Which of the following commands update the stack by adding or removing values? Opop command ret command both of them none of them
Q: Multithreading methods are tested on uniprocessor and multiprocessor systems running…
A: On a multiprocessor system, many threads may run on different CPUs at the same time. Consequently,…
Q: Top-down design: have you utilized it? Explain if yes. Discuss at least one top-down design example…
A: Top-down design is widely used in various fields, incorporating computer learning, for…
Q: What problems could occur if an agile software development organization implements structured…
A: The answer is given below step.
Q: s the innovation that started the digital revolution, and why did it start it?
A: The innovation that started the digital revolution was the development of the microprocessor, also…
Q: Are there any key distinctions between the two forms of encryption that you can describe?
A: Encryption is a process of converting plaintext (readable and understandable data) into ciphertext…
Q: What kind of worries and challenges could be brought on by the implementation of a disjointed…
A: The implementation of a disjointed information system refers to a scenario where different parts or…
Q: Example-based real-time OS definition. Differentiate it from a conventional OS. Real-time operating…
A: A real-time operating system (RTOS) is an operating system designed to meet strict timing…
Q: to install and configure a firewall? If yes, what are the steps you should take to get it up and…
A: The question is asking whether it is necessary to install and configure a firewall. If the answer is…
Q: Is it necessary to install and configure a firewall? If yes, what are the steps you should take to…
A: The question is asking whether it is necessary to install and configure a firewall. If the answer is…
Q: What distinguishes cloud storage from other forms of storage are its defining characteristics?
A: Cloud storage is a type of data storage service that allows users to store, manage, and access their…
Q: What precisely differentiates the Screen and Overlay blending modes in Photoshop from one another?
A: Differences between the Screen and Overlay blending modes in Photoshop in tabular format given below…
Q: Data Bus
A: A crucial part known as the "Data Bus" is essential in the complex world of computing because it…
Q: According to the strategy, what are the several ways that information may
A: Information dissemination is an important part of a company's incident response plan concerning…
Q: What exactly is the difference between symmetric and asymmetric cryptography when it comes to the…
A: 1) Cryptography is the science and art of securing information and communication through the use of…
Q: Explanation of cloud computing in its totality, including the benefits of using it: what are they?
A: Cloud computing refers to the delivery of computing services and resources over the internet.…
Q: How do you decide whether a modification should be made?
A: Software modification begins with identifying a need. This call for could occur due to practical or…
Q: What is the difference between a logical subdivision and a subsystem, and why is it important to…
A: Logical subdivision refers to the process of dividing or grouping elements within a system based on…
Q: Explanation of cloud computing in its totality, including the benefits of using it: what are they?
A: Cloud computing is a technology paradigm that involves the delivery of various computing services,…
Q: What practices ensure a secured RESTful web service?
A: A RESTful web service is a type of web service that follows the principles of Representational State…
Q: Local centers should process sensor data. PDA access and a user-friendly dashboard application are…
A: The output of a device that detects and reacts to some kind of input from the physical world is…
Q: Cache memory speeds up software loading in modern systems. Cache memory's function and why it wasn't…
A: Cache memory is a speedy storage area of the computer main memory (RAM).It stores frequently…
Q: In the event of a database system failure, it is necessary to make certain assumptions. Could you…
A: The topic at hand is the recovery techniques used in database systems in the event of a failure.…
Q: A high-level model may generate executable code using model-driven architectures. Examine the…
A: Model-driven architecture (MDA) represents a software design approach that leverages high-level…
Q: In a complete binary tree, every node save the last has precisely two children, and the deepest…
A: Given,In a complete binary tree, every node save the last has precisely two children, and the…
Q: The SOX compliance standard requires IT infrastructure controls and security to protect financial…
A: The Sarbanes-Oxley Act (SOX) is a US federal law enacted in 2002 to enhance corporate governance and…
Q: What kind of technology is behind the cloud's data storage capabilities?
A: Cloud data storage is a sophisticated technology that allows individuals and businesses to store…
Q: Big O category of database execution time? I'll do it. How many deletions per operation? Even for a…
A: The answer is given below step.
Q: Which Event Viewer log would you use to monitor attempted computer logins?
A: To monitor attempted computer logins on a Windows operating system, you would use the "Security" log…
Q: In which of the six steps that make up the DBLC process does the data dictionary play a part?
A: The Data Dictionary plays a significant role in the Design phase of the Database Life Cycle (DBLC)…
Q: An artificially intelligent hospital management system, PEAS (Performance Measure, Environment,…
A: The PEAS (Performance Measure, Environment, Actuator, and Sensor) framework forms the basis of any…
Q: Create a simple cryptocurrency tracker using an API in JavaScript
A: Create an HTML file (e.g., index.html) and add the following code:<!DOCTYPE html><html…
Q: What are the three processes that are considered to be the most essential in the subject of…
A: Cryptography is the learning and practice of safe communication in the presence of…
Q: What does it mean when it is written using the first compound notation
A: Compound memorandum, as the name suggest, is a mathematical notation that unites two or more simpler…
Q: Which Event Viewer log would you use to monitor attempted computer logins?
A: In the realm of computer security, monitoring attempted logins is a critical aspect of safeguarding…
Q: What precisely is meant by the term "chipset," and how does its titular component work?
A: An essential part of electronic devices, particularly computers and mobile devices, is a chipset. It…
Q: How can an Internet of Things system include edge and cloud computing? Where is the database system…
A: A system that uses the internet of things and is linked to an IoT device is referred to as an IoT…
Q: Which network topologies do you think are possible and the most effective?
A: Network topology refers to the arrangement of nodes and connections in a computer network. Different…
Q: What is the correct way to refer to more than one "computer mouse"?
A: A mouse is a corded or wireless device that moves the pointer on your computer as you move the…
Q: What factors contributed to the evolution of computer security into the current state of information…
A: The evolution of computer security into information security has been driven by technological…
Q: How may resistance, acknowledgement, recovery, and reinstatement help system resilience?
A: These variables impact quality planning since they will determine the requirements that must be…
Q: Authorisation lists must be encrypted to prevent tampering. If updated suddenly, what harm may these…
A: Authorization lists are important elements in any system's security framework as they dictate who…
Q: Which approaches are used for defining and putting into practice multiprocessing?
A: There are two main approaches to defining and putting into practice multiprocessing: shared memory…
Q: What is the difference between a relational database management system (RDBMS) that is homogenous…
A: A relational database management system or RDBMS is a software application that allows or enables…
Q: Provide five common network topologies. Which of the three is most reliable?
A: Network topology is defined as the physical and logical arrangement of nodes and connections in a…
Q: Throughout the history of computer science, what are some of the most notable software failures that…
A: Software failures refer to the unexpected and unintended malfunctions or errors in computer programs…
Q: Security management concepts and principles should be explained?
A: 1) Security management refers to the process of planning, implementing, and overseeing measures to…
Q: what do you mean when you refer to "rate limiting"?
A: => An API, or Application Programming Interface, is a set of rules and protocols that…
Q: What steps are involved in submitting a request using HTTP?
A: Submitting a request using HTTP is the process of a client asking a web server for specific…
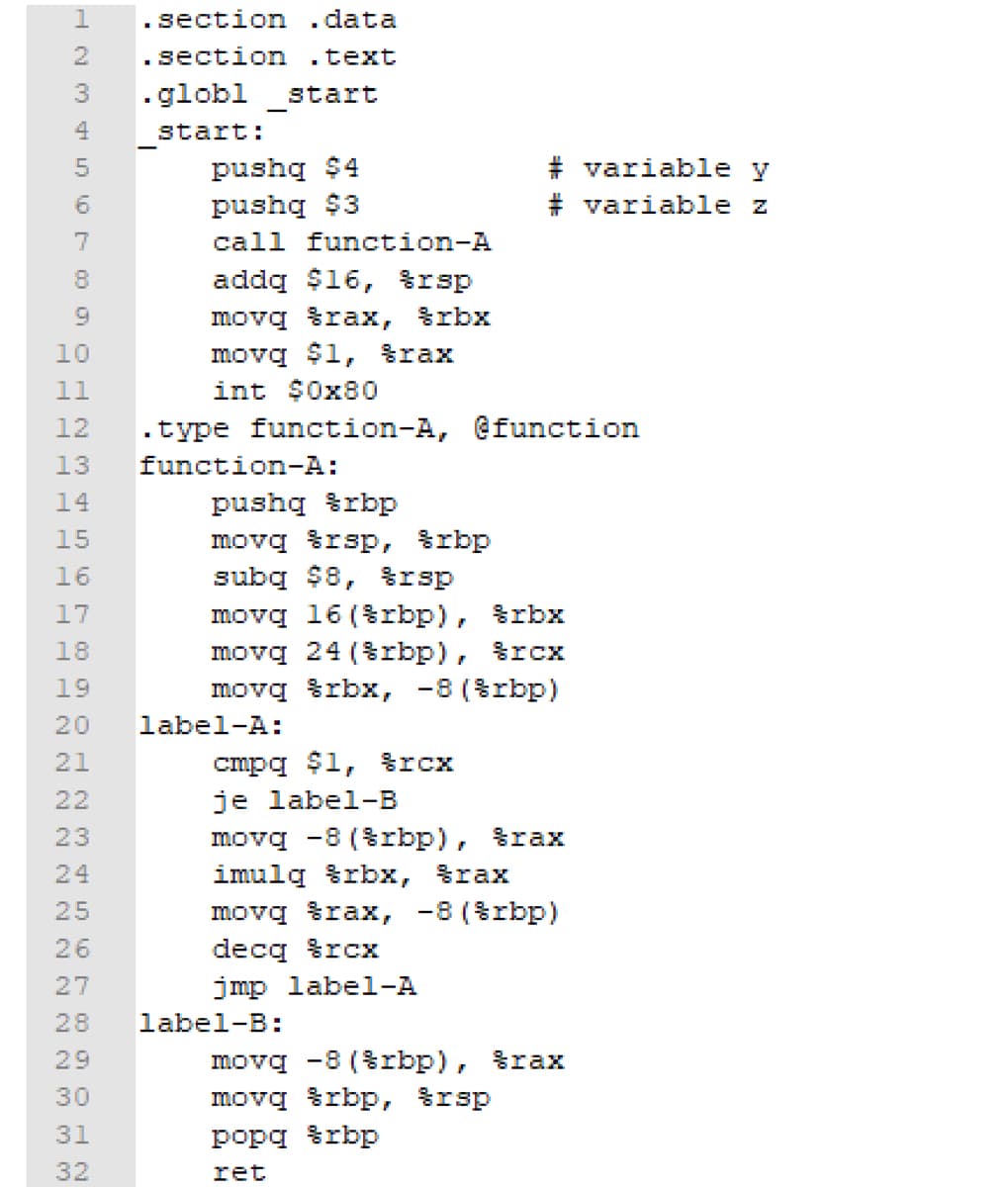
Q: Which of the following commands update the stack by adding or removing values? push command call…
A: The "push" Command: The "push" command is used to push (add) data onto the stack. It decreases the…
Q: What happens when you make a new map entry using a key that already exists on the map and click on…
A: When you attempt to create a new map entry using a key that already exists within the map, the…
Step by step
Solved in 3 steps

- In Dist.txt it will add vaccine in storage like how many vaccines are needed and from where is coming and Add search function in which from user it will check how many vaccines are available in storage this will be done in Vaccine.txt somewhat like in image given #include <stdio.h>#include <stdlib.h>#include <string.h> struct vacc{ char vaccName[15]; char vaccCode[2]; char country[15]; int qty; float population; }v[10]; // Function Declarations void create_inventory(); void update_vacc_qty(); int search_vaccine(); void display_vaccine(); // Main Function starts here int main() { //create_inventory(); //display_vaccine(); //search_vaccine(); update_vacc_qty(); return 0; } //Function to Create Vaccine.txt as per the given table void create_inventory() { int option = 1; // variables to collect data as per table given char vaccName[15]; char vaccCode[2]; char country[15]; int qty; float populaion; //File definition FILE *infile; infile = fopen("Vaccine.txt","w");…Twitter Data: twitter_url = 'https://raw.githubusercontent.com/Explore-AI/Public-Data/master/Data/twitter_nov_2019.csv'twitter_df = pd.read_csv(twitter_url)twitter_df.head() Question: Write the Number of Tweets per Day Write a function which calculates the number of tweets that were posted per day. Function Specifications: It should take a pandas dataframe as input. It should return a new dataframe, grouped by day, with the number of tweets for that day. The index of the new dataframe should be named Date, and the column of the new dataframe should be 'Tweets', corresponding to the date and number of tweets, respectively. The date should be formated as yyyy-mm-dd, and should be a datetime object. Hint: look up pd.to_datetime to see how to do this.IN SCALA COULD YOU COMPLETE THE FOLLOWING FUNCTIONS: // Regular Expressionsabstract class Rexpcase object ZERO extends Rexpcase object ONE extends Rexpcase class CHAR(c: Char) extends Rexpcase class ALTs(rs: List[Rexp]) extends Rexp // alternatives case class SEQ(r1: Rexp, r2: Rexp) extends Rexp // sequencecase class STAR(r: Rexp) extends Rexp // star // some convenience for typing regular expressions //the usual binary choice can be defined in terms of ALTsdef ALT(r1: Rexp, r2: Rexp) = ALTs(List(r1, r2)) import scala.language.implicitConversions import scala.language.reflectiveCalls def charlist2rexp(s: List[Char]): Rexp = s match { case Nil => ONE case c::Nil => CHAR(c) case c::s => SEQ(CHAR(c), charlist2rexp(s))}implicit def string2rexp(s: String): Rexp = charlist2rexp(s.toList) implicit def RexpOps (r: Rexp) = new { def | (s: Rexp) = ALT(r, s) def % = STAR(r) def ~ (s: Rexp) = SEQ(r, s)} implicit def stringOps (s: String) = new { def | (r:…
- please i need this code Flowchart // for residentalconst double Bill_Proc_For_Res=4.5;const double Service_For_Res=20.5;const double Prem_Ch_For_Res=7.5; // for businessconst double Bill_Proc_For_Bus=15;const double Service_For_First10=75;const double Service_For_Add=5;const double Prem_Ch_For_Bus=50; int main(){int Accunt_Num;char Costomer_Code;int Num_OF_Prem_Ch;int Num_OF_Connectors;double Total_bill; cout << "Enter Ur Account number" << endl;cin >> Accunt_Num; cout << "Enter Ur Costomer Code" << endl;cout << "R || r for residental" << endl;cout << "B || b for business" << endl;cin >> Costomer_Code; cout << "Enter How many premiume channel U want" << endl;cin >> Num_OF_Prem_Ch; if (Costomer_Code == 'R' || Costomer_Code == 'r'){Total_bill = Bill_Proc_For_Res + Service_For_Res + (Num_OF_Prem_Ch*Prem_Ch_For_Res);cout << "Ur account Number is: " << Accunt_Num << endl;cout << "The total…Write an application (including algorithm) that uses the predefined functions,“exp” (exponential), “log10” (common logarithm), “fmax” (maximum value), “fmin”(minimum value), and “div” (integer division). The declaration of thesefunctions are contained in either “cmath” or “cstdlib” header files. The application run in a loop until user makes a selection, using a switch statement to determine the choice.given ASCIIOFSET .FILL x0030 NegASCIIOFSET .FILL xFFD0 ASCIINewline .FILL x000d ; Newline ascii code ASCIISpace .FILL x0020 ; Space ascii code ASCIIComma .FILL x002C ; Comma ascii code Use LC-3 I/O device to print number, commas, and spaces in printCommaSpace subroutine, also check code to see if it follows instructions and modify accordingly
- Fix the following code:Dim dblRegularPay As DoubleDim dblOvertimePay As DoubleintRegularPay = 783.87intOvertimePay = 105.92lbl.TotalPay = (dblRegularPay + dblOvertimePay).ToString ('C')Which of the following statement(s) are true for the above code? Group of answer choices the code allocates space for a local variable and a global array the code allocates space for a local variable and a local array The code utilizes the index register the code utilizes the stack pointer the code uses 5 different addressing modesPlaese code in python Create another function count_glorious(low, high) that takes in two positive integers and returns a count of the number of “glorious” numbers between low and high, inclusive. If low is greater than high, return 0. Constraints: count_glorious must contain at least one call to the glorious function from part A. for glorious function refer to the link belowhttps://www.bartleby.com/questions-and-answers/computer-science-question/3b61b8cb-5bda-4d0d-9345-688dd5fb674e
- #include <stdio.h>#include <stdint.h> char sz_1[] = "Upper/LOWER.";char sz_2[] = "mIXeD CaSe.."; /* copies psz_2 to psz_1, downcases all letters */void dostr (char* psz_1,char* psz_2) {uint8_t u8_c; while (*psz_2 != 0) {u8_c = *psz_2;if (u8_c > 0x2F) {/* make sure it is not a special char */*psz_1 = u8_c | 0x20; /* sets this bit */} else {/* leave special chars alone */*psz_1 = u8_c;}psz_1++;psz_2++;} } int main(void) {// Bug: MPLAB X v1.80 printf bug means strings vis %s don't print correctly.// So, break printf into two statements.printf("Before...\n");printf("sz_1: '"); printf(sz_1); printf("'\n");printf("sz_2: '"); printf(sz_2); printf("'\n");dostr(sz_1,sz_2);printf("After...\n");printf("sz_1: '"); printf(sz_1); printf("'\n");printf("sz_2: '"); printf(sz_2); printf("'\n");return 0;}convert it in assembly(This is for devc++ version 5.11) Create a text file with following data to test your code. Please use array of structure and try to use functions and pass array of structures to functions. Read the following data from this text file: Johnson 85 83 77 91 76Aniston 80 90 95 93 48Cooper 78 81 11 90 73Gupta 92 83 30 69 87Blair 23 45 96 38 59Clark 60 85 45 39 67Kennedy 77 31 52 74 83Bronson 93 94 89 77 97Sunny 79 85 28 93 82Smith 85 72 49 75 63 LOOK AT PICTURESwrite one line of code ONLY.Given list below: myNums = [-2, 28, 4, -2, 36, 2] Using the built-in functions, print the smallest value and the largest value in the list, myNums. Just make sure to precisely match the output format below.Write your code in the ANSWER area provided below (must include comments if using code is not covered in the course). Example OutputSmallest = -2Largest = 36



