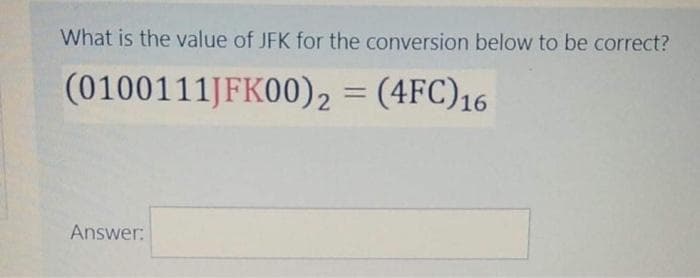
What is the value of JFK for the conversion below to be correct? (0100111JFK00)2 = (4FC)16 %3D
Q: What prompted the development of the RISC architecture concept?
A: RISC(REDUCED INSTRUCTION SET ARCHITECTURE):It is a small and reduced set of instruction. It is a CPU…
Q: Developing a threat model is a complicated process
A: The answer is as follows.
Q: Demonstrate that under reversal, the class of context-free languages is closed.
A: CFG is an abbreviation for context-free grammar. It is a formal grammar used to produce all possible…
Q: Deeply and briefly explain about intel AI for youth?
A: Artificial intelligence can be defined in a variety of ways, owing to the difficulty of defining…
Q: One advantage of compiling to bytecode rather than machine code is that it saves time.
A: Byte code is the intermediate code between the source code and machine code. The byte code is…
Q: Do you consider Ada Lovelace to be a cryptographer or a computer programmer when you think of her?
A: The following is the distinction between programming and cryptography: Computer programming is…
Q: What role does a motherboard play in a computer?
A: Components of a computer system: Computers may be made up of distinct specialized parts and…
Q: Because a data warehouse is too large for business intelligence, a data mart is preferable to a data…
A: Justification: A data warehouse is a sort of data management system that is intended to facilitate…
Q: What is a poison packet assault and how does it work? Give two instances of this kind of assault in…
A: Introduction: Poison packet assaults are the most prevalent kind of attack in which attackers…
Q: Assume you want to use parallel arcs to solve a maximum flow problem, but you don't have a maximum…
A: The Maximum Flow Issue: A maximum flow issue involves determining a viable flow across a leading…
Q: There should be four vulnerability intelligence sources specified and described. Which one appears…
A: The solution to the given question is: Vendors CERT organization Public network sources Membership…
Q: SELECT emp_name FROM department WHERE dept_name LIKE ' [A]Computer Science'; In the above-given…
A: I have given answer in next step
Q: Consider the dept name attribute of instructor to the department relation. Give two examples of…
A: - follow the diagram
Q: what are Genetic and evolutionary algorithms ?
A: Below is the answer to above question. I hope this will be helpful for you..
Q: In your own words, explain as a criminology student, why there's a need to know and study about film…
A: The topic of film processing in forensic photography has been debated for years. This is because it…
Q: Which fibre is utilised to protect the inner core and prevent the cable from straining in fiber-…
A: A Fibre optic wire is a similar wire to electrical cable, which is also called as Optical fibre…
Q: Q. 2 (a) When dynamic routing would be preferred over static routing? Refer to the above figure, a…
A: In dynamic routing, routing tables are dynamically updated Use complex algorithms for routing…
Q: Logical data modeling demonstrates how data is arranged and how it connects to other data without…
A: Data models: Data models are those models that serve as the foundation for an organization's project…
Q: Build the following function using only one 4x1 Mux: F(A,B,C,D) = E (0,4,5,6,8,10,12,13,15) NB: Your…
A: Here the number of variable is 4. For 4x1 MUX number of select lines is 2. So the input will be…
Q: What kinds of systems are most suited to agile development?
A: Agile technique is a product advancement strategy that is individuals centered…
Q: The words subnet, prefix, and BGP route should be defined and contrasted with one another.
A: Subnet: A subnetwork, often known as a segmented piece of a more extensive network, is a network…
Q: The following are some of the most major computer hardware advancements that you believe will take…
A: Hardware for computers: Writing letters, sending emails, organizing meetings, and communicating with…
Q: What are the three primary modes of operation for an x86 processor?
A: x86 processor: The x86 processor has a number of fundamental architectural elements, including…
Q: Make a list of two external and two internal impediments to good listening.
A: Justification: Furniture placement, external noise such as traffic or people chatting, physiological…
Q: Convert NFA to DFA start 1 2 3 4 6 7 (a) a b start 1 3 a b a (b)
A: Below is the answer to above question. I hope this will be helpful for you..
Q: What is the difference between authentication and authorisation and how do they differ? What is…
A: Authenticaton: it is the process of providing the security. Authorisation:Authorisation is the…
Q: Define a Rectangle class that also inherits from Quadrilateral, with the following methods:…
A: #Program class Quadrilateral: def __init__(self, side_a, side_b, side_c, side_d):…
Q: Specifically, which memory management strategy is superior and why.
A: Memory Management: The paging approach is widely regarded as the most efficient memory management…
Q: When you declare a value type variable, how much memory does the compiler allocate?
A: Type of value: Variables' actual values are stored in the value type, which is one of the many data…
Q: What are the various datatypes that may be utilised in C?
A: A data type can be defined as a set of values with similar characteristics.
Q: computer Do you have any knowledge of Ada Lovelace's ideas?
A: Ada Lovelace (Ada) Lovelace (Ada) Love Ada Lovelace was a brilliant mathematician, author, and…
Q: Provide me with the MATLAB code to swap the first and last row of the matrix given below, mat = 1111…
A: Answer :
Q: Explain the difference between the asynchronous counter and the synchronous counter.
A: According to the question the asynchronous counter is called as the ripple counter and different…
Q: A new computer display has been gifted to you by your uncle. When you try to connect it, none of the…
A: There are two basic kinds of displays: LED and liquid crystal displays. These displays are fairly…
Q: Examine and explain one noteworthy data or text mining application?
A: Exploration of data Data mining is the practice of identifying patterns in huge data sets using…
Q: Write a function with one argument n, to return the nth row of the Pascal's triangle. For example,…
A: Then formula for xth element in nth row is :
Q: Code an application ClientUI which will instantiate a client object and to carry out the following…
A: Client Class: package bankDemo;public class Client { //instance fields private String…
Q: Recast the following computational problems as decision problems. a. Sorting
A: a. Sorting Sorting is the process of ordering or arranging a given collection of elements in some…
Q: Q2) Consider the regular expression: (ablac)* a. Use Thompson's construction to construct a NFA. b.…
A: The Answer start from step-2.
Q: What are the benefits of utilizing an iPad in the utility department
A: Field service labour is essentially mobile, so the industry's newest tools offer such potential.…
Q: We've already tried comparing 3 numbers to see the largest among all, so let's try a more…
A: Algorithm 0. Start 1. Ask user to enter five integers and store it in variables first integer,…
Q: Based on Binary Search Tree implementation (BinarySearchTree.cpp) we covered last week, extend BST()…
A: Answer in step 2
Q: Mobile privacy and data security is a growing concern.
A: Consumers care about data privacy because a data breach might jeopardize an individual's fundamental…
Q: What exactly is a router?
A: Here in this question we have asked that what exactly is router
Q: This code is for c++ Write the Program for both the .h and the .cpp for the UML diagram Account…
A: Account.h code: #ifndef AccountH #define AccountH #include <iostream> using namespace std;…
Q: results. What is the advantage of combining neural network systems with fuzzy logic control? Discuss…
A:
Q: e step by step
A: I have written code below:
Q: Is Ada Lovelace credited with helping to build current computer technology
A: Ada Lovelace is one of the great computer programmer and mathematics which has helped in building…
Q: What five graphical data properties does data visualization use to convey a story?
A:
Q: When converting a randomly generated array of size m to a heap, what is the temporal complexity?
A: Find the answer with explanation given as below :
1
Step by step
Solved in 2 steps

- What is the number of trailing zeros in base 16 in C(1000, 500)? Explain youranswer.So here VRC will be last row: 01110011 and LRC will be last column- 00000000110001100 or we can write it as:110001100 Follow up Question: What will be the indicate the character that should be given the VRC and LRC above. Thanksn2 is in Omega(log n) true or false?
- How many significant digits are in 7bar (00)?Upvote for correct answer. Thank you. (4) Convert the following numbers from the base shown, to the base requested. (4.1) 38 base 10 = ?? base 2 (4.2) 10100011 base 2 = ?? base 10 (4.3) 15B base 16 = ?? base 10 (4.4) 423 base 5 = ?? base 3Compute the values: D2-2D1, D3-3D2, D4-4D3, D5-5D4, …, D10-10D9, where the D’s are the derangements values described on P.335. What is the pattern?
- The following message arrived protected by the following CRC polynomial. Does the message have an error or not? Why? In the below table, show your work that allowed you to make the determination of whether an error exists in the message or not. Add rows and columns to the below table as necessary. M(x): 11010011100011 CRC-3-GSM: x3 + x + 1 CRC that was in the message: 011 X0 T(x) C(x) RemainderCan you please show the shifts for the encrypt & decrypt in this format? For example, like this : Example:ABCDEFGHIJKLMNOPQRSTUVWXYZ Row 1FGHIJKLMNOPQRSTUVWXYZABCDE Row 2 If the plaintext to encrypt is:THIS IS THE ANSWER The ciphertext becomes:YMNX NX YMJ FSXBJW This is for me to help understand and to redo the problem for studying. Thank you!!One digit in this identification number of apostal money order is smudged. Can you recover thesmudged digit, indicated by a Q?a) Q1223139784
- Don't try to copy others. Send unique answer only.please send answer Q3 for part b iii please send proper answerWhich one of the following is done first, while calculating the median for an ungrouped data in case of odd numbers? a. Divide the data into two equal parts b. Take the average of two middle numbers c. Arrange the data in ascending order d. Calculate N/2

