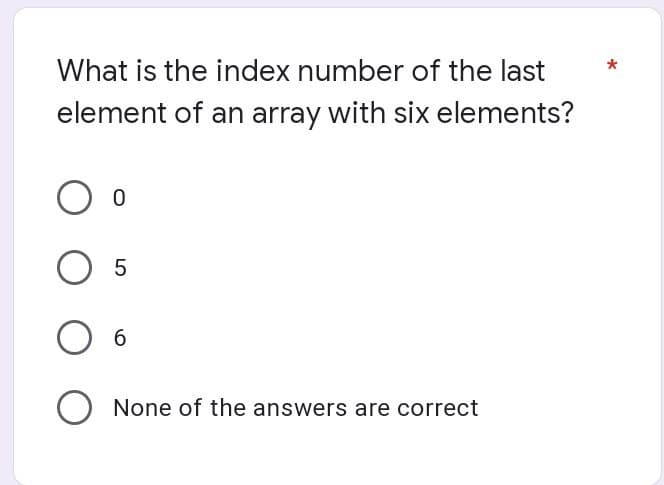
What is the index number of the last element of an array with six elements? 5 O None of the answers are correct
Q: The Mac OS, unlike most other PC operating systems, saves a major chunk of the operating system in…
A: Intro ROM: • ROM is "inherent" PC memory having data that regularly must be perused, not written…
Q: Explain why we study graphics in C and what uses C graphics have.
A: Intro The use of graphics makes computer applications quite effective and beautiful. The c graphics…
Q: please no copy from internet Write a python program to solve N Queen problem using backtracking.
A: I give the code in Python along with output and code screenshot
Q: What are the fundamental prerequisites for new hardware and software in a computer system?
A: System requirements are specific requirements that a device must have in order to operate particular…
Q: Which form of software application is most suited to the layered architectural style?
A: Layered architecture Layered architecture is the most common architecture, it is also called as…
Q: Computer science What is the procedure for assessing an RFP?
A: Intro RFP: The most common goal of supply Associate in Nursing RFP is to seek out the “best” vendor…
Q: What role does ethics play in information technology?
A: Introduction: What role does ethics play in information technology?
Q: 10.4 (THE MYPOINT CLASS) Design a class named My Point to represent a point with x- and…
A: The question is to write the JAVA code for the given problem.
Q: What are some of the governance concerns to consider when transitioning from on-premise servers to…
A: Introduction: The charity management use the infrastructure as a service (IaaS) deployment strategy…
Q: Is the HFC transmission rate allocated to a single user or shared? Is it conceivable for collisions…
A: HFC: It stands for Hybrid Fiber Coax. it uses both coaxial cables and fibers. In the downstream…
Q: Can someone explain how this recursive function output is 12? Recursion is hard for me
A: Thank you __________ print(R(0)) So here it will go to def R(n): So if 0>=5 false so it…
Q: What are the different parts of a typical V
A: A web application (or web application) will be application software that sudden spikes in demand for…
Q: What would the class names, class characteristics, and class methods be if you were developing…
A: A class is like a blueprint of a specific object. In the real world, every object has some color,…
Q: Can you provide a full examination of the network adapter's functioning and performance?
A: The network adapter allows the device to communicate over the local area network or LAN, connecting…
Q: working blo
A: Social media are intuitive digital channels that facilitate the creation and sharing of data,…
Q: What methods of usability testing, such as cognitive walkthrough, may be used to assess the online…
A: Introduction: Candidate Usability Analysis Methods, Candidate Usability Analysis Methods will…
Q: Please mention Three internal gateway protocols (IGPs)
A: Answer: Internal gateway protocols are routing protocols used to exchange routing information…
Q: For systems where one component creates data and another consumes it, which architectural pattern is…
A: Let's have a look at the answer: A classic data vaulting college's architectural architecture is…
Q: What is the significance of the difference between changeable and immutable values in the…
A: Intro The creation of a mutable object differs from that of an immutable object in that it can be…
Q: What are the core concepts of software engineering that are missing? explain?
A: Failure to Recognize the Requirements of the Organization: One of the primary reasons software…
Q: Problem 5: Using KMaps, find the simplest POS expression of F Ilw.x.y(1, 4, 5, 6, 7).
A: Answer:
Q: As a result of these project failures, what is the most essential lesson that new systems analysts…
A: Intro What is the most important lesson that new systems analysts can learn from these project…
Q: What are the advantages of a compiled language over an interpreted language? In what circumstances…
A: The term "interpreted language" refers to a programming language that does not need a program to be…
Q: So, what exactly are the parts of a computer?
A:
Q: What does the LIKE operator in SQL do? Give an example to back up your claim.
A: The LIKE operator is used in a WHERE clause for search for a specified pattern in a column.…
Q: In Computer Science class, how do we take notes on our work? Discuss.
A: Given: How should we take notes in Computer Science? Discuss. Sometimes, taking notes in notepad or…
Q: What are the top five uses of sentiment analysis?
A: Introduction: In real time, sentiment analysis of social media data will maintain a close eye on…
Q: d by w
A: Cloud computing is an assortment of virtual servers (in the cloud) that give different types of…
Q: Explain how interruptions are crucial to the machine using one practical example.
A:
Q: Compare and contrast any two validation methods. - Software Testing
A: Compare and contrast any two validation methods
Q: Explain why professional software designed for a client isn't just a collection of programmes that…
A: Introduction: Because professional software is nearly typically packed with supporting documentation…
Q: Explain how interruptions are crucial to the machine using one practical example.
A: Interruptions are essential to the machine because they allow the system to interact with its…
Q: Computer science What exactly are phishing attacks? Briefly discuss.
A: Intro Phishing is the fraudulent theft of sensitive information using electronic media fraud to…
Q: Computer science Distinguish between internet, intranet, and extranet.
A: Introduction: Internet This is the global network of computers that anybody with an Internet…
Q: What are the drawbacks of employing the shadow-paging technique?
A: Intro Shadow paging is a method for giving atomicity and toughness in data set frameworks.…
Q: What justifies the use of such a diverse set of partitioning methods by operating systems?
A: Introduction: For example, the first method of establishing partitions is to divide the space into…
Q: Component-based programming and the impact it has had on the market for software components are the…
A: Before understanding component-based programming, it is vital to grasp the definition of a…
Q: Traditional Turing architecture is inefficient in terms of energy consumption. Explain why the…
A: Introduction: Future computing advancements will be built on computer models that do away with…
Q: Computer science What methods may be utilised to secure IIS? What are some examples of automated…
A: Introduction: Internet Information Services (IIS) is an abbreviation for Internet Information…
Q: What is the significance of cypher in the context of communication security protocols?
A: Given: Cipher is a cryptographic algorithm that is often used in cryptology (the study of…
Q: What does it imply for a collection of language characteristics to be orthogonal (for example, a…
A: Introduction: Orthogonality in a programming language refers to the fact that a relatively limited…
Q: Page size is 4 bytes, page number is 3, frame number is 2, and offset is 8. What is the frame…
A:
Q: Because the capacity of the internal hard drive is insufficient, we must rely on external hard…
A: Introduction: In the field of computer science, there are many different types of storage methods…
Q: What exactly is the distinction between syntax and semantics.
A: Syntax Syntax: It refers to the guidelines for creating statements in programming languages such as…
Q: Can you define and illustrate the concept of a Matlab "local variable" with an example?
A: Variables that are specific to a location Each MATLAB function contains a set of local variables…
Q: A certain architecture is used to create all software applications. Explain the various…
A: Introduction: A certain architecture is used to build all software applications. Discuss the various…
Q: Which “Cryptographic Technique” can we use to safeguard our data?
A: "The Principle of Security" is a cryptographic technique by which we can implement the "Principle of…
Q: What is the byte data type range in Java?
A: Introduction Byte by name can store a byte of data
Q: What are some of the advantages of the Database language? Is there a specific example you'd want to…
A: Database language: SQL is a kind of computer language used to create and manage databases. There…
Q: Distinguish between C++ and Java
A: Intro C++ It is a programming language that includes the function of C programming language in…
Step by step
Solved in 2 steps

- There is an array with the original content as follows12,6,32,45,98,56,85,21,58,69,79,84,86,91Now execute Sequential search, how many comparisons are required for the following numbers?20 : ___45 : ___Write a program that deletes the first element in an array which matches a search key. Advance thanks <3Is it true or false? The final element's subscript is always one less than the array's Length attribute.
- Given the following array, what is the content of the array after Three passes of Insertion Sort? array: 44 12 50 3 40 23 Question 5 options: 3 12 44 50 40 23 12 44 50 3 40 23 12 3 23 40 44 50 12 3 44 50 40 23In an unsorted array with N items, how many items must be examined to find a particular item on average case?Required to answer. Single line text.Please code give_ Q. How to find the smallest positive integer value that cannot be represented as sum of any subset of a given array?. Thanks.
- What is the subscript of the last cell of an Array of size n4 ? (in terms of n)In the "Common Array Algorithms" section, you learned how to find the position of an element in an array. Suppose you want to find the position of the second match. You could remove the first match and start over, but that would be wasteful. Instead, adapt the algorithm from that section so that it starts the search at a given position, not zero. Complete the following code.There is an array with the original content as follows5,6,7,20,33,44,46,47,48,99,101,102,105Now execute Sequential search, and the state of the sorted array has been completed in the array, how many comparisons are required for the following numbers?48 : ___100 : ___
- Given the following array, what is the content of the array after Two passes of Selection Sort? array: 44 12 50 3 40 23 Question 1 options: 12 3 40 23 44 50 40 12 23 3 44 50 3 44 12 40 23 50 12 44 3 40 23 50given an array of integer values , return true if 6 appears as either the first or last element in the array. firstLast6([1,2,36]) true firstLast([6,1,2,3]) true firstLast([13,6,1,2,3]) falseComplete the following sentences by filling the right word To know the number of items in the first row in a 2D array variable array2D we use the command ………





