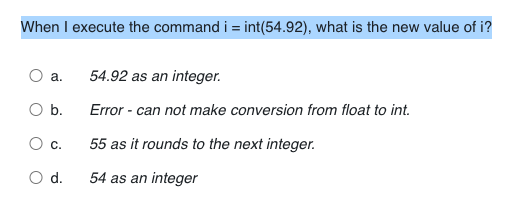
When I execute the command i = int(54.92), what is the new value of i? %3D
Q: Which of the following is NOT an example of methodical alignment of data? Predicting user…
A: Introduction: Which of the following is NOT an example of methodical alignment of data? Predicting…
Q: What precisely differentiates static memory allocation from dynamic memory allocation?
A: Given: What exactly is the difference between dynamic memory allocation and static memory…
Q: Formula for Savings is A. Yd - C = S B. Yd + S = C C. Yd - S = C D. Yd + C = S
A: The correct answer is : A. Yd-C=S
Q: Im really interested in learning the names of the three basic frequency bands that are used in…
A: The names of three basic frequency bands utilised in wireless communication systems are discussed…
Q: Which is safer for frequent reuse patterns: a low reuse factor or a high reuse factor? Provide an…
A: When channels are allocated and reused over a certain coverage area, the term Frequency Reuse is…
Q: Consider the internal attacks on higher education. Please let us know if you have any suggestions…
A: Consider the internal attacks on higher education. Please let us know if you have any suggestions…
Q: Suppose you want to use Heapsort to sort the contents of the following array in alphabetical order:…
A: Given that array is Suppose you want to use Heapsort to sort the contents of the following array in…
Q: 5. Round Robin(RR) Scheduling (Quantum = 3, Context Switch = 1) according to the below table: Note:…
A: Here is the solution
Q: 8 X 8 Router, where each input runs at 5 Gbps. Assume, the average RTT = 160 msec. What is the rule…
A: Given , 8 X 8 Router Input speed = 5 Gbps (giga bytes per second) = 5 × 103 Bytes/sec. RTT = 160…
Q: Certain credit card issuers provide one-time-use credit card numbers for electronic payments as a…
A: Every time a user makes an online purchase, he enters his PIN and then the one-time code that…
Q: However, there is still the issue of determining precisely what we are referring to when we discuss…
A: 4G or 5G networks: In a nutshell, the shift from the 4G network to the 5G network is being driven by…
Q: According to Network Analysis, Architecture, and Design, there are a few key distinctions between…
A: Introduction: According to James D McCabe's book, there is a distinction between network design and…
Q: Detailed information on the Domain Name System (DNS), including iterated and non-iterated searches,…
A: The goal of DNS is to translate a domain name into an IP address. This is done by getting the DNS…
Q: Q:IF R auto =BO00 and its operand is (AO) hex the content of register C= (8C) hex what is the result…
A: Given: R auto=B000, it's operand is A0 hex C = 8C hex Given instruction is: LOAD _ (Rauto), C
Q: Paging as a memory management strategy has many benefits and cons.
A: Given:Explain in further depth three benefits and three drawbacks associated with the use of paging…
Q: What is dynamic memory allocation and how is it implemented? When it comes to the user, what are the…
A: Given: How does dynamic memory allocation work? Dynamic memory allocation is used when an operating…
Q: Make a C program that prompts the user to input a positive integer value, and compute the following…
A: Sample Output Screenshot:
Q: How does symmetric key cryptography differ from asymmetric key cryptography?
A: Given Question: What is the difference between symmetric and asymmetric key cryptography?
Q: accel = OxA4; PORTB = 0x23; What is the value of PORTB after the following mask operation? PORTB =…
A:
Q: The MetaData component of the architecture is the most crucial component of the architecture. This…
A: INITIATION: According to the inquiry,The database is based on the main webpage.This database is…
Q: How does connecting to a Wi-Fi hotspot and using WhatsApp to make a VoIP call when travelling abroad…
A: Introduction: Mobile carriers face both a danger and an opportunity from over-the-top (TOT) services…
Q: Q1\Write a program that sums the numbers between 1 and 9 and finds the sum total
A: As no programming language is mentioned, I am using C++ There are two ways of doing this: Run loop…
Q: Consider a 200 cylinder hard disk with one arm. Suppose the following cylinder requests arrive in…
A: Consider a 200 cylinder hard disk with one arm. Suppose the following cylinder requests, made by…
Q: Test if the value of the variable age is greater less than or eg ual to 4O 0 If it i s print "Vou're
A: JavaNote: PLease use BufferedReader insteaad of Scanner Test if the value of the variable age is…
Q: Q1\Write a program that sums the numbers between 1 and 9 and finds the sum total
A: Here language is not mentioned so i write c code to sum between 1 to 9: (2+3+4+5+6+7+8)…
Q: Describe how computers help scientists.
A: Describe how computers help scientists.
Q: Examine the different development methodologies utilized to create the Windows and Android operating…
A: Windows is a group of various proprietary graphical operating systems which is provided by Microsoft…
Q: Why is the most important aspect of a data warehouse referred to as MetaData, and what exactly is it…
A: A user-requested piece of metadata is information about data or documentation on data. Metadata is a…
Q: Common Lisp and Scheme are diametrically opposed in what respects?
A: Introduction: Common Lisp is more simpler and more compact in comparison to Scheme. Although Scheme…
Q: Create a program of "SERVER AND MULTIPLE CLIENTS CHAT ROOM WHICH INCLUDE FILE TRANSFER PROTOCOL" in…
A: Create a program of "SERVER AND MULTIPLE CLIENTS CHAT ROOM WHICH INCLUDE FILE TRANSFER PROTOCOL" in…
Q: Add string conversion operations to the following print statement such that
A: The answer is
Q: Create a program that will allow the user to enter a string. The program should then randomly…
A: ALGORITHM:- 1. Take input for the string from thr user. 2. Generate a random number. 3. Print the…
Q: Voice and video traffic are handled uniquely by the network in comparison to other kinds of data,…
A: Given: The network processes speech and video differently than other forms of data for obvious…
Q: This article explains dynamic scoping, including when and why it is used, the performance…
A: Explain in detail the errors that newcomers to the field of machine learning should avoid: 1) The…
Q: Vrite a program using MATLAB to multiply any number of numbers by the numbers between 1-49
A: Given:
Q: As an alternative to connection-based protocols, connectionless protocols have been proposed. Please…
A: Data communication occurs when two or more computers linked to the same or different networks send…
Q: Question 1 Every disconnected graph is a simple graph True False -- / Question 2 A graph is…
A: Answer 1 Disconnected Graph: A graph is considered disconnected if at least two of its vertices are…
Q: Compilers have a tough time implementing either the VLW or the superscalar architecture. Which…
A: VLIW versus superscalar: Which is harder to implement? Why? The abbreviation "VLIW" stands for…
Q: In the context of computer security, how exactly does ransomware function?
A: Computer security, often known as cybersecurity, protects computer systems and data from harm,…
Q: Describe how computers help scientists.
A: Introduction: In scientific investigations, computers can evaluate data in ways and at speeds that…
Q: There are a few different categories into which one may place protocols that are used on networks
A: The term "network" refers to a collection of computers and other electronic devices that are linked…
Q: When it comes to computers, how are embedded systems different from regular ones?
A: According to the information given:- We have to define the difference between the computer and…
Q: Problem: A Hamiltonian cycle, also called a Hamiltonian circuit, Hamilton cycle, or Hamilton…
A:
Q: QUESTION 15 The following algorithm finds the same character in two strings: string, -xx2Xn and…
A: The following algorithm finds the same character in two strings: string=X1X2..Xn, and…
Q: The following is a summary of the three-sphere model of systems management. Exist alternatives to…
A: The answer to the following question:-
Q: Why may stack systems use reverse Polish notation to represent arithmetic expressions?
A: Polish Notation in Reverse: It is a method of encoding arithmetic expressions in which the operator…
Q: the introduction to INTERFACING SEVEN-SEGMENT DISPLAY should include
A: Given: A seven segment display module is an electrical gadget with seven LED segments that is used…
Q: When it is helpful to arrange processes and programs into subsystems that function on a large…
A: Introduction: Hardware and software are the two essential components of every computer system. The…
Q: What's the difference between embedded system software and system software in general? What are some…
A: System Software: System software is software that is used to operate and control a computer system,…
Q: User On-boarding Please, provide the following information. Before your information can be…
A: 1-> for validation of fields like name, and password I have used the HTML pattern attribute.…
Step by step
Solved in 2 steps

- The following code I have written is supposed to check if the first character of the first given command line argument is the same as the last character of the last command line argument. However, I keep getting false when I am running it. Why is this occurring? #include <iostream>#include <string>using namespace std; #define N 1000 int checkChar(char str[]) { //method to check first and last char in string int n = strlen(str); char first = str[0], last = str[n - 1]; //if first equals to last then returns 1 if (first == last) return 1; //otherwise 0 else return 0; } //end of checkChar int main(int argc, char* argv[]) { //main method int check; //check variable which stores either 0 or 1 // new str string with initial size N char str[N]; for (int i = 1; i < argc; i++) { //for-loop to copy argv array element in str char type array //strcat_s(str, argv[i]);str[i] = *argv[i]; } //calling method checkChar by passing argument str check = checkChar(str); if (check) // when…Which of the following will not provide a valid output? int(str(23)) float(2.3e2) bool(divmod(3,0)) bool(0.0e1) bool(divmod(6,7))Which of the values below will not be printed to the console when this code is executed?for (int i = 0; i < 3; i++) { for (int j = 0; j < 2; j++) { if (i == j) { continue; } System.out.println("i = " + i + " j = " + j); }} a. i = 0 j = 1 b. i = 1 j = 0 c. i = 2 j = 0 d. i = 2 j = 1e. i = 1 j = 1
- Which of the following is correct about the first parameter of the "main()" function? a) The first argument is of int type b) Stores the count of command-line arguments c) The first argument is non-negative d) All of the mentionedCalculate 2nd element of ??=[?,??,??,??] divided by 1st element of ??=[?,??,??,??]. Use two def and return commands instead of indexing. Print the result and store it as a variable (float or integer). With Python and simple codes please.Write a code that only utilises the XOR method after getting two numbers from the user. When saving integers in a temporary variable, you should not swap them. Your application should have an acceptable and useful input prompt, as well as report the findings in a logical manner.
- Can you exlplain with comments following data .data prompt byte1 "Input number1:-" mynumber1 byte1 10 prompt byte2 "Input number2:-" mynumber2 byte2 10 .code main PROC cmp mynumber1 , mynumber2 jl Less move Word [temp] , mynumber2 jump both: Less: move Word [temp] , mynumber1 Both: prompt demo "Input Newnumber1:-" demo1 demo10 cmp demo1, temp jl Less move Word [temp] , temp jump both: Less: move Word [temp] , demo1 And the cycle continuesWhich of the following will not provide a valid output? Group of answer choices float(2.3e2) bool(divmod(6,7)) bool(0.0e1) int(str(23)) bool(divmod(3,0))Which of the following Python statements assigns a variable to an increasing set of values with constant increment? a. import numpy as np b. dBdt = k1*Ca = k2*Cb c. t= np.linspace(0,5,100) d. C0 = [Ca0, Cb0, Cc0]
- This code is correct i just want an explanation pleased) Write the command that express a pi as a character and ?an integerWhich XXX is needed for enterNumber() to read a value from standard input? publicintenterNumber()XXX{int value;value = System.in.read();return value;} a. import java.io b. throws SystemException c. nothing is needed d. throws IOException JAVA



