Which of the following is FALSE regarding a Disk-Oriented DBMS architecture?
Which of the following is FALSE regarding a Disk-Oriented DBMS architecture?
A+ Guide To It Technical Support
10th Edition
ISBN:9780357108291
Author:ANDREWS, Jean.
Publisher:ANDREWS, Jean.
Chapter14: Troubleshooting Windows After Startup
Section: Chapter Questions
Problem 1TC: A user complains that her computer is performing slowly. She tells you the problem started about a...
Related questions
Question
DO NOT COPY FROM OTHER WEBSITES
Upvote guarenteed for a correct and detailed answer. Thank you!!!
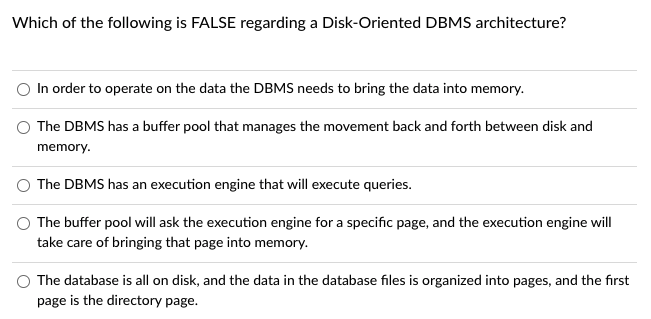
Transcribed Image Text:Which of the following is FALSE regarding a Disk-Oriented DBMS architecture?
In order to operate on the data the DBMS needs to bring the data into memory.
O The DBMS has a buffer pool that manages the movement back and forth between disk and
memory.
The DBMS has an execution engine that will execute queries.
The buffer pool will ask the execution engine for a specific page, and the execution engine will
take care of bringing that page into memory.
O The database is all on disk, and the data in the database files is organized into pages, and the first
page is the directory page.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L