Which of the following code snippets represents well-written code and the best desi problem (assume //code here represents valid code)?: *
Which of the following code snippets represents well-written code and the best desi problem (assume //code here represents valid code)?: *
Chapter6: Using Arrays
Section: Chapter Questions
Problem 2CP
Related questions
Question
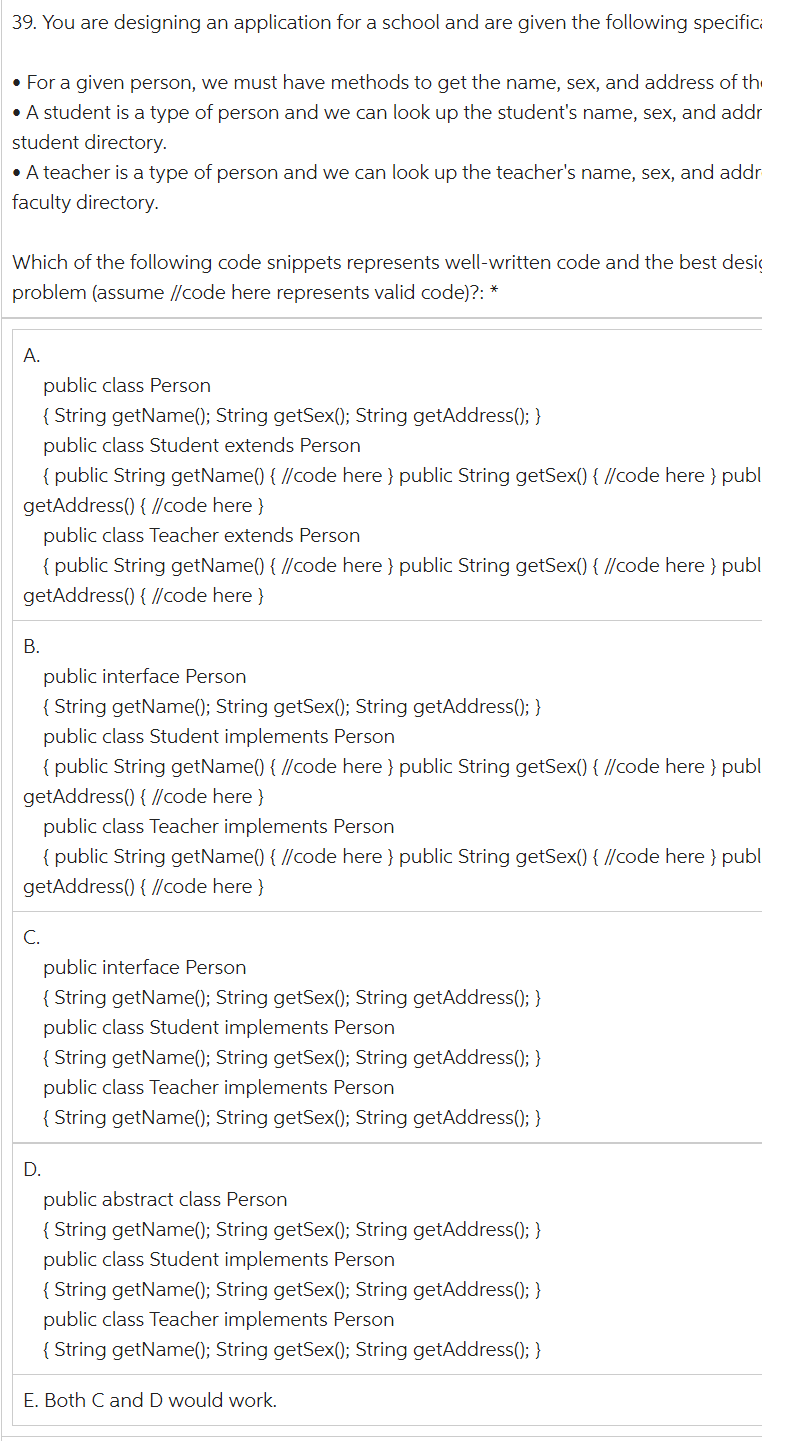
Transcribed Image Text:39. You are designing an application for a school and are given the following specifici
• For a given person, we must have methods to get the name, sex, and address of th
• A student is a type of person and we can look up the student's name, sex, and addr
student directory.
• A teacher is a type of person and we can look up the teacher's name, sex, and addr
faculty directory.
Which of the following code snippets represents well-written code and the best desig
problem (assume //code here represents valid code)?: *
A.
public class Person
{ String getName(); String getSex(); String getAddress(); }
public class Student extends Person
{ public String getName() { //code here } public String getSex() { //code here } publ
getAddress() { //code here}
public class Teacher extends Person
{ public String getName() { //code here } public String getSex() { //code here } publ
getAddress() { //code here }
B.
public interface Person
{ String getName(); String getSex(); String getAddress(); }
public class Student implements Person
{ public String getName() { //code here } public String getSex() { //code here } publ
getAddress() { //code here }
public class Teacher implements Person
{ public String getName() { //code here } public String getSex() { //code here } publ
getAddress() { //code here }
C.
public interface Person
{ String getName(); String getSex(); String getAddress(); }
public class Student implements Person
{ String getName(); String getSex(); String getAddress(); }
public class Teacher implements Person
{ String getName(); String getSex(); String getAddress(); }
D.
public abstract class Person
{ String getName(); String getSex(); String getAddress(); }
public class Student implements Person
{ String getName(); String getSex(); String getAddress(); }
public class Teacher implements Person
{ String getName(); String getSex(); String getAddress(); }
E. Both C and D would work.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT