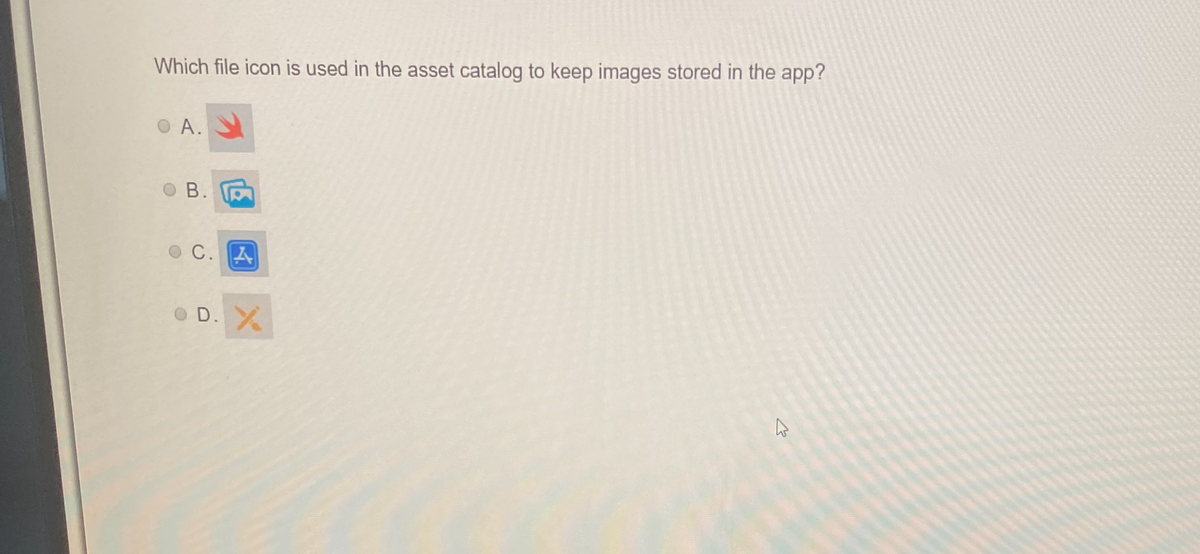
Which file icon is used in the asset catalog to keep images stored in the app? OA. B. OC. A OD. X ←
Q: Why should a computer have several subsystems and logical divisions?
A: Subsystems and logical divisions are crucial for enhanced functionality and efficiency in A computer…
Q: Compare and contrast Governance and Management in information system audits.
A: What is information: Information refers to processed or organized data that is meaningful and useful…
Q: 4. Given two heads of two singly linked list, return the node at which the two lists intersect. If…
A: Problem 4: Finding the intersection point of two linked lists Initialize two pointers, ptrA and…
Q: In this presentation, it is recommended that a single slide be used to communicate an overview of…
A: What is presentation: A presentation is a method of delivering information or ideas to an audience…
Q: Instead of focusing just on speed, explain why having deep access rather than shallow access is…
A: Having deep access, instead of shallow access, gives a few benefits to software developers. While…
Q: What are the advantages of using a compiled language over an interpreted language? In which…
A: Compilers translate compiled languages into machine code that can be executed by the processor. As a…
Q: How can I save time and money with the IT simulation viewer?
A: Hello student Greetings In today's fast-paced and cost-conscious business environment, finding…
Q: Create a method that accepts a pointer to a Node structure as an argument and returns a full copy of…
A: According to the information given:- We have to create a method that accepts a pointer to a Node…
Q: Explain how each of the eight cost estimating strategies may be used with various heuristic criteria…
A: Cost estimating strategies in a DBMS are crucial to evaluate the efficiency of various query…
Q: Throughout your computer science study, you were advised to make a relationship between the…
A: In computer science, object-oriented systems are a fundamental concept used to model and design…
Q: What computer architecture dominates smartphones? Explain why.
A: In mobile devices like smartphones, the most commonly used computer architecture is the ARM…
Q: Please explain the circumstances that have led to computers becoming so prevalent in today's…
A: In recent years, the presence of computers in educational settings has become increasingly…
Q: Please help me learn Python.
A: Learning Python, a popular programming language, can open up a world of possibilities for…
Q: Please explain the circumstances that have led to computers becoming so prevalent in today's…
A: The popularity of computers in schools today can be attributed to many factors that contributed to…
Q: Explain why deep access is better for software developers, not simply performance.
A: What is software: Software is a collection of programs, data, and instructions that enable computers…
Q: What does "many processes" imply vs "many threads" in this situation? Could you clarify your…
A: In the field of computing and programming, concurrent execution is a common requirement for…
Q: Foreign keys safeguard databases how? You have proof?
A: A foreign key is a folder design notion used to preserve the truth and start a logical relationship…
Q: Compare and contrast the similarities and differences between Governance and Management in the…
A: Governance and management are two distinct but interconnected concepts in the context of information…
Q: How do foreign keys safeguard databases? What evidence do you have?
A: What is database: A database is a structured collection of data organized and stored…
Q: Data protection—how? Which option best authenticates and protects data?
A: Data protection safeguards critical statistics from being tamper with, compromise, or lost. With the…
Q: ake a python program that does the following. Make sure that it works and interfaces with the user…
A: Dear Student, The required code along with implementation and expected output is given below -
Q: In this post, we'll look at four different logical security strategies that, if implemented, would…
A: Data security ensures that digital information is safeguarded against unauthorized access, theft,…
Q: When it comes to the most important duties, how do the Phases of Compiler handle them? How may…
A: The question explores how the phases of a compiler handle the most important duties in the…
Q: 1C. Consider the grammar E-TE' E' → + TE' | E T → FT' T'→ *FT' | E F→ (E) | digit For the given…
A: your answer is given below!!!
Q: Which of the following sentences best expresses your opinion on the need of preserving data security…
A: Hi.. Question look like choose the best answer without option. pls check below for the answer. TO…
Q: Was there a significant difference between compiled languages and interpreted languages?
A: Difference between compiled languages and interpreted languages
Q: Smart cards are more secure than magnetic stripe cards.
A: Payment and identification systems, the security of card-based transactions is of paramount…
Q: Multitasking makes switching apps easy. Can a machine run several OSes? Yes or no? If so, what are…
A: In computer science, running several operating systems (OSes) on a single system is possible. This…
Q: Here is an in-depth examination of the Access Control List.
A: An Access Control List (ACL) is a safety instrument used in computer systems toward define and…
Q: Explain why programmers prefer deep access over shallow access, not only performance.
A: Explain why programmers prefer deep access over shallow access, not only performance answer in below…
Q: Siobhan uses an 8-gigabyte computer. Her software need 8 GB of RAM on her computer, including 2 GB…
A: Data centers play a crucial role in providing computational resources, including storage and…
Q: What are some of the ways in which the spiral model of software development may be beneficial for…
A: The spiral model combines the idea of iterative development with the systematic, controlled aspects…
Q: you are tasked with analyzing an algorithm which schedulea processes in a multiprogramming system.…
A: In a multiprogramming system with two CPUs, each having two threads, we are analyzing an algorithm…
Q: Q2:Write a row-level trigger that executes before updating a project’s location in the project…
A: your answer is given below!!!
Q: 1- What is the differences between Link state routing and distance routing algorithms
A: In the realm of computer networking, efficient and reliable routing is essential for the successful…
Q: How are items carrying data in a partially filled array tracked when the array is only partially…
A: When working with partially filled arrays, it is important to have a mechanism for tracking the…
Q: Why must computer communication employ numerous protocols? Explain
A: Numerous protocols are used in computer communication to provide dependable and effective data flow…
Q: The Von Neumann Architecture made computers "Universal (General) Machines" from "Special Purpose…
A: John Von Neumann's conceptual architecture was introduced in 1945, significantly Changing computer…
Q: One explanation for this is the amazing capability that today's computers possess. Is there any…
A: In the early 1980s, computers begin to find their way into classrooms, initial in urban countries…
Q: Q4. Do only part b) and c). Suppose the PDA P = = ({q,p}, {0, 1}, {Zo, X}, 8, q, Zo, {p}) has the…
A: PDA stands for Personal Digital Assistant. It refers to a handheld electronic device that combines…
Q: In this presentation, one slide should provide information assurance and critical upgrade needs.
A: What is presentation: A presentation is a communication tool used to deliver information, ideas, or…
Q: How can I make the most of the IT simulation viewer in order to save time and money?
A: The IT Simulation watcher is an priceless tool that allows you to view IT systems' Behaviors,…
Q: Review the code snippet. struct appDevGrades ( var Joe = 90 var Viki = 99 var Jess = 78 var Angie =…
A: - I am solving the first question according to the guidelines. We need to get the code snippet that…
Q: four different logical security strategies that, if implemented, would provide the system security…
A: Here are four different logical security strategies that, if implemented, would provide the system…
Q: As you studied, there are several exceptions, one of these allows the program counter to increment…
A: The correct answer is 3) Fault. In computer architecture, the program counter (PC) is a register…
Q: What are the contemporary issues concerning the field of Computer Engineering
A: Computer engineering is a rapidly evolving field that intersects computer science and electrical…
Q: Layered architecture benefits which software?
A: A software design pattern called "layered architecture," commonly referred to as "n-tier…
Q: Draw an inheritance hierarchy: apple, ice cream, bread, fruit, food item, cereal, orange, dessert,…
A: Food Item | Fruit | Apple Orange | Dessert | Chocolate mousse Ice…
Q: Every kind of virtualization (Language, Operating System, and Hardware) is considered.
A: Virtualization is a concept in computing that allows for the emulation of resources, including…
Q: Why should data be backed up to prevent computer failure or data loss?
A: Data backup is a critical aspect of computer systems and information management. It involves…
Step by step
Solved in 3 steps

- Question 4 What command will create the archive pics of the folder camera? A. tar cf pics.tar camera B. tar cf pics camera C. tar cf camera pics.tar D. tar cf pics camera.tar Full explain this questionWhich option is used with touch command which forces the command not to create file, if it does not exists. i. -h ii. -c iii. -t iv. -fWhich of the following option creates a Microsoft Word document file in MS Access without exiting the application? a. OLE Object b. Hyperlink c. Memo d. Attach Document
- Which file contains default information such as UID and GID ranges and minimumpassword length to be used at user creation?a. /etc/skelb. /etc/passwdc. /etc/login.defsd. /etc/default/useraddWhich of the following commands will remove a file called myfile.c from the file system? O a. edit-out filesystem | myfile.c Ob. del myfile.c O c. remove myfile.c Od. del –f myfile.c Oh e rm -f myfile.cWhich filenames would be a subsequent ls command display?$ lsabc abd abe abf abg abh$ rm abc ab*rm: cannot remove ‘abc’ : No such file or directory
- Which cat command is used to create empty files? i. cp ii. cat iii. touch iv. createWhich file contains information regarding the users, computers, and commands used bythe sudo command?a. /etc/sudob. /etc/su.cfgc. /etc/sudo.cfgd. /etc/sudoersWhich file access flag enables writing output to the end of the file? Group of answer choices ios::in ios::out ios::app ios::binary
- Which of the following commands can be used to list the files contained within aninstalled RPM package?a. rpm –qa packagenameb. rpm –qi packagenamec. rpm –ql packagenamed. rpm –q packagenameWhich one of the following is correct about the Save and Save As options of File menu in Microsoft Office programs Word, Excel and Power Point?. Choix unique. a) “Save” saves the document with a different name to a different folder b) “Save As” saves the document with a different name to a different folder c) Only “Save”, makes the document saved d) Only “Save As”, makes the document saved 22, What settings can be done from the Print option of File menu in Microsoft Office programs Word, Excel ve Power Point? I. Selecting printer, II. Paper width and length, III. The number of pages per sheet, IV. Which pages to print, V. Double sided/single sided selection, VI. Page layout, VII. Margins, VIII. Number of pages per sheet. Choix unique. a) None b) I,II,VI c)II,IV,VII d)All 33, Which option in the Home menu in Microsoft Office Word, gives the text effects of reflection, shadow and glow ?. Choix unique. a) b) c) d) 44, With…Which one of the following tool deletes your files/data permanently. a. Change Directory b. SDelete c. WinRaR d. Rename

