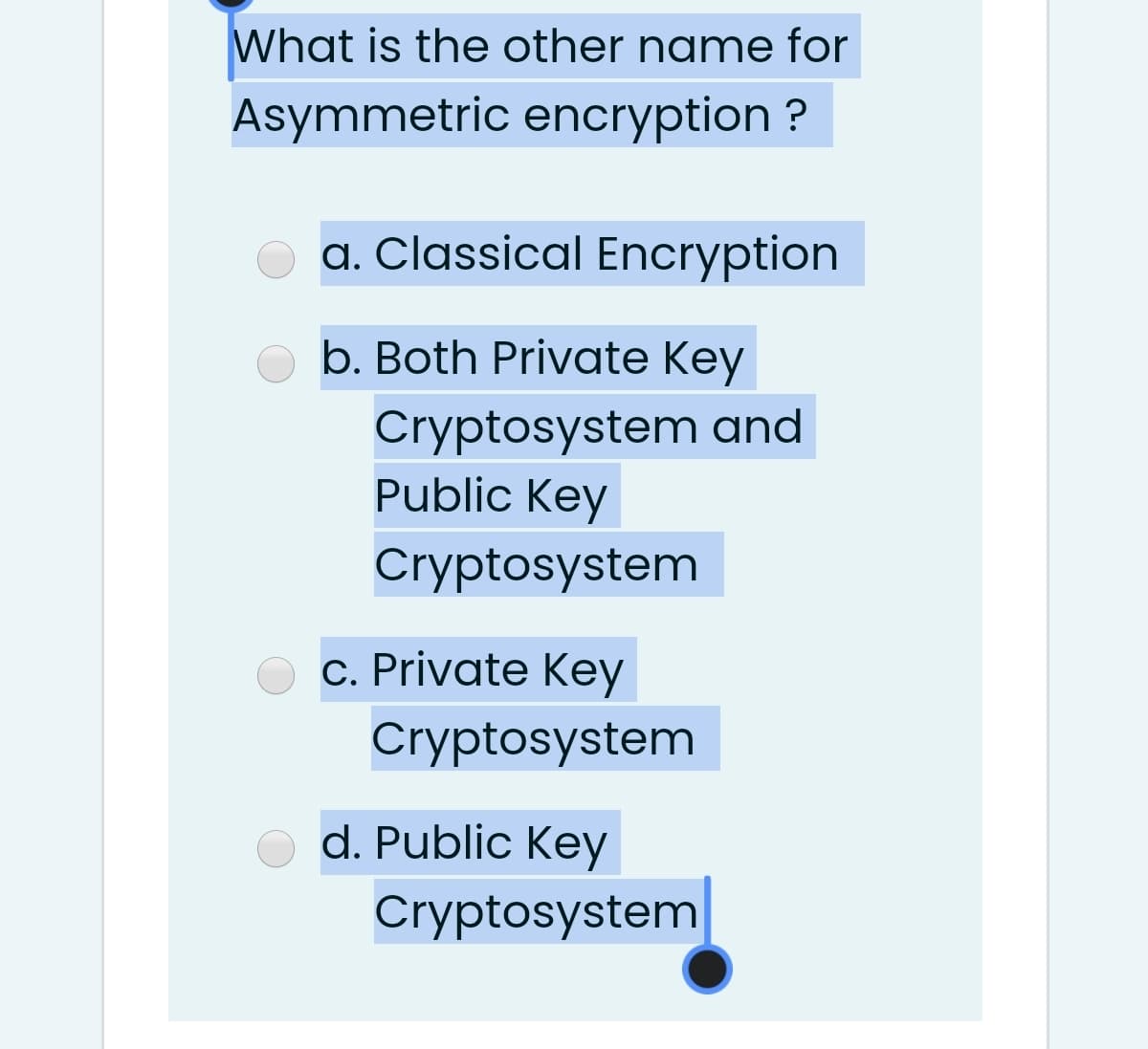
What is the other name for Asymmetric encryption ? a. Classical Encryption b. Both Private Key Cryptosystem and Public Key Cryptosystem c. Private Key Cryptosystem d. Public Key Cryptosystem
Q: What are the three most basic operations in the realm of cryptography, and what are they called
A: Cryptography Cryptography uses encryption to protect private information to keep it safe from…
Q: 1. Find the false statement: a. In modern Cryptography, symmetric key algorithms use same key both…
A: Given: -
Q: True or False?
A: Given statement is true.
Q: Is there a difference between symmetric and asymmetric key cryptography?
A: Yes, there is a difference between symmetric and asymmetric key cryptography. The detailed…
Q: 3. What are the shortcomings of key administration in symmetric encryption? 4. How many keys are…
A: 3. The biggest problem with symmetric key encryption is that you need to have a way to get the key…
Q: What exactly is the distinction between symmetric key cryptography and asymmetric key cryptography,…
A: Solution: When delivering communications, symmetric encryption uses a single key that must be shared…
Q: Which of the following goals of cryptography would be compromised, if an attacker is able to modify…
A: Which of the following goals of cryptography would be compromised, if an attacker is able to modify…
Q: Select the false statement from the list below. To encrypt data using public key cryptography, one…
A: Public key Cryptography: A pair of the keys called public key and a private key (a public key…
Q: the difference between secret and public key in cryptography
A: the difference between secret and public key in cryptography
Q: What's the difference between linear and differential cryptanalysis?What's the difference between…
A: Introduction of Cryptanalysis Cryptanalysis is the study of ciphertext, ciphers, and cryptosystems…
Q: What are the four main goals of cryptography? Explain the difference between symmetrical and…
A: Cryptography is the technique that is used to secure message or data usually in the field of…
Q: How many keys are needed if mutual secret key cryptography is used?
A: Mutual authentication, also known as two-way authentication, is a security process in which entities…
Q: Question 5: a. Using the key LARGES following the Playfair Cipher encrypts the message: NEED TO SEE…
A: a. Given that, Keyword = LARGES Plain text message= NEED TO SEE YOU IMPORTANT BEFORE SUNSET Play…
Q: Please make it readable and clear if you will write it so that i can understand the answers. Thank…
A: GIVEN: Please make it readable and clear if you will write it so that i can understand the answers.…
Q: Give an explanation of the distinctions between public key cryptography and private key encryption.…
A: distinctions between public key cryptography and private key encryption. List three benefits of…
Q: Between asymmetric and symmetric encryption which is more secure
A: Solution :
Q: Kerberos relies exclusively on __________ . A. symmetric encryption B. asymmetric encryption C.…
A: Asymmetric encryption: Asymmetric encryption is a public key encryption. It is a form of data…
Q: How many keys are required to achieve authentication and confidentiality in public key…
A: Public key cryptosystem is one which involves two separate keys for encryption and decryption. Each…
Q: What is a message authentication code in Cryptography?
A: MAC: In cryptography, a message authentication code (MAC), generally called a tag, could be a short…
Q: What is the difference between differential and linear cryptanalysis in Cryptography?
A: Differential cryptanalysis is a general form of cryptanalysis applicable primarily to block ciphers,…
Q: b) Discuss on the following cryptographic tools. (i) Public-Key Infrastructure (PKI) (ii) Digital…
A: According to the these tools is very useful in our daily life and reduce our hard work or save time…
Q: Discuss Bring Your Own Encryption (BYOE) as a type of encryption.
A: Discuss Bring Your Own Encryption (BYOE) as a type of encryption.
Q: What type of key is used in symmetric cryptography, must be known by both parties, and is used for…
A: Symmetric cryptography (Symmetric-key encryption):It is an encryption technique in which a single…
Q: Hi! This is not a graded question I just need it for my reviewer. Thanks? 3.a) What is the RSA…
A: RSA: asymmetric cryptography algorithm, which means this algorithm will work on bith public key and…
Q: uld you do if the keys were all di
A: 1. How many passes should you do if the keys were all different?
Q: 1. Which one of the following is true for asymmetric-key cryptography? a. Private key is kept by the…
A: Answer: a. Private key is kept by the receiver and public key is announced to the public.
Q: Select the false statement from the list below. To encrypt data using public key cryptography, one…
A: Answer:
Q: Is any of the following not a primary objective of cryptography? a) Confidentiality b) Data…
A: The four primary objective of cryptography is : 1. Confidentiality 2. Data Integrity 3.…
Q: Provide any 5 differences between private key encryption (symmetric encryption) and public key…
A: This question comes from Cryptography in Cybersecurity which is a paper of Computer Science. Let's…
Q: What exactly is the difference between symmetric key cryptography and the more traditional kind of…
A: here in the question ask for a difference between symmetric key cryptography and traditional kind…
Q: Assume the Public Key E=7 and N=35, encrypt the letter 'C' using RSA and write down the…
A: Here, E = 7 N = 35
Q: Q1: Cryptography and Information Assurance subject solve the question and the question A and…
A: Cryptography is a technique for safeguarding information and interchanges using codes, so just those…
Q: he public key encryption is explained in detail here.
A: USE OF A PUBLIC KEY FOR DESCRATCHING: Cryptographical encryption is the technique of encrypting data…
Q: Name the authentication technique that uses public key cryptography between the sender and the…
A: Message authentication Code Message Authentication Code (MAC) is a symmetric key cryptographic…
Q: n the world of cryptography, what would you say are the three most essential procedures
A: Answer : In cryptography three main procedures that are used are : Encryption of data
Q: One of the most basic problems that public key cryptography set out to solve was the problem of key…
A: The desire to tackle two significant challenges, one of which was key distribution, drove the…
Q: Who practices keeping the messages secure? a. Cryptologists b. Cryptanalysts c. Cryptanalysis d.…
A: Cryptologists are responsible for interpreting and analyzing information Cryptanalysts are…
Q: In which cryptography technique, sender and the receiver use different keys?.
A: Because asymmetric key cryptography is also known as public key cryptography in which it utilizes…
Q: How many keys are needed to use cryptography with a shared secret
A: A secret key (or "private key") is a piece of information or structure used to decrypt and encrypt…
Q: Was it ever a good idea to be "out of band"? What is the significance of exchanging keys outside of…
A: 1) In the correspondence, the definition of the phrase "Out of Band" is questioned. 2) The…
Q: fference between linear and
A: Solution - In the given question, we have to tell the difference between linear and differential…
Q: What is the precise distinction between symmetric key cryptography and more conventional encryption?
A: The Answer is in step-2.
Q: For each of the following cryptographic algorithms, describe what they do your own words and state…
A: For each of the given cryptographic algorithms, we need to describe their role and type.
Q: What is the difference between symmetric key cryptography and asymmetric key cryptography, and how…
A: Symmetric encryption utilizes a specific key that needs to be divided between the people who need to…
Q: Find the false statement: a. In modern Cryptography, symmetric key algorithms use same key both for…
A: Here the false statement is Answer c. The AES (Advanced Encryption Standard ) cryptosystem allows…
Step by step
Solved in 2 steps

- q6- What is the encryption of the message m = 9 in the RSA system which has <n= 91, e= 3> as a public key ? Cipher Text : ? Hint: n = p*q = 7*13 = 91Which of the following assertions is false: There are two keys used for encryption and decryption in public-key cryptography. O Unencrypted data is the same as plain text. None of the above choices ring true. The terms encryption and cipher text are not interchangeable.Which of the following statements is FALSE regarding cryptography? a. Asymmetric ciphers use the sender’s public key to encrypt a message b. The difficulty of breaking RSA algorithm depends on prime number factorisation c. DES algorithm is an example of stream cipher d. Symmetric ciphers are faster than asymmetric ciphers
- Which of the following operations do not achieve non-repudiation? a.Encryption using hybrid cryptosystems b.Digitally signing a message digest c.Digitally signing a complete message d.MAC2. RSA uses modulo math as the basis for creating a public and private key True. or. False 4.When the intruder knows some of the plaintext and cipher-text pairings, this is known as what type of attack? Cipher-text attack Known-plaintext attack Chosen-plaintext attackThe following is a message encrypted using keyword cipher and you know the keyword is CYBERSECURITY and the key letter is “a”. Decrypt the message and show all your work. OIR GJN OTG KJM OCH OCO OTO PER OIC OBC HYR SJM GRE TNO ICO JSE RNT MRO JUJ JHF RCM H
- Which of the following description regarding the RSA encryption are correct? Group of answer choices RSA Encryption is a symmetric key crypto In RSA Encryption, only the private key can be used to encrypted data. RSA Encryption is an asymmetric key crypto In RSA Encryption, both private key and public key can be used to encrypted data.The following is a message encrypted using keyword cipher and you know the keyword is CYBERSECURITY and the key letter is “a”. Decrypt the message and show all your work. OIR GJN OTG KJM OCH OCO OTO PER OIC OBC HYR SJM GRE TNO ICO JSE RNT MRO JUJ JHF RCM HTH UWhich of the following is wrong? (a) Symmetric encryption algorithms are faster than asymmetric encryption algorithms. (b) Symmetric encryption is not scalable. (c) Asymmetric encryption offers e-signature. (d) Secure key distribution in asymmetric encryption algorithms is even more difficult than in symmetric encryption algorithms.
- What type of key is used in symmetric cryptography, must be known by both parties, and is used for both encryption and decryption? Group of answer choices Ciphertext Shared secret Private key Public keyInstructions: 1. Read: Computer Security Fundamentals, 4th edition (Chapter Eight) 2. Answer: Answer the following questions: • Question 1: It is easy to use encryption to hide messages inside of other objects. Steganography is the art of hidden writing. You can get Hide In Picture (HIP) at https://hide-in-picture.soft112.com/.. You can then encrypt a message or even a program that can be extracted by using an encryption key. Download HIP, hide a text message in a picture, and send the picture and key to your classmate to see whether he can extract the secret message. How could you detect hidden messages in web page images? Individual Assignment 2 • Question 2: ROT13 is an interesting encryption algorithm in that it has no key. It uses a form of the Caesar cipher to encrypt text. Try encoding a message by entering text in the box at http://www.rot13.com/. Exchange your encrypted message with someone else in class. Then enter their coded message you've received into the text box.…You encrypt the message zzzzzzzzzz (there are 10 z's) using the following cryptosystem: Vigenère cipher with key length 7. Eve intercepts the ciphertext. She knows the encryption method (including key size) and knows what your plaintext is. For the cryptosystem, determine whether or not Eve can use this information to determine the key. Explain your answer.

