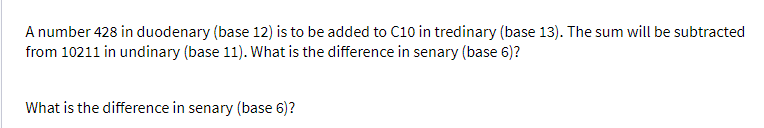
What is the difference in senary (base 6)?
Q: Define HTTP and explain how it differs between non-persistent and persistent HTTP.
A: HTTP stand for Hypertext Transfer Protocol.
Q: Define and explain the concept of application virtualization.
A: Introduction: The act of generating a virtual (rather than actual) version of something, such as…
Q: What does the word "System Mission" mean to you, and how would you describe it? What is the…
A: answer is
Q: My Solutions > MATLAB Documentation Reset FA1.5-3_Function Triangle_Area Create a function…
A:
Q: Query Processing and Query Optimization Multiple costs exist when deciding how to optimize a…
A: Multiple costs exist when deciding how to optimize a process on a database. One cost is several…
Q: The ways to communicate with the LMC are ?
A: LMC: The full form of the LMC is little man computer. LMC computers are purely depend on the…
Q: Write the C statements necessary to do each of the following. Do not write complete programs. Unless…
A:
Q: e input of age of 3 people by user and determine oldest and youngest among th
A: Lets see the solution.
Q: A multiprogramming and time-sharing environment is one in which several people share the same…
A: Stealing or copying files from other users: Multiple processes are enabled to run in a…
Q: 19 A 27 25 15 18 B -11- -10- 31 10 15- G E 20 8 F
A: We are given a graph and we are going to find out if we use Primm-Jernik’s algorithm, then which…
Q: 11. Given the following sample of the Web graph: a) Compute the transition matrix M.…
A: According to our guidelines we solve first three:…
Q: What is an application life cycle management environment? What are two examples of ALM?
A: "Environment for Managing Application Life Cycles":
Q: 8The Control Unit determines the _. a. particular instruction to be executed by interpreting the…
A: The CPU is the central processing unit of the computer. It handles all instructions it receives…
Q: What is the importance of drafting the following protocols in research
A: A. Data gathering protocol
Q: at are two reasons why layered protocols are used? Give
A: Justification for the Use of Layered Protocols Layered protocols are primarily utilised in…
Q: how to covert image to graph in a python (spyder) i need a source code a bout this technique .
A: In the below step we are converting image into particular graph.
Q: What precisely is a system model? When developing the foundational models, what should be taken into…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. System…
Q: 4. To burn a CD-R, the laser must pulse on and off at a high speed. When running at 10x speed in…
A: Answer
Q: Use an example from your personal experience to fully explain the wait() process's role in…
A: Introduction: A process is essentially a running software. basically, the execution of a process…
Q: What type of protection is provided by IPsec for VPN traffic? 4 O Hashing O User authentication O…
A: We are going to understand what are the services provided by the IPsec for VPN traffic.
Q: Define the basic roles and duties of the Chief Information Officer (CIO) and Chief Technology…
A: A Chief Information Officer's responsibilities: Include overseeing the development and progress of…
Q: Learn about private and public-key cryptography, and how they are different. Is it possible to…
A: answer is
Q: Examine how information and communication technology (ICT) may be utilized to enhance organizational…
A: ICT: Technology for Information and Communication (ICT) is an abbreviation for the terms information…
Q: Give a brief explanation of what the Solution Explorer window does.
A: Windows Explorer is the file manager used by Windows 95 and later versions. It allows users to…
Q: What does it signify when software configuration management policies are changed?
A: The following is information about software configuration management policies, as well as links to…
Q: What is meant by online analytical processing is the processing of data in real time?
A: INTRODUCTION: Here we need to define online analytical processing is the processing of data in…
Q: esign the restaurant’s menu as an XML file. It should store the different dishes available, along…
A: The XML code has been written in step 2 and the hierarchy tree has been attached in step 3. You can…
Q: Examine how technology affects health-care data systems.
A: Technology affects health care data systems: Medical technology improvements are expensive. Thus,…
Q: 5)Which of these sets of logic gates are known as universal gates? a. NOR, NAND b. OR, NOT, XOR c.…
A: A universal gate is a logic gate which can execute any Boolean function without need to utilize…
Q: Determine if the following relationship is reflexive, symmetric, antisymmetric, or transitive (or…
A: Reflexive relation: Every element maps to itself then it is reflexive. Symmetric relation: If a…
Q: Asymmetric encryption systems, such as those used in public key cryptography, offer numerous…
A: Foundation: Public-key cryptography is another name for it.It encrypts and decodes a message using…
Q: [Part 2] Tree. Decode each bit string using the given Huffman codes. 1. 1110011101001111 Answer: 2.…
A: In order to decode a encoded data , we need Huffman tree. Here we are given Huffman tree. We iterate…
Q: You provide a significant explanation to support your solution to the question, "What is the…
A: Databases are used to store data. A transaction is a logical unit of work composed of one or more…
Q: Explain the operation of a challenge–response authentication system. What makes it more secure than…
A: Definition: Password-based authentication is often used in client-server databases. The password…
Q: What is a cryptographic hash function (CFH), and how does it work??
A: Cryptographic hash function: It's a mathematical function that turns a message's arbitrary length…
Q: When selecting a system model, what steps are taken to ensure that it is appropriate?
A: System Model: A System Model is a representation of the many components of a system and its…
Q: Deadlocks can be broken using one of two methods?
A: A deadlock occurs when the two computer programmes that share the same resource effectively block…
Q: 2. Conversions: This set of problems involves conversions of a value in one unit to another unit.…
A: Step 1 : Start Step 2 : In the main function , print the user interface. Take user input for the…
Q: Define the basic roles and duties of the Chief Information Officer (CIO) and Chief Technology…
A: A Chief Information Officer's responsibilities include overseeing the development and progress of…
Q: . Assume we want to use bloom filtering to filter product numbers. Assume we are only interested in…
A: Answer is given below-
Q: Convert the following English sentences to first-order logic. • There is a healthy food that is…
A: Answer
Q: When you say "IOP," what exactly do you mean? Make use of a flow graphic to explain the idea of…
A: An input-output processor (IOP) is a processor with direct memory access capability. In this, the…
Q: onsider money is transferred from (1)account-A to account-B and (2) account-B to account-A. Which…
A: Lets see the solution.
Q: 6)The COFFEE BREAK instruction is defined as op-code __ a. 2 b. 3 c. 1 d. 0
A: The COFFEE BREAK instruction is also known as HALT instruction. The COFFEE BREAK instruction pauses…
Q: Three processes share five resources of the same kind to form a system. Two resources are required…
A: Total number of resource=5 Total number of process =3 # of instance required by each process=2
Q: Description 1. (Geometry.c) Write the following functions that compute the volume and surface of a…
A: I give the code in C along with output and code screenshot
Q: Show that p Aq=q^p.
A: Propositional Logic: It is a collection of declarative statements which has either a truth value…
Q: Describe the steps involved in doing a thorough walkthrough. During a walkthrough, who is…
A: Introduction: In a walk-through test, an auditor will examine how a transaction is begun and…
Q: There are distinctions between hard and symbolic linkages.
A: The linkages are of two types:- 1. Hard 2. Symbolic
Q: Public key cryptography is an example of an asymmetric encryption method with numerous benefits over…
A: Asymmetric cryptography, often known as public key cryptography, is a method of encrypting and…
dont dont answer without knowledge sure report skip if dont know
Step by step
Solved in 2 steps

- A number 428 in duodenary (base 12) is to be added to C10 in tredinary (base 13). The sum will be subtracted from 10211 in undinary (base 11). What is the difference in senary (base 6)? What is the difference when the sum of 428 in duodenary (base 12) is to be added to C10 in tredinary (base 13) will be subtracted from 10211 in undinary (base 11)?A number 428 in duodenary (base 12) is to be added to C10 in tredenary (base 13), what is their difference in decimal (do NOT include the base in your answer)?Find the value of S, where A = 348 ; B = 8FB16 ; C = B316 and D = 11012, given that S = ( C * D - B + A ). What is S in decimal?
- A number is divisible by 11 if the difference of the sum of its digits at odd places and the sum ofits digits at even places is either 0 or divisible by 11.For example, for 2547039:(Sum of digits at odd places) - (Sum of digits at even places) = (9 + 0 + 4 + 2) - (3 + 7 + 5) = 0So 2547039 is divisible by 11.But for 13165648:(Sum of digits at odd places) - (Sum of digits at even places) = (8 + 6 + 6 + 3) - (4 + 5 + 1 + 1) = 1212 is not divisible by 11 so 13165648 is also not divisible by 11.2. If a number A is arithmetical right shifted by K times to get a number B, then prove that B = A/(2*K).In a given 32-bit floating-point representation of numbers, if the number of bits of the mantissa is reduced to accommodate an increase in the number of bits of the exponent, this will result in the following: (select the best answer) Increased range of the numbers at the expense of the precision Increased precision of the numbers at the expense of the range Both range and precision increase Both range and precision decrease
- 3. In base 26, multiplication of YES by NO gives – i) THWOE ii) MPAHT iii) MPJNS iv) THWAEThere are, by hypothesis, infinite number bases, but in computing we use hexadecimal, octal and binary bases. So that we can correctly perceive the quantities involved in these bases, it is necessary that we transform them to the decimal base, with which we are used to. Check the alternative that shows the correct value of converting the following number in hexadecimal C02A,51(16) to decimal. A) 491910(10) B) 49194,316(10) C) 49194,375(10) D) 12593745(10) E) 12593745,365(10)How many integers between 1000 and 9999, inclusive, have an odd number of positive integer divisors?
- Determine the place value of each digit in a four-digit number in base 16 (hexadec-imal). Which places or digits in an arbitrarily long base-2 number have the same place valuesrespectively?How many binary numbers of xed length 8 have weight 3?6358×47328= show working out, leaving the answer in the octal form.

