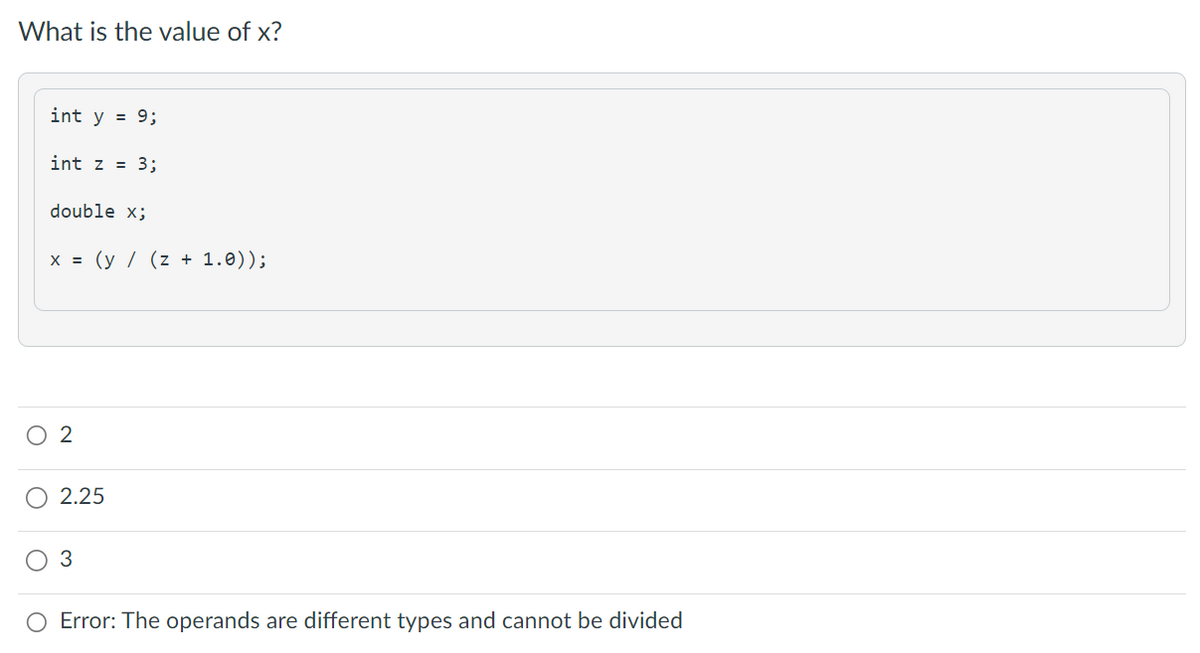
What is the value of x? int y = 9; int z = 3; double x; x = (y / (z + 1.0)); O 2 2.25 3 Error: The operands are different types and cannot be divided
Q: What type of solutions are possible when there are just two possible variables in a preemptive goal…
A: Goal programming is a subset of linear programming in which a set of objectives are supplied in…
Q: INTERFACING SEVEN-SEGMENT DISPLAY needs an introductory section that includes
A: The answer is given in the below step
Q: transparency features that should be included at a bare minimum in a distributed database management…
A: The question asks about the minimum transparency features that should be included in a distributed…
Q: 1. Suppose a knowledge base has the following sentences Sam plays baseball or Paul plays baseball…
A: Given- Sam plays baseball or Paul plays baseballSam plays baseball or Ryan doesn't play baseball We…
Q: 1. Direct Mapped. 2. 2-way set associative. 3. Fully associative You need to fill the table and…
A: Cache mapping: Cache mapping is the process of determining how the main memory addresses are mapped…
Q: Yelp is a successful social networking site. After reading the information presented in this module…
A: In this question we have to understand how Yelp may help in generating revenue? How Yelp can benefit…
Q: What is the role of cryptography in cybersecurity, and how do computer engineers design and…
A: Your answer is given below.
Q: How does ransomware fit into the larger picture of computer security
A: Ransomware is a type of malware that infects a computer system and holds the user's data hostage,…
Q: a.) What does it mean to append data to a file? b.) How do you open a file so that new data will be…
A: We have to explain a.) What does it mean to append data to a file? b.) How do you open a file so…
Q: Can you explain what "memory leaks" are in the context of dynamic memory allocation?
A: Memory that is dynamic: Memory is allotted dynamically at the time of runtime in the technique known…
Q: What is the logic behind an associative cache?
A: The question is asking about the logic behind an associative cache, which is a type of cache memory…
Q: While developing application software, what are some of the situations in which you would argue that…
A: Assembly Language is a low-level programming language, as explained. It makes it easier to translate…
Q: Translate the MIPS codes for "arr [i] = arr[i - 1] + arr[i - 2]" to Machine language code
A: To translate the MIPS code "arr[i] = arr[i-1] + arr[i-2]" to machine language, we first need to…
Q: When it comes to the world of computers, what precisely is the difference between architecture and…
A: In the world of computers, architecture and computer organization are two related but distinct…
Q: What are the most vital factors to think about while creating a presentation? Provide five examples…
A: Introduction: A presentation is a form of communication that involves conveying information or ideas…
Q: Multiprocessor systems have the advantage of being more flexible. This advantage does, however, add…
A: Two-dimensional materials may be less brittle because they are more flexible. Imagine a smartphone…
Q: Outline a few options for seizing control of the meeting. How would one defend themselves from such…
A: Depending on location and vector, attackers may hijack a user's session. Attackers leverage server…
Q: a. Design and implement a method height for BinarySearchTree that returns the height of the tree…
A: A binary search tree (BST) is a data structure that consists of nodes in a hierarchical tree-like…
Q: In the grand scheme of things, what role does MVC play in the creation of online applications? What…
A: MVC (Model-View-Controller) is a design pattern that is commonly used in the development of web…
Q: Define the term "virtual machine" and explain why it is necessary.
A: A virtual machine (VM) is a software emulation of a physical computer that can run its own operating…
Q: What were the main advantages of DDR over the older SDRAM technology?
A: To determine: How did performance-wise DDR outperform SDRAM: In this case, SDRAM is used to refer to…
Q: Take the case of a recent authentication or access control breach that made headlines. If so, what…
A: These models are used to maintain control over security objectives including Confidentiality,…
Q: The following is a list of the most important things that an OS does:
A: Operating System: An Operating System (OS) is a piece of software that serves as a mediator between…
Q: What's the dissimilarity between a top-down and a bottom-up strategy for information security?…
A: According to the information given:- We have to define the dissimilarity between a top-down and a…
Q: Describe the changes between a two- and three-tier application architecture. Which one works best…
A: Introduction: Compare two-tier and three-tier programme design in this query. Distinguishing These…
Q: How does MVC fit into the larger scheme of web app development? Why is it advantageous to use an MVC…
A: Introduction: Model, View, and Controller (MVC) are the three logical components that make up an…
Q: So, users may choose to enter information through the command line rather than the graphical user…
A: Introduction: In the world of computing, users have a choice between entering information through…
Q: The CAP theorem is defined for NoSQL databases. Why can't requirements B and C be met…
A: Distributed System: This network of many nodes duplicates data so that it may be stored in many…
Q: What does "scrubbing" mean in the context of RAID systems, and why is it so crucial?
A: We have to explain What does "scrubbing" mean in the context of RAID systems, and why is it so…
Q: MYSQL 3-Display the last name, job, department number, and department name for all employees work…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!! I…
Q: Outline a few options for seizing control of the meeting. How would one defend themselves from such…
A: Depending on location and vector, attackers may hijack a user's session. Examples of session…
Q: ntext of priority scheduling, please provide a concise explanation of what "process starvation"…
A: A scenario known as "process starvation" occurs when a process is unable to function because other…
Q: In what ways does an operating system have to deal with issues unique to a simultaneous…
A: Answer:
Q: Write a BNF description and a denotational semantics mapping function for the Java do-while…
A: Introduction: The do-while loop is a control structure in Java programming that allows a block of…
Q: Provide an outline of the two-tier and three-tier architectures for applications. Which is…
A: Introduction: two-tier architectures : Multi-level system design. The client component is the lower…
Q: Aim: We will learn how to join tables and how to retrieve data from multiple tables. When data from…
A: The question is related to joining tables in a database using SQL. The aim is to learn how to join…
Q: Given that we generate our tables in Microsoft Access, how do we decide which model to develop?
A: It would be beneficial if you first setup a database. To start, create a new database in Access. All…
Q: Why do we often confuse segmentation and paging? What does it mean to thrash?
A: Thrashing, a state of excessive paging opera, occurs in a virtual storage system. Why is paging…
Q: Some people find cybercrime fascinating. It's not for certain people
A: Cybercrime: Cybercrime refers to criminal activities carried out using the internet or computer…
Q: The term "apriori pruning principle" seems interesting; please elaborate. Provide an example, if you…
A: Provide an explanation of the apriori pruning principle and an example of its application. Answer:…
Q: I need help write this java code, image described below public class AnimalData { private int…
A: Coded using Java.
Q: Think about the significance of wireless networks in developing countries. Why are some companies…
A: Introduction: Wireless networks have become increasingly popular in recent years, not only in…
Q: Please explain what a memristor is and how information is stored in it.
A: Introduction: The memristor, which is the fourth two-terminal circuit component after resistors…
Q: If a Java class called Point is defined as follows public class Point{ //a point in three dimension…
A: A class which defines state placeholders and behavior common to all objects of its kind. Everything…
Q: The use of wireless networks is not without its challenges. Due to safety issues, should wireless…
A: Introduction: Wireless networks have become an integral part of modern communication, and many…
Q: Wireless networks outperform both wired and wireless ones when it comes to throughput speed. Where…
A: Introduction: Wireless networking is used in homes, telecommunications networks, and corporate…
Q: Just what is Blazor, and how does it operate? What makes Razor stand out from other software…
A: Blazor leverages Mono WebAssembly runtime to construct single-page ".Net" apps. Blazor is a mix of…
Q: What parameter must be set when redistributing a route into EIGRP? Many factors, such as the…
A: Introduction: EIGRP (Enhanced Interior Gateway Routing Protocol) is a protocol used for routing data…
Q: What is a "what you see is what you get" (WYSI
A: Introduction: A "what you see is what you get" (WYSIWYG) editor is a type of software that allows…
Q: It is possible for MAC addresses to be used by many interfaces simultaneously. Just why wouldn't you…
A: Introduction: MAC addresses are unique identifiers assigned to network interfaces in computer…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Java Programming: Write a program that reads five integer values from the user, then analyzes them as if they were a hand of cards. When your program runs it might look like this (user input is in orange for clarity): Enter five numeric cards, no face cards. Use 2 - 9. Card 1: 8 Card 2: 7 Card 3: 8 Card 4: 2 Card 5: 9 Pair! (This is a pair, since there are two eights). You are only required to find the hands Pair and Straight.use java : write an application that reads English-Language phrase and encodes it into morse code. also write an application that reads a phrase in morse code and converts it into the English-Language equivalent . Use one blank between each Morse-code letter and three blanks between each Morse-coded word.Write an application that reads an integer value from the user and prints the sum ofall even integers between 2 and the input value, inclusive. Print an error message ifthe input value is less than 2. Use Java. Sample Run Examples: Example 1:the user enters 14Output: Sum: 56Example 2:the user enters 1Output: Error number must be greater than 1
- In a C# Console App do the following Write a method that takes three integers and returns true if their sum is divisible by 3, false otherwise. Write a method that takes two strings and displays the string that has fewer characters. Write a method that takes two bool variables and returns true if they have the same value, false otherwise. Write a method that takes an int and a double and returns their product.cerat javaFX 9-Rock, Paper, Scissors GameCreate a JavaFX application that lets the user play the game of rock, paper, scissors againstthe computer. The program should work as follows.1. When the program begins, a random number in the range of 1 through 3 is generated. If the number is 1, then the computer has chosen rock. If the number is 2, thenthe computer has chosen paper. If the number is 3, then the computer has chosenscissors. (Do not display the computer’s choice yet.)2. The user selects his or her choice of rock, paper, or scissors by clicking a Button. Animage of the user’s choice should be displayed in an ImageView component. (Youwill find rock, paper, and scissors image files in the book’s Student Sample Files.)3. An image of the computer’s choice is displayed.4. A winner is selected according to the following rules:l If one player chooses rock and the other player chooses scissors, then rock wins.(Rock smashes scissors.)l If one player chooses scissors and the other player…Evaluate the following expression static_cast<int> (7.6 + static_cast<double>(17)/3 = a. 12.6 b.13 c. 13.2
- In Java, Write an application that reads a line of text, tokenizes the line using space characters as delimiters and outputs only those words beginning with the letter "b". JavaISP-Java Write a program whose input is two integers, and whose output is the first integer and subsequent increments of 10 as long as the value is less than or equal to the second integer. For coding simplicity, output a space after every integer, including the last. Ex: If the input is: -15 30 the output is: -15 -5 5 15 25 Ex: If the second integer is less than the first as in: 20 5 the output is: Second integer can't be less than the first.1 int[] a = new int[n]; 2 a[0] = 0; a[1] = 1; 3 int x = 0; 4 for (int i = 2; i < n; i++) { 5 x = 3 * (i-1) * (i-1); 6 x += 3 * i - 2; 7 a[i] = a[i-1] + x; 8 } The code can be simplified by replacing lines 5, 6, 7 with a single line of code. Write the single line of code below:
- Code in python only. You are given four integer esteems a, b, c and m. Check if there exists a string that contains: a letters 'A'; b letters 'B'; c letters 'C'; no different letters; precisely m sets of nearby equivalent letters (precisely m such positions I that the I-th letter is equivalent to the (i+1)- th one). Input :The primary line contains a solitary integer t (1≤t≤104) — the number of testcases. Every one of the following t lines contains the portrayal of the testcase — four integers a, b, c and m (1≤a,b,c≤108; 0≤m≤108). Output :For each testcase print "YES" if there exists a string that fulfills every one of the necessities. Print "NO" in case there are no such strings. You might print each letter regardless you need (thus, for instance, the strings yEs, indeed, Yes and YES will all be perceived as sure reply).def get_numbers(): user_input = input() values = [] for token in user_input.split(): values.append(int(token)) return values def print_selected_numbers(): numbers = get_numbers() for number in numbers: if number < 5: print(number) print_selected_numbers() considering the inputs are 3 17 13 1 6 14 what is the outputWhat will be printed on the console? 1. What will be printed on the console char c = '0'; if(c > 90) ; cout << "The value of C is greater than 90\n"); cout << (int) c << endl; cout << static_cast<int> (c) << endl;

