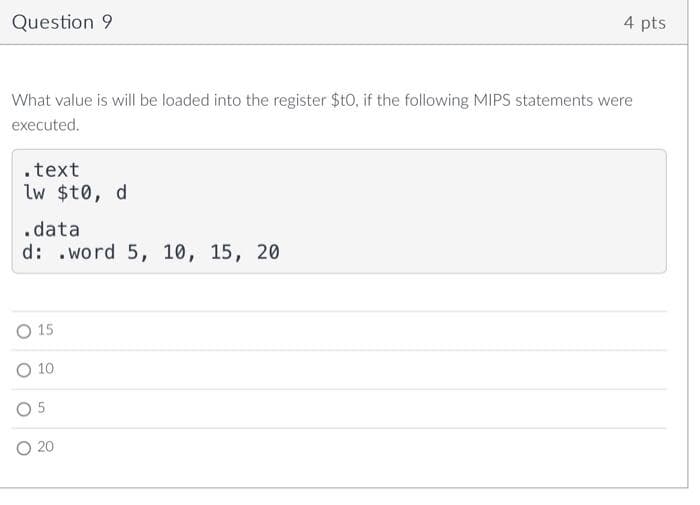
What value is will be loaded into the register $t0, if the following MIPS statements were executed. .text lw $t0, d .data d: .word 5, 10, 15, 20 O 15 O 10 O5 O 20
Q: Find the sop (sum of Poreluet) of this following Expresion. F(6%;2)= Em{ 011, 3,5,6)
A:
Q: Programming Assignment Implement the following pseudocode in x86 assembly language. Use short-circu...
A: Solution:: Let's see the above question is assembly language:: Assembly code: cmp val1, ecx jnb ...
Q: WSNs are a type of communication network. WSNs use sensor nodes to transmit data between each other ...
A: EXPLANATION AND ANSWER: If we talk about wireless sensor networks, small devices called sensor nodes...
Q: 3. Which ISA classified architecture makes the efficie main memory because the complexity (or more c...
A: Answer: The CISC architecture is designed for the efficient use of main memory because, in the CISC,...
Q: What ideas of functions are there in Swift once more? What are some of the aspects of Swift's functi...
A: Functional programming isn't a language or a syntax , however rather a programming paradigm — some w...
Q: Based on the fig below create RDD using sparkContext.parallelize() a) #Create RDD from parallelize P...
A: If you are using scala, get SparkContext object from SparkSession and use sparkContext.parallelize()...
Q: /* spwd.c: a simplified version of pwd * * starts in current directory and recursively * climbs up t...
A: #include <stdio.h>#include <sys/types.h>#include <sys/stat.h>#include <dirent.h...
Q: pervisors across multiple physical servers located in a data center. If the be extended across multi...
A: Lets see the solution.
Q: ite algorithm and draw a flow chart to develop a simple calculator that perform addition, subtractio...
A: Lets see the solution.
Q: Use the def keyword to create a funtion that will say. "Have a nice day!" You can name the function ...
A: We will see the above queries in python using Visual Studio Code : Code: def naming(name): ...
Q: Create a case problem with the application of liner programming distribution models (assignment prob...
A: Task : Formulate the sample LLP problem. Define : 1.Decision variable 2. Objective function 3. Con...
Q: Lesson 9: Database - Java programming 1. Create a database of salesman: a. Table Descripti...
A: As per the requirement created a table When we enter the record in a table at the starting commissio...
Q: Write a program in C++ to manage a bank using class?
A: #include <iostream>using namespace std; // classclass Bank {private: int acno; char name...
Q: 5. What type of language is built up or instructions that requires particular registers for arithmet...
A: The programming languages that are used for creating the discrete statements are the popular program...
Q: 5. One of your group members asks you to review a paragraph he wrote for the Background Information ...
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Below i expl...
Q: A. Write a C program that reads two integers from the user and displays the result of the division o...
A: Introduction: Here we need to write a c program that reads two integers from the user and displays t...
Q: 1. T/F-if (B)=D006000 (PC)=003600 (X)=000090, for the machine instruction Ox032026, the target addre...
A: As per bartlby guidelines, only 3 sub questions can be answered.
Q: Construct a PDA which accepts the set of bit strings with 2/3 as many 0 bits as 1 bits. (For example...
A:
Q: Match the definition to the Windows facility: Allows starting programs and tools with elevated privi...
A: Secondary logon is a service of windows which allows the administrator to run administrative tasks a...
Q: Use the given string and generate the following output. String = 'A BATA BTATB ABTA T' Output1 = [('...
A: Since no programming language is mentioned, I am using python. Algorithm: Start Initialize s='A BAT...
Q: Write a program to store 5 consecutive bytes of data into the data segment. The first data element s...
A: ; multi-segment executable file template. data segmentsource db 0ah,09h,08h,07h,06hdb 11 dup(0)dest ...
Q: What is a collision domain, and how does it work?
A: Introduction: A domain is a collection of computers that can be accessed and directed using a standa...
Q: For what reason is it necessary for the symbol or name used in the C++ inclusion guard on a library ...
A: Introduction : The symbol / name used in the c++ inclusion guard on a library interface file must be...
Q: In the. computer architecture, both data and instructions are saved in same memory. Select one: O a....
A: 1) The Von Neumann is a computer architecture consists of a single, shared memory for programs and d...
Q: A disk stores 512 bytes per sectors, 13 sectors per track, 55 tracks per side and has 2 sides. What ...
A: Given a disk is having 2 sides Each side is having 55 tracks Each track is having 13 sectors Each se...
Q: Edge triggers should be utilized in shift registers for a variety of reasons.
A: Introduction: Shift registers are used to store temporary data. Additionally, shift registers are ut...
Q: What exactly is a database management system (DBMS)? Make a list of the positives and disadvantages.
A: Introduction: A database management system is abbreviated as DBMS. It is a collection of programmes ...
Q: The per-router control plane (also known as the classical network) makes use of destination IP-based...
A: The answer is as follows.
Q: Discuss the five particular instances of fuzzy logic applications in artificial intelligence that ha...
A: Fuzzy logic is employed in a variety of sectors, including automobile systems, household products, e...
Q: When do you think it's best to keep all data and programs on-premises and when do you think it's bet...
A: Yes, your data is quite secure on the cloud—likely far more secure than on your local hard drive.Add...
Q: Tablets, built for consumers, are aggressively disrupting how businesses utilize, access, and find d...
A: KPI software alludes to devices that naturally track key execution pointers continuously and present...
Q: Let f be a function from the set of length 10 binary numbers to the set of subsets of A={1, 2, ...,1...
A: Let f be a function from set A to set B. If f is a one-to-one correspondence( one-to-one, and onto),...
Q: Write a program that reads a string of 5 characters and converts alternating characters to uppercase...
A: Iterate over the given string In even indices change it to upper case and in odd indices change it t...
Q: n Nasm assembly language, how can i create a function to exit a program anytime by a use
A: Utilize the END guidance to end the gathering of a program. You can likewise supply a location in th...
Q: Provide a Flowchart and a Python program (In Python IDLE or PyCharm) that will ask the user to type ...
A: Due to company policies I am compelled to solve only one question and that is the flowchart part. Pl...
Q: What exactly is the Medium Term Scheduler?
A: Introduction: Time scheduling is a collection of techniques used to construct and present schedules ...
Q: When beginning a new project in Word, you'll often want to start with a new blank document. True O F...
A: ->When beginning a new project in Word, you'll often want to start with a new blank document Tru...
Q: 1. Create a simple system
A: given- create a simple system specification for an automated vending machine
Q: When representing the structure of a database, you may use either an E-R diagram or a DBDL. Which st...
A: ER diagrams are used to investigate existing databases in order to identify and resolve logic or dep...
Q: For Intel 8237A Registers: 1- Specify the bits in the Single Mask register to set mask for channel 2...
A: For Intel 8237A Registers: 2) MASK REGISTER : 1)The mask is clear or sets all of the masks with one ...
Q: List four different types of external disk interfaces.
A: INTRODUCTION: Here we need to answer the four different types of external disk interfaces.
Q: There are two parts to this assignment. Part 1) Submit the three function prototypes (ReadInputRecor...
A: A function contains a block of code which performs a specific task. A function prototype is declarat...
Q: Write a line of Python code to randomly select 4 items from the list menuitems and assign it to the ...
A: Python is the coding language and is the object-oriented requirement as the dynamic, code strong and...
Q: Slot Machine Simulation A slot machine is a gambling device that the user inserts money into and the...
A: Solution :: Let's see the above question in Java programming language.. Code ::
Q: Reference link: https://www.healthit.gov/providers - professional /faqs/what - does - http-web - ad...
A: HTTP and Web Address - HTTP stands for hypertext transfer protocol which means that it provides comm...
Q: cessing syst
A: given - what is ict to functions of information processing system?
Q: 2. What is the bandwidth of a signal that can be decomposed into five sine waves with frequencies at...
A: The answer for the given question is as follows.
Q: do a Geomtric class have Circle + rectangle data and method then use inhertance for other class one...
A: do a Geometric class have Circle + rectangle data and method then use inheritance for other class on...
Q: Q-1. What is at put gf thie logic gatu? F=?
A: AND gate: OR gate:
Q: Discuss the different number representatio
A: Lets see the solution.
Step by step
Solved in 2 steps with 1 images

- Given two numbers: s0=1001 0101 0011 1101s1=1101 0101 0101 1111 a) What numbers do the following two numbers represent when they are and’ed and or’ed together? b) Given the following code and register values, what are the final values of the registers s0 and s1?Question 13 sum.mov AL,7ah mov BL,AL and AL,0fh and bl,0f0h What will be the values of AL and BL registers when the above program runs and terminates? Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineIn the following code segment, f, g, h, i, and j are variables. If the five variables f through j correspond to the five registers X19 through X23, what is the compiled LEGv8 code for this C if statement? if (i > j) f = g + h; else f = g − h;
- Please write essential MIPS statements to read a number including a prompt , save it to RAM, load it from RAM to a register.From the given code from step 1-step19 a- What are the memory location addresses that will be accessed in memory data segment in this program? b- What is the content of each memory location accessed in memory data segment in this program? c- What does the content of each memory location refer to?Write a program to set b0,b1, reset b2,b3 and complement b6,b7 for the content of memory location [2800], store the result in [2801]. Note ([2800]= (6C)] The solution thats on this website is incorrect and would like another one
- Question 4 Which of the following SystemVerilog statements takes, as input, an unsigned 8-bit value and multiplies it by 3? a. b = {a,1'b0} + {1'b0,a}; b. b = {1'b0,b} + {1'b0,b}; c. b = {a,1'b0} + {a,1'b0}; d. b = {1'b0,a} + {1'b0,a}; Full explain this question and text typing work onlyC codes on the following Read and Write? Read a byte (into TMP, where TMP is at GPR address = 0X60)) from GPR at address 0X1C3 (Bank 3)Variable A contains the value 0x01. What will be the content of the Z status bit after execution of the following instruction? movf A, W Z = [?]
- Q2) (a) For the expression given ( An + B’n ) * ( C’n + Dn ) , you should write Zero-Address instructions to compute the same expression? Also mention what type of computer organization will use these instructions.need a new java .asm file and fill it with all of the required directives. Next, write a program that does the following: Create two variables with any names and initial values. One must be type "DWORD" and the other must be type "SBYTE". Set the value of the EAX and EBX registers to any numbers of your choice. Add EAX to your DWORD variable. The result should remain in the variable (not the register). Add EBX to your DWORD variable. The result should remain in the variable. Set the value of the CL register to any number of your choice (since it is only byte sized the upper limit for the number is 255) Subtract the CL register from your SBYTE variable three times. The result should remain in the variable. You can debug your program to verify that the arithmetic is performed correctly.The below program is: A MIPS program that executes the statement: s = (a + b) – (c + 101), where a, b, and c are user provided integer inputs, and s is computed and printed as an output. .data askA: .asciiz "Enter value of a: " askB: .asciiz "Enter value of b: " askC: .asciiz "Enter value of c: " msgS: .asciiz "Result s: ".text # Prompt user to enter value of a li $v0, 4 la $a0, askA syscall # Get user input li $v0, 5 syscall #store the result in t0 move $t0, $v0 # Prompt user to enter value of b li $v0, 4 la $a0, askB syscall # Get user input li $v0, 5 syscall #store the result in t1 move $t1, $v0 add $t2, $t0, $t1 # Prompt user to enter value of c li $v0, 4 la $a0, askC syscall # Get user input li $v0, 5 syscall #store the result in t0 move $t0, $v0 add $t1,$t0,101 sub $t0,$t2,$t1 li $v0, 4 la $a0, msgS syscall #print or show the age li $v0, 1 move $a0, $t0 syscall My question is, I want to…

