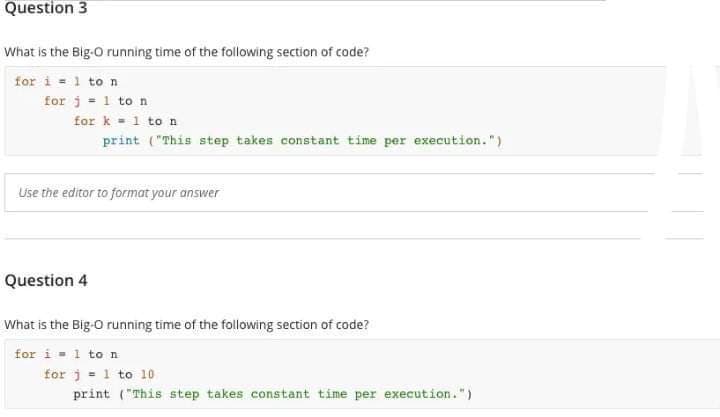
What is the Big-O running time of the following section of code? for i=1 to n for j = 1 to n for k=1 to n print ("This step takes constant time per execution.") Use the editor to format your answer Question 4 What is the Big-O running time of the following section of code? for i=1 to n for j = 1 to 10 print ("This step takes constant time per execution.")
Q: There are many distinct kinds of instructions included in the Instruction Set. Identify the…
A: Introduction: A Complicated Set of Instructions (CISC)A Complex Instruction Set Computer, often…
Q: Java // Complete the missing code in the main function in the Main class below import…
A: 1. Create an ArrayList of type Student2. Add 4 Student objects to the list3. Iterate through the…
Q: Cloud computers and mobile devices are connected, but how? By using cloud computing, mobile devices…
A: Answer: We need to explain the how Cloud computers and mobile devices are connected and its…
Q: Give an explanation of the inner workings of the arithmetic operators.
A: Arithmetic operators return a single numerical value after accepting a numerical value as their…
Q: Determine why wireless networks are so important in third world countries. In place of LANs and…
A: Our daily lives are permeated by radio technology, which is employed in short-range gadgets,…
Q: Is there a limit on the size of a user ID?
A: Introduction: Variable, function, structure, and other things have identifiers. Because it uniquely…
Q: Accounting Information System Prepare a collection flowchart (step-by-step) for a…
A: Introduction Analysis: Analysis is the process of breaking down information into smaller parts to…
Q: In certain cases, the cost of preventing a stalemate is cheaper than the cost of discovering one…
A: An operating system is a programme that runs application programmes and acts as a communication…
Q: Why is it that the bulk of multimedia content on the Internet today is sent via TCP rather than UDP?
A: Both UDP and TCP: The full name of "UDP" is "User Datagram Protocol." It allows the raising…
Q: Design a CFG which recognizes the language L={ w | all the letters on the first half of w are the…
A: - We need to create a Context Free Grammar for the language definition provided.
Q: Fix the following method printEvenIndex so that it will print out the Integers at even indices of…
A: Algorithm of the code: 1. Instantiate an empty ArrayList called values2. Create an array of integers…
Q: 5. Compute the double sum Σ=o Σ=o ij3.
A: In this question we have to compute the double sum of ∑2(i=0) ∑3(j=0) i2 j3 Let's solve, hope this…
Q: 2) complete the following chart: DECIMAL 77 OCTAL HEXADECIMAL BASE 4
A: Given: The decimal number 77 is given. Requirement: Convert the decimal number to OCTAL,…
Q: please code in JAVA Write two formulas. The formulas will be used to separate a series of items…
A: Given a list of items, write a Java program to separate the items into six categories. The program…
Q: Describe the various semantic categories, including their applications, advantages, and…
A: Introduction There are actually two different definitions of semantics that apply to different…
Q: Can you think of anything that distinguishes computer science distinct from other academic…
A: The differences between computer science and other subjects are described further below. Information…
Q: As a software developer, how would you describe your typical day? What are the three pillars upon…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: Even though sudo is the recommended method, root access is still possible on certain Linux systems.…
A: Introduction: Linux is a free and open-source operating system (OS). An operating system is…
Q: Assignment for Computer Architecture You are to write a program in MIPS that computes N! using a…
A: Introduction Computer Architecture:: computer Architecture refers to the fundamental design and…
Q: Explain some advantages of Linux in your own terms. Thank you in advance for any extra information…
A: An operating system is a programme that runs application programmes and acts as a communication…
Q: The Issue: You are aware that the software breaks during the 487th loop iteration. You'll have to…
A: Stopping the Program at the Right Place Create a debugging point.
Q: If you're going to explain how the internet works, why not go ahead and list all the components that…
A: HOW THE INTERNET WORKS: The computer network known as the internet is described as transmitting…
Q: Does anybody know the criteria for a legitimate numerical variable in programming?
A: In programming, a numerical variable is considered legitimate if it meets the following criteria:…
Q: Where does Linux stand when it comes to protecting its data? (Referring to the show itself)
A: File protection: how does Linux implement it? CS Linux was created on MINIX. Linux was based on…
Q: Detail the many kinds of semantics, when and how they should be used, and the pros and cons of each.
A: Introduction : Semantics is the study of meaning in language. It looks at how the meaning of words,…
Q: Content, accessibility, logical structure, and physical organization are all factors that should be…
A: In reality, information is stored in a database. EXPLANATION: Creating a database requires careful…
Q: Evaluate Ubuntu's speed in comparison to that of other Linux distros. My strong convictions have…
A: Users may modify Linux, a powerful and efficient operating system. You know that Linux apps are…
Q: When compared to on-premises solutions, how secure is business use of cloud services?
A: Simply put, cloud computing is the provision of computing services such as servers, storage,…
Q: Adjustments are evaluated, approved (or rejected), administered, and tracked. The Change Control…
A: Given:- In software configuration management, modifications are evaluated, accepted (or refused),…
Q: Does the workflow management system target a particular area of difficulty?
A: Introduction: To describe this issue using a planning language, we may define two types of actions:…
Q: Specifically, how does Oracle's database differ from relational databases?
A: Databases with relations: The mathematical set theory behind the relational model forms the basis of…
Q: When it comes to computer programs, what exactly is SCM and why is it so crucial?
A: Introduction: SCM stands for Software Configuration Management, and it is a set of practices and…
Q: Why is it crucial to have a systems analyst on board throughout the building of a system?
A: Introduction: A systems analyst plays a crucial role in the building of a system because they serve…
Q: When it comes to the loT, what kinds of attacks have we seen recently?
A: IoT- the Internet of Things, refers to the overall network of interconnected devices and the…
Q: Where exactly does PACS fit in when it comes to the Internet of Things?
A: Internet: The internet is a huge computer network that links various devices and transmits various…
Q: ● ● ● ● Create a new project called mySite. Start an application called personal. Our end-goal will…
A: Approach Start Create project of name mySite Create about you page In about you page mention the…
Q: Please code in JAVA In JAVA Declare an integer variable named result. Write the formula to have…
A: The JAVA code is given below with output screenshot
Q: Give a brief explanation of source data automation (SDA), highlighting its at least two (2)…
A: Introduction: SDA: Source Data Automation The process of acquiring digital values at the source and…
Q: How much storage and processing power does % say recursive functions need?
A: With an Explanation, This Is The Response: Utilizing the system stack, recursion calls itself…
Q: The chapter demonstrates how to decrypt TLS in the Chrome web browser. Try using an other browser,…
A: PC archives, messages, texts, trades, images, and Internet accounts may be used as evidence. For…
Q: If you were asked to define the term "network security," what would you say? You can explain the…
A: Network security involves a vast array of strategies, tools, and processes. Software- and…
Q: Give a rundown of the Assembly Registers and explain why it's important to utilize them.
A: Assembly record: The register in assembly is used to the processor which may act upon numeric…
Q: Mobile networks can't be built without using wireless technology in some capacity. For cell signal…
A: Given: It is challenging to construct a mobile network without utilising wireless technology in some…
Q: Just how unstable is UDP compared to IP? I'm interested in hearing your take on this. What is your…
A: Despite not being equally unstable, UDP and IP are both unreliable. Unlike UDP, which has four…
Q: Define how the Internet has changed the face of IT and communication.
A: Internet use has become an integral component of our everyday life. Internet use that is appropriate…
Q: Using the OSI paradigm would not work in this case. Why is it necessary for one layer's functioning…
A: In light of the fact that: Find the assertion that cannot be related with the functionality of the…
Q: illustrates the algorithm for search procedure on a skip list S for a key K. The algorithm employs…
A: Skip list is a type of data structure which consists of two types of layer which are lowest layer…
Q: Compress the following IPv6 addresses into their shortest expression…
A: Compress the following IPv6 addresses into their shortest expression…
Q: The ability to recover from deadlocks depends on the strategies you identify.
A: INTRODUCTION: The term "deadlock" refers to a scenario in which two computer programs that share the…
Q: List some possible approaches that may be used to ensure that deadlocks are recoverable.
A: Definition: A structure chart (SC) in software engineering and organisational theory shows how a…
Step by step
Solved in 2 steps

- Write programs that will accomplish the desired tasks listed below, using as few lines of code as possible.Use only opcodes that have been covered in class. Comment on each line of code. m) Copy the external code byte at address 007Dh to the SP n) Copy the data in register R5 to external RAM address 032Fh o) Copy the internal code byte at address 0300h to external RAM address 0300h p) Swap the bytes in TIMER 0 ; put TL0 in TH0 and TH0 in TL0 q) Store DPTR in external RAM locations 0123h (DPL) and 02BCh (DPH) r) Exchange both low nibbles of registers R0 and R1 ; put the low nibble of R0 in R1, and the low nibble of R1 in R0Consider the following procedure:procedure mystery (x, y, z); integer x, y, z;beginz = x - 1;y = 1;endand consider the following code fragment:A[1] := 3;A[2] := 3;n := 1;mystery (A[2], A[n], n); A) What will be the final values of n, A[1] and A[2] if the parameters are passed by reference? B) What will be the final values of n, A[1] and A[2] if the parameters are passed by value? C) What will be the final values of n, A[1] and A[2] if the parameters are passed by name?4) Which of the following is/are valid ways to allocate memory for an integer by dynamic memory allocation in CPP? a. int *p = new int(100);b. int *p; p = new int; *p = 100;c. int *p = NULL; p = new int; *p=100;d. Only 1,2e. All of these 5) Choose the correct option?#include<iostream>using namespace std; class Base {}; class Derived: public Base {}; int main(){Base *bp = new Derived;Derived *dp = new Base;} a. No Compiler Errorb.Compiler Error in line “Base *bp = new Derived;”c. Compiler Error in line ” Derived *dp = new Base;”d. Runtime Error
- What will be the value of AL after running code? MOV AL, 10 MOV AH, 10 MOV BL, 5 MOV BH, 5 MUL BLFor this assignment you are tasked with writing a command-line Java program that evaluates Reverse Polish notation (RPN) formulas. Here are the details:• This must be a Java program that:• Correctly compiles under the UNIX command line (for optimal results, test your program on Raptor). • When run from the command line your program must read from standard input an RPN formula.• You can assume there is a space between every operator and number. Every number will be a 32 bit integer.• Your program should be able to correctly handle the operations: +, -, x. • IMPORTANT: be careful that your program recognises precisely the three characters above (plus sign, minus sign, and the lowercase letter “x”, respectively).• Your program then should write to standard out a single line with the correct output in standard integer format. The following example shows correct behaviour for your program cd472$ javac Submission.javacd472$ echo 75 125 + | java Submission200Which of the following statements is correct? 1.Average execution rate and Harmonic mean rate always give the same results 2.Harmonic mean rate is very related to Execution Time 3.Average execution rate explains the execution time more clearly 4.None of these
- Write programs that will accomplish the desired tasks listed below, using as few lines of code as possible.Use only opcodes that have been covered in class. Comment on each line of code. m) Copy the external code byte at address 007Dh to the SPn) Copy the data in register R5 to external RAM address 032Fho) Copy the internal code byte at address 0300h to external RAM address 0300hp) Swap the bytes in TIMER 0 ; put TL0 in TH0 and TH0 in TL0q) Store DPTR in external RAM locations 0123h (DPL) and 02BCh (DPH)r) Exchange both low nibbles of registers R0 and R1 ; put the low nibble of R0 in R1, and the lownibble of R1 in R0s) Store the content of register R3 at the internal RAM address contained in R2. (Be sure the addressin R2 is legal)t) Store the content of RAM location 20h at the address contained in RAM location 08hu) Store register A at the internal RAM location address in register AYour task is to complete the code below in order to evaluate the results of four basic arithmetic operations. # input a float value for variable a here# input a float value for variable b here # output the result of addition here# output the result of subtraction here# output the result of multiplication here# output the result of division here print("\nThat's all, folks!") The results have to be printed to the console. You may not be able to protect the code from a user who wants to divide by zero. That's okay, don't worry about it for now. Test your code - does it produce the results you expect? We won't show you any test data - that would be too simple.THIS IS IN JAVA A programmer intended to compute (a AND b) OR c, and wrote the following code, which sometimes yields incorrect output. Why? <pre><code>c | (a & b)</code></pre> A. The parentheses are interfering, and should not be present B. The ORing with c should appear after the parentheses, not before C. The bitwise operators should be replaced by logical operators D. If code only sometimes yields incorrect output, the compiler is likely broken
- Hello I need help with the following question, I have provided my work that I have done and an example of completed work from the class. This is the question I need help with. A system currently accessing 3.8 G bytes of RAM and 10 M bytes of ROM. Compute the number of address lines required to access the designated storage. For a given # of lines how many more storage space is accessible? Currently out of 3.8 G, 3 G is used by the system programs, .4 G by an application. Can we expand the memory by another 890 M to support a new application? show total storage use and available. Show all your work.use ibm is400 series to answer the following question (the output should shown in screenshot) 1 - develop a new Library called MnnLIB1 (NN is your student login id number) using the command CRTLIB 2 - develop a new Jobq MnnJOBQ1 and Outq MnnOUTQ1 in the Library MnnLIB1 using the command crtjobq and crtoutq 3 - Grant *PUBLIC *USE Authority to your MnnLIB1 library using the command wrkobj MnnLIB1 and then option 2 4 - Submit 3 jobs using sbmjob in your MnnJOBQ1, these jobs will not run, since they are not attached to any sub-system. Check it out by using wrkjobq command 5 - Change the 3 jobs submitted in step #4 to run in sub-system QINTER and change the out to MnnOUTQ1. These jobs will run, and the results will be in MnnOUTQ1. Check it out by using wrkoutq command 6 - develop a new Source File called MnnSRC in your library MnnLIB1 using command crtsrcpf 7 - develop a new Save File called MnnSAVF in your library MnnLIB1 using command crtsavf 8 - Run DSPJOBLOG command and save the…Which of the following is/are valid ways to allocate memory for an integer by dynamic memory allocation in CPP? a. int *p = new int(100); b. int *p; p = new int; *p = 100; c. int *p = NULL; p = new int; *p=100; d. Only 1,2 e. All of these

