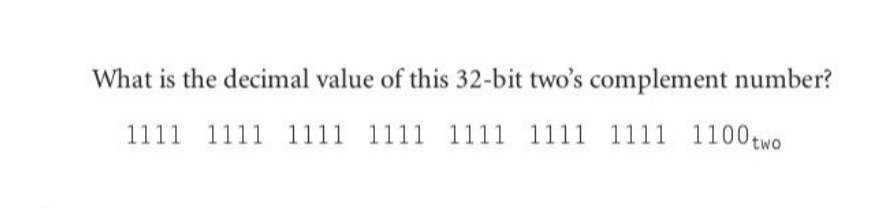
What is the decimal value of this 32-bit two's complement number? 1111 1111 1111 1111 1111 1111 1111 1100 two
Q: The database needs to be managed by an administrator to ensure its smooth operation. Just what does…
A: Explanation: The creation, maintenance, backups, querying, tuning, user rights assignment, and…
Q: Question 13 sum Which of the following supervised learning data mining techniques are considered as…
A: Answer: A computer is taught using "labelled" data in supervised learning. When input and output…
Q: Name Name Birthdays Add a Birthday All Birthdays Birdy 7/31 9/19 Add birthday Please do provide the…
A: HTML(Hyper Text markup language): HTML is a markup language that is used to structure content on a…
Q: To what extent does SAS excel over SCSI, and what are those benefits?
A: The answer is given below step.
Q: Write a function named encode_string[sentence) that takes a string value as its input and returns an…
A: Below I have provided a program for the given question. Also, I have attached a screenshot of the…
Q: Write a function named encode_string(sentence) that takes a string value as its input and returns an…
A: In this question we need to implement a function which takes a string as parameter and returns…
Q: How is the S-box constructed?
A: Introduction: Block ciphers rely heavily on substitution boxes, often known as S-boxes, which have…
Q: Given numbers = (54, 22, 48, 53, 13), pivot = 53 What is the low partition after the partitioning…
A: In this question we have given an unsorted array and a pivot element and we need to determine the…
Q: What type of information might be derived from a traffic analysis attack?
A:
Q: Define What is Kerberos.
A: Please check the step 2 for solution.
Q: Differentiate internal and external error control.
A: An error detecting code, also known as a frame check sequence or checksum, is utilised in the…
Q: So, what makes emerging technologies so different from their ancestors?
A: The following are some characteristics of emerging technologies: Radical innovation, rapid growth,…
Q: Which accessibility characteristic is a solution for users with hearing impairment? Transcript of…
A: Computer systems provide various featured programs and tools that help hearing impaired persons to…
Q: What is the role of session key in public key schemes?
A: Answer: In order to guarantee the security of a communications session between a user and another…
Q: Define What is Kerberos.
A: Kerberos Kerberos is a network protocol that uses the secret key cryptography to authenticate the…
Q: Explain scope in JavaScript.
A: Definition: JavaScript uses the term "scope" to refer to the current context of the code. This…
Q: What are your thoughts about why MIDI, a protocol created in the 1980s, is still prevalent today?
A: Thought many of us use USB now-a-days, still some people's use MIDI.
Q: Create a high gui banking application in java that includes balance, withdraw, deposit, account…
A: As per your requirement the below one is solution please follow it step by step
Q: extract [y(1:12000, :)]; for counterme = 2:10 extract= [extract y(((counterme-1)*12000) +1:…
A: Lets understand how for loop works in the given code: extract = [y(1:12000,:)];for counterme = 2:10…
Q: List the Limitation of SMTP.
A: These question answer is as follows,
Q: Explain DOM in JavaScript.
A: Web documents have a programming interface known as the Document Object Model (DOM). So that…
Q: Music Are you okay with others listening to your music on the small speaker in their cellphone…
A: Music can be streamed at multiple settings i.e. when the bit rate is high which corresponds to high…
Q: Explain scope in JavaScript.
A: The answer to the question is given below:
Q: Briefly describe Sub Bytes.
A: The study of secure communication techniques that allow only the sender and intended recipient of a…
Q: Question 9 na When Agglomerative Hierarchical Clustering (AHC) is used with single linkage, the…
A: The process of grouping the data in a dataset is called clustering. Data points and sets belonging…
Q: make Algorithm for Alpha-beta pruning using minimax. Minimax-Alpha-Beta(v, α, β) in: node v; alpha…
A: Algorithm for Alpha-beta pruning using minimax given next step:
Q: Complete the following class in java all the methods according to the requirements shown in the…
A: Solution: java Code: HeapDriver.java package org.learning.opps.heappack;import…
Q: After executing the floating-point instruction: FINIT(); how many of the eight FPU registers will be…
A: Int and float usually occupy "one word" in memory. Today, with the move to 64-bit systems, this can…
Q: Explain what is key distribution.
A: Definition: A key distribution centre is a type of symmetric encryption that enables access to two…
Q: Why is recording with sampling rates above 44,100 is advantageous?
A: Introduction: When we record sound, we start with an analog signal. This is true whether the signal…
Q: What is the purpose of the State array?
A: The answer to the question is given below:
Q: Explain scope in JavaScript.
A: Introduction: The "scope" of the code in JavaScript is the current environment. The variables that…
Q: Define a Bastion Host?
A: A computer network refers to interconnected computing devices that can exchange data and share…
Q: CH 6: Debug Files A high school is holding a recycling competition, and this program allows a user…
A: I have fixed the code according to the bugs in the question. I have commented the fixed lines for…
Q: 3. Write 3 main objectives of cell planning problems? a. b. C. [3]
A: Let us see the answer:- Introduction:- Before installing a GSM mobile system, cell planning is one…
Q: Match the proper answers to each question: The smallest 8-bit signed number in Hex is: The smallest…
A: Below I have provided a solution for the given question.
Q: 3. Write a Java program that uses a for iteration statement in order to generate and print the sum…
A: The java program is given below:
Q: What are the current applications of data mining methods, benefits, implications, and/or possible…
A: This topic examines the methodology, advantages, ramifications, and/or potential future advances of…
Q: Write a script that creates a user-defined database role named OrderEntry in the MyGuitarShop…
A: Please find the attached solution of the given problem:
Q: Please answer in python Write a method called add_racer which takes in a Boat object and adds it to…
A: Add a new file called very_short.cvs in the current working directory and add the content.…
Q: Please comment the two codes below. (//1)The first is writing numbers vertically and second is on…
A: I commented on the portion and also highlighted it and provide the output after commenting it and…
Q: Write a program that implements the methods of a list using LINKED LISTS
A: Algorithm to implement Linked List Linked List contains the nodes that store the data and address…
Q: How can decide a unique Binary tree according to the following descriptions ? multiple choice a.…
A: SEE THE ANSWER SECOND STEP
Q: Step 7 - Descriptive Statistics - Points Scored By Your Time in Away Games The management also wants…
A: Solution: Given, MEAN FUNCTION : .mean(your_team_home_df) MEDIAN FUNCTION:…
Q: What is power analysis?
A: A power analysis is a calculation that is used to determine the smallest sample size required for an…
Q: 2. What are the 4 multiplexing schemes normally used? [3]
A: Your answer is given below.
Q: Write two programs in Python. The Client program to contact the Server program and send any string…
A: A simple server-client program : Server : A server's bind() method ties it to a particular IP…
Q: mum length of the g data at a rate of et LAN with frames
A:
Q: using System; using System.Text.RegularExpressions; class chapter8 { static void Main() { string…
A: tprogram to search for dates instead of ages, and use a grouping construct to organize the dates.…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- What decimal number does this two’s complement binary number represents (1111 1111 1111 1111 1111 1111 1111 1111)2What decimal number does the bit pattern 1011 1111 1100 0000 0000 0000 0000 0000 represent if it is a floating point number in IEEE 754 standard (single precision)?What is the range of this signed binary number? 19 bits and 26 bits
- What decimal number does the bit pattern 0×0C000000 represent if it is a fl oating point number? Use the IEEE 754 standard.Convert the following decimal numbers to 8-bit two’s complement numbers1. 42 10 (Subscript is 10)What decimal number does the bit pattern 0×0C000000 represent if it is a floating point number? Use the IEEE 754 standard.

