors but it does not correct them. Error detection is an important aspect…
Q: As an additional security measure, your company has mandated that all employees check in using a…
A: Reader for fingerprints Instead of typing a username and password, a fingerprint reader is a…
Q: Walk me over some of the risks I face if I decide to use my credit card to transfer money online.
A: The credit card number is encrypted and concealed behind a mathematical code when you add a credit…
Q: To what extent does it harm users if their email service provider reads their correspondence?
A: E-mail can spread computer viruses. Email delivery is not guaranteed.
Q: Do you know what top-down design is all about? Do I have it right? Give an example of top-down…
A: Please refer to the following step for the complete solution to the problem above.
Q: How does the linker determine which of these two duplicate routines to use?
A: Linkers are enable separate compilation. Instead of managing a massive application. Comparable to…
Q: in the followings find the "best" big-O notation to describe the complexity of the algorithm. Choose…
A: Big O notation:- Big O notation is a way of quantifying the amount of time and/or space necessary to…
Q: What are some applications of Embedded and Real-Time Systems?
A: Computer system:- A computer system is a combination of hardware and software components that…
Q: Recently, three improvements were made to the Linux core. It's possible that this might jeopardize…
A: Introduction: The Linux kernel is the operating system's central processing unit. It is a…
Q: Walk me over some of the risks I face if I decide to use my credit card to transfer money online.
A: To prevent theft, your mobile wallet encrypts credit card numbers using a mathematical method.…
Q: Recently, three improvements were made to the Linux core. How safe is the release then? Exactly what…
A: INTRODUCTION: The kernel of the Linux operating system is similar to Unix in that it is a…
Q: Describe the significance of database backup and recovery procedures and why they are so important.…
A: The process of making and keeping copies of data that can be used to safeguard organizations against…
Q: How may one go about making sure that their passwords are safe from prying eyes?
A: Introduction: A password that cannot be cracked cannot be created. Someone who is intelligent enough…
Q: Do you know what top-down design is all about? Do I have it right? Give an example of top-down…
A: Answer: We need to explain the top down design so we will see in the more details with the proper…
Q: How did the early PCs protect their users' private information? Explain
A: Early PCs did not have strong security measures to protect users' private information. There was…
Q: nux distribution is and name some of the
A: The solution is a given below:
Q: Give me a couple of real-world examples of menus in action in some popular software. How does…
A: Menu A menu is a graphic user interface component that offers the user a list of options to select…
Q: User interface and user experience are two distinct aspects that must be evaluated separately at all…
A: A user interface designer is in charge of a website's appearance. "User experience" refers to all…
Q: Should you choose the classic waterfall approach or the more flexible iterative waterfall approach…
A: The iterative waterfall approach for your Project is suitable.
Q: Jump to level 1 pq r_p→(qvr) TTT TT F TFT T FF FT T FTF FFT F F Check LL Fill in p→(qvr). 3
A: 1. Given Truth table contains three variables, that are p, q and r. The given proposition is:…
Q: It is not the same thing to model software or how it will be developed. Each person's contribution…
A: In software engineering, a software process is defined as the division of development operations…
Q: Financial institution debit cards are protected by personal identification numbers (PINS). Personal…
A: PIN plays as a security means in debit cards.
Q: To illustrate the potential for sharing between several nodes in a distributed system, a number of…
A: The shared software resources of a distributed system are briefly outlined here. centralised system:…
Q: It has been called into question whether or not users can effectively maintain their privacy while…
A: Since you inquired about the lack of privacy on social media platforms like Facebook, let's discuss…
Q: In order to hook and chain a FIQ interrupt method, one must begin at the specified offset in the…
A: Microprocessor:- A microprocessor is a small electronic device that is used to control and manage…
Q: Give me a couple of real-world examples of menus in action in some popular software. How does…
A: GUI DRIVEN BY MENU: This menu-driven design is highly straightforward and user-friendly. There are…
Q: Consider a function f : S→T defined by f(n) = n², where the domain is the set of consecutive…
A: One-to-one means that for every element in the range T there is exactly one element in the domain S…
Q: The question "Which is better?" is raised by the Iterative Waterfall Model in comparison to the…
A: A traditional Waterfall technique requires knowing project requirements before starting. Like the…
Q: What criteria may be used to determine whether a Linux distribution is a direct forebear of Ubuntu…
A: Ubuntu Linux is a popular open-source operating system based on the Debian codebase. It has gained…
Q: A grid must have a mechanism for numbering the tiles in order to support random-access search. A…
A: Introduction The "tile" which refers to an important enough object in the game of "Memory" that we…
Q: I am not really clear on how wildcards and serialization work. A concrete illustration should…
A: This question expresses my confusion regarding the existence of serialisation and wildcards. For…
Q: The exponential growth in computer processing power over the past few years is to blame for this.…
A: According to the facts given: We must determine how powerful computers have become recently.…
Q: Python code to simply calls this method to find the centrality values for the graph of Fig. 10.6 and…
A: Degree centrality is a measure of the importance of a vertex in a graph, defined as the number of…
Q: Kindly provide a list of at least three classes in C++ that may be used to generate input streams.
A: Answer: We need to explain the at least three classes in C++.so we will see in the more details with…
Q: Both the Linux and Windows netstat programs provide a list of currently active network connections.…
A: Given: Both the Linux and Windows netstat programs provide a list of currently active network…
Q: Give me a couple of real-world examples of menus in action in some popular software. How does…
A: GUI DRIVEN BY MENU: This menu-driven design is highly straightforward and user-friendly. There are…
Q: There are several steps involved in the process of developing a website. Each step's function has to…
A: 1) A website is a collection of web pages that are connected and accessible through the Internet. It…
Q: What kind of non-free Linux firewall was discussed in the presentation, and how would you classify…
A: It is recommended that you use a Linux firewall: Any answer or service that can control, safeguard,…
Q: User accounts on a computer network require passwords that contain 6 characters: The first character…
A: The above question is solved in step2 with all the necessary steps.
Q: Q Sum For parts (d) -(e), decide if it is true or false. If the statement is true, then prove it…
A: Introduction A mathematical language called asymptotic notation is used to represent how functions…
Q: Please explain the software development phases of the waterfall paradigm. It would be interesting to…
A: Waterfall and spiral model are the types of software development approaches.
Q: A parallel interface is an electrical connection that may move eight or more bits of data…
A: Due to this: Why is a parallel interface an electrical interconnection that allows 8 or more bits of…
Q: When creating software, think about the advantages of a step-by-step approach as compared to a…
A: A step-by-step approach and a waterfall technique are two popular software development…
What is the big O notation for this function?
Step by step
Solved in 2 steps

- def get_numbers(): user_input = input() values = [] for token in user_input.split(): values.append(int(token)) return values def print_selected_numbers(): numbers = get_numbers() for number in numbers: if (number % 2) != 0: print(number) print_selected_numbers() Input 1 7 4 19 2 10 what is the output please explainIn Java Write a Java Program to find the factorial of a number. The factorial of nonnegative integer n (denoted by n!) is the product of all positive integers less than orequal to n. Example: 4! = 4 × 3 × 2 × 1 = 24. The value of 1! Is 1 and the value of0! Is 1 too. Do not accept negative numbers.Sample Run:Enter a positive integer: -1Invalid entry.Enter a positive integer: -15Invalid entry.Enter a positive integer: 5Factorial of 5 = 120The Problem The Mastermind game board game is a code breaking game with two players. One player (your program) becomes the codemaker, the other the codebreaker. The codemaker (your program) creates a 4 digit secret code which is randomly generated by the supplied code below and the codebreaker tries to guess the 4 digit pattern. import randomsecretCode =[]for i in range (0,4): n = random.randint(1,9) secretCode.append(str(n)) print (secretCode) # take this out when you are playing the game for real because it is a secret The secret code pattern generated above will consist of any of the digits 1-9 and can contain multiples of the same digit. Your program should then tells the codebreaker which digits should be in their guess by displaying a sorted list of the digit characters contained in the secret code python list . Use the loopfor digit in sorted(secretCode): #display each digit on the same line for the player to see; there could be duplicate digits in the secret Prompt…
- Write an application that reads an integer value from the user and prints the sum ofall even integers between 2 and the input value, inclusive. Print an error message ifthe input value is less than 2. Use Java. Sample Run Examples: Example 1:the user enters 14Output: Sum: 56Example 2:the user enters 1Output: Error number must be greater than 11. Write an algorithm that asks the user to enter ten numbers and then prints the largest one.2. Write an algorithm that asks the user to enter a positive integer n and prints the sum of the divisors of n.01. Please _Given an integer num, repeatedly add all its digits until the result has only one digit, and return it. Example 1: Input: num = 38 Output: 2 Explanation: The process is 38 --> 3 + 8 --> 11 11 --> 1 + 1 --> 2 Since 2 has only one digit, return it. Example 2: Input: num = 0 Output: 0 Constraints: 0 <= num <= 231 - 1 Follow up: Could you do it without any loop/recursion in O(1) runtime? //code here class Solution {public: int addDigits(int num) { }}; //.
- ntegers outerRange and innerRange are read from input. Complete the outer while loop so the inner loop executes (outerRange + 1) * innerRange times. Ex: If the input is 6 5, then the output is: Inner loop ran 35 times import java.util.Scanner; public class LoopCounter { public static void main (String[] args) { Scanner scnr = new Scanner(System.in); int outerRange; int innerRange; int count; int i; int j; outerRange = scnr.nextInt(); innerRange = scnr.nextInt(); count = 0; i = 0; while (/* Your code goes here */) { j = 0; while (j < innerRange) { ++count; ++j; } ++i; } System.out.println("Inner loop ran " + count + " times"); } }(java programming language) Given f(x) = x+ x2/2+ x3/3+…… xn/n. Using do-while, write a program to compute f(x) for given x andn. The user should enter x and a positive integer n. Save your file as Q3.JavaZombie World ------------ input 10 2 4 9 output YES */ #include<iostream> using namespace std; int bubbleSort(int a[],int n) { int temp; for(int i=0;i<n-1;i++) { for(int j=0;j<n-i-1;j++) { if(a[j]<a[j+1]) { temp = a[j]; a[j]=a[j+1]; a[j+1]=temp; } } } } int main(int argc, char const *argv[]) { int b,n; cin>>b>>n; int z[n]; for(int i=0;i<n;i++) { cin>>z[i]; } bubbleSort(z,n); int flag = 1; for(int i=0;i<n;i++) { if(b<z[i]) { flag =0; break; } b = b - (z[i]%2 + z[i]/2); } if(flag==1) cout<<"YES"; else cout<<"NO"; return0;.
- Write a program that reads integers, finds the largest of them, and counts its occurrences. Assume the input ends with number 0. Suppose you entered 3 5 2 5 5 5 0; the program finds that the largest is 5 and the occurrence count for 5 is 4. (Hint: Maintain two variables, max and count. max stores the current max number and count stores its occurrences. Initially, assign the first number to max and 1 to count. Compare each subsequent number with max. If the number is greater than max, assign it to max and reset count to 1. If the number is equal to max, increment count by 1.)In Python, The function add_char_counts takes three parameters: a string s and two strings of length 1, char1 and char2, and returns the total number of times either char1 or char2 appears in s. For example, the word "scallions" has 2 s's and 1 n, so add_char_counts("scallions", "s", "n") returns 3. Hint: Use a string method to help solve this problem (count). You do not need an accumulator. For example: Test Result print(add_char_counts('Indiana', 'a', 'b')) 2 print(add_char_counts('BAHAMAS', 'A', 'B')) 4 print(add_char_counts('Mississippi', 'i', 'M')) 5 print(add_char_counts("spam spam spam spam", "s", "p")) 8public class Question1 {public static void main(String[] args) {double val;int counter = 0;int numIterations = 0;/*** Part a: Implement a branching condition that increases counter by 1 if val is larger than 0.5*/val = Math.random();/*** Part b: Add a loop around the code created in Part a that continues until counter equals 3.*//*** Part c: Use the variable numIterations to count how many times your loop in Part b iterates*/System.out.println("Number of Iterations until 3 random values greater than 0.5 were generated: "+ numIterations);}}











