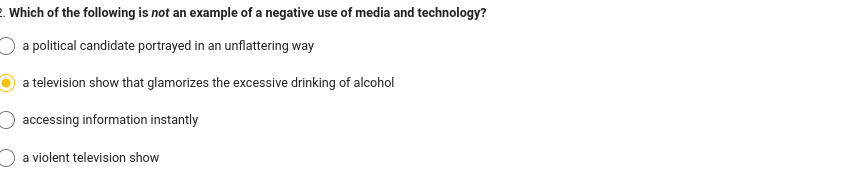
Which of the following is not an example of a negative use of media and technology?
Q: You're social media-savvy. Autonomous cloud computing? Examples show this. Weblogs and cloud…
A: Social media platforms rely heavily on cloud computing to provide users with fast, reliable, and…
Q: Most Internet users are productive. Why is it vital to distinguish telemedicine from telesurgery?
A: 1) Telemedicine and telesurgery are two distinct applications of technology in the medical field…
Q: In the process of developing software, what are the several stages of the waterfall methodology? It…
A: A popular project management technique with a linear approach is the waterfall methodology. In a…
Q: What makes CentOS unique?
A: The answer is given below step.
Q: After jotting down all of the different mathematical operations, arrange them in a logical order.
A: Mathematical operations are important tools for problem solving and making sense of our…
Q: In what ways does the waterfall approach differ from other SDLC models in terms of the stages it…
A: The Waterfall model is one of the earliest software development life cycle (SDLC) models. It was…
Q: following proposition is true QI= truth table, show that the P→ (7->r) # (P→7)->
A: Answer is explained below
Q: Why would it be bad for an email service provider to go through the inbox of one of its customers?
A: Email is becoming a necessary form of communication for individuals and organizations in the digital…
Q: In case of an emergency, be ready in advance. Where do mobile backup solutions and conventional…
A: In today's digital age, data is one of the most valuable assets that individuals and organizations…
Q: Use a computer with physical and logical partitions. Some benefits:
A: In computer systems, logical partitions can offer several advantages over physical sections.
Q: Why may it be a bad idea for email service providers to go through the messages sent and received by…
A: Our daily routines have become increasingly dependent on email service providers (ESPs), which…
Q: Explain why incremental development is preferable to the waterfall method by giving three concrete…
A: Incremental Model Several development cycles are conducted, and each process is broken down into a…
Q: es of the software development life cycle (SDLC) models does the waterfall technique incorporate?…
A: The Waterfall model is a linear and sequential approach to software development, where each stage of…
Q: You could pick the waterfall approach over a more modern one. Choose a contemporary flexible…
A: The Liner Sequential Life Cycle Model, often known as the Waterfall Model, is a modelling technique.…
Q: How should Web application components communicate data?
A: A web application is any piece of software that is hosted on a web server and accessible through a…
Q: Operating systems' process execution is uncertain
A: Yes, the process completed in an operation can be unbiased due to many factors. These can include…
Q: DMA may boost system concurrency, but how? What inhibits technological progress?
A: Computer systems employ direct memory access (DMA) as an approach of data transmission amongst…
Q: What are the benefits of carrying out medical research over the internet? What technical advantages…
A: Medical research and therapy are two critical parts of healthcare that have been significantly…
Q: Explain the advantages that come with the middleware that is offered by the operating system. In…
A: 1) Middleware is software that resides between applications and the operating system, and provides a…
Q: Find out which sectors make use of web technology and what challenges they face in terms of…
A: Web technology is used by many different businesses, including e-commerce, finance, healthcare, and…
Q: You're social media-savvy. Autonomous cloud computing? Examples show this. Weblogs and cloud…
A: Cloud computing: It provides a flexible, scalable, and economic Internet-based computer services.…
Q: Please explain why challenge-response authentication is needed. Password solutions are far less…
A: Challenge-response authentication is a more secure way of verifying the identity of a user compared…
Q: Is it true that some types of systems benefit more from the use of agile development approaches than…
A: Yes, it is true that some types of systems benefit more from the use of agile development approaches…
Q: Provide an illustration of how a distributed system could profit from shared software resources.…
A: Distributed System is a collection of autonomous computer systems physically separated but connected…
Q: Several things might impact network functioning.
A: The functionality of a network may be affected by many things, from hardware to software settings.…
Q: Assess how wireless technology affects underdeveloped countries. Why establish wireless networks…
A: The concept of "wireless technology" emphasizes the use of wireless transmission to send data…
Q: The most significant aspect of implementation development is the creation and adherence to the…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Consider your project in light of the article's example and decide whether waterfall is right for…
A: The Waterfall technique, a type of project management, is frequently used to oversee the software…
Q: By using the DJNZ command and indirect addressing, create the data given below to the addresses…
A: The 8051 microcontroller is an 8-bit microcontroller designed in 1980 by Intel for use in embedded…
Q: What is Turing Test? How to pass it?
A: Turing test It is a test to see if a computer can "think" and communicate like a human being. The…
Q: Think about the advantages and disadvantages of adding a gateway to your network.
A: A network is a group of two or more computers that can talk to each other and share information and…
Q: RANK(t, x) rank = 0 while (t#x) if (t.key < x.key) if t.left # NIL rank += t.left.size rank++ t =…
A: In this question, we were given an algorithm named RANK(t,x), which returns the rank of a given node…
Q: In this section, you will find an explanation of the idea of a computer's environment, as well as an…
A: A computer's environment is the combination of its hardware, software, and other components that…
Q: Can the Internet help programmes in many ways? These services vary significantly.
A: The world of programming has recently been significantly impacted through the internet, which has…
Q: Explain several methods for getting software, such as offline and online software development…
A: While online software requires an internet connection, offline software does not. Offline software…
Q: Do IT pros worry about email encryption from an ethical standpoint?
A: Here is your solution -
Q: The Step-by-Step Guide to Creating an Active Directory and Configuring DNS in Windows 2008
A: Windows Server 2008 is a server OS developed by Microsoft and part of the Windows NT family. On…
Q: The waterfall technique covers what stages of SDLC models? You may find answers to your questions…
A: The waterfall technique covers the stages of the Software Development Life Cycle (SDLC) model in a…
Q: Expansion or new features may result. Provide instances to distinguish the two ideas. How can you…
A: In any software development project, there are two possibilities that may arise: expansion or the…
Q: Explain the R, J, and I directions. Much appreciated. This page describes instruction set types,…
A: 1) In computer architecture, an instruction set architecture (ISA) defines the machine language…
Q: Modulation is the process of: a. converting a digital signal to analog. b. altering the amplitude…
A: Modulation is defined as the process of superimposing a low-frequency signal on a high-frequency…
Q: Explain why incremental development is preferable to the waterfall method by giving three concrete…
A: Software is built and delivered gradually, in manageable bits or iterations, using the incremental…
Q: Why is it more probable that the content of an email may be misconstrued, and what factors…
A: Dear learner, hope you are doing well. I will try my best to answer this question. Thank You!!
Q: See past, current, and future computer setups here.
A: According to the data provided: Past, current, and future computer setups must be defined. Different…
Q: please do fast i will give you thumns up Discussion: Social Engineering Attacks Social…
A: An attack is a deliberate and intentional action taken by an individual or group to harm, damage, or…
Q: To summarize, while no security solution can provide perfect protection, applying a combination of…
A: The answer is given below step.
Q: Create an expansion of the structure. MyVector is a new vector that has the sort technique. The…
A: Here's an expanded version of the steps: Define a new class called MyVector as an extension of the…
Q: How may internet tools improve health? What makes telesurgery different from telemedicine?
A: How may internet tools improve health? What makes telesurgery different from telemedicine answer in…
Q: Comprehending the project better may be accomplished by drawing its map with and without the…
A: Creating a project map can be a useful way to visualize and understand the various components of a…
Q: What distinguishes real-time and non-real-time computer operating systems?
A: Operating systems (OS) are software programs that run on a computer and manage its hardware…
need correct answer plz
Step by step
Solved in 3 steps

- Describe the basic concept of freedom of speech. Relate freedom of speech to the Internet. Articulate both sides of the video game violence affecting actual violence debate, and discuss solutions that do not violate the First AmendmentThe use of the Internet has evolved to the point where it is now an indispensable instrument for exercising one's right to free speech. It's standard practise for people to use hate speech to spread on social media platforms like Facebook and Twitter. Should there be no restrictions placed on the right to free speech for those who use the internet? The operators of social media platforms need to carefully assess the extent to which they may cut down on the number of negative comments they publish.kindly answer 1 and 2 What is informational privacy and why are certain aspects and uses of Internet search engines controversial from a privacy perspective? What is informational privacy and why are certain aspects and uses of Internet search engines controversial from a privacy perspective? What are some of the arguments used for and against the use of technology to monitor employees? Explain with the help of suitable examples.
- The use of the internet is now required in order to properly exercise one's right to freedom of expression. A significant number of individuals and groups are using social media platforms to disseminate hate speech. Should there be any limits placed on the right to free expression online? How can internet platforms make certain that obscene or nasty comments are not posted?Which of the following is not an example of Personally Identifiable Information? A. Education and employment history B. Your browsing history for a hotel lobby computer which doesnt verify your identity or room number C. Website cookies placed on your laptopD. Government identifiers such as Tax ID number or passportThe first week of October of 2021 was full of news about Facebook. First related to Facebook, Instagram, and WhatsApp blackout, then the Facebook whistleblower testifying to Congress. The attached article from The New York Times discusses the possible threats to the tech giants caused by not following the ethical values set by society. Much more information is available on how Facebook controls information and misleads the public (e.g., CBS News). Based on the article and other sources (maybe from your favorite news lines), think about the importance of ethical behavior for the tech industry and address the topic in an essay of 1200 -1300 words. In your essay: Bring the update of the current situation with Facebook and the accusations made by Frances Haugen. Identify the ethical dilemma and negative and positive rights involved in the case. Try to stake out a position but be sure to discuss arguments for both sides. Answer the following questions: Should Facebook control the…
- which among the following is not a privacy harmInternet access is now required for exercising one's right to free expression. A vast number of individuals and groups use social media to disseminate hate speech. Should limitations be placed on online free speech? How can internet platforms prevent the posting of abusive comments?The CAN-SPAM law applies to commercial email; political messages are exempt. Present argumentsthat laws to restrict or regulate spam should treat both categories of bulk email the sameway. Present arguments to justify different treatment of these two categories.
- Which one of the following best describes Restitution? a. Legal obligation of an entity extending beyond criminal or contract law b. Fixed moral attitudes or customs of a particular group c. Compensate for wrongs committed by an organization or its employees d. Body of expectations that describe acceptable and unacceptable employee behavior’s in the workplaceCreate a 10 commandmets that would serve a a guide and warning for people when using the technologies specifically the internet. The commandments should be in relation with digital citizenship.In recent years, the Internet has swiftly developed into a crucial instrument that may be used by individuals to exercise their right to freedom of speech as guaranteed by the First Amendment. Some people are spreading hate speech via social media platforms like Facebook and Twitter. This is an unfortunate reality. Should there be no limits placed on people's ability to express themselves freely on the internet? What measures need to be taken by social media platforms in order to stop the propagation of anti-Semitic content?



