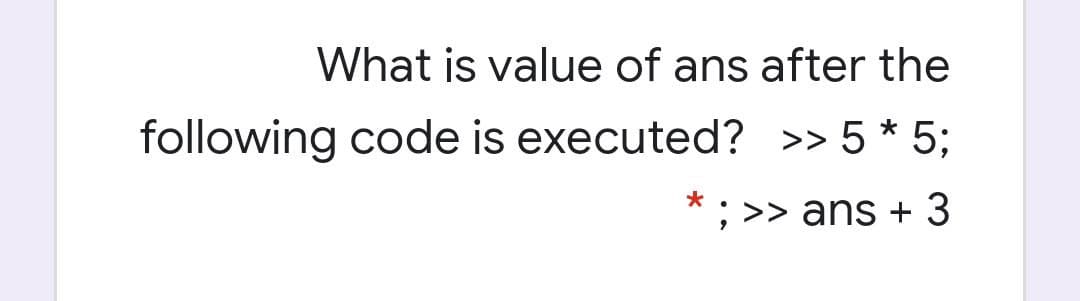
What is value of ans after the following code is executed? >> 5 * 5; ; >> ans +
Q: What are some of the challenges and concerns that arise when users utilise an unintegrated…
A: Answers Loss and failures associated with computers are major computer issues, leading to…
Q: How may artificial intelligence (AI) assist in the alleviation of network congestion
A: Artificial intelligence is regarded as a technological revolution. AI is a term that refers to…
Q: Why have microblogging systems grown in popularity despite the existence of conventional blogging?
A: Conventional: complying or adhering to established norms, as of conduct or taste. related to…
Q: What are the advantages of having a company-wide incident response strategy?
A: The company or organisation must have an incident response plan in place even if a cyber-attack…
Q: Subtract the given number system. Show your solution. 1. 24325- 1345 2. 32547- 2567 3. 27648– 5358 -
A: In number system of base 5, if we want to have a borrow from previous place, you will get 5 added…
Q: In order to determine whether or not a control shows on the form at runtime, what is the control's…
A: Introduction: The Control class is used to create styles that draw attention to important…
Q: The spiral model is one of numerous software process models that has garnered much study but is…
A: Evolutionary software process model: The Spiral model, a risk-based software development process…
Q: Part F 133.58 Do not add any extra 0 after the last significant non-zero digit. N16 = Submit Request…
A: Here, we are going to convert the given numbers in the required number format. Binary number system…
Q: In software development, what are the four most important characteristics? Your opinion on which of…
A: Software Development : A software developer achieves the goal by developing computer code. It also…
Q: in MARIE Architecture, PC has the length of Select one: O a. 14 bits O b. 8 bits O c. 16 bits O d.…
A: Answer: In the MARIE architecture,1 A 12-bit program counter (PC) A 12-bit memory address register…
Q: Suggestions and explanations for TWO (2) methods for ensuring that only authorized individuals have…
A:
Q: Distinguish between Agile and XP system development methods.
A: Agile and XP System: Extreme Programming, like other Agile techniques, involves the client in the…
Q: What is the Internet of Things (loT) and how does it work? How might that be possible? How does this…
A: Internet of Things (IoT): The Internet of Items is a network of physical things or devices that can…
Q: Write Pascal code to print odd numbers between 1 to 100 Print 5 numbers in each line
A: Odd number is the one which is not divisible by 2. So in this program we have to print odd numbers…
Q: Question 1: a) Address translation is an important component in MMU. Let's consider a logical…
A:
Q: What is a stateless linux server?
A: Introduction: A stateless Linux server is a unified server wherein no state exists on the solo…
Q: Consider how reporting systems, data mining systems, and Big Data systems differ. What do they have…
A: mining systems and big data systems: The following are the distinctions between reporting systems,…
Q: What are design patterns and how may they be used successfully in software engineering? Give three…
A: A design pattern is an overall repeatable answer for a regularly happening issue in programming…
Q: There are a slew of problems that arise as a result of having disparate information systems.
A: Disparate Information Systems: Integrated information systems are information systems that combine…
Q: a) Outline the two most basic principles of Lehman's rules of software evolution and discuss the…
A: Principles of Lehman's rule: Initially, Lehman presented three laws expressing three fundamental…
Q: When it comes to IT security, what are the differences between installations in a traditional…
A: Systems are linked in on-premises data center's through a local network. Cloud computing…
Q: explain why it's critical to understand these links when designing network systems
A: Network Influence- The topology of a network is a diagram that depicts the current state of the…
Q: Construct CFG from the following productions of Context Free Grammar (CFG) S - aSbb | abb
A: Context Free Grammar: A grammar contain a context free grammar then it must be a context free…
Q: These five models are all part of the SDLC or software development life cycle (SDLC). Briefly…
A: To design any software, a framework is used to describe the system. This framework is referred to as…
Q: A PHP-based website differs in that it is not based on HTML, CSS, or JavaScript.
A:
Q: How have people's lives been impacted by the evolution of the Internet?
A: Answer:- In today’s world Internet has become one of the most important mediums of communication. It…
Q: What is the definition of data leakage? What happened, and how did it happen? by whom are you…
A: Data is the new oil in this 21st century.
Q: explain why it's critical to understand these links when designing net systems
A: Below why its critical to understand these links when designing network systems
Q: What is computer programming, and how does it work? Before deciding on a programming language, what…
A: Computer Programming: Method of instructing machines on what to do next is computer programming.…
Q: Krushi and Mansi volunteered for the Coldplay concert. Chris Martin loved the crowd which is why he…
A: Input/Output Explanation: In the input the first line of input contains integer N denoting the…
Q: When discussing system notions, what does the phrase "interdependence" imply? How is it different…
A: Interdependence: Interdependence is defined as being mutually reliant or simply dependent on one…
Q: What makes a good disaster recovery plan?
A: Given: As companies use more technology and electronic data, disasters are becoming more common.…
Q: What exactly does the -3 option in the tail command in Linux accomplish
A: Tail command is used to get last n number of data. By default n is 10.
Q: Analyze and discuss some of the good and bad things about the internet. Does it, in your opinion,…
A: Introduction: The internet refers to the interconnection of computer systems or nodes that can…
Q: Construct a Context Free Grammar (CFG) for the regular expression (0+1) *
A:
Q: Explain what is a trojan horse and express if it is a compositing of other malicious malware.…
A: In computing, a trojan horse is a malicious code or program downloaded and installed on a computer…
Q: The following array of integers are to be sorted into ascending order: 4 2 10 8 6 12 If…
A: The program is written in Java. Check the program screenshot for the correct indentation. Please…
Q: information system
A: An information system (IS) is a structured, sociotechnical organisational structure used to gather,…
Q: When it comes to health care, what are the benefits of using the internet? Treatments delivered by…
A: Use of internet has impacted almost all the industries.
Q: Explain the difference and connection between process and multithread, as well as the state,…
A: Lets understand each terms, relationships and differences between them in below step
Q: What are the advantages and disadvantages of using the waterfall methodology over incremental…
A: Introduction: The given challenge is about software development models, and the given models must be…
Q: pologies can b
A: Topology characterizes the design of the organization of how every one of the parts are…
Q: The structure and function of the system aren't the only things Structured English may be used for.
A: Structure Functional: The definition of systems analysis is "the act of assessing a method or…
Q: A list of the six elements of an information system, as well as definitions for each one, should be…
A: Start: An information system (IS) is a system for organizing, storing, collecting, and transmitting…
Q: IT security, what are the differences between installations in a traditional on-premises data center…
A: IT security is the assurance of data and particularly the handling of data. Forestalling the control…
Q: & Moving to the next question prevents changes to this anwer. Question 6 Decrypt the following…
A:
Q: Define page fault and the reasons behind it. In the event of a page fault, what OS steps are…
A: According to the information given:- We have to define page fault and the reasons behind it. In the…
Q: Vhen using vi on Ubuntu, what command pushes the cursor forwa ncidence of the character t on the…
A: Below the command pushes the cursor forward to the first incidence of the character on the current…
Q: What does it mean to speak a language that is problem-oriented?
A: The Answer is in step-2.
Q: When using vi on Ubuntu, what command pushes the cursor forward to the first incidence of the…
A: There are commands available to search for a character or pattern in current line or next line which…
Step by step
Solved in 2 steps

- The operators that cannot be overloaded are__________________________________________________________________________What is error in this codeNeed help with a c++ building block question! Nongraded Implement the copy assignment operator= for the StringVar class using the options given on the right side window. Place the code into the left side using the arrows. It is possible to get the test case correct but not complete NOTE: Be careful! There are decoys! The this pointer is used extensively.. Assume that StringVar.h has the following declaration: #include <iostream> class StringVar {public:StringVar() : max_length(20) { // Default constructor size is 20value = new char[max_length+1];value[0] = '\0';}StringVar(int size); // Takes an int for sizeStringVar(const char cstr[]); // Takes a c-string and copies itStringVar(const StringVar& strObj); // Copy Constructor~StringVar(); // Destructorint size() const { return max_length; } // Access capacityconst char* c_str() const { return value; } // Access valueint length() const { return strlen(value); } // Access lengthStringVar& operator= (const StringVar&…
- Here thr____Calculator.java, to accept an expression as astring in which the operands and operator are separated by zero or more spaces.For example, 3+4 and 3 + 4 are acceptable expressions. Here is a sample run:++PROGRAMMING LANGUAGE: C++ Is it possible to overload the ‘+’ operator for data type int?(Evaluate expression) Modify Listing 20.12, EvaluateExpression.java, to addoperators ^ for exponent and % for remainder. For example, 3 ^ 2 is 9 and 3% 2 is 1. The ^ operator has the highest precedence and the % operator has thesame precedence as the * and / operators. Your program should prompt theuser to enter an expression. Here is a sample run of the program: Enter an expression: (5 * 2 ^ 3 + 2 * 3 % 2) * 4(5 * 2 ^ 3 + 2 * 3 % 2) * 4 = 160 Here is the Listing 20.12 to modify: import java.util.Stack; public class EvaluateExpression { public static void main(String[] args) { // Check number of arguments passed if (args.length != 1) { System.out.println( "Usage: java EvaluateExpression \"expression\""); System.exit(1); } try { System.out.println(evaluateExpression(args[0])); } catch (Exception ex) { System.out.println("Wrong expression: " + args[0]); } } /** Evaluate an expression */ public static int evaluateExpression(String expression) { // Create operandStack to store operands…
- Write code using the in operator that determines whether 'd' is in mystring.in this code, what does 2 mean and what does it do?Please solve usnig c++ programming language. Number Converter Program as described in the UML has the following functionality.1. Read a number from the user and find its base. If number is exceeding the limit of 16-bits,ask user to re-enter the number. Use parameterized constructor Conversion(char *) toinitialize the data member.int FindBase(char []);There are a few assumptions. i) If all digits of a number are 0 or 1, the number is binary. For example, 1010 will beconsidered a Binary number only.ii) A hexa-decimal number must have letter A, B, C, D, E or F. Otherwise the number willnot be considered a hexa-decimal.iii) Decimal number must have minimum one digit greater than 7. Otherwise, the numbercan be considered as Octal if it does not meet the criteria in point no. i and ii.2. Converting the number to Binary if the number is not Binary.char * ToBinary(char *);3. Converting the number to Octal if the number is not Octal.char * ToOctal(char *);4. Converting the number to…
- If the new operator cannot allocate the amount of memory requested, it throws_____________When a function is executing, what happens when the end of the function block isreached?he function drawFractalLine is recursive. Write a script that draws the Koch snowflake. Define a function main that will draw a Koch snowflake with the following parameters when the program is run: Width = 200 Height = 200 Size = 150 Level = 4



