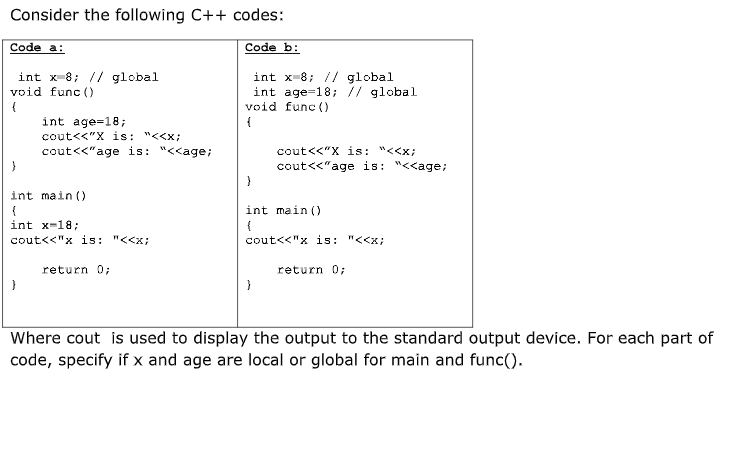
Consider the following C++ codes: Code a: Code b: int x-8; // global void func () int x-8; // global int age-18; // global void func () int age-18; cout<<"X is: "<
Q: Discuss real-world scenarios in which an array (linear) version of a stack could be acceptable, as…
A: Answer
Q: When string primitives are executed, which Direction flag setting causes index registers to flow…
A: The direction flag, which is stored in the FLAGS register on all x86-compatible CPUs, regulates the…
Q: Write a simple program (using Java) that contains a static method. Briefly explain the difference…
A: Static Method A static method is also called a class method and is common across the objects of…
Q: Define a function called bell which takes a non-negative integer n and returns the number of…
A: You are not mention programming language here so I am going to solve this question in c++ language.…
Q: What exactly is the Maple command?
A: Intraduction: COMMANDER MAPLE: The maple command used to automatically finish the work of…
Q: Explain how the Internet of Everything (loE) differs from the Internet of Things (loT) in terms of…
A:
Q: What are the different MMC types that are utilized in current devices?
A: MultiMediaCard, officially abbreviated as MMC, is a standard memory card used for solid-state…
Q: What is the difference between data, information, and knowledge, and can you give me some instances…
A: EXPLANATION: Data: Data is/are the world's facts in whatever form and may be seemingly meaningless…
Q: Explain the concept of quantum computing.
A: Answer
Q: What is the attack on the DNS (Domain Name System) in computer networking?
A: Introduction: It's called "NS" (Domain Name System)The domain name system (DNS) is database that…
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in…
A: We need to write a PhP code, to convert the degree celsius, entered by the user to Fahrenheit.
Q: What do you mean by subnet mask?
A: A subnet mask is a 32-bit number. It is used to differentiate the network component of an IP address…
Q: Is it necessary to sanitize data on a regular basis? Give examples to support your response.
A: Data cleansing is the process of cleaning up data. The term "data cleansing" refers to the process…
Q: create a truth table that will accpet 2-bits as input (A,B) and will generate the square of the…
A: Here in a 2 bit number, the highest possible integer value is 3 Square of 3 is 9 . The output 9…
Q: What recent cyber-attacks have hampered WFH (Work From Home) or distance learning?
A: Introduction: Many companies enable workers to take some work home with them because it boosts…
Q: Data storage and visualization are two of the most important aspects of data management. Explain how…
A: Business intelligence, as we know it today, would not be possible without the data warehouse. At its…
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in…
A: <?php $fahrenheit =(int)readline('Enter an integer: '); $celsius =…
Q: What is the difference between a DLL and an EXE in the.NET Framework and why is it important?
A: The Answer is in given below steps
Q: Write a C++ program that contain a menu rto call user defined functions on a one dimendional array :…
A: In the given c++ program we can take array elements greater than 20,print the contents of array and…
Q: What makes the LEA instruction superior than the OFFSET operator?
A: Introduction: There is an instruction called LEA (Effective Load Address) and an alternate OFFSET…
Q: What is the attack on the DNS (Domain Name System) in computer networking?
A: DNS attack is exploitation where the attacker takes advantage of the vulnerability of the domain…
Q: hat is the definition of the closest neighbor (
A: Lets see the solution.
Q: With Uber as an example, distinguish between disruptive products and disruptive processes.
A: Since Christensen introduced his theory to the corporate world, the two phrases have been often…
Q: Explain the concept of quantum computing.
A: According to the question the field of the quantum computing was discovered that certain…
Q: What is the attack on the DNS (Domain Name System) in computer networking?
A: Introduction: It is possible for a bad actor to either attempt to hack into a network's Domain Name…
Q: Write an adder python program that prints the sum of all the integer command line arguments passed,…
A: Code: summ=0while(1): a=input("Enter: ") if(a=="-1"): break elif(a.isnumeric()):…
Q: Give examples of when you might prepare ROM, budgeted, and definitive cost estimates for an IT…
A: INTRODUCTION: The project, in reality, is a set of tasks that must be accomplished to achieve a…
Q: Explain why the MUL and one-operand IMUL instructions do not cause overflow.
A: Introduction: Multiplication instructions are MUL and IMUL. MUL instructions are used to multiply…
Q: Create a two-instruction AX program that transforms a two-digit ASCII decimal number to binary.
A: INTRODUCTION: When a product fits completely within its register, the IMUL instruction extends it…
Q: List the metrics used by Hofstede to study the different dimensions of behavior
A: Dr. Geert Hofstede, a psychologist, in the late 1970s he developed his cultural dimensions model ,…
Q: Which list below includes only items that would be expected to be included in a block header? O…
A: Solution: Given, Correct answer is: timestamp, transaction data, nonce
Q: How do you know whether a system component should be a source or a sink? or as a method?
A: Given: The source denotes the point at which data enters the system, whereas the sink denotes the…
Q: Solve problem by us ing PYTHON Program to remove the ith occurrence of the given word in list where…
A: Create a python program to delete the Nth occurrence of a word from the python list. First, read a…
Q: The Fast Freight Shipping Company charges the freight based on the weight of the package as per the…
A: In this problem i have used Netbeans to create GUI -> first create a gui swing in netbeans ->…
Q: In computer programming... 10 % 3 * 3 – (1 + 2) =
A: Explanation:-The priority of the operators present in the given equation is as follows:- () > %…
Q: Explain in a few words how would you use a truth table to determine whether the given proposition is…
A: Dear student, let's see what is tautology first. Tautology It's simple, if all the values are true…
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in…
A: PHP program to convert degree Celsius to Fahrenheit. For this we can use formula F=(C * 9/5)+32…
Q: How do you create an index? How do you create a unique index? What is the difference between an…
A: -Creating an index involves the CREATE INDEX command. -it allows us to name the index, to specify…
Q: How to decide if your variable
A: Q)How to decide if your variable should be declared as an enum type or any other data types? Support…
Q: You were just appointed as your company's CIO. As Chief Information Security Officer, your first…
A: Data loss is said when information systems are corrupted, deleted, or unrecoverable. It most…
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in…
A: In the given php program we can take a input as fahrenheit temperature and it will be converted into…
Q: Is there anything else that connected-car technologies could provide automakers like BMW in terms of…
A: Introduction: Car-to-car communication: Cars that are linked to the internet and the internet of…
Q: Explain the different collaboration tools available and how they may be used to improve project…
A: Technology for Collaboration: Collaborative technology is a term that refers to tools and systems…
Q: Is there anything else that connected-car technologies could provide automakers like BMW in terms of…
A: Introduction: Car-to-car communication Cars that are linked to the internet and the internet of…
Q: Write down the essential processes that the website takes to load when a user or customer requests…
A: Introduction: A web application is an application program that operates on a web server instead of…
Q: What will be the impact of the internet of things (loT) on our everyday lives? Justify your position…
A: If we talk about the future of technology or of Internet of Things, It we will be able to do any…
Q: Explain the different collaboration tools available and how they may be used to improve project…
A: The solution to the given question is: Collaboration technology is a combination of powerful online…
Q: Assume s is a string. Write an expression that results in a string consisting of the third through…
A: Your C++ program is given below as you required with an output.
Q: 4. Try to perform four mathematical operations to add, subtract, multiply, and divide into two…
A: Solution: # !/bin/bash # Take user Inputecho "Enter Two numbers : "read aread b # Input type of…
Q: Using the below grammar,
A: Solution - In the given question, we have to show a complete leftmost derivation for the given…
Step by step
Solved in 2 steps

- Problem: Write a C++ program that would implement the function called filterString which accepts a string s that contains numbers and letters mixed up. The function must return an integer corresponding to the numbers in s in the order that they appear. If there are no numbers in s, the function should return 0. TEST CASES: filterString(‘123’) = 123 filterString(‘abc’’) = 0 filterString(‘aa 112 3dd’) = 1123 ASSUMPTIONS Assume that all the inputs are strings (no need for try-catch method)(Civil eng.) Write a C++ program to calculate and display the maximum bending moment, M, of a beam that’s supported on both ends (see Figure 3.8). The formula is M=XW(LX)/L, where X is the distance from the end of the beam that a weight, W, is placed, and L is the beam’s length. You program should produce this display: The maximum bending moment is xxxx.xxxx The xxxx.xxxx denotes placing the calculated value in a field wide enough for four places to the right and left of the decimal point. For your program, assign the values1.2,1.3,and11.2toX,W,andL.AHPA #9:A Gas Station• You have been asked to create a C program to manage the gaspumps at a gas station. The station has four pumps connectedto four tanks with capacities: 100, 75, 50, and 150. Every timea car fills up it takes 10 gallons. You’ll know that a car hasarrived because the carArrived function will return with apump number. After a car has filled up, print out the currentcontents of all four tanks.• Write a C program that can track each of the four tanks. Updatethe amount of gas remaining in a tank when a car fills up.When a tank gets to less than 20 gallons of gas remaining,make a call to request a refill truck visit the station(refillRequest). This will cause the tank to berefilled automatically
- Computer Science **C language not C++!** ** Write C program (NOT C++) which takes as input a positive integer n and decides whether or not n is prime. The decision is made by the int isPrime(int) function whose return value is 1 if the number is prime, otherwise 0. **C language not C++!** **in c++ language Write a C++ function named greater_10. This function returns an int and has two integer arguments, number1 and number2. greater_10 returns 1 of the sum of number1 and number2 is greater than 10 otherwise return -1.Jeff and Gern run a furniture company specializing in tables and chairs. To save time, when a new order comes in, a special shorthand is used to describe the order. The rules for their shorthand are as follows • The first character is "T" for a set of tables, or "C" for a set of chairs. If the order includes both tables and chairs, the order shorthand begins with "TC" • Next they indicate the number of tables or chairs for the order. If the order includes both tables and chairs, they'll write the number of table first, then the number of chairs, separated by a dash. An order comes in for three standard tables constructed using Oakwood. What would the order shorthand be for this order?
- Write a main function that calls div (int x, int y); Write the code below. Use C++ programming language.Write these codes in c language please. Thank you in advance. 1. Define a function CalcPyramidVolume with double data type parameters baseLength, baseWidth, and pyramidHeight, that returns as a double the volume of a pyramid with a rectangular base. CalcPyramidVolume() calls the given CalcBaseArea() function in the calculation.Relevant geometry equations:Volume = base area x height x 1/3Base area = base length x base width.(Watch out for integer division). 2. Complete function PrintPopcornTime(), with int parameter bagOunces, and void return type. If bagOunces is less than 3, print "Too small". If greater than 10, print "Too large". Otherwise, compute and print 6 * bagOunces followed by " seconds". End with a newline. Example output for ounces = 7:42 seconds 3. Write a function PrintShampooInstructions(), with int parameter numCycles, and void return type. If numCycles is less than 1, print "Too few.". If more than 4, print "Too many.". Else, print "N: Lather and rinse." numCycles…Define the function: int power (int base, int exp) {/*It accepts the arguments for base and exponent and returns power. The algorithm is to repeatedly multiply the value of the base to how many times the value of exponent. Test the function inside main(). Write the complete C program. */} For example: Intput. Result 2 32 5
- a. Write a c program that asks a user for an integer. Declare a variable num3. Let num3 = --x; Display the values of x, and num3.b. Write a c program that asks a user for an integer. Declare a variable num4. Let num4 = x--; Display the values of x, and num4.Consider the following C++ structure and declarations: struct Player { string firstName; string lastName; int hits; int runs; }; int main() { Player p = { "Jackie", "Robinson", 1518, 947 }; Player team[24]; Player *tPtr = team; team[0] = p; // INSERT CODE HERE } The statement tPtr = team+9; will assign the same memory address to tPtr as the statement tPtr = &(team[9]); A) True B) FalseC++PROBLEM: Write a C++ program that will accept 3 strings (these should be of different sizes) then sorts them from least to highest number of characters. Your program should only accept a maximum of 15 characters and display a message if exceeded. SPECIFICATIONS: - All lines of codes should have a comment. TEST CASES: If a user inputs valid strings: Enter string 1: Cherries Enter string 2: Apple Enter string 3: Banana Result:Sorted Strings: AppleBanana Cherries If a user inputs not valid: Enter string 1: Apple Enter string 2: Apple Cherries Banana Result: Oooops! Exceeded the maximum number of characters!

