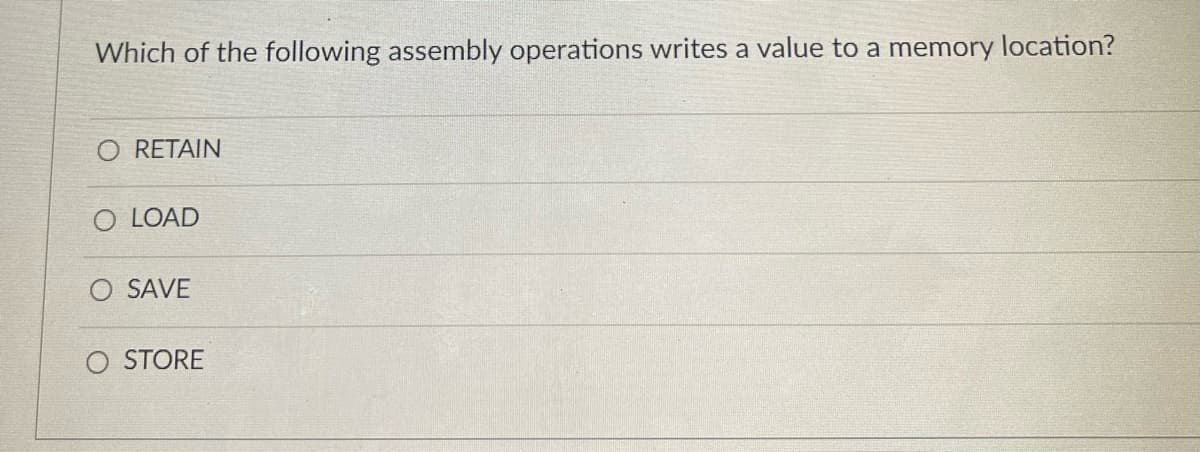
Which of the following assembly operations writes a value to a memory location?
Q: Investigate and make insights from people's reactions to computer and mobile application…
A: Intro Computer and Mobile application problems: People react unfavorably to software flaws that…
Q: the cost per mile for a rented vehicle is one dollar for the first 100 kilometer, 0.8 dollar for the…
A: The solution to the given question is:
Q: please solve question 4 python
A: Here I have created the string and stored it in the variable. Next, I have updated the variable by…
Q: Both the sequential search algorithm and the binary search algorithm have distinct benefits, but…
A: Introduction: Searching in a particular order. There is no need for a sorted list. It can be used in…
Q: What is the type of traffic imposed by this ACL? HTTP HTTPS DNS Telnet FTP
A: What is the type of traffic imposed by ACL?
Q: What exactly is meant by the term "device driver," and how does one work
A: A device driver is an extraordinary sort of programming program that controls a particular equipment…
Q: Methodologies and SDLC are obviously distinct. You may explain the software development life cycle…
A: Introduction: SDL (Software Development Lifecycle) manages projects effectively.
Q: Do you have any recommendations for minimising the network's risk?
A: Introduction: Because of the alarming rate at which internet dangers are multiplying these days, it…
Q: Both the sequential search algorithm and the binary search algorithm have their own set of benefits,…
A: Answer:
Q: Discuss five (5) computer security attacks from within and outside of a firm, as well as appropriate…
A: Introduction: The term "insider threat" refers to the situation in which persons with intimate ties…
Q: Explain briefly the associative memory operation when the argument register A the key register K…
A: Fixed memory can be thought of as a unit of memory where data is stored that can be identified to be…
Q: it comes to multimedia applications, what exactly are they
A: When it comes to multimedia applications, what exactly are they?
Q: You are welcome to submit your own reasons about the importance of computer operating systems and…
A: Answer: The operating system (OS) goes about as a chief for all the I/O gadget, memory, CPU,…
Q: A forensic picture can be copied from a hard drive with a capacity of 1 terabyte to a flash drive…
A: Given: A hard drive is a nonvolatile data storage device that is used to store large amounts of data…
Q: Consider a database that belongs to an airline and employs snapshot isolation for its database…
A: Scenario: Consider a web based airline reservation system with database that uses snapshot…
Q: Q.6/Underline the adjectives in the following sentences. (choose eight only) 1. The clever boy…
A: Answer the above questions are as follows
Q: What characteristics define software engineering as a subfield of engineering, and what…
A: Answer: Software engineering is characterized as a course of breaking down client prerequisites and…
Q: What sets relational database management systems different from non-relational database management…
A: A database management system is a way the data and records and stored, maintained and manipulated.…
Q: There are various essential features and behaviors for descriptive models that we will go through in…
A: DESCRIPTIVE MODEL Descriptive research is a form of research technique that describes all of the…
Q: How similar are the benefits of the cloud computing? What are the risks and challenges of using…
A: The solution to the given question is: Cloud Computing Cloud Computing is the deployment of…
Q: How susceptible are security solutions that are hosted in the cloud to data breaches? If there is…
A: Introduction: The occurrence of a data breach results in an unauthorised person gaining access to…
Q: In what instances, in your experience, would you propose using assembly language code in the…
A: An assembly language is refers to a low-level programming language designed to interface directly…
Q: How did they come up with the phrase "spool" when talking about the output of a printer?
A: The spool is an acronym that stands for concurrent peripheral operations online. Spooling arose in…
Q: 6) The function returns the value of x def my_func (x, p):
A: Algorithm: The algorithm to return the value of xp is: Start def my_func(x,p): y=x**p…
Q: Equipment and people in the same geographic area may communicate with each other over a local area…
A: A local area network is a group of computers and peripheral devices that share a common…
Q: In software development, several models are employed, and the utility of each model varies based on…
A: When starting any new application or software development project, it is important to consider the…
Q: Which QoS model is NOT very resource intensive and provides the highest guarantee of QoS?
A: The answer to the following question:-
Q: A forensic picture can be copied from a hard drive with a capacity of 1 terabyte to a flash drive…
A: Given: The hard drive is a device for storing data that is non-volatile and is used for long-term…
Q: Is it feasible to capture data flows in a number of different ways?
A: A data flow diagram shows how information flows through a process or system. Includes data inputs…
Q: Are you able to mention at least five important distinctions between the usual information…
A: Intro IT Datacenter Security: The physical security of the data structure and its components is…
Q: Estate Property Management is a long-standing family business and has been the only real estate…
A:
Q: What are the applications of Subneting?
A: A subnet or a subnetwork is a subdivision of a single physical network or an IP network. The…
Q: There are various obstacles to overcome before mobile technology becomes a reality. How much money…
A: Web-based services: A web service (WS) is either a service provided by one electronic device to…
Q: What, exactly, is the difference between the design of a computer and the organisation of its…
A: Difference in step 2
Q: Intel P965 Express chipset
A: Hey there, I hope you find my solution helpful.
Q: please solve question 19 python
A: Coded using Python 3.
Q: A) state the difference between MATLAB program and other languages program? B) write a program to…
A: MATLAB Program and C++ Program: MATLAB Program C++ Program It is platform independent language.…
Q: Q2: create a script file to generate NXN matrix in form like: 1 2 1 2 1 21 2 1 2 1 2 1 2 2 1 2 1 2 1…
A: Here we have given a script file to generate NxN matrix. You can find the solution in step 2.
Q: Watchdog clocks are frequently utilised by embedded systems for a variety of reasons.
A: An embedded system is a microcontroller or microprocessor-based system designed for a particular…
Q: The OSI security architecture contains a wide array of advanced precautions to ensure the…
A: Intro The route used by all packets between their source and destination is the same. It is not…
Q: What does the internet of things (IoT) signify in our everyday lives? Consider using an intelligent…
A: IoT stands for the "internet of things," which refers to a network of interconnected,…
Q: Q1:let x = [5 18 9 11 -2 -1 0 13 9 6 2 1]. Use a commands to do the following 1) Set the positive…
A: Answer in step 2
Q: What are the characteristics that set computer systems apart from one another?
A: Computer: A computer is a kind of machine that, in its most fundamental form, operates by receiving…
Q: The deployment of mobile technology involves a number of challenges. Money saved against web-based…
A: Introduction: Mobile technology refers to a sort of technology in which a user performs…
Q: You are going to create a website for your new business, explain all steps to develop an E-commerce…
A: The above question is solved in step 2 :-
Q: { int x, y = 1; For(x=0; x<50; x+ =5) { cout << x << “ “<<y; y ++; }}
A: C++ programming
Q: a reliable data transmission while it is simultaneously operating over UDP? Then, may I ask h
A: In PC organizing, the User Datagram Protocol (UDP) is one of the core members from the Internet…
Q: It is true that we are not responsible for the way in which operating systems carry out the…
A: Answer: An operating system (OS) is the program that, in the wake of being at first stacked into the…
Q: In terms of search algorithms, what is the difference between a BFS (Breadth First Search) and a DFS…
A: BFS BFS or the breadth first search are used to find the shortest path in the unweighted(that have…
Q: User manuals, online assistance, and tutorials may all be classified into one of these three…
A: Intro Manuals: This manual describes the system's operations and capabilities, as well as…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- TASK 2.2:Open Terminal.Type in the following commands and show outcomes:To identify the available CPU, memory, and disk resources, we can used the following commands:cat /proc/cpuinfo (read the CPU information)cat /proc/meminfo (read the memory (RAM) information)df -h ( find out secondary storage (hard-disk) information)Which of the following is a valid name for a memory location? a. dbljan.Salesb. decMarch$Sales c. dblBONUS_RATE d. all of the aboveError: ENXIO: no such device or address, open '/dev/tty' I have another problem when I run the code in "js" const prompt = require("prompt-sync")(); // checking whether it is prime or not function isPrime(n){ if(n <=1) console.log("False"); varc = 2; varbool = true; while(c*c <= n){ if(n % c === 0){ bool = false; break; } c++; } // displaying reuslt if(bool === false) console.log("False"); else console.log("True"); } // entering number var n = prompt("Enter a positive number:"); isPrime(n);
- Q 10 - Which of the following preprocessor directive allows generating a level one warning from a specific location in your code in C#? A - warning B - region C - line D - errorWhich of the following initializes the variable order? a. DECLARE order NUMBER(2); departure DATE;BEGIN ---- executable statements ---END; b. DECLARE order NUMBER(2) = 0; departure DATE;BEGIN ---- executable statements ---END; c. DECLARE order NUMBER(2) := 0; departure DATE;BEGIN ---- executable statements ---END; d. DECLARE order NUMBER(2) =: 0; departure DATE;BEGIN ---- executable statements ---END;The symbol table stores the memory address associated with each variable. What is the memory address of the start_time variable in main()? You only need to fill in the last 2 digits of the address. 0x7ffd949d30__ What symbol was added after the data type of MoveSchedule's start_time and end_time parameters? Place a check (✓) beside your answer. int * & start_time What is the memory address of the start_time variable in MoveSchedule()? You only need to fill in the last 2 digits of the address. 0x7ffd949d30__ What happens to the value of the start_time variable in main() when the start_time variable in MoveSchedule is updated? Place a check (✓) beside your answer. start_time in main remains the same start_time in main gets the value assigned to start_time in MoveSchedule start_time in main changes to 0.
- Which of the following operations should only be allowed to be done when the CPU is in kernel mode? Group of answer choices 1) Read data from a file 2) Open a file for reading, writing, or both 3) Set the time-of-day clock 4) Read the time-of-day clock A programmer opened a file using the file descriptor fd. The file contains the following sequence of bytes: 12, 14, 33, 33, 33, 12, 14, 1, 6, 33, 12, 14, 1, 6, 12 The programmer then uses these two system calls: lseek(fd, 3, SEEK_SET); read(fd, &buffer, 4); note, the lseek call makes a seek to byte 3 of the file. What does buffer contain after the read system call completes? Group of answer choices 1) 33 33 33 12 2) 33 33 12 14 3) 33 12 14 1 4) 33 12 14 In a uniprocessor system, multiprogramming increases processor efficiency by: Group of answer choices 1) All of the above 2) Increasing processor speed 3) Eliminating all idle processor cycles 4) Taking advantage of time wasted by long wait…Please identify the correct statement(s) for the following code snippet from the script: while inst_iter.hasNext() and not monitor.isCancelled(): ins = inst_iter.next() addr = ins.getAddress() pcodeList = ins.getPcode() for pcode in pcodeList: if pcode.getOpcode() == PcodeOp.FLOAT_DIV or pcode.getOpcode() == PcodeOp.INT_DIV: print("Address: {}, Inst: {}, Pcode: {}".format(addr, ins, pcode)) addrSet.add(addr) Question 1 options: It saves the address of the disassembled instruction that introduces division. This snippet uses refined/high p-code. This snippet uses raw p-code. It uses p-code opcode to identify the division operator. It uses the mnemonic string of a disassembled instruction to identify the division operator. It saves the sequence number of the p-code instruction that introduces division.The shortcut command of ‘save’ in MS- WORD is _______________________. Select one: a. Ctrl + C b. Ctrl + S c. Ctrl + A d. Ctrl + V
- Which of the following statements best describes the benefits and drawbacks associated with disk write caching?Which one of the following functions calls is vulnerable to buffer overflow? Choose an answer A fgets() B sprint() C strncat() D strncpy()A process's ID is 5988, what does the following command do? ps -o ppid= -p 5988 and ps -o ppid= -p 5988 a) Display the state of this process b) Display the memory usage of this process c) Display the child processes of this process d) Display the parent process of this process



