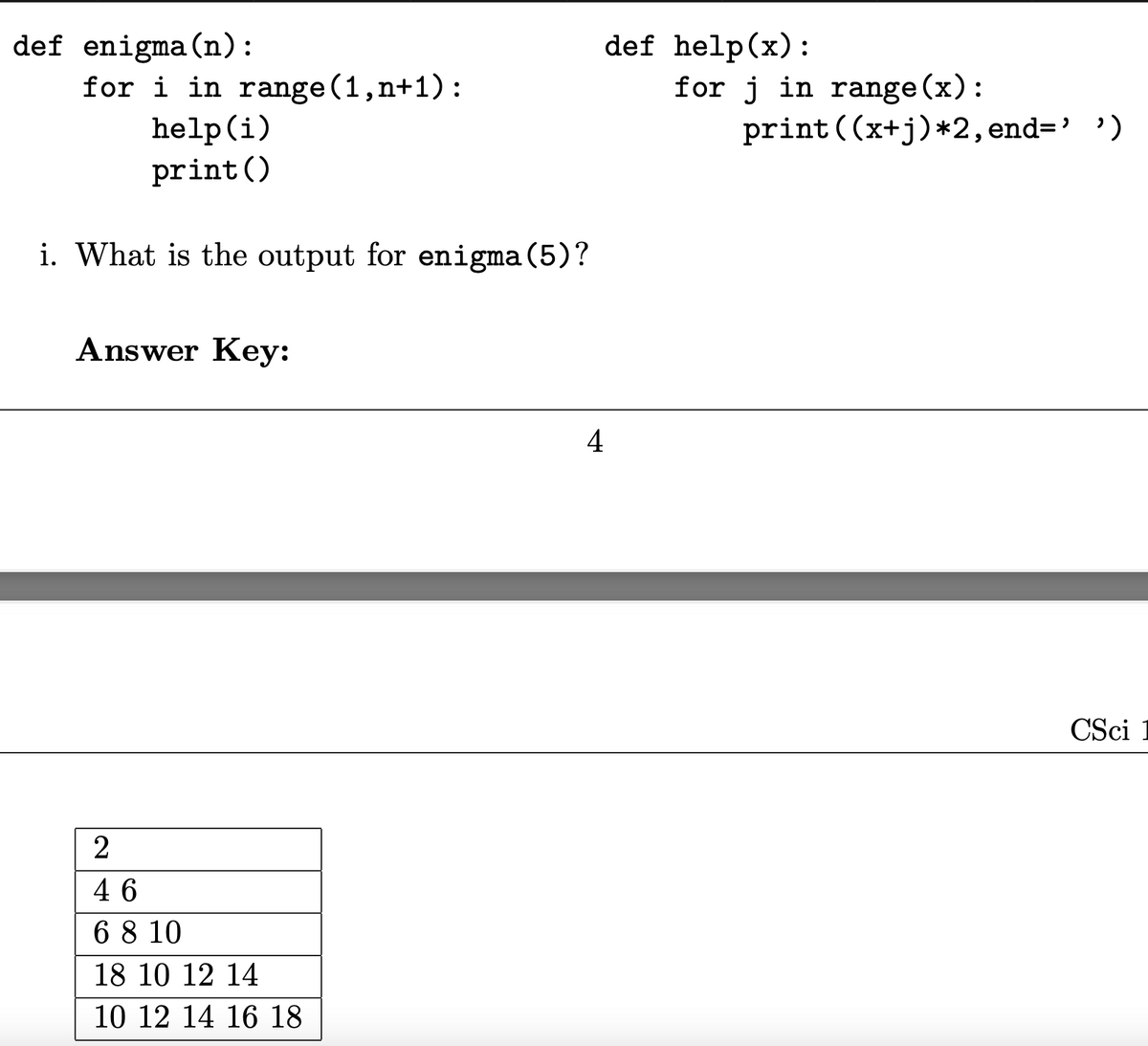
What is the output for enigma(5)?
Q: What's the difference between what a user wants and what a system wants?
A: The user's world is the basis of the issue while discussing user needs. They explain what the…
Q: What does it imply when websockets allow full-duplex communication, and how did we obtain equivalent…
A: WebSocket: What does it mean when websockets provide full-duplex communication, and how did we get…
Q: A cellular network is designed to achieve a maximum data rate of 1 Gbps in the downlink in a 20 MHz…
A: A cellular network is designed to achieve a maximum data rate of 1 Gbps in the downlink in a 20 MHz…
Q: Count to 3, then asks the user to continue or not. (The student must use loop to print the counter)…
A: ALGORITHM:- 1. Create a variable count and initialise it with 1. 2. Use a loop to print till 3 and…
Q: how artificial neural networks operate,
A: Artificial neural networks, also known as neural networks inspired by the neural networks of the…
Q: how services and apps that are hosted in the cloud may be accessed and utilized.
A: Given: Users can use a browser or an app to access cloud services. They connect to the cloud over…
Q: In the context of a wireless network, what precisely does the term "Access Point" refer to? In what…
A: Compared to using cables and connections to connect any PC or device in your firm, WAPs are a more…
Q: b. Perform multiplication of 4-bit twos complement binary numbers (-3 x -5), by showing the steps…
A: We are going to multiply (-3)×(-5) using Booth's algorithm. In Booth's algorithm, we run it till the…
Q: Create a program that will sort the following words: Example: Will, Mike, Dustin, Lucas, Max, Eleven…
A: Answer in step 2
Q: Isit feasible to create a succession of interrelated judgments using dynamic programming? What am I…
A: Dynamic Programming: Utilizing dynamic programming to solve issues that can be decomposed into…
Q: QUESTION 1 Which of the following keywords is used to inherit a class? A. this B. super C. extends…
A: Inheritance is a concept in Object oriented programming where a child class gets to inherit the…
Q: Masking effects in acoustics and their significance in MP3 compression may be explained in your own…
A: Given: Explain acoustic masking phenomena and their importance in MP3 compression in your own…
Q: Questions about Repetition Structure Which is the easiest way to looping? Explain. Find working…
A: The answer is given in the below step
Q: Design a 4-bit 2’s complementer circuit. The unknown will be treated as don’t care. Include the…
A:
Q: 2. application of formal concept analysis in artificial intelligence
A: Introduction: Artificial intelligence Overview Artificial intelligence is defined as the ability of…
Q: Symmetric vs asymmetric key cryptography: what's the differenc
A: Symmetric key cryptography or Private key encryption: The encryption and decryption of the…
Q: 'How are RGB color beams formed in CRT displays?'
A: CRT: CRT stands for cathode-ray tube, which is used in TVs, computers, and other devices to display…
Q: What is the most important technique database designers may employ to influence database performance…
A: Denormalization is a strategy enabling rapid access to stored data used by database designers to…
Q: > X(XY) = XY + XX
A: All are wrong X(XY) XY ALL OPTIONS ARE NOT EQUAL to XY
Q: Describe how virtual machines lack support for instructions set architectures.
A: Introduction: Virtual machines Computers within computers which are virtualized A virtual machine,…
Q: The shortest route between the source and the destination should be determined in a backbone…
A: This question tells you how to find the shortest path from the source to the destination in a…
Q: You are planning to call 8 of your relatives on the first day of Ramazan Holiday. On this day the…
A:
Q: How exactly does the notion of an infrastructure-based wireless network operate? What other tasks…
A: A Wireless Network that Is Based on Existing Infrastructure: The term "infrastructure-based network"…
Q: how services and apps that are hosted in the cloud may be accessed and utilized.
A: This question pertains to accessing and utilizing cloud-based services and applications.
Q: It's possible that social networking sites are a good place to get useful in formation.
A: Social networking sites (SNS) are a means for maintaining offline connections despite geographical…
Q: Describe how a computer's operating system does its two primary tasks.
A: The operating system functions are: System for employment accounting This information may be used to…
Q: What criteria should be used to assess a cloud computing service by a company?
A: Faster delivery times and cheaper infrastructure costs are transition-specific benefits. To begin,…
Q: By default, the system journals are kept in what directory?
A: The tern journal refers to the systemd capable to have its own logging system. By default, the…
Q: What challenges have you encountered when adding or removing users from Windows 10 and Linux
A: Viruses are programs intended to damage the system.
Q: What is the process that is used to route data in a wide area network?
A: Introduction: What is the process that is used to route data in a wide area network?
Q: What does a wireless infrastructure network do? What happens when a network isn't in infrastructure…
A: What is wireless infrastructure and how does it function? What does the network do when it is not…
Q: When packets traverse networks, what happens to their MAC addresses? When IP addresses traverse…
A: Intro A network consists of two or more computer that are linked in order to share resources and…
Q: What exactly is a "man in the middle" assault and how does it work?
A: Cyberattack: Any offensive move that targets computer information systems, computer networks,…
Q: 1) Explain all types of loop [for, foreach, while do while, nested loop] with suitable program
A: As per our guidelines, we are supposed to answer only one question. Kindly repost the remaining…
Q: Describe how virtual machines lack support for instructions set architectures
A: Introduction: Describe how virtual machines lack support for instructions set architectures.
Q: Is it possible for businesses to make use of cloud services in a risk-free and protected manner?
A: Businesses will learn how to use cloud services safely and securely: Cloud computing may be utilized…
Q: It is easy to see how the execution of instruction set architecture exemplifies abstraction in…
A: Abstraction: It is a device used to conceal irrelevant nuances and emphasize just the essentials so…
Q: What signs could point to a hacked laptop's operating system?
A: What signs could point to a hacked laptop's operating system?
Q: What are the legal ramifications of the data concerns that are being discussed?
A: Information Property: Because access to and exploitation of Big Data is becoming essential to future…
Q: System administrators need to know why and how backups are necessary.
A: Data Backup: A backup or data backup is a duplicate of computer data that is collected and stored…
Q: What are the three most important database management tasks?
A: Introduction: Hardware.The hardware refers to the computer equipment that is used to store and…
Q: how services and apps that are hosted in the cloud may be accessed and utilized.
A: Answer: Introduction: The services and the apps that are hosted in the cloud will be accessed either…
Q: What is "gid computing"? What is "cloud computing"?
A: Given: Grid computing is the utilisation of a large number of devices, generally distributed…
Q: Decoder can be considered as : MUX DEMUX ENCODER ADDER
A: Given question are multiple choice option selected question.
Q: How many gates are needed to implement equation F- XYZ+ XYZ + XZ, Draw the equivalent circuit using.
A: Total 4 gates ara required for above circuit. They are 3 AND gates and 1 OR gate.
Q: 5. Draw a decision table for the following scenario. A private bank provides loan for its account…
A: Here we have given a decision table for the loan amount. you can find the solution in step 2.
Q: 2 Create a truth table for conditional statements Pis true then Qis true" write the implication.
A: The conditional statement "If P is true then Q is true" for this the truth table is The…
Q: What makes commercial SSDs distinct from those used in laptop computers?
A: Answer:
Q: Task 06: Use the recursive definition of Fibonacci series and write a function int fib(int n) that…
A: ALGORITHM:- 1. Take input for the value of n from the user. 2. Pass it to the fib() function. 3.…
Q: In a wireless ad hoc network, what kind of metrics are used for routing?
A: Introduction: Here we are required to explain what kind of metrics are used in ad hoc network…
Can you please explain this?
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- PYTHON! How is the ouput of this 13? This confuses me def Q2(n): if (n <= 0): return 1 return 1 + Q2(n-2) + Q2(n-3)print(Q2(6))Find the value of n that solves this puzzle. At what value of n does s reach 39?The code is in C int n = ? int m = 39 int t = 39; int s = 0; while(n>1){ if(n & 1){ n = (n<<2) - n + 1; } else { n = n >> 1; } if(s == t && m == t){ return; } s++; } failure("Seems you forgatz the essence of Collatz");On a piano, a key has a frequency, say f0. Each higher key (black or white) has a frequency of f0 * rn, where n is the distance (number of keys) from that key, and r is 2(1/12). Given an initial key frequency, output that frequency and the next 4 higher key frequencies. Output each floating-point value with two digits after the decimal point, which can be achieved by executingcout << fixed << setprecision(2); once before all other cout statements.
- Many user-created passwords are simple and easy to guess. Program that takes a simple password and makes it stronger by replacing characters using the key below, and by appending "q*s" to the end of the input string. i becomes ! a becomes @ m becomes M B becomes 8 o becomes . Ex: If the input is: mypassword the output is: Myp@ssw.rdq*s IN JAVA. USING LOOPSStart with any positive number n. If n is even divide it by 2, if n is odd multiply by 3 and add 1. Repeat until n becomes 1. The sequence that is generated is called a bumpy sequence. For example, the bumpy sequence that starts at n = 10 is: 10, 5, 16, 8, 4, 2, 1and the one that starts at 11 is11, 34, 17, 52, 26, 13, 40, 20, 10, 5, 16, 8, 4, 2, 1 Write a function named lengthBumpy that returns the length of the bumpy sequence generated by its integer argument. The signature of the function is int lengthBumpy(int n) Examples:lengthBumpy(10) returns 7, and lengthBumpy(11) returns 15. You may assume that the argument n is positive and that the sequence converges to 1 without arithmetic overflow.Substitution ciphers are encryption/decryption algorithms that replace one letter or number with another. The first attested use of a substitution cipher in military affairs was by Julius Caesar, described by him in Gallic Wars (cf. Kahn pp83-84). In caesar cipher , you replace each letter by 3rd letter on. If it is out of bound (later than Z), then round to the head (letter A) and continue the shift. For example:meet me after the toga party PHHW PH DIWHU WKH WRJD SDUWB Please write a program in Java to implement the Caesar Cipher: a. Implement the encryption algorithm. Ask the user to input one all lower case normal sentence (called plaintext) using the nextLine method, and then output the encrypted text (called ciphertext). b. Implement the decryption algorithm. Ask the user to input one encrypted sentence (i.e. ciphertext) using the nextLine method, and then output the decrypted text (i.e. plaintext).
- Write a Java program to read in a maximum integer n and use nested loops to print a list of divisors for each of 1 through n as shown in the following ways: Largest integer? 95 1: 1 2: 1 2 3: 1 3 ... 95: 1 5 19 95In Python, Solve the locker riddle which reads as follows:Imagine 100 lockers numbered 1 to 100 with 100 students lined up in front of those 100lockers:The first student opens every locker.The second student closes every 2nd locker.The 3rd student changes every 3rd locker; if it’s closed, she opens it; if it’s open, she closes it.The 4th student changes every fourth locker (e.g., 4th, 8th, etc.).The 5th student changes every 5th locker (e.g., 5th, 10th, etc.).That same pattern continues for all 100 students. Which lockers are left open after all 100 students have walked the rowof lockers?Computer Science In Erlang, how do i create this: % in1to10(n, outside_mode)% Given a number n, return true if n is in the range 1..10, inclusive. Unless "outsideMode" is true, in which case return true if the number is less or equal to 1, or greater or equal to 10. in1to10(_,_) -> true.
- Note: I got provided with the wrong answer class Calculator: def add(n1,n2): return n1+n2 def subtract(n1,n2): return n1-n2 def multiply(n1,n2): return n1*n2 def divide(n1,n2): return n1//n2m=int(input())op=input()n=int(input())print("Let's Calculate!")print("Value 1:",m)print("Operator:",op)print("Value 2:",n)if op=='+': Result=Calculator.add(m,n)elif op=='-': Result=Calculator.subtract(m,n)elif op=='*': Result=Calculator.multiply(m,n)elif op=='/': Result=Calculator.divide(m,n)print("Result:",Result) This was the question: Question 1 Suppose your little sibling wants your help to check his math homework. He is done with his homework but wants you to see if all his results are correct. Since the student with all correct results gets 3 stars. However, you want your brother to check this on his own. So, you design a calculator for him in python. You could have given your scientific calculator but you wanted to give him a…Java Program Please Write a program that will print a histogram of stars indicating the number of students who earned each unique exam score. last 10 lines of outputs should look like below: (there are 5 students who scored 90 and 1 student who scored 99 for example) 90: ***** 91: *********** 92: ******** 93: ****** 94: ** 95: ******** 96: ***** 97: **** 98: ** 99: * 100: **On a piano, a key has a frequency, say f0. Each higher key (black or white) has a frequency of f0 * rn, where n is the distance (number of keys) from that key, and r is 2(1/12). Given an initial key frequency, output that frequency and the next 4 higher key frequencies. Output each floating-point value with two digits after the decimal point, which can be achieved by executingcout << fixed << setprecision(2); once before all other cout statements. Ex: If the input is: 440.0 (which is the A key near the middle of a piano keyboard), the output is: 440.00 466.16 493.88 523.25 554.37 Note: Use one statement to compute r = 2(1/12) using the pow function (remember to include the cmath library). Then use that r in subsequent statements that use the formula fn = f0 * rn with n being 1, 2, 3, and finally 4.











