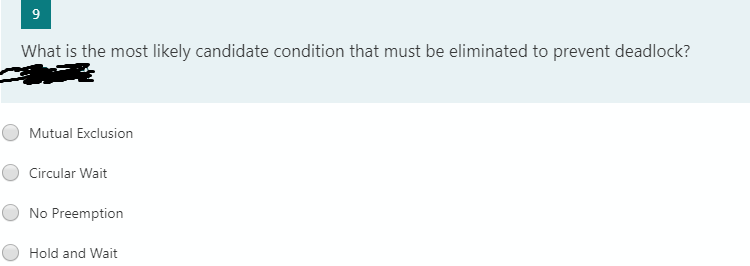
What is the most likely candidate condition that must be eliminated to prevent deadlock? Mutual Exclusion Circular Wait No Preemption Hold and Wait
Q: In order for there to be a deadlock, there must be mutual exclusion, there must be no preemption,…
A: Answer: In this question, three criteria must be satisfied in order for a stalemate to occur. And…
Q: Explain the difference between optimistic and pessimistic locking
A: Given: Explain the difference between optimistic and pessimistic locking
Q: Define the following and give at least an example for each or use one example for that can explain…
A: We use Bind variable in place of variables or literals values in sql statements. this helps improve…
Q: Is a deadlock possible? If so, write a C program that implements the deadlock-free solution. The…
A: Defined a deadlock possible or not and a C program that implements the deadlock-free solution
Q: t was stated that deadlock cannot occur for the situation reflected in Figure 6.3. Justify that…
A: Given: Justify your claim that the situation depicted in Figure 6.3 cannot result in stalemate.
Q: How may a stalemate be avoided by utilising a required condition? Discuss in depth.
A: Intro A situation in operating systems when there are two or more processes that hold few resources…
Q: Describe the necessary conditions for deadlocks to exist.
A: Resources Resources square measure the passive entities required by processes to try and do their…
Q: The dining philosopher problem is a classic problem in deadlock management. The problem can be…
A: Actually, given information The dining philosopher problem is a classic problem in deadlock…
Q: a. None of the options b. It does not satisfy the mutual exclusion c. It satisfies the mutual…
A: Below is the answer is reason explained:
Q: Discuss in brief about the following, (i) Strict two-phase locking (ii) Granularity.
A: The Answer is
Q: occurring? If th
A: Most modern operating systems are incapable of preventing deadlocks.When a deadlock occurs,…
Q: What are the methods for avoiding deadlock? Hello, it seems that the ones I was provided were…
A: A deadlock occurs when two PC applications using the same asset effectively prevent each other from…
Q: I'm trying to create a trigger function according to the following question: If an account is…
A: If an account is deleted, then write a trigger to delete the dependent tuple(s) from the depositor…
Q: commitment
A: Cisco Packet Tracer as the name suggests, is a tool built by Cisco. This tool provides a network…
Q: Consider the following RAG and choose the correct answer P3 R1 R2 a. Hold and wait situation b.…
A: 1. Deadlock can exist if and only if following 4 conditions hold simultaneously: 1. Mutual…
Q: Which of the following necessary and sufficient for deadlock? Select one: a.Circular wait b. No…
A: Deadlock : A Deadlock is a situation where each of the computer process waits for a resource which…
Q: Examine the below loop and find the true dependencies, output dependencies and anti dependences.…
A:
Q: s not a necessary condition for the occurrence of deadlock
A: Deadlock is a condition in transaction management where transactions are encircled in an infinite…
Q: Briefly describe the techniques for dealing with deadlocks.
A: Deadlock can be defined as any task or a set of task is in waiting state to get for getting complete…
Q: Deadlock is a term that refers to a situation where there is no way out What is the difference…
A: Introduction: Deadlock: A deadlock occurs in an operating system when any process enters a waiting…
Q: J 2 Indicate whether the following statements are True or false. Justify the reasoning and provide a…
A: The question has been answered in step2
Q: (X) Question 6 Determine what rule of replacement was used: ((~ O v P) V ~Q)·(~ 0 v (Pv ~ Q)) .: (~…
A: The question is to choose the correct option for the given question.
Q: What can be done to prevent or fix deadlocks in the Dining Philosopher's problem
A: Dining Philosopher's Problem:- The dining philosophers issue is one more exemplary synchronization…
Q: Given the final analysis of deadlock avoidance strategy, which of the four deadlock conditions does…
A: I have given an answer in step 2.
Q: Consider the traffic deadlock depicted in the Figure. Show that the four necessary conditions for…
A: Firstly , we should know what is deadlock ? Thereafter, we will discuss this realistic situation . A…
Q: write a C program that implements the deadlock-free solution.
A: Code: #include <pthread.h>#include <semaphore.h>#include <stdio.h> #define N…
Q: For a deadlock to arise, which of the following conditions must hold simultaneously
A: The answer:
Q: Consider a two-class case with classes fraudulent and nonfraudulent. A data mining routine has been…
A: Given: 50 records as fraudulent (30 correctly so) and 950 as nonfraudulent (920 correctly so)
Q: Discuss the 3 approaches for dealing with deadlock
A: Deadlock: Deadlock is the process in which tow or more transactions wait infinitely for the other…
Q: Is a deadlock possible? If so, write a C program that implements the deadlock-free solution. The…
A: ANSWER : The Dining Philosopher Problem – The Dining Philosopher Problem states that K philosophers…
Q: when do you use indirect method of deadlock prevention? please no handwritten answers, no one…
A: Solution: Given, when do you use indirect method of deadlock prevention
Q: 93. ODL supports which of the following types of association relationships? a. Unary b. Unary and…
A: Here is the solution which is mentioned below:
Q: Discuss the four conditions that are required for a deadlock to occur
A: Answer : Four necessary condition for occuring deadlocks : 1) Mutual exclusion 2) Hold and wait…
Q: 51. A direct method of deadlock prevention is to prevent the occurrences of ................... a.…
A: A direct method of deadlock prevention is to prevent the occurrences of Circular waits.
Q: Which of the following goals of a "good" locking scheme could using yield () in combination with…
A: All the given options are correct which means that Progress, Bounded waiting, Performances, Mutual…
Q: lock prevention is to prevent the occurrence of ………….. a. Mutual exclusion b. Hold and wait c.…
A: Given we are required to find out the direct method of deadlock prevention is to prevent the…
Q: Explain how the phantom problem might develop when key-value locking is utilised using sample…
A: Introduction: Within transactions, a problem known as phantom occurs when the same query produces…
Q: Consider a two-class case with classes fraudulent and nonfraudulent. A data mining routine has been…
A: Consider a two-class case with classes fraudulent and nonfraudulent. Calculate the overall error…
Q: what are the first three conditions for a deadlock to occur? please no handwritten answers, no one…
A: A deadlock is a one of the situation in which two computer programs sharing the same resource are…
Q: Using Referential Integrity Constraint with Cascading option risky from
A:
Q: When a stalemate is identified, the required resources are made available to those who are unable to…
A: Introduction: We must now recover the deadlock after it has been found. There are generally two ways…
Q: Now assume that the philosophers need both the forks to eat AND the sauce bowls to eat. Write…
A: Program For philosophers need both the forks to eat AND the sauce bowls to eat.
Q: Briefly describe the strategies for dealing with deadlocks.
A: Introduction: A deadlock occurs when one or more processes are stalled while waiting on a…
Q: Does the following approach ensure mutual exclusion? Provide reasoning. Does the following approach…
A: We are given two processes and we are given an algorithm which is suppose to ensure mutual exclusion…
Q: Q5) Mutual Exclusion: Peterson's solution Given the following code for Peterson's solution for two…
A: Answer 5: Peterson’s Algorithm is used to synchronize two processes. It uses two variables, a bool…
Q: In multiple-granularity locking, what is the difference between implicit andexplicit locking?
A: Answer: The multiple-granularity locking protocol ensures serializability by using various lock…
Q: The dining philosopher problem is a classic problem in deadlock management. The problem can be…
A: Assume that the philosophers need to access only a single fork to eat. In ad-dition to the forks,…
Q: A deadlock situation can arise if which of the following conditions hold simultaneously in a system.…
A: When two or more process waits for each other, So, both are waiting for each other to release the…
Q: what are the deadlock avoidance approaches? hello, it seems like the ones given to me were…
A: A deadlock is a circumstance where two PC programs having a similar asset are viably forestalling…
Step by step
Solved in 2 steps

- CSC 385 –Assignment 4 –Faster SortingAlgorithms .This problem is taken from a hackerrank programming challenge. The problem is tagged as having medium difficulty in hacker rank:(https://www.hackerrank.com/challenges/fraudulent-activity-notifications) Problem Description—Fraud DetectionHackerLand National Bank has a simple policy for warning clients about possiblefraudulent account activity. If the amount spent by a client on a particular day is greaterthan or equal to 2 ×the client's medianspending for the last d days, they send the client a notification about potential fraud. The bank doesn't send the client any notificationsuntil they have at least d prior days of transaction data.Given the value of d and a client's total daily expenditures for a period of n days (where n>d) write amethod which returns the number of times the client will receive a notification over all days.Note: Your algorithm time efficiency should not exceed O(nd) where n is the total number of daily…51. A direct method of deadlock prevention is to prevent the occurrences of ................... a. Mutual exclusion b. Hold and wait c. Circular waits d. No preemptionQuestion # 3 Assume that Dominique and Pricilla agreed to use an auto key cipher with initial keyvalue k1 = 11. Now Dominique wants to send Pricilla the following message“THE CLASS IS CANCELLED”. Encrypt the message before transmitting it over the Internet Remember: i need a Mathematics solution not computer program You must show all the steps of your work
- 54. A direct method of deadlock prevention is to prevent the occurrence of ………….. a. Mutual exclusion b. Hold and wait c. Circular waits d. No preemption70. For a deadlock to arise, which of the following conditions must hold simultaneously ? a. Mutual exclusion b. No preemption c. Hold and wait d. All of the mentionedSuppose Alice has r and w rights over the file book. Alice wants to copy r rights to book to Bob. a.Assuming there is a copy right c, write a command to do this. b.Now assume the system supports a copy flag; for example, the right r with the copy flag would be written as rc. In this case, write a command to do the copy. c.In the previous part, what happens if the copy flag is not copied? Note:Follow the concept of access control matrix and do not use commands like chmod.
- What is the difference between a binary semaphore and a counting semaphore? Question 9 options: A binary semaphore is used for mutual exclusion, while a counting semaphore is used for synchronization. A binary semaphore can only take two values, while a counting semaphore can take any positive integer value. There is no difference between a binary semaphore and a counting semaphore. A binary semaphore is used for synchronization, while a counting semaphore is used for mutual exclusion.Software caching. Since the default implementation of contains() calls get(),the inner loop of FrequencyCounterif (!st.contains(word)) st.put(word, 1);else st.put(word, st.get(word) + 1);leads to two or three searches for the same key. To enable clear client code like thiswithout sacrificing efficiency, we can use a technique known as software caching, wherewe save the location of the most recently accessed key in an instance variable. ModifySequentialSearchST and BinarySearchST to take advantage of this idea.Which of the following is true on Deadlock detection a. Must know the maximum need of resources b. Can avoid the deadlock c. Does not need to know the maximum need of resources d. None of the above
- q1- Confidentiality of Information is protected by ? a. Encryption b. Salting c. Encoding d. HashingHackerLand National Bank has a simple policy for warning clients about possiblefraudulent account activity. If the amount spent by a client on a particular day is greaterthan or equal to 2 ×the client's medianspending for the last d days, they send the client a notification about potential fraud. The bank doesn't send the client any notificationsuntil they have at least d prior days of transaction data.Given the value of d and a client's total daily expenditures for a period of n days (where n>d) write amethod which returns the number of times the client will receive a notification over all days.Note: Your algorithm time efficiency should not exceed O(nd) where n is the total number of daily expenditures and d is the number of prior day expenditures used for frauddetection.Your algorithm space complexity should not exceed O(n+d).where n is the total number of daily expenditures and d is the number of prior day expenditures used for frauddetection.Space complexity is defined as the…Determine the security flaws that are present in each method of authentication, then provide a solution to the problem that is described below:Bob makes a hash of a password, and then he checks it against a database of previously hashed passwords.Bob runs a password via a hashing algorithm and then checks it against a database of passwords that have been hashed twice.



