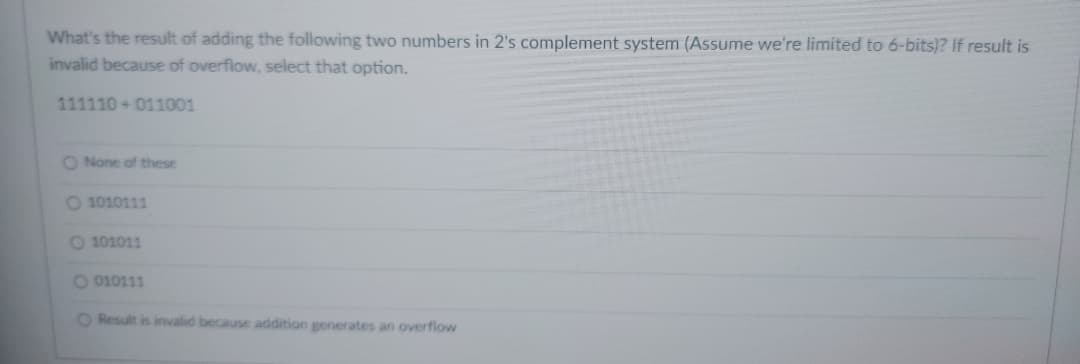
What's the result of adding the following two numbers in 2's complement system (Assume we're limited to 6-bits)? If result is invalid because of overflow, select that option. 111110 011001 O None of these O 1010111 O 101011 O 010111 O Result is invalid because addition generates an overflow
Q: It is important to explain how a challenge–response authentication system works and how it…
A: What are your odds of getting the challenge answer right: Verification of a challenge's response may…
Q: The TCP protocol's RTO and RTT parameters should be described in detail.
A: Retransmission Timeout (RTO): A retransmission timeout (RTO), on the other hand, is quite a…
Q: Describe in detail how the RTO and RTT parameters function while transferring data via the TCP…
A: The solution to the given question is: RTO A RTO occurs when the sender misses too many…
Q: 1. The Caption' property is used to change. (a) Color (b) Name (c) Font (d) Size 2. If you want a…
A: solutions in below step
Q: (A) Define the following Vector, Matrix, M-file scripts, ans., Whos, Matlab
A: Answer:
Q: Question: 13 Cache memory acts between (A) CPU and Hard disk (B) RAM and ROM (C) CPU and RAM…
A: Cache memory acts between CPU and RAM.
Q: 1- To clear all variables from Command window, we type Clear or Clear All. 2- Realmax is the…
A: 1. True 2. False 3. False
Q: I have to create my own Customized 2d Array (Matrix ) class in c++, which includes three private…
A: The class Matrix defines a 2D array with three private variables: int **matrix, int row, int col.…
Q: Which of the following functions covered in INT 10h moves the contents of a rectangular window up?
A: The BIOS interrupt call 10hex, also known as INT 10h, INT 10H, or INT 16, is the 17th interrupt…
Q: Explain what critical tasks you would recommend being included in an information security program…
A: Information security program: The InfoSec programme is used to create, implement, and maintain an…
Q: Distinguish the pros and cons of different authentication systems for security.
A: Answer: 1. SMS CodesSMS codes created by exceptional administrations are the most widely recognized…
Q: Task 19: List the REP_ID and the corresponding sum of the balances, as BALANCE, of all customers for…
A: List the REP_ID and the corresponding sum of the balances, as BALANCE, of all customers for each…
Q: DATA DEFINING ASSEMBLER DIRECTIVES PROVIDE THE PSEUDO INSTRUCTION FOR THE FF: (LABEL=VARIABLE)…
A: I will explain it in details and also give all answers,
Q: (B) Write a program to move the text (The Second Stage) from textbox to message box And change the…
A: The answer is given in the below step
Q: * Friend, friendly. Joy joyful O joyous O joyless O joying O
A: Answer to the given question: Friend - friendly Joy - Joyful
Q: (B) Write a program to move the text (The Second Stage) from textbox to message box And change the…
A: The answer is given in the below step
Q: The code segment, the data segment, and the stack segment are all distinct. Then, determine the mix…
A: A process (a running software) takes up a particular amount of memory: It may be used to store…
Q: The formatting character should be preceded by a ____ symbol. (A) + (B) / (C) % (D) -
A: The formatting character should be preceded by a % symbol.
Q: Two problems, the solutions to which may be found in computer simulations.
A: Introduction: Using simulation, management can quantify and monitor the system's behavior. Whether…
Q: Please explain what took place during the data breach that was reported before in your own words.
A: let us see the answer:- introduction:- A data breach occurs when confidential or protected…
Q: HD어 Hot Hot Hot D a) Write the expression related to the logic circuit given above as the sum of…
A: The answer is given in the below step
Q: What is the main folder on a storage device called? (A) Device driver (B) Root directory (C)…
A: Answer: The main folder on a storage device called root directory.
Q: (A)- Answer with True or False and correct the error 4- The abs(x) is maximum value. 5- The fprintf…
A: Solution : The answer of the all three questions are given in below.
Q: Living in France is hard work O a mess fast asleep O O O
A: The role is to complete the sentence.
Q: EPROM stands for (A) Electronic programmable read-only memory (B) Electrical principal read-only…
A: Option C
Q: Which SDLC should we utilize for an LMS portal?
A: Please find the detailed explanation in the following steps.
Q: (A) If the matrix A = [3 5 7; 10 11 12; 2 4 6; 13 14 15], find A([23].[21]) 1. 2. A (3.:) 3. A(:.2)…
A: Find the required answer given as below and output : As per company guidelines we are supposed to…
Q: Write A Matlab Code To Generate Row Vector At Range (0-5) With (11 Elements). write codes to:
A:
Q: We propose that Flynn's taxonomy be expanded by one level. What makes computers at this level…
A: Flynn's taxonomy: The taxonomy of Flynn is a classification of parallel computer architectures.…
Q: An operating system kernel is a complex structure that includes a number of subsystems.
A: Given: There are many different types of operating systems, but they all have one thing in common:…
Q: (A) Define the following Vector, Matrix, M-file scripts, ans., Whos, Matlab
A: Matlab is a programming platform designed specifically for engineers and scientists to analyze and…
Q: b. Discuss why maintenance of a software is important? Discuss some of the problems that are faced…
A: b) Software Maintenance :- Software Maintenance is part of the software development life…
Q: What are some of the first things that come to mind whenever you hear the term "email"? When an…
A: Email: Electronic mail (e-mail) is a computer-based programme that allows users to exchange…
Q: Discuss major OOP concepts briefly
A: Object-Oriented Programming or OOPs refers to languages that uses objects in programming
Q: Write a Technical Report on how Active Directory and Domain Name Systems can be used to manage Users…
A:
Q: You are a security analyst at a university. The university uses Linux-based tools when systems are…
A: The answer is given in the below step
Q: Draw the following diagrams to depict the scenario towards the development of the system: i.…
A: Planning -> Requirement Analysis -> Design -> Implementation -> QA -> Solving Bugs…
Q: (B) Write a program to move the text (The Second Stage) from textbox to message box And change the…
A: Since the language is not specified I wrote in the following language: C# private Point…
Q: (A)- Answer with True or False and correct the error 1. To clear all variables from Command window,…
A: The answer of this question is as follows:
Q: It is recommended that a description of the GetConsoleTitle function be provided.
A: Please refer below for your reference: GetConsoleTitle : It reciver the title bar string for the…
Q: An operating system kernel is a complex structure that includes a number of subsystems.
A: Kernel: The Kernel is the first software stacked after the bootloader since it handles the rest of…
Q: Think about creating a self-driving cab using PAGE; the goal is the O a. Stop b. Get to your…
A: An autonomous vehicle - (AV), often known as a driverless car or robo-car, is a vehicle that can…
Q: A) Answer with True or False 1. The Shape is a tool, which has no events. 2. There are two Methods…
A: In this question we have to prove the statement's whether these are true or false for the given VB…
Q: Draw a UML Use Case diagram for the following • Customer browses catalogue & selects items to buy. ●…
A: It is defined as a Unified Modeling Language which is a graphical notation used to construct and…
Q: Create a MATLAB code that solves roots of non-linear equations using False-Position Method. The code…
A: BELOW IS THE ANSWER- %ingridients f= input('enter your function: '); a= input('enter left side of…
Q: FOSCO is contemplating the possibility of creating a suitable software to improve the overall…
A: i) As being a software engineering i would be making the requirement on the basis of the front-end…
Q: Q2: Write A Matlab Code To Generate Row Vector At Range (0-5) With (11 Elements) And Then write…
A: Introduction: Row vector: It is a matrix having rows. It can be created by predefined function…
Q: Discuss why QoE instead of network capability should be considered while
A: The nature of involvement (QoE) of a given application or administration is estimated. It considers…
Q: What is the most effective method for acquiring application software? Your response need to provide…
A: Answer:
Q: CD-ROM stands for
A: Option(D) Compact Disk Read Only Memory is correct option CD-ROM stand for Compact Disk Read Only…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- The question is A=12 B=9 C=6 All of them base 10 We have to compute +A-B-C Using 1 compliment and 2 complement With using 8-bit binary signed numbers I have done it down but I think I am mistaken please check it And also we have to test the overflow for the complementsHow many bits do I need at a minimum to represent a 5-digit decimal number using packed decimal? How many for two’s complement? How many for unsigned binary? Explain. Do the following addition/subtraction problems in two’s complement binary (show your work) assuming 8 bit operands/result. If overflow happens, indicate it. a. 101 – 35 b. 101 + 94Kindly answer the following questions. j. The one thing that causes the most trouble with 2's complement numbers is the special case of the negative number which consists of a 1 followed by all 0's (1000 ... 000). If this number is n bits long, what number does it represent and why? (It is not negative zero.) a. Represent 187 in BCD code, excess-3 code, 6-3-1-1 code, and 2-out-of-5 code.
- The binary numbers illustrated below are 4-bit 2's complement binary numbers. Which of the following operations generates an overflow? Justify your answer by converting the operands and outcomes to decimals. a. 1111 + 0111 b. 1001 - 0011 c. 0111 + 0110Kindly answer the following questions. f. If the word length is 6 bits (including sign), what decimal number does 1000002 represent in sign and magnitude? In 2's complement? In 1's complement? g. What is meant by an overflow? How can you tell that an overflow has occurred when performing 1's or 2's complement addition? Does a carry out of the last bit position indicate that an overflow has occurred?For the decimal numbers A = -17 and B = 21, calculate A-B using only 6 bits in 2’s complement by following the steps below. Clearly indicate your 6-bit result and analyze whether or not it is correct by inspecting overflow. (a) Find 2’s complement representations of A and (-B) using 6 bits (b) Do 2’s complement addition A + (-B), where both numbers are represented with 6 bits 2’s complements (c) After handling with carryout, check possible overflow to decide if 6 bits is enough.
- Question 13 sum .Convert the following numbers to the destination system using 16-bit two's complement. I want the process only using two's complement step by step. transforming de number into binary, invert 0's and 1's , add 1 at the end. give the conversion of the result of the number into decimal/hexadecimal. give the final solution. (4096)hexadecimal --> convert to --> decimal (1110111000010001) binary--> convert to --> decimal (1010100111100101)binary -> convert to -> decimal (9105)hexa -> convert to-> decimal Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineWhat is the result of performing a 1-bit left circular shift on the following bytes represented in hexadecimal notation? Give your answer in hexadecimal form. 1.0xAB 2.0x5CBy using 2’s Complement arithmetic, write the following decimal numbers to equivalent8-bit signed numbers and perform the addition. Write the final result after the addition by showing yoursteps. (check the image for reference) i. 6 ii. 14 iii. 15 iv. -6+ 3 + (-5) + (-25) + ( -9)
- The following 6-bit binary numbers have a sign in the leftmost position and if negative are in 2’s complement form. Perform the indicated arithmetic operations and indicate whether an overflow occurs. A) 001011+100110= Overflow? B) 101110-110111= Overflow?1) In a 6-bit two's complement system, A=010110, B=001100, when perform X=A - B, which of following statement is true? Hint: perform C= NEGATE B, then perform X = A+C Question options: a. X is 001010, NZCV=0011 b. X is 001010, NZCV=0010 c. X is 101010, NZCV=0011 d. X is 101010, NZCV=0010 e. X is 001010, NZCV=0001Convert the following decimal numbers to 6-bit two’s complement binary numbers and add them.Indicate whether or not the sum overflows a 6-bit result (-16) + (-25):a. 100011 overflowb. 100111 no overflowc. 110000 no overflowd. 010111 overflow

