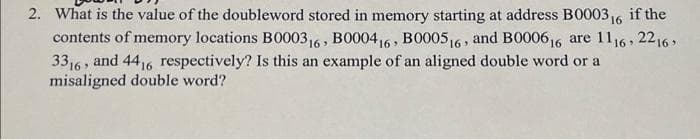
What is the value of the doubleword stored in memory starting at address B000316 if the contents of memory locations B000316, BO00416, BO00516 , and B000616 are 1116, 2216 33,6, and 4416 respectively? Is this an example of an aligned double word or a misaligned double word?
Q: In mobile applications, privacy and data protection are important.
A: In mobile applications, privacy and data protection are important. With any application there is a r...
Q: She conveyed to others in her lifetime a sense of ____ she was ____ made and makes her worth knowing...
A: - We need to select the correct words to fill the spaces. - The first space is talking for the ref...
Q: Describe what a data model is and why it's important in database design?
A: Introduction The question is about data model is and why it's important in database design and here ...
Q: What is the impact of social interaction? Subject human computer interaction
A:
Q: Suppose we are given an array of numbers A[0], A[2], . . . , A[n - 1]. You may assume that n is a mu...
A: The answer is given below:-
Q: SPI and FC are extremely useful ways of transferring data between devices, but the synchronous seria...
A: Disadvantages of synchronous serial communication - The accuracy of the received information relie...
Q: Discuss: If you could create a dashboard that met your personal or business needs, what would you sh...
A: If you could create a dashboard that met your personal or business needs, what would you show?
Q: Create a function print_double_spaced(cs) that takes a C string as an argument and prints the charac...
A: Answer :
Q: dth:160px; height:160px; border:1
A: A simulation creates a model of a real-world situation, allowing us to introduce a variety of condit...
Q: The main idea and purpose of Zachman framework (1-2 sentences) Answer:
A: your question is about main idea and framework of Zachman framweork
Q: 5. Write out an algorithm to find the insertion position from the last position in pseudo- code, bas...
A: Given :- Write out an algorithm to find the insertion position from the last position in pseudo-code...
Q: x = 1002 and fl(x) = 1001. Show the relative error is roughly smaller than the condition number time...
A:
Q: Dihan has completed his bachelor's degree from the University. The University of offers bachelor pro...
A: NOTE: As per guidelines, we are allowed to answer only one independent question per post. Please pos...
Q: What competitive advantages has Vivobarefoot achieved as a result of its infrastructure upgrade?
A: The question is to write the competitive advantages has Vivobarefoot achieved as a result of its inf...
Q: Even if the original data is analog, much of the data storage and communication in recent years has ...
A: To put it simply, a digital signal consists of a series of discrete numbers, It is feasible for a di...
Q: entify the Boolean algebra law or rule that is used in the following statements AB'CD + ABD = DAB'C ...
A: For part a) ab'cd+abd=dab'c+dab As we can see both LHS and RHS are same but inorder to make RHS simi...
Q: What keyboard shortcut is used to close the DevC? Select one: a. Alt+C b. Ctrl+C C. Alt+X d. Alt+F4 ...
A: Answer : d. Alt+F4 is shortcut used to close DevC.
Q: What three functions are defined by network protocols to allow communication between known source an...
A: A Network Protocols is a collection of rules that will define how data transmitted between different...
Q: Please tell me how to distinguish #include and #include? When should I use the first one, and when I...
A: Please find the answer below
Q: Problem 2: Input age and identify the hours lived and hours slept using the formula below. HL - Age ...
A: Given: Goal: Write the program for the problem.
Q: You are reading someone's mind by asking them to chooose a number between 1 and 63. They tell you th...
A: The number that the person may have chosen would be 30
Q: Your program is going to create a searchable contact list. The program should read names and phone n...
A: The answer is given below:-
Q: Design a Turing machine to recognize the language L = {a ^ 2 ^ n | n2 0}
A: Designed a Turing machine for the given language
Q: 1- Given R0, RI, R2, and R3 followed by the indicated base; i- Convert each value into its correspon...
A:
Q: Microprocessor is one of the unsung heroes of the modern era. Discuss the importance of microprocess...
A: - We need to talk about microprocessor and microcontrollers.
Q: 9. Within this document, embed an image of the basic troubleshooting utility in Windows. (Hint: with...
A: Troubleshooting is a systematic process used to locate the cause of a fault in a computer system a...
Q: 1. (a) i. Convert 1610 to 8-bit sign-magnitude. ii. Convert -2410 to 8-bit sign-magnitude. iii. Perf...
A: The answer is given below:-
Q: Determine where the filter is the low pass filter of high pass filter and use the EAYSEDA software s...
A: The answer is given below.
Q: his is what test developers usually do in order to save time and to use as less resources as possibl...
A: Answer 1) cross-validation because it is also used machine learning to test and train data. get ref...
Q: Exercise 4 Take in one number and check if it is even or odd. Then, print out the number and tell me...
A: Given : To write a program to take one number and check if it is even or odd. The program is written...
Q: e system development process, the computer-aid fits and drawbacks of adopting the CASE technie ot to...
A: Lets see the solution.
Q: Why is Reddit more popular than instant messaging? What are the advantages of Reddit?
A: Reddit is a social news site. Despite of a basic interface lots of people are visiting this site on ...
Q: Please help with the bolded functions: I need to implement the following two functions that get a s...
A: Given data, Need to implement the following two functions that get a string and compute an array of ...
Q: May someopne please help me with dbms? a. Primary keys in student and subject tables: b. Composite...
A: Ans a: Primary keys in student and subject tables: Student_Number, Subject_Number Ans b: Composi...
Q: According to Computer Forensics, Certified Computer Examiners (CCE) need to follow the code of ethic...
A: The computer forensics deals with the usage of techniques that can be utilized to generate proof or ...
Q: PLEASE USE JAVA Equivalence Class Software Testing Question: A function foo has k integers a...
A: Given The answer is given below
Q: 1.In what year does the C-language was implemented? Select one: a. 1971 b. 1970 c. 1972 d. none of ...
A:
Q: Write a shell script that will take an input file and remove identical lines (or duplicate lines fro...
A: Answer :
Q: Is the Big Data Market Being Driven by Mass Hysteria? What are the two advantages and disadvantages ...
A: Introduction: This phenomenon is known as mass hysteria, and it is marked by uncontrollable emotion...
Q: What is Enumerated Integer providing an example to illustrate your point?
A: Enumerated Integer specifies a list of labeled integer values.
Q: YOu are given a string ot engih 23.Print the middle 3 characlers il thelengh is od or the middle 2 c...
A: In this question, we are asked to write java program: which return mid 3 characters if length is eve...
Q: Reflection Question: Creating and Editing Documents What is the relationship between legibility and ...
A: The answer is
Q: For the purpose of determining the most efficient path for a message's delivery, a router searches w...
A: The Answer is in step2
Q: models
A: Introduction: The classification or categorizing of knowledge things is known as data types. It offe...
Q: геcurrencе Ice
A: Given :- A recurrence relation as, T(n) = T(n-2) + n^3 is mention in the above given question Nee...
Q: CREATE A GUI PROGRAM FOR THE PURPOSE OF FINDING THE TEMPERATURE OF A BODY USING NEWTON'S COOLING EQU...
A: % % % b(1) = T_a, b(2) = kTfcn = @(b,t,T_0) (T_0 - b(1)).*exp(b(2).*t) + b(1); tv = [ 0; 5; 10];T...
Q: Discuss the differences between using Word in a corporate setting and in an academic setting.
A: Introduction: Word, often known as Microsoft Word, is a popular word-processing tool that is mostly ...
Q: Given two READY processes, one CPU-bound and the other I/O-bound, which process should be given grea...
A: INTRODUCTION: The machine-independent I/O layer is written in the assumption of idealized (virtual) ...
Q: Write a c program where user will enter a string. Then, the program will determine the length of the...
A: Code to determine the length of a string; for example, the string "C program" is 9 characters long (...
Q: HW 3 (due 2/15) draw the graph below with 2 self-intersections
A: Solution: If a feature intersect itself at a point and continue by crossing itself, it is consider...
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Show the content of the individual bytes allocated in memory in hexadecimal for the following declarations. Assuming that the address of I is 404000h, what are the addresses of J, K, and L? What is the total number of allocated bytes?By assuming that X = 3, and 33 is a two digit number, consider memory storage of a 64-bit word stored at memory word 33 in a byte-addressable memory (a) What is the byte address of memory word 33? (b) What are the byte addresses that memory word 33 spans? (c) Draw the number 0xF1234567890ABCDE stored at word 33 in both big endian and little-endian machines. Clearly label the byte address corresponding to each data byte value.Consider the following hexadecimal readout: 000000 8A00 8E00 CFA1 48BF 7900 3202 9015 AD34 000010 0218 6D30 028D 3402 AD35 0288 3102 8D35 000020 0E30 0290 DAEE 3102 4C00 0200 0040 004B Refer to the first byte of memory shown above, address 000000. Assume that this byte is used to store an 8-bit unsigned integer. What is the decimal value stored in this byte? Group of answer choices 138 -27 22,842 66
- By assuming that X is the last digit of your student number and 3X is a two digitnumber, consider memory storage of a 64-bit word stored at memory word 3X ina byte-addressable memory(a) What is the byte address of memory word 3X?(b) What are the byte addresses that memory word 3X spans?(c) Draw the number 0xF1234567890ABCDE stored at word 3X in both big-endianand little-endian machines. Clearly label the byte address corresponding to eachdata byte value.Suppose, 3BD15 H is a particular physical location, and 1234 is the value of the offset.What should be the base address of the segment? Will there be any problems with this base address? Please give your workings and your opinion in this matter. Suppose, you want to design a Microwave and are in need of a processing unit. Would you choose to use a microprocessor or a microcontroller for this purpose? Explain with logic.15. Consider the following Java-like code: int number = <<read number from user>>; int mask = MASK; int result = number OP mask; if (result != 0) { print("Bit 8 was set"); } The above code is supposed to print “Bit 8 was set” if bit 8 of user’s number was set to 1. If bit 8 was not set, then this code should not print anything (result==0). What hexadecimal value should MASK be, and what bit-wise operation should OP be, for the above code to work correctly?
- A CPU that supports little endian format reads two integer (4-byte) values from address 0x1000 and 0x2000. The values read are 55 and 6850 respectively. Please show the memory contents (byte-wise) at address 0x1000 and 0x2000?Q1- Write a program in assembly language for the 8085 microprocessor to send one byte of data located at the memory address (3000H ) using SOD at a baud rate of 1200. Information: The 8085 processor operates at a frequency of 3.072 MHz . When sending the required byte, you must adhere to the following: The two high bits of the start bits(1 1) must be sent, after that the data bits are sent, after that the low bit of the stop bit (0) is sent. The following flowchart will help you. The solution must be integrated and include the calculation of the baudrate delay timeThe contents of memory location B0000, are FF 16, and those at B0001 6 are 0016. What is the data word stored at the address B0000? Is the word aligned or misaligned?
- Given rax = 0x0000000200000100, rbx = 0x0000000000000100, and rcx = 0x0000000000000001,and the following values in memoryaddress -> byte at that address0x0000000000000100 -> 0x010x0000000000000101 -> 0x000x0000000000000102 -> 0x000x0000000000000103 -> 0x000x0000000000000104 -> 0x020x0000000000000105 -> 0x000x0000000000000106 -> 0x000x0000000000000107 -> 0x00what is the new value in %rax after the following operation?subq -0x04(%rbx, %rcx, 4), %raxIf the value 8 is stored in the memory cell corresponding to the address 5, what is the practical difference between writing the value 5 into cell number 6 and copying the contents of cell number 5 into cell number 6?Question/ program give below run on 8086 used to add two 32-bit number. Fill the missing code to store the result immediately in location start with 30042 3000[ 12 4000 [ 12 3004[ 24 3001 [ 11 4001 [ 10 3005 [ 21 3002{ 02 4002 [ 21 3006( 23 3003 01 4003 [C04 3007 05 Mov AX.3000h Fig (1) memory data segment Mov DS, AX Mov AX.4000 MovES, AX Mov SI,0000h Mov DI0000h Mov CX,04h NEXT: Mov AX, [SI] Mov BX, [DI] ADD AX, BX,

