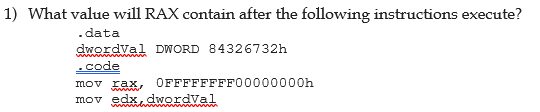
What value will RAX contain after the following instructions execute? .data dwordVal DWORD 84326732h w .code mov xax, OFFFFFFFF00000000h mov edx, dwordval
Q: What is the definition of "network topology"? Various network topologies must be recognized and…
A: Introduction: The physical or logical arrangement of nodes and links makes up the network's…
Q: In terms of authentication, define what a challenge–response system is. How does it give a higher…
A: Introduction : Authentication is the process of identifying users that request access to a…
Q: Do you mind providing a comprehensive breakdown of the database's file structure?
A: File formats are used to hold communal knowledge and data. A file is a collection of records…
Q: For each invoice placed on November 15, 2021, list the invoice number along with the ID, first name,…
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful.…
Q: Photographs are maintained in databases and the design/structure we've picked contains some highly…
A: Databases and the Design/structure Similar to a spreadsheet, relevant data is organized into tables…
Q: How can the 'Event Table' be evaluated to confirm that the design is accurate?
A: Encryption: There are two distinct approaches that are used to evaluate the event table in order to…
Q: What is a computer language called Data Definition Language? Give me an example of what you're…
A: Definition of Data in Language: Data Definition Language refers to the SQL commands that create and…
Q: Is it possible to draw a line of demarcation between the Internet and the World Wide Web (WWW)?
A: Introduction: The Internet is a worldwide network of interconnected computers. It isn't necessary…
Q: Is there an appropriate definition for the idea of "privacy"? Create a list of the top five things…
A: Confidentiality of information: Concerning the Privacy of Information and the Methods Used to…
Q: idea of privacy in relation to information security is one that is tough to get one's head around
A: Answer:
Q: How does multifactor authentication work? When it comes to preventing password theft, what function…
A: Authentication is the process of determining if a person or thing is who or what they claim to be…
Q: Take into account the following: Do you agree that it is ethical for producers of mobile apps to…
A: Yes, a growing number of available apps now request some of your most basic personal information,…
Q: We'll go through the most pressing issues with your company's information system, as well as the…
A: Given: Managing an information needs corporation, on the other hand, comprises managing information…
Q: 2. Given the definition of the array. Give reason why definition is not correct. a) float points…
A: The complete answer is discussed below with an explanation why each of the above statements are…
Q: To what extent may binary search trees' pre-order traversal be used to its utmost extent?
A: Introduction: To begin with, the binary tree's root node is traversed using the preorder traversal…
Q: Write an assembly language program to find the square and cube of a number. Users can enter a…
A: Here is the assembly code for your problem, Kindly check the spaces and intendations.
Q: Authentication's purpose Compare authentication techniques' pros and cons.
A: Authentication serves the following purposes: A server will employ authentication to detect who is…
Q: Draw the state diagram of the machine that performs the following operation: The machine turns on…
A: State machine diagram which is also known state chart or state transition diagram shows the…
Q: How does one go about using multifactor authentication? What are the benefits of maintaining the…
A: Multifactor Authentication: MFA is an authentication mechanism that requires a user to give two or…
Q: Draw the graph U(5,3,0).
A: Let's see what are we given in the question. U(n, k, i) where the graph has the vertex set of…
Q: Is a 16-bit register containing address
A: Solution - In the given question, we have to select the correct answer.
Q: While developing software system models, how should different views be taken into consideration?
A: let us see the answer:- Introduction:- The practice of creating abstract models of a system, each of…
Q: Scripts and stored procedures vary in the following ways: What's the point of each of these? Are…
A: stored procedures used over other techniques in a database so what are the reasons behind using…
Q: dentify and discuss the contributions of the first two key players in the development of the…
A: The approach of new data and correspondence innovations has deciphered the worldwide town idea of…
Q: Besides HTML, CSS, and JavaScript, what separates PHP-powered websites from those constructed using…
A: JavaScript: Cascading Style Sheets (CSS) is utilised in the process of developing websites in order…
Q: Using a file system-based website rather than an HTTP-based website has what advantages over the…
A: Start: Both the File System website and the HTTP(Hyper Text transfer protocol) website are used for…
Q: Provide an overview of the essential ideas behind the development of data input fields. Are there…
A: Fundamental concepts: A notion is a mental classification system for the universe. The hierarchical…
Q: Investigate people's reactions to the computer and mobile application problems they've experienced…
A: Computer and Mobile application problems: People react unfavorably to software flaws that have not…
Q: Solve the system by using linsolve in Matlab -x-5y+6z=-24
A: here in given question solve the equation using linsolve in matlab.
Q: Would it be possible for you to supply me with a more in-depth look at the metrics that were used…
A: "Software measure" refers to a percentage of quantifiable or countable programming attributes. The…
Q: 5. Identify which of the following array declaration are invalid. If a declaration is…
A: According to C programming language, written valid and invalid statements.
Q: Instead of an HTTP-based webpage, why use a file system?
A: File system site and HTTP(Hyper Text transfer protocol) site both are utilized for correspondence or…
Q: What do you think of a detailed explanation of the file system used by the database
A: Please find the answer below :
Q: wo early internet pioneers should be mentioned and explained.
A: The initial idea of the Internet was mooted by Leonard Kleinrock in his first paper entitled…
Q: B3 Order Tree Proceed insertion on that tree above with these data: E,I,L,G,X and deletion after…
A: According to the information given:- We have to follow the instruction to proceed insertion and…
Q: Q3. You are given an one dimensional array. Write an algorithm that finds the smallest element in…
A: We need to write an algorithm to find the smallest number in an array.
Q: Examine the differences between groups and roles in the context of the computer security access…
A: Answer: A group is an assortment of clients with a given arrangement of consents relegated to the…
Q: Write an algorithm that defines a two-dimensional array.
A: Algorithm for two dimensional array: 1. type Matrix is array(1..3, 1..3) of Integer;…
Q: What do you think of a detailed explanation of the file system used by the database?
A: According to the information given:- We have to define the file system used by the database.
Q: Capability to describe and operate with basic databases utilising database software.
A: The principle of using database management systems in business was initially introduced many years…
Q: Describe your solution to deploying the Mobile IP solution at ten machines on the current IPv4…
A:
Q: HOW CAN ORGANIZATIONS MAKE THE MOST OF THE OPPORTUNITY PRESENTED BY ARTIFICIAL INTELLIGENCE TO DRIVE…
A: Artificial intelligence is defined as the intelligence that is demonstrated by machines. It is also…
Q: What exactly do you mean when you talk about the goals of the authentication process? Analyze how…
A: Authentication refers to the procedure of confirming a user's identity. This approach associates…
Q: rams might be conceptual or actual. What's the difference?
A: Data Flow diagram: A data flow diagram is a visual representation of data flowing in a system or…
Q: Internet search engines have legal and ethical ramifications that need to be considered.
A: The legal and ethical ramifications of using search engines on the internet are debated in this…
Q: How should different points of view be considered when creating software system models
A: Please find the detailed answer in the following steps.
Q: Q2. Write an algorithm that defines a two-dimensional array.
A: The two dimensional array is represented in the form of rows and columns, also known as matrix. It…
Q: Imagine you have a spare desktop computer at home that you want to use as a general-purpose computer…
A: I will explain it in details,
Q: Do you feel that a company should be able to avoid criminal culpability for the actions of its…
A: Introduction: Employees frequently follow a corporate instruction, a goal, a policy, or other…
Q: Discuss the importance of data privacy and the many means through which it may be safeguarded.
A: Data privacy, which is sometimes also referred to as information privacy, is a subfield of data…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- What value will RAX contain after the following instructions execute in hexadecimal?.datadwordVal DWORD 11111111h.codemov rax,FFFFFFFF00000000hmov eax,dwordValWhat value will EAX contain after the following instructions execute?.datadVal DWORD 12345678h.codemov ax,3mov WORD PTR dVal+2,axmov eax,dValWhat will be the value of BX after the following instructions execute?mov bx,91BAhand bx,92h
- What will be the value of RBX after the following instructions execute?mov rbx,0AFAF649Bhxor rbx,0FFFFFFFFhSomeone has modified the utils.asm file to insert a PrintTab subprogram immediatelyafter the PrintNewLine subprogram as shown below (changes are highlighted in yellow).The programmer complains that the PrintTab command cannot be called using the "jalPrintTab" instruction. What is wrong, and how can this be fixed? Explain all theproblems in the code this programmer has written.# subprogram: PrintNewLine# author: Charles Kann# purpose: to output a new line to the user console# input: None# output: None# side effects: A new line character is printed to the# user's console.textPrintNewLine: li $v0, 4 la $a0, __PNL_newline syscall jr $raSomeone has modified the utils.asm file to insert a PrintTab subprogram immediatelyafter the PrintNewLine subprogram as shown below (changes are highlighted in yellow).The programmer complains that the PrintTab command cannot be called using the "jalPrintTab" instruction. What is wrong, and how can this be fixed? Explain all theproblems in the code this programmer has written.# subprogram: PrintNewLine# author: Charles Kann# purpose: to output a new line to the user console# input: None# output: None# side effects: A new line character is printed to the# user's console.textPrintNewLine: li $v0, 4 la $a0, __PNL_newline syscall jr $ra .data __PNL_newline: .asciiz "\n"PrintTab: li $v0, 4 la $a0, tab syscall jr $ra.data tab: .asciiz "\t"
- What will be the contents of DX after the following instructions execute (STC sets theCarry flag)?mov dx,5stc ; set Carry flagmov ax,10hadc dx,ax14) Enter the following two instructions in MARS, and assemble them. What differences do younotice? Are the results the same? Will one run faster than the other? Explain what youobserve.addiu $t0, $zero, 60000ori $t0, $zero, 6000015) Write a program to retrieve two numbers from a user, and swap those number using only theXOR operation. You should not use a temporary variable to store the numbers whileswapping them. Your program should include a proper and useful prompt for input, andprint the results in a meaningful mannerInput This program will create a date in the Microsoft Disk Operating System File Allocation Table (DOS FAT) date format. You should write a sequence of instructions which receives three variables in registers as input: M - a month between 1 and 12 (in register 1) D - a day between 1 and 31 (in register 2) Y - a four-digit year value between 1980 and 2127 inclusive (in register 3) Processing: You must start by validating that these values are all within the appropriate ranges (1-12, 1-31, 1980-2127). If not, place a value of minus one in register 0 and end the program. Then use shift and bitwise instructions to create a Microsoft DOS FAT file system date. This has the format: Year in bits 15..09 Month in bits 08..05 Day in bits 04..00 This is a 16-bit number. The upper bits (31..16) should be set to zero. Output: Output shall be placed in register zero. If any of the parameters are invalid, place a value of minus one in register 0. Grading: Correct output values for selected…
- The starter file: def main():# Add code that reads the file n_pets.txt,# computes the total number of pets,# the average #, the minimum #, and the maximum ## and displays those numbers as specified in the instructions.main() The data file: 24632341355114422Write an ARM assembly program to convert temperatures from Celsius to Fahrenheit orfrom Fahrenheit to Celsius. Here are the two formulas for your reference. Use variable toread and store values, you can initialize any integer value into the variables (Do not expectdecimal results we are only doing integer operations).C = 5 × (F − 32) / 9F = (9 × C / 5) + 32Name the file TempConvert.s add the below commenting statements in the program;Name:;Date:;Give which expression you use Please don't copy and paste the old answer.Write an ARM assembly program to convert temperatures from Celsius to Fahrenheit orfrom Fahrenheit to Celsius. Here are the two formulas for your reference. Use variable toread and store values, you can initialize any integer value into the variables (Do not expectdecimal results we are only doing integer operations).C = 5 × (F − 32) / 9F = (9 × C / 5) + 32Name the file TempConvert.s add the below commenting statements in the program;Name:;Date:;Give which expression you use



