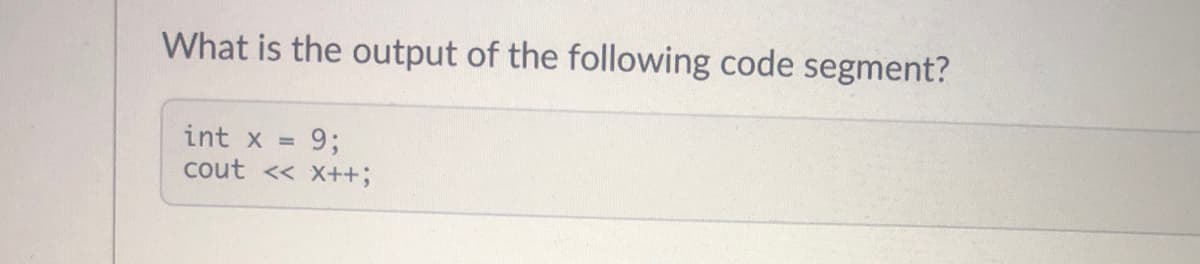
What is the output of the following code segment? int x 9; %3D cout << X+3B
Q: Check all 16 combinations of S, R, Q and Q and verify that the five output states of the NAND-based…
A: From the description, we can define the function as f(A,B,C,D)=∑(4,6,8,10,12,14)+d(0,1,2)
Q: Computer science What are the different gadgets that are employed in the creation of security…
A: Introduction: Security systems are intended to assist people in determining who the unauthorised…
Q: For Letter -> A | B Digit -> 0 | 1 Id -> letter (letter | digit)* Generate NFA and…
A: The above rules are for what are allowed IDs Id -> letter (letter | digit)* This says that id has…
Q: Write an assembly program to perform the signed multiplication of: In masm A. Byte (-8) by byte…
A:
Q: In terms of application and implementation, distinguish between data mining and warehousing.
A: Introduction: Data warehouse: A data warehouse is a sort of database that is used to compile and…
Q: Given the following variable declarations: const size_t n = 50; Write the declaration of an an array…
A: The answer as given below:
Q: Prescription is in 2NF. Is table Prescription in 3NF, given the dependencies? If yes, why? If not,…
A: Data Structure Software: Tools are necessary to eliminate excess and inconsistencies, preserve…
Q: dentify and categorize the data on your computer or PDA. What information is confidential, sensitive…
A: Information is defined as news or knowledge that is received or imparted. A piece of information is…
Q: What are the basic functions of a network operating system?
A: Functions of network operating system: A network operating system is an operating system designed…
Q: Embedded system Write the code in MPLAB and apply it on Protues to make the led blink on bit five…
A: We will write code which will blink LED on particular port with a delay of one second. For this we…
Q: When you go into the boardroom and attempt to connect your laptop to the projector, you find that…
A: Introduction: When you walk into the boardroom to connect your laptop to the projector, you discover…
Q: Describe the processes required to get a fresh new computer ready for use.
A: Intro Preparing a brand new computer focuses on the performance and the infrastructure of the…
Q: Explain why a Group chart of accounts isn't required when all of the business codes in the group…
A: COMPANY CODES USE THE SAME ACCOUNTING SYSTEM: When the group's company codes share an operational…
Q: Computer science A mobile application is used to display local traffic conditions. Which of the…
A: Introduction: Crowdsourcing: Crowdsourcing is the process of acquiring input or information for a…
Q: Explain the flow of this program ? def new_game(): guesses = [] correct_guesses = 0…
A: The given code is a quiz application where the program displays 4 questions one by one with its…
Q: What is the difference between the java.io and java.nio packages?
A: Answer is given below
Q: What are the many types of general concerns that may have an impact on software?
A: Introduction: According to the question, when software is released into the market, they confront a…
Q: What is the purpose of arithmetic operations?
A: INTRODUCTION: Here we need to tell the purpose of arithmetic operations.
Q: Surpreeth wishes to add two more client entries to the customer table. Which command is used to do…
A: Intro We are given a situation in a database table where we are going to apply SQL command to add…
Q: ugh maps, simplify the following Boolean functions: E = F(x, y, z) (0,1,4,5) Question 3B: Make a…
A: Solution - In the given question, we have to simplify the given boolean function using Karnaugh map…
Q: Write a Program to reverse a given 5 digit Integer number.
A: code : program ReverseOfAFiveDigitInteger;uses crt;var five_digit_number, reverse : LONGINT;begin…
Q: Kindly draw the Data Flow Diagram (DFG) for code. function parseString(str, a, b) { var cb, options;…
A: The DFD for the given program is as follows.
Q: System administrators are well-versed in the systems they oversee. What are the essential skills for…
A: Introduction: System administrators have two key responsibilities: problem solving and problem…
Q: Write a program called TwoDimensionalSearch.java that prompts the user to enter a integer. You…
A: Step-1: StartStep-2: Declare an array data with array element { 1, 2, 3, 4, 5, 6, 7 }, { 8, 11, 15,…
Q: Convert the code into compiled RISC-V code in simplified solution : for(i=0;i< size;i++) If(B[i]…
A: The solution to the given question is: RISC-V code: f(int*, int*): # @f(int*, int*) addisp, sp, -32…
Q: What is the evolution of computer security into current information security? Explain.
A: Computer security is the process of defending a computer system against theft or damage to its…
Q: B/ what is the general formula for each expression? 1-linear spacing. 2- rand function. 3- subplot.
A: Please refer below for your reference: According to the guidelines of company we are restricted to…
Q: DBMs
A: DBMS: DBMS stands for database management system which is a software system that is used to store…
Q: How would you define magnitude as a computer scientist?
A: Intro The representation of a number's magnitude (decimal) in computer science is the…
Q: The given SQL creates a Movie table and inserts some movies. The SELECT statement selects all…
A: Answer
Q: What role may health informatics experts play in health data standardisation?
A: Introduction: Professionals in the subject of health informatics utilize their skills and expertise…
Q: Explain why professional software generated for a customer is more than just a collection of…
A: Introduction: Due to the fact that professional software is nearly often packed with relevant…
Q: What exactly is a datapath?
A: Intro A datapath is a communication link between two points and is sometimes used to describe the…
Q: 1. In Enterprise Architecture, what is the distinction between View and Viewpoint? 2. What exactly…
A: 1. The main difference that we can notice between them is that what you see is a view and from where…
Q: erm Paper on "Implement Floyd–Warshall Algorithm Using C Language". You have to follow these…
A: #include <stdio.h> // defining the number of vertices#define nV 4 #define INF 999 void…
Q: In the contact management AddressBook application we studied in this course, how are the Java Server…
A: To find which option are the Java Server Faces pages connected to the named or Managed Bean.
Q: put Enter Course Name Advanced Programming
A: Java Code: here After Pressing the ok button, I am displaying the course name as a label and After…
Q: Wh ded te me e O R O PO O Serve
A: LAN or Local area network is a network in which some computers are connected to each other to form a…
Q: What exactly is a process? Describe how operating systems describe processes.
A: The process is to implement a package that performs the actions defined in that database. As an…
Q: If the task runs an average input of size 100, rank the algorithms from least time- complex to…
A: The answer is
Q: und describe the eight
A: In order to better understand the communication process, we can look at eight essential components:…
Q: If you compare incremental development to the waterfall technique, what are the three benefits of…
A: Introduction: When comparing incremental development to waterfall devilment, what are the three…
Q: Most programming languages currently adopt Algol60's free structure, where statements can begin…
A: Readability, writability, and security as a result of free format: Free-format languages are those…
Q: How can a computer program be optimized so that it runs quickly and consumes little energy on a…
A: Gathering instructions from the processor through a pipeline is known as pipelining. It provides for…
Q: What is the ICT for you?
A: The answer is given below :
Q: How many host addresses are available in a /17 network?
A: Introduction In a /17 network, how many host addresses are there to choose from
Q: NAME three important features of VLANS which make them useful in computer networks. What is the NAME…
A: Vlan stands for virtual local area network . The concept of VLAN is based on connecting the devices…
Q: How would i use python the create a function to display the different stores that made a sale in…
A: The first thing to be done is to copy the csv file in the root folder where python files are…
Q: What is the distinction between two-tiered and three-tiered architectures, and where are the four…
A: Two tiered: The two-tier depends on Client Server architecture. It resembles a customer or client…
Q: 10. Propositional logic with three proposition symbols A, B and C can tell apart eight different…
A: Here in this question we have given three proposition symbol..and with 8 different word how many can…
Step by step
Solved in 2 steps with 1 images

- What is the function of the following code?//code startconst size = 4;const ArrayOfSize = [];for (var i = 0; i < size; i++);{ArrayOfSize.push(i + 1);}ArrayOfSize;//code endWhat is the final value of x when the following code is run? int x;for(x =1; x<20; x+=2) {}What will be the value of x after the following code is executed? int x = 0; while (x < 50) { x += 20; } 50 20 40 60
- can you check which part my code wrong? #include <iostream> using namespace std; int main(){ int board [3][3] = {15, 25, 13, 20,4,7,11,18, 14};for (int r=0;r<3; r++) board[r][2] = board[r] [2] + 5;for (int r=0; r<3; r++) for (int c=0; c<3; c++);{ cout << board [r][c];cout << endl; } return 0; }trace the following code and give the output. for (int a = 1; a <= 3; a++) for (int b = 1; b <= 3; b++) cout << a+b << endl;what are the values of the variables when runned? int j,kboolean mj = 1k = j++m = (++k == j++) ------------------ int x = 3if (x == 2)x= 0if (x==3)x++elsex+=2 --------------- how many times will it be looped for(int x = 0; x== 2; x++){//body of the loop}
- Assume int[][] x = {{1, 2}, {3, 4}, {5, 6}}, what are x.length are x[0].length? 5 3 and 2 4 2 and 1 3 2 and 3 2 2 and 2 1 3 and 3For the following code fragment, what is the value of the variable b at the end? int a = 0; int b = 3;int c = 2;while ( a < 5 ){ a = a + 1; b += 3;continue;c = c * 2; }What is the output of following code fragment? int e = 7; int f = e--; System.out.println(e + " " + f);





