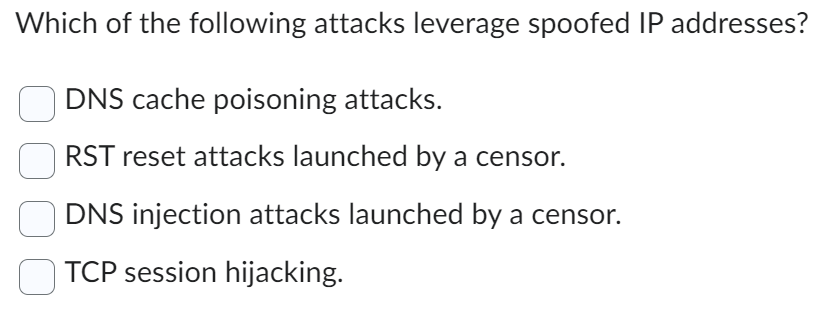
Which of the following attacks leverage spoofed IP addresses? DNS cache poisoning attacks. RST reset attacks launched by a censor. DNS injection attacks launched by a censor. TCP session hijacking.
Q: This is a c language question I do not know how how to make main.c and stock.c along with reporting,…
A: C is used to develop operating systems , web browsers, computer games, and many other applications.…
Q: Can you explain why it's preferable to use DNS as a distributed database rather than a traditional…
A: Introduction: Solution: a distributed domain name and IP address resolving system. Each site updates…
Q: Why don't you name two tools that every system administrator should have?
A: System administrators:- System administrators are responsible for the continued maintenance and…
Q: As a system, how do you define progress?
A: Answers:- I can provide a general definition of progress in the context of systems or organizations.
Q: Which tables does EIGRP utilize, and why?
A: The answer of this question is as follows.
Q: Data flow diagrams may be classified as either "logical" or "physical." A data warehouse cannot…
A: Yes, data flow diagrams can be classified as either "logical" or "physical". Logical data flow…
Q: It's unclear why cache memory is necessary if RAM and cache memory have the same transistor…
A: Although cache memory and RAM share the same basic transistor architecture, they serve different…
Q: Maze Runner Function - Implementation of this function is done in a1_partd.py We describe a maze as…
A: In this question we have to write a maze runner function with a recursive function Let's code and…
Q: the secrets of d
A: "the secrets of dat". Data is simply information that is stored and processed by computer systems,…
Q: What exactly is an anomaly, and how would you define it? Were there really three outliers in the…
A: This topic examines the chance of discovering three outliers in a database as well as the anomalies…
Q: Outline three additional troubleshooting steps to do if the standard debugging steps don't provide…
A: While there isn't a comprehensive process for addressing every fault in your code, there are several…
Q: Do you know of any drawbacks to changing the physical location of a server's data storage?
A: SERVER DATABASE: A database server is, according to the client-server model, a server that manages…
Q: DML refers to the language used to manipulate data. Explain what it is.
A: Introduction: DML stands for Data Manipulation Language and is used to access and modify data stored…
Q: Think about the hole that was just discovered in the system that controls authentication and who may…
A: INTRODUCTION: Authentication: The act of validating the identity of an entity, such as a person, a…
Q: A crucial concept in cryptography is the difference between private keys and public keys.
A: Introduction: private key : Decrypt messages and get to money stored in a digital wallet. A private…
Q: In PYTHON Write a function that prints multiple times a vector from its first element up to the…
A: We have used while loop to print a vector multiple times from its first element to upto the next…
Q: ello. I need help with this: determine whether the given pair of graphs is isomorphic. Exhibit an…
A: In the given two graphs, Set of vertices of first graph= {u1, u2, u3, u4, u5, u6, u7, u8} Set of…
Q: How does Compiler Phases vary from other forms of compilation? Can you provide some examples for…
A: Introduction of Compiler: A compiler is a computer program that translates source code written in a…
Q: Utilize Python Multiprocessing module to perform non-locking parallel array summing on different…
A:
Q: Why is SAS better than SCSI?
A: The choice of interface in high-performance storage applications can have a considerable impact on…
Q: As more and more people rely on mobile devices—which often have less-powerful processors, run…
A: Due to their portability, mobile devices employ Internet-dependent apps. They depend on server…
Q: What are some examples of the many different types of problems that simulation models may possibly…
A: Simulation modelling is the process of creating and analysing a digital prototype of a physical…
Q: Explain the advantages of digital radiology in terms of: Yo. image quality ii. Time saving iii.…
A: Your answer is given below.
Q: While working together, why is it crucial to synchronize processes? A program's critical sections…
A: Answer is
Q: When it comes to creating a distributed database, what are the main differences between a local area…
A: A LAN, or local region network, is a network that covers a small geographic area, such a home,…
Q: Which is better, a.NET DLL or an executable file (EXE)? ?
A: DLL (Dynamic Link Library):- A DLL (Dynamic Link Library) is a type of file that contains a set of…
Q: What role does the data dictionary play in each of the DBLC's six phases?
A: Your answer is given below.
Q: How critical is it that schools employ technology to help pupils learn?
A: How did technology help learn essential topics? Technology in the classroom provides a pleasant…
Q: What infrastructure supports "Cloud Computing
A: Introduction: Cloud computing has become a ubiquitous technology that allows users to access various…
Q: Can you explain the difference between an encrypted password database and a file containing hashed…
A: Yes, I can explain the difference between an encrypted password database and a file containing…
Q: Computers, data networks, and the World Wide Web have proliferated rapidly in recent decades,…
A: What ethical difficulties should be dealt with in relation to computer technology, information…
Q: A notation for describing the form and structure of data, data description language is used to make…
A: Answers:- Yes, that is correct. A data description language (DDL) is a syntax or notation used to…
Q: While doing data backups and recoveries, what do you consider to be the most important…
A: Here are some important considerations to keep in mind while doing data backups and recoveries:
Q: It may be possible to demonstrate that database values may be updated covertly if error detection…
A: A group of numbers generated by certain procedures with the intention of identifying errors in data…
Q: What are some of the most essential considerations while making backups and restoring data?
A: Introduction Restoring data: Recovering lost or damaged info from the backup source is referred to…
Q: What exactly is an anomaly, and how would you define it? Were there really three outliers in the…
A: This topic examines the possibility of detecting three outliers in a database and the resulting…
Q: Adapt your VPython code do the following: Integrate x2 between -1 and 3 between using both the stone…
A: In this question we have to write a python code to integrate x2 between -1 and 3 between using both…
Q: What are the benefits of elliptic curve cryptography?
A: The ECC has several benefits, the most essential of which is that it is just. a more secure…
Q: 27 (base 7) = _______________________ (8-bit Two's complement binary number)?
A: Introduction Each digit in a binary number represents a power of 2, with the rightmost digit…
Q: Do a SQL query using their data format to see who hasn't attended any classes there. Please avoid…
A: SQL command The SQL query to list every student's ID who hasn't attended a university course may be…
Q: Let's pretend a financial institution uses a database management system that provides snapshot…
A: Databases store information. The database organises data for retrieval and analysis. Imagine the…
Q: I have written a class that has the characteristics of the data structure Set and within it house an…
A: Please refer to the following steps for the complete solution to the problem above.
Q: Is there a clear advantage to cloud computing over traditional, on-premises deployments?
A: Introduction : When data on a storage medium cannot be accessed normally, data recovery is the act…
Q: Develop a variation of the hybrid merge-join method where none of the relationships is physically…
A: The merge join and the hybrid merge join are two different concepts. As seen in the merge join…
Q: Now that you have a job managing a database, you may choose to implement either a trigger or a…
A: A database trigger is a particular stored procedure that executes automatically when a database…
Q: To be more specific, what do you mean when you say "metadata"? Metadata, as it pertains to a data…
A: Metadata: Metadata is data that describes other data. It can provide information about a particular…
Q: To what extent can we classify data-structure as a noun? Could you please explain the various data…
A: Data Structure: A data structure, also known as a data element group, is a grouping of data elements…
Q: Specifically, which high-availability DHCP solutions do you believe you would use at your firm, and…
A: DHCP—Dynamic Host Control Protocol—configures IP addresses for network-transmitting systems. DHCP…
Q: How do LANs and WANs differ when it comes to accessing data from a decentralized database?
A: Introduction : LAN (Local Area Network): A LAN is a network that is limited to a small geographic…
Q: To further understand the need of access control and authentication, consider studying a recent case…
A: Access control and authentication are critical components of an organization's security posture.…
The answer is given in the below step
Step by step
Solved in 2 steps

- A spoofed DNS record spreads to other DNS servers. What is this attack called? a. ARP poisoning b. DHCP snooping c. MitM attack d. DNS poisoningWhich of the following layer 2 attacks will prevent an authorized user from receiving a lawful IP address? A MAC address flood B DHCP starvation O C DHCP spoofing O ARP spoofing d.Firewalls: which is true? A packet filter firewall may prevent dangerous files. Packet filter firewalls accept or reject data packets without feedback. Packet filter firewalls inspect all packets. Packet-filtering firewalls may inspect the application layer?
- 1. What is session hijacking2. Why is session hijacking done? 3. What is the difference between session hijacking and IP spoofing? 4. How would an attacker use source routing to hijack a session? 5. How can continuous ACK transfer be stopped? 6. How would an attacker perform TCP session hijacking with packet blocking? 7. What does the command netstat –nra do at a Windows command prompt? 8. What is the default loopback address? 9. Where does a packet go if the address in its destination field is unknown in the route table? 10. What are the two main functions of Hunt? 11. Name five encryption protocols. 12. How common are duplicate packets and retransmission on most TCP/IP networks?22. Checksum, as used in the transport layer, can detect all errors.a. Trueb. False 23. Which of the following protocols cannot be used by a user agent to retrieve email messages fromits SMTP server?a. POP3b. SMTPc. IMAPd. HTTPe. All of the aboveWhich of the following is not a step involved in a session fixation attack? The attacker sends an email to the victim that contains a link with a fixed session ID. The attacker visits the bank website and logs in using their credentials. The victim clicks the link and is redirected to the bank website. The web server sets a session ID on the victim’s machine.
- 8. Write the iptables command:Set firewall http INPUT policy to DROP Set firewall telnet OUTPUT policy to ACCEPT 8.7.3Could someone kindly answer this? Im doing HW and am stuck....... Which term describes an attack that changes URLs in a server's domain name table? Swimming Whaling DNS poisoning VishingAll the following hacking activities can result in session hijacking except for which one? Spoofing Internet Protocol addresses Juggernaut Hunt Smurf
- There are events from different web server logs (see below). What can you tell about each row? What is happening in each row? What might be interesting in case of incident investigation? timestamp="09/Mar/2016:11:14:34 +0300" client_ip="73.9.84.166" user_agent="Debian APT-HTTP/1.3 (0.8.16~exp12ubuntu10.26)" url="/precise-security/stable/amd64/Packages.bz2"[09/Mar/2016:11:14:35 +0300] wiki-api.company-realm.ru 25.255.240.122 "GET /_api/frontend/.is_readonly?=&__uid=1120000000006167 HTTP/1.1" 200 "-" "-" "ivanovaa" "companyuid=5986251411438764783" - 717 0.022 0.022[09/Mar/2016:11:14:35 +0300] fml.company-realm.ru 202a:6b8:b010:2048:0:d0c0:5:12 "GET /rest/v2/call/collectPoolFromQueriesRatings/32b86116-e409-11e5-bdc7-0025909427cc?ticket=3201127 HTTP/1.1" 414 "-" "Apache CXF 3.0.4" "-"[09/Mar/2016:11:14:35 +0300] 127.0.0.1:443 127.0.0.1 "GET /ping HTTP/1.0" 200 "-" "KeepAliveClient" "-" "companyuid=-" - 273 0.146 0.146[09/Mar/2016:11:14:34 +0300] st.company-realm.ru 127.0.0.1 "GET…Which encryption benchmark ensures data is not modified after it’s transmitted and before it’s received? Confidentiality Integrity Availability Symmetric Which remote file access protocol is an extension of SSH? SFTP TFTP FTPS HTTPSStateful inspection firewalls forward subsequent packets (non-first packets) mainly based on what? A. MAC address table B. Session table C. Routing table D. FIB tabl

