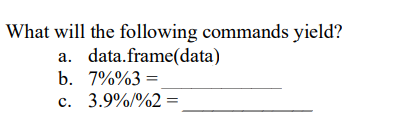
What will the following commands yield? a. data.frame(data) b. 7%%3= c. 3.9%/%2 =
Q: Assume you have a sorted list of 100 pre-sorted elements and a recursive implementation of…
A: The answer for the above given question is given below:
Q: What does the term "lazy evaluation" mean? What are promises exactly? What does the word…
A: Lazy Evaluation:- Lazy evaluation, also known as call-by-need analysis, is a technique used in the…
Q: What time management method is not a preemptive algorithm? Why is this happening, exactly? Round…
A: Introduction The issue at hand is the scheduling technique used in processing, in which the…
Q: If all of the RadioButton controls are in the same GroupBox, how many of them may be chosen…
A: Given: Controls for "RadioButton" may be found in "GroupBox.""RadioButton" controls are utilised…
Q: What distinguishes traditional deterministic programming from probabilistic dynamic programming?
A: Introduction In this question, we are asked to distinguish traditional deterministic programming…
Q: What benefits do enumeration types provide over a collection of named constants? What benefits does…
A: Enumeration Enumeratiоn types are data types that the user has specified. It enables the addition of…
Q: What is the Manhattan distance between different points as shown below? Fill the table with…
A: Manhattan distances The separation of two points determined along right-angled axes. It is |x1 - x2|…
Q: Why is it OK for a function to sometimes produce side effects?
A: A function or expression in computer science is said to have a side effect if, in addition to…
Q: How does a file management system operate and what is it?
A: What is File Management System? A file management system is utilized for document upkeep (or the…
Q: What exactly does the term "location aware application" mean?
A: The location-aware programme offers internet material to users contingent on their precise…
Q: Question 1: Write An ISEmpty Method For Array List.
A: The Java ArrayList isEmpty() method checks if the arraylist is empty or not. The syntax is:…
Q: The phrase "de-normalization" refers to the process of altering something from its initial…
A: Given: Denormalization is a method that is employed in typical databases that were established in…
Q: What distinguishes a text file from a binary file? Can a text editor be used to see a binary or text…
A: Text files are typically used to store a stream of characters and are those in which data is stored…
Q: Windows file explore or apple finder are types of
A: Windows file explore:- To open The File Explorer icon located in the taskbar. you can open the File…
Q: The definitions of "strict" and "loose" name equivalency are given.
A: "strict" and "loose": A philosophy of constitutional interpretation known as strict construction…
Q: What are the main features of graphics and media programmes such desktop publishing, computer-aided…
A: Various software and their functions: people also use specially designed software for their field of…
Q: Why is it that most languages do not specify the order in which the parameters to an operator or…
A: Parameters of the Function: The names of the arguments that are passed into a function are referred…
Q: What exactly are aggregates, and how can I tell? Who will gain from them?
A: Exactly are Aggregates: What Exactly Are These Things Called Aggregates? Sand, gravel, and crushed…
Q: 1. Should specialized courts for computer related crimes be created? 2. which categories of…
A: Yes, the creation of a cyber court would be advantageous for the courts in many ways. Primarily,…
Q: Description of Each request has its own object. b. Directions versus c. Model-View-Controller
A: The objects Request and Response Hyper Text Transfer protocol is what the whole internet is based on…
Q: What do you mean by Data Terminal Equipment(DTE) ? (
A: Data Terminal Equipment (DTE) is equipment that is either a destination or source for digital data.
Q: hat precisely is a grouping of items (also known as a container instance)?
A: The container instance or the grouping of items, are the services which is being provided by the…
Q: Why is it OK for a function to sometimes produce side effects?
A: When something has side effects, what does it mean? An operation, function, or expression is said to…
Q: Describe the position of the 802.11 beacon frames.
A: The solution is given in the next step
Q: If all of the RadioButton controls are in the same GroupBox, how many of them may be chosen…
A: We have to explain that if all of the RadioButton controls are in the same GroupBox, how many of…
Q: Nancy is leading a Scrum project for her organization. The project is to create new software for the…
A: The scrum team discusses the project requirements and helps Nancy and Tom identify the team's…
Q: What is growth function? What connection exists between fundamental algorithmic analysis and the…
A: Given: Can you explain the concept of functional growth? How the development of functions and the…
Q: What actions can you take to support green computing?
A: Green Computing Green computing refers to the ethical and sustainable use of computers & their…
Q: Please provide a brief explanation of Unicode.
A: Answer: Unicode is a standard for character encoding. The presentation of ASCII characters was…
Q: The difference between a threat and an assault
A: Introduction Threat: A threat is a potential security breach that may take advantage of a system's…
Q: In a few phrases, describe caching.
A: Hello student The asnwer will be in next step and as per my best of knowledge
Q: How is a double-valued vector created? How can a vector have a double attached to it? What is the…
A: Enter duplicate in vector: Then, using Push back (element: elementType): Void to add an item to a…
Q: What does the term "lazy evaluation" mean? What are promises exactly? What does the word…
A: Introduction: Lazy Assessment: Lazy evaluation, also known as call-by-need in programming language…
Q: 0 = {0} True or False explain why
A: A binary number is a number represented in a base-2 number system or binary number system, usually a…
Q: Describe why the programmes that have been built and delivered do not constitute the professional…
A: The Answer is in given below steps
Q: What precisely is a grouping of items (also known as a container instance)?
A: Grouping of items/collection of items: A container is another word for a collection. It is a piece…
Q: The difference between a threat and an assault
A: Threat and an Assault Threats can be intended, such as when someone is negligent, or unintended,…
Q: Why is it difficult to identify every use of an uninitialized variable during compilation?
A: undefined variable: Uninitialized variables are ones that are defined but are not initialised with a…
Q: Which problems could occur while employing communication technology?
A: Six Common Communication Technology Issues in Healthcare Communication is critical in healthcare…
Q: What precisely is a grouping of items (also known as a container instance)?
A: container instance
Q: Please show work and answer neatly In a classroom of 27 students, 11 students have a blue pen, 12…
A: We are given information about a classroom of 27 students. We are asked how many students carry only…
Q: There are differences between type conversion, type coercion, and nonconverting type casts.
A: There are differences between type conversion, type coercion, and non-converting type casts. While…
Q: What is ITIL 4 in detail? Give particular examples to illustrate the importance of this.
A: What is ITIL 4 ITIL (Information Technology Infrastructure Library) is a framework designed to…
Q: sketch whether one could, in a single stroll, cross all seven bridges of the city of Königsberg…
A: the solution is an given below :
Q: Justify why the professional software produced for a customer is more than simply a collection of…
A: Answer is in next step.
Q: What are universal reference types? What are their functions?
A: Presented: Please explain what universal reference types are and the function they provide. The…
Q: An overview of Visual Studio should be provided.
A: Microsoft is the world's largest provider of computer software.
Q: Give examples of how all types of software systems may benefit from the key software engineering…
A: Basic computer fundamentals Software is a collection of programming instructions that, when…
Q: In a classroom of 27 students, 11 students have a blue pen, 12 students have a red pen, 7 students…
A: We are given information about a classroom of 27 students. We are asked how many students carry only…
Q: Write a function, which given an int n, prints out a slash-based ASCII art of size n. Below is an…
A: The Python code is given below with code and output screenshot Happy to help you ?
r
Step by step
Solved in 2 steps

- Which of the following commands would display all files that start with the characters song and end in a number 100-599? A. ls song??? B. ls song[100-599] C. ls song[0-9][0-9][0-9] D. ls song[1-5][0-9][0-9]What does the following command do? $ mkdir dir dir/dir_01/dir_02Which pattern will match all filenames containing a "b"? [!b]* *b* *b b*
- What will be the value in EAX after the following lines execute?mov eax,30020000hdec axWhich of the following lines of code will not create a file “abc.txt”? Choose an answer A cat >abc.txt B touch abc.txt C >abc.txt D echo abc.txtIn your notebook, you want to load a CSV file into a DataFrame df. This CSV is in the path 'data/payments.csv' relative to the notebook. Which command do you use? Select an answer: df = pd.read_excel('payments') df = pd.read_csv('data/payments.csv') df = csv('data/payments.csv') df = read_csv('payments.csv')
- Can someone make a flowchart out of this? ss_kiosk_df = pd.read_excel("DATA SUPREME SURVEY FORM (Responses).xlsx") ss_kiosk_rename = pd.read_excel("DATA_SUPREME_COLUMN_RENAME_MAPPING.xlsx") ss_kiosk_drop = ss_kiosk_rename.loc[ss_kiosk_rename['column cleanse'] == 'Remove'].new.to_numpy() ss_kiosk01_df = ss_kiosk_df.copy() df01_col_cleansed = ss_kiosk01_df.rename(columns=ss_kiosk_rename.set_index('old')['new'].to_dict()).drop(ss_kiosk_drop, axis=1) df01_row_cleansed = df01_col_cleansed.loc[df01_col_cleansed['Kiosk Experience'] == 'Yes'] df01_row_cleansedWhat are the resulting values of the following commands. (* 3 5)2. (+ 1 2 3) 3. (+ 2 (- 7 2)) 4. ((LAMBDA (x) (* x x)) 4)write the code to lookup, add and remove phoneentries from the phonebook text file . These are the code we use for the lookup, add and remove in the case statement.(Lookup)# Look someone up in the phone bookgrep $1 phonebook (add)echo "$1 $2" >> phonebooksort -o phonebook phonebook (Remove)grep -v "$1" phonebook > /tmp/phonebookmv /tmp/phonebook phonebook Write a complete Bash script which will accept up to three command-line arguments: the first one is either (lookup, add or remove), the second one is a name enclosed in single quotes and the third one (if doing an add) is a phone number enclosed in single quotes. Using a case statement to match on either lookup, add or remove, the script should then perform the requested operation. Again here, you should first check for null arguments before continuing with the rest of the script or requested operation. In addition, the person may not be in the phonebook for lookup or remove so, you need to account for this.
- Which cat command is used to create empty files? i. cp ii. cat iii. touch iv. createWhich of the following utilities was designed to support data extraction from tabulated files? sed grep awk uniqTry giving these 2 commands $ echo cat$ cat echoExplain the differences between the output of each command.







