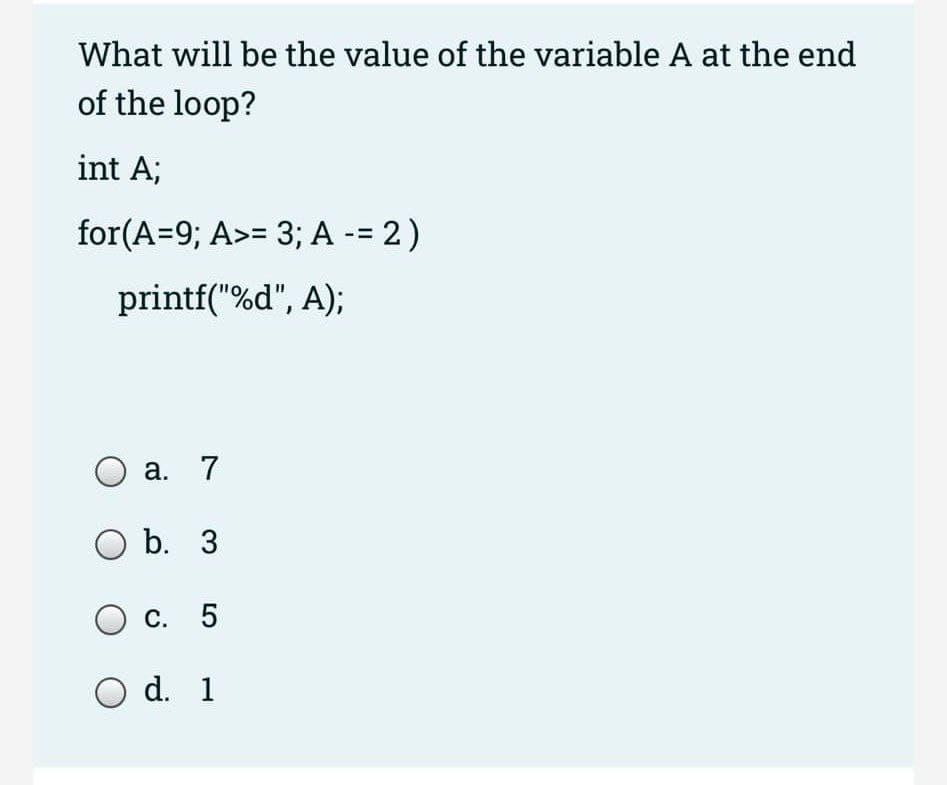
What will be the value of the variable A at the end of the loop? int A; for(A=9; A>= 3; A -= 2) printf("%d", A); а. 7 O b. 3 с. 5 O d. 1
Q: i The medel belew caleulates eral utputs frem the gen inguts. (Thi madeled in all ef the rcies in…
A: As per our guidelines, we are supposed to answer only one question. Kindly repost the remaining…
Q: Consider improving student satisfaction with the course enrolling process at your own university or…
A: I graduated from the 'WBTU state university. The institution provides online registration for…
Q: What happens to the data in a buffer when it is not being used?
A: Data buffer: A data buffer (or simply buffer) is a memory space used to temporarily hold data while…
Q: Show the Huffman code for each character in the table below. Symbol Frequency e 40 30 20 10
A: I have prepared code in C++ as follows: Please appreciate and upvote: NOTE: HUFFMAN CODING is…
Q: AVL Tree Implementation program Important note: You must separate your program into three files:…
A: cpp code: #include<iostream> #include<cstdio> #include<sstream>…
Q: Explain distributed architectural patterns and weigh in on their benefits and drawbacks.
A: Distributed architecture patterns: Distributed architecture patterns are made up of various pieces…
Q: QUESTION 3 create a 2 tape Turing machine that has on tape 1 the alphabet of a,b,null, on tape 2 the…
A: Please find the Answer below in second step:-
Q: What are the various sorts of computer languages that are currently available to us? In a few words,…
A: Please appreciate and Upvote, Thank you. A computer programming language is any of several languages…
Q: How do we close the window by adding a condition if escape key is entered then close the window. i…
A: If you set the Form's 'KeyPreview Property to 'true, then it handles a Key Event before any of the…
Q: In your own words, explain as a criminology student, why there's a need to know and study about film…
A: The topic of film processing in forensic photography has been debated for years. This is because it…
Q: Was the mechanical computer introduced to the globe for the first time around this time?
A: Mechanical Computer: This computer is commonly considered as the precursor to the modern computer,…
Q: Create and implement a function given using a multiplexer and decoder. f=ПM(1,3,4,7)
A: We need to implement a function given using a multiplexer and decoder. f=ПM(1,3,4,7)
Q: If you don't give a seed value to a Random object, what value does it use?
A: If you don't give a seed value to a Random object, what value does it use?
Q: Q1. Write the Characteristics and Operations of Mode 0.
A: The internal machine cycles are counted in the timer mode. As a result, every machine cycle, this…
Q: Encode the number using the given public key. Encode the number M = 14 using the public keyn= 77 and…
A: Here, we are going to find out the encoded number using RSA cryptosystem. Using RSA; Encoded number=…
Q: What are the three primary modes of operation for an x86 processor?
A: x86 processor: The x86 processor has a number of fundamental architectural elements, including…
Q: Why do you need database in an application and why do we need to communicate? Show the process of…
A: Various needs of database in an application are: Oversees a lot of informationA data set stores and…
Q: How can reference parameters be used to communicate between methods?
A: Given: A reference parameter is a reference to a variable's memory location that is sent as a…
Q: Assume you want to use parallel arcs to solve a maximum flow problem, but you don't have a maximum…
A: The Maximum Flow Issue: A maximum flow issue involves determining a viable flow across a leading…
Q: Formulate the overall reliability of LCD display unit that consist of a display, backlighting panel…
A:
Q: Which of the following IoT properties is not one of them
A: The Internet of Things (IoT) is a term that refers to a network of connected devices. The Internet…
Q: Deeply and briefly explain about intel AI for youth?
A: Artificial intelligence can be defined in a variety of ways, owing to the difficulty of defining…
Q: What does dynamic memory entail, and how does it differ from regular memory?
A: Computer Memory: Memories are used to store information on computers, and in computer science, they…
Q: Which fibre is utilised to protect the inner core and prevent the cable from straining in fiber-…
A: The explanation is as follows.
Q: The size of the main memory in a computer system is 16 megabytes (MB), where each byte is directly…
A: The question is to choose correct option from the given four options.
Q: Q2) Consider the regular expression: (ablac)* a. Use Thompson's construction to construct a NFA.
A: The Answer of (a) is in step-2.
Q: We'll say that a String is ab-balanced if for all the 'a' chars in the string, there exists a 'b'…
A: - We have to create an ab balanced string program. - We are using Java here.
Q: Please describe how Stack and Heap are utilized. Could you provide more information about the stack…
A: Foundation: When comparing stack memory with heap memory, the main distinction is that the stack is…
Q: Examine the information stored on your computer. Is there any personal information on your computer?…
A: introduction: Hackers have been known to use stolen information to perform a range of crimes. Using…
Q: True or False Topic: Visual Basic a. Each array element has a unique subscript (or index) assigned…
A: Each array element has a unique subscript (or index) assigned to it. indexing assignment begins at…
Q: What are whole disc encryption (WDE) solutions, and when should you use them?
A: Definition Whole Disk Encryption (WDE) solutions play the foremost role in…
Q: The words subnet, prefix, and BGP route should be defined and contrasted with one another.
A: Subnet: A subnetwork, often known as a segmented piece of a more extensive network, is a network…
Q: what is IaaS? what are the advantages and disadvantages of IaaS?
A: Infrastructure as a Service- IaaS is a cloud infrastructure service. The internet is used to…
Q: Recall a frequent usage of an information system, such as online banking, payroll, or airline…
A: Banking system accessible through the Internet The primary objective of an online banking system is…
Q: why do device dvivs heed -lo be nstalted whin the bros alveody has Code to connect with the…
A: The flaws of traditional x86 BIOSThe BIOS contains just the code needed to communicate with a subset…
Q: Suppose that you have formatted your disk with a block size of 1024 bytes and assume that we have…
A: The Answer start from step-2.
Q: Using the picture, use Java to design and implement the class PascalTriangle that will generate a…
A: Algorithm: for (initialExpression; testExpression; updateExpression){ // body of the…
Q: Decode the number using the given private key. Decode the number M = 15 using the private key d = 53…
A: We are given, Private key d = 53 n = 77 And message M = 15 Let the decoded number be x. In RSA…
Q: What exactly is system image recovery, and how does it work?
A: Start: An whole image file of Windows 10 or Windows 11 is created rather than simply a selection of…
Q: Create an ordered, rooted tree that represents the infix form of the following equation. Then write…
A:
Q: You've been given the task of setting up a LAN for your office after completing this course. Which…
A: A LAN is a local area network which is a network of few computers and devices located within a…
Q: Assume a program requires the execution of 75 x106 FP instructions, 112 x106 INT instructions, 88…
A: Time taken for n instructions of a common type= n*CPI/(clock rate) (a) Let the new CPI for FP…
Q: What considerations may prevent a transaction processing system from scaling linearly? Which of the…
A: Nothing Architectures: A shared-nothing architecture (SN) is a distributed computing architecture in…
Q: Is it really necessary to provide data into a function using a formal parameter when you could just…
A: Formal parameters are the parameters that are mentioned when writing a function and when a function…
Q: Like a kite and a spool of string, how is the relationship between an object and a reference…
A: The primary distinction between an object and a reference is that an object is a subclass of a class…
Q: Which of the following SQL statements displays the all unique job ids from the WORKERS table? A.…
A: A) SELECT job_id FROM WORKERS; This SQL query selects the table's specific columns. This statement…
Q: There are advantages and disadvantages to wireless networking to consider. Should wireless…
A: Wireless networking : Wireless networking cannot be used as the primary transmission source in the…
Q: For simplicity, let us assume that each instruction on a RISC processor is executed in 2…
A: Introduction: Interrupt handling in a RISC processor: Interrupts are a technique for preventing the…
Q: The term "LAN" stands for "local area network."
A: A local area network (LAN) is a connected environment covering one or more buildings – typically…
Q: help asap pls for number 5 less than 30 mins i'll give you an upvote when i'm back later
A: The statement "5 less than 30 ". It is way of writing a mathematical expression in statement form.…
Step by step
Solved in 2 steps with 2 images

- Below is a nested loop containing an assignment statement. How many times will the assignment statement (z = z + 1) execute up to big theta? int z; for (int x = 1; x <= n; x++) { for (int y = 1; y <= floor(i / 3); y++) { z = z + 1; } }At a coffee shop , a coffee cost $1. Each coffee you purchase, earns one star. Seven stars earns a free coffee. In turn, that free coffee earns another star. Ask the user how many dollars they will spend, then output the number of coffees that will be given and output the number of stars remaining. Use A loop. Please Write the code in Java and use the test case examples as reference.What is the output of the following (when embedded in a complete program)? int n = 5; while (--n > 0) { if (n ==2) break; cout<<n<<””; } cout<<”End of Loop.”;
- 1. a)What is the value of num when the following code snippet runs successfully? int num = 100; if (num < 100) { if (num < 50) { num -= 5; } else { num -= 10; } } else { if (num > 150) { num += 5; } else { num += 10; } }Convert the following code into descriptive code, and verify using White Box Testing. a = 2 b = 10 c = a * b for( i = a, i < b, i = i+a) result = a + i if ( result % 2 == 0) print (“Even”) else print (“Odd”) end-if end-for **************************************** I want a solution like this photoInput a value for the variable y so that the variable x becomes 4 after the code executes. favorite_numbers = y favorite_numbers.remove(-1) x = len(favorite_numbers)
- At a coffee shop , a coffee cost $1. Each coffee you purchase, earns one star. Seven stars earns a free coffee. In turn, that free coffee earns another star. Ask the user how many dollars they will spend, then output the number of coffees that will be given and output the number of stars remaining. Use A loop. Please Write in Java and use the test case examples as reference.What is the output of the following code? int num = 12;while (num >= 0){if (num % 5 == 0)break;cout << num << " ";num = num - 2;}cout << endl;What is the value inside the "value" variable at the end of the given code snippet? int main() { int value = 3; value = value – 2 * value; value++; return 0; } a) –2 b) 0 c) 2 d) 4
- stoppingDistance = speed * (2.25 + speed / 21)Write a program which determines whether a vehicle’s tailgating distance is safe.The program should read in the speed of the vehicle and the vehicle’s tailgatingdistance. The program should then calculate the distance that would be required tostop the vehicle.If the stopping distance is less than the tailgating distance, your programshould print “No problem.” If the stopping distance equals the tailgatingdistance, your program should print “Minor wreck.” If the stopping distanceis greater than the tailgating distance, your program should print “Majorwreck!”stoppingDistance = speed * (2.25 + speed / 21)Write a program which determines whether a vehicle’s tailgating distance is safe.The program should read in the speed of the vehicle and the vehicle’s tailgatingdistance. The program should then calculate the distance that would be required tostop the vehicle.If the stopping distance is less than the tailgating distance, your programshould print “No problem.” If the stopping distance equals the tailgatingdistance, your program should print “Minor wreck.” If the stopping distanceis greater than the tailgating distance, your program should print “Majorwreck!”Notice that the expression on the right side of the formula above will force thecompiler to convert everything to type double. Use type double for your workingvariables. Write your program so that it is able to produce the following screendisplay:Sample session:Enter your speed (in mph): 60.0Enter your tailgate distance (in feet): 240.0Major wreck!Please use loop and add comment on each line. Thank you Write down a method named: hasTwoConsecutiveLetters() in Java, to check if the input (argument) string has two consecutive occurrences of the same letter (alphabetic characters). The method should be case insensitive. Write a test program that prompts user to input a string and invokes this method. Here is the sample run. Example: Enter an input string: aabcded Output: The input string aabcded has two consecutive same letters Enter an input string: ababab Output: The input string ababab has no two consecutive same letters Enter an input string: abbbabab Output: The input string abbbabab has no two consecutive same letters [Note: In the case above we will not consider bbb as there are three consecutive b’s, we only need to find instances where there are only two consecutive letters]





