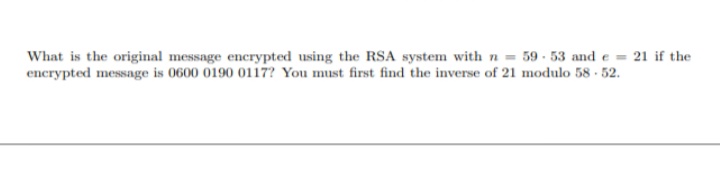
What is the original message encrypted using the RSA system with n= 59-53 and e = 21 if the encrypted message is 0600 0190 0117? You must first find the inverse of 21 modulo 58-52.
Q: ssues that simulation models may be able to expla
A: Introduction: Simulated models are parameterized models that are computer-solved because they are…
Q: 2. What are the design issues for character string types? 3. What is the primary difference between…
A: Given question: 2. What are the design issues for character string types ? 3. What is the primary…
Q: Please make a table contrasting engineering and computer ethics and provide five examples of when…
A: The answer to the question is given below:
Q: Exercise 1. Recall the Partition subroutine employed by QuickSort. You are told that the following…
A: We have to find the pivot elements from the given array.
Q: Implement the following: 1) Define a class Course with three attributes title, term, and enrollment.…
A: Solution: Required language is python. Please follow the below steps for solution. This question…
Q: Why do we need virtual LANs if many subnets can be created on a single switch, and if users on…
A: To route across distinct VLANs, you require a router. Additionally, the same IP subnet cannot be…
Q: Think about what you'd want to see in an entity identifier, then write it down.
A: The above question is solved in step 2 :-
Q: Have you ever seen an instance of internet bullying or harassment? To begin with, how did you feel…
A: On Facebook, I saw one of my friends being bullied. Whenever he publishes something—a joke, a…
Q: In terms of data transfer, do access points behave more like switches or hubs? Explain
A: Definition: In order to transfer network data from one device to the target device, a switch only…
Q: The OSI security architecture includes elaborate safeguards for the data it manages.
A: The executives in control of an organization's security can describe the need for security using the…
Q: a function deleteProp that has 2 parameters: obj an object to update keyName, a string - a key…
A: Please find the answer below :
Q: An end station sends 135,200 bits into a Frame Relay network in 200 milliseconds. The CIR is 400,000…
A: a) i have answered A part of the question.
Q: First, briefly explain what a method is before walking through its three main parts.
A: Modular programming is a software design technique that emphasizes dividing a program's…
Q: Among the following, which two are the strongest justifications for using layered protocols? If you…
A: Which two factors support layered protocols the most? The layers above and below it are unaffected…
Q: What are some of the benefits that RSA has over other symmetric encryption techniques, and why…
A: Introduction: We'll talk about the advantages of RSA versus symmetric encryptions. Because it…
Q: What are the potential repercussions that might arise from the implementation of a security…
A: Introduction: The process of systematically applying management policies, methods, and practices to…
Q: Loss of throughput in wireless networks is far greater than that in wired ones. Please provide the…
A: Introduction: Wireless networks often have collisions, which increases the overhead for each…
Q: In this program, you are provided with phenotype counts of F1 and F2 offspring at two research…
A:
Q: 1. Two m X n matrices are said to be row equivalent if one can be obtained from the other by a…
A: MATLAB code and it's answer a)
Q: So i need help understanding some stuff for my principles of programming class Can someone…
A: Primitive data types : The primitive data types are the data types that does not have any…
Q: Copy the main function and complete set function. The set function takes two arrays x, y and their…
A: Solution: Given,
Q: What are the most common components seen in network diagrams?
A: A network diagram is a graphical depiction of a project consisting of a sequence of linked arrows…
Q: Information stored in memory may be retrieved using either the sequential access technique or the…
A: Answer:
Q: appreciate it if you could tell me what may be slowing down my computer's startup time
A: Summary suffering with a slow pc? find out why your pc is slow and discover how to velocity it up.…
Q: How can you defend yourself from falling victim to a man-in-the-middle (MITM) attack? Act out your…
A: Introduction A "Man in the Middle" attack is a type of attack in which an intruder, more…
Q: of the OSI model requires th
A: Solution - In the given question, we have to tell which layer of the OSI model requires the highest…
Q: in the question it said that "Assume that the Reward and Department tables have already been created…
A: The correct SQL statement is given in the below step
Q: 4. What is the value of Y after solving the following expression? Y-Not 15 Mod 5-24/6 And 50/2>5^2…
A: The relationship between operands in a logical expression is defined by the logical operators AND…
Q: Wireless networks are pillars of mobile computing despite their known limitations. Many techniques…
A: Wireless networks These are the PC networks that are not associated with links of any sort. The…
Q: Scenario: A former employee repeatedly accessed his previous supervisor’s email account after…
A: Organizations must make sure that no unapproved individuals have access to any assets that could be…
Q: Authenticating messages may be done in a variety of ways
A: Answer:
Q: Using C# in Microsoft Visual Studio* create an application that lets the user enter a nonnegative…
A: The C# code is given below with an output screenshot
Q: need help writing a function, sumDigits, that sums up all the digits of a number passed in as an…
A: Answer:
Q: In what ways does the Tor network have restrictions?
A: Tor Network: Tor is an incredible device for web obscurity as long as you Just utilize their…
Q: Wireless networks are pillars of mobile computing despite their known limitations. Many techniques…
A:
Q: Would your school or place of work benefit from cloud computing? Identify at least two cloud…
A: Introduction Benefits of cloud computingCloud computing offers your business several edges. It…
Q: What is a Linux Distribution?
A: A computer operating system made up of components developed by several open source developers and…
Q: I want to convert string to int and then put them in two dimensional array I.e: "142045585" AS…
A: Solution: Given, I want to convert string to int and then put them in two dimensional array…
Q: Sum: a recursive function that computes the sum of integers 1, 2, 3, …., n for a given number n.…
A: Let's first discuss about recursion. Recursion:- It is the process in which a function calls itself…
Q: For our simple 2-stage pipeline, we run a particular benchmark program and find that it has 19%…
A: Stage 1 Keep in mind that we planned multicycle data sets in Section 4 based on (a) building…
Q: What is the result when evaluating the following Boolean expression? NOT ((false OR true) AND…
A: BOOLEAN EXPRESSION:- A Boolean expression is a mathematical expression that evaluates to either true…
Q: If you turn on a computer for the first time and nothing happens, is it indicative of a problem with…
A: Introduction Central Processing Unit, or CPU, is the term for the bulk of the computer's hardware…
Q: Please keep your responses to no more than three or four at the most. What does it look like to have…
A: Scientific learning drives technology. Because science is adaptable, you may find technical and…
Q: 2. Use JFLAP to design a Turing machine that accepts language L = {w: no(w) ni(w) and no(w)…
A: In 1936, Alan Turing created the Turing Machine, which is used to accept Recursive Enumerable…
Q: What are the advantages and disadvantages of the various generations of networking technologies, and…
A: Main Memory in Mobile: Main memory is the area within mobile devices where data may be kept. It…
Q: Please explain how a computer uses a cassette drive and how it is different from a regular tape…
A: Introduction: The first iteration of the IBM Personal Computer and the IBM PCjr both included…
Q: Another questions: this is my code (see image), and I was trying to let the turtle to draw 4…
A: In this question we have to draw the different sides square using turtle in java I will explain the…
Q: Analyze and have a conversation about the many techniques that may be taken using artificial…
A: Introduction: methods using artificial intelligence? There are four distinct forms of strategy. only…
Q: Explain in your own words the monetary upsides that certain persons or organizations may enjoy if…
A: Explain in your own words the monetary upsides that certain persons or organizations may enjoy if…
Q: What are the three conditions that must be true for a network to function effectively and…
A: Introduction: Networking isn't usually simply the changing of data with others — and it's really not…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- We receive the encrypted message 098 1 046 1. What is the decrypted message if it was encrypted using the RSA cipher from Example I I?Use the key 1010 0111 0011 1011 to encrypt the plaintext "ok" as expressed in ASCII, that is 0110 1111 0110 1011. The designers of S-AES got the ciphertext 0000 0111 0011 1000. Do you? Please explain step by step how to do as I am not clear how to doWe use DES in cipher feedback mode (CFB) to encrypt a plaintext m = m1m2 ...m100 into a ciphertext c1c2 ...c100, where each mi is 8-bit long. The ciphertext is sent to Bob. If c15 and c25 are missing and c8 and c88 are received as c8' and c88' wrongly, what mi’s can B compute correctly from the received ciphertext?
- What is the formula used for decoding the ciphered text using affine cipher(a,b are constants and x is the numerical equivalent of a letter to be encrypted)? 1. (a^-1) (x-b)%26 2. (ax+b)%26 3. (b^-1)(x-a)%26 4. (b^-1)(x-a)The affine cipher f(p) = (9p + 10) mod 26 is used to obtain the encrypted message F EMV Z,where p is the two digit representation (00-25) of each character in the original message. What is the original message?Using the RSA algorithm, perform an encryption and decryption of:i. Message M=15 using prime numbers p=7 and q=5 ii. Message M=13 using prime numbers p=11 and q=7
- Teemo has just received a message from Draven that was encrypted using the RSA algorithm. The public key that encrypted it was (95, 7). Decrypt the message from the laner. "37 79 43 43 54 35 79 43 70 27 67 44 00 70 70 11 44 70 27 85 85 00"How would I decrypt an RSA message? Let's say we're given C, p, q, e.In an RSA cryptosystem, you intercept a ciphertext C = 2022 sent to a user whose public key is (e = 27893, n = 124711). What is the plaintext M? Show your steps.
- Using the RSA algorithm, perform an encryption and decryption calculation of a Message M=32 using prime numbers p= 5 and q=11 Message M=25 using prime numbers p=11 and q=7 Message M=30 using prime numbers p=13 and q = 7Give encryption or decryption of these hexadecimal messages using the one-time pad algorithm, giving the result in hexadecimal also. You may wish to convert to binary first. a. m = 0xdeadbeef, K = 0x4ea04002, c = ? b. c = 0x84848484, K = 0xffffffff, m = ? c. c = 0x104557ce, K = 0xdabbad00, m = ?In a public-key system using RSA, suppose you intercepted a cipher text C = 61 sent to a user whose public key is e = 11, n = 91. What is the plaintext M? Explain the steps that you find the plaintext.

