Which of the following are correct definitions of defences: a. Stateless firewalls maintain a list of running sessions and permit unchecked access once a session is on the list b. Denial of service attacks affect the confidentiality of data on a network Oc. Dorothy Denning was a pioneer in developing Intrusion Detection Systems Od. Stateless firewalls do not process every single packet that passes through them ☐ e. Intrusion Detection Systems are based partly on the hypothesis that exploiting a system's vulnerabilities is likely to result in abnormal network activity Of. Proxy firewalls carry out external network access on behalf of clients on the internal network
Which of the following are correct definitions of defences: a. Stateless firewalls maintain a list of running sessions and permit unchecked access once a session is on the list b. Denial of service attacks affect the confidentiality of data on a network Oc. Dorothy Denning was a pioneer in developing Intrusion Detection Systems Od. Stateless firewalls do not process every single packet that passes through them ☐ e. Intrusion Detection Systems are based partly on the hypothesis that exploiting a system's vulnerabilities is likely to result in abnormal network activity Of. Proxy firewalls carry out external network access on behalf of clients on the internal network
Chapter14: System Administration
Section: Chapter Questions
Problem 2RP
Related questions
Question
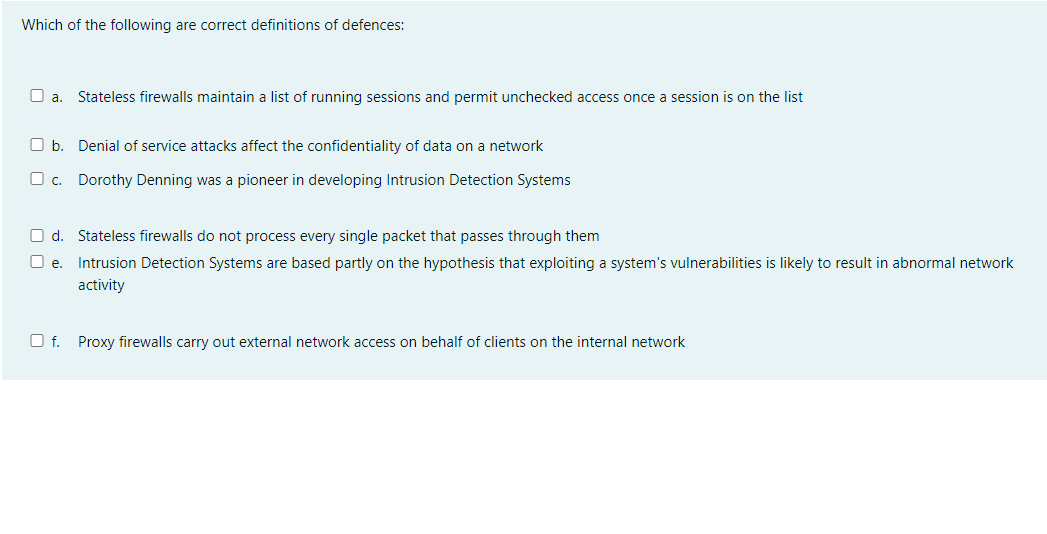
Transcribed Image Text:Which of the following are correct definitions of defences:
O a. Stateless firewalls maintain a list of running sessions and permit unchecked access once a session is on the list
O b. Denial of service attacks affect the confidentiality of data on a network
O c.
Dorothy Denning was a pioneer in developing Intrusion Detection Systems
O d. Stateless firewalls do not process every single packet that passes through them
e. Intrusion Detection Systems are based partly on the hypothesis that exploiting a system's vulnerabilities is likely to result in abnormal network
activity
Of. Proxy firewalls carry out external network access on behalf of clients on the internal network
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

Management Of Information Security
Computer Science
ISBN:
9781337405713
Author:
WHITMAN, Michael.
Publisher:
Cengage Learning,