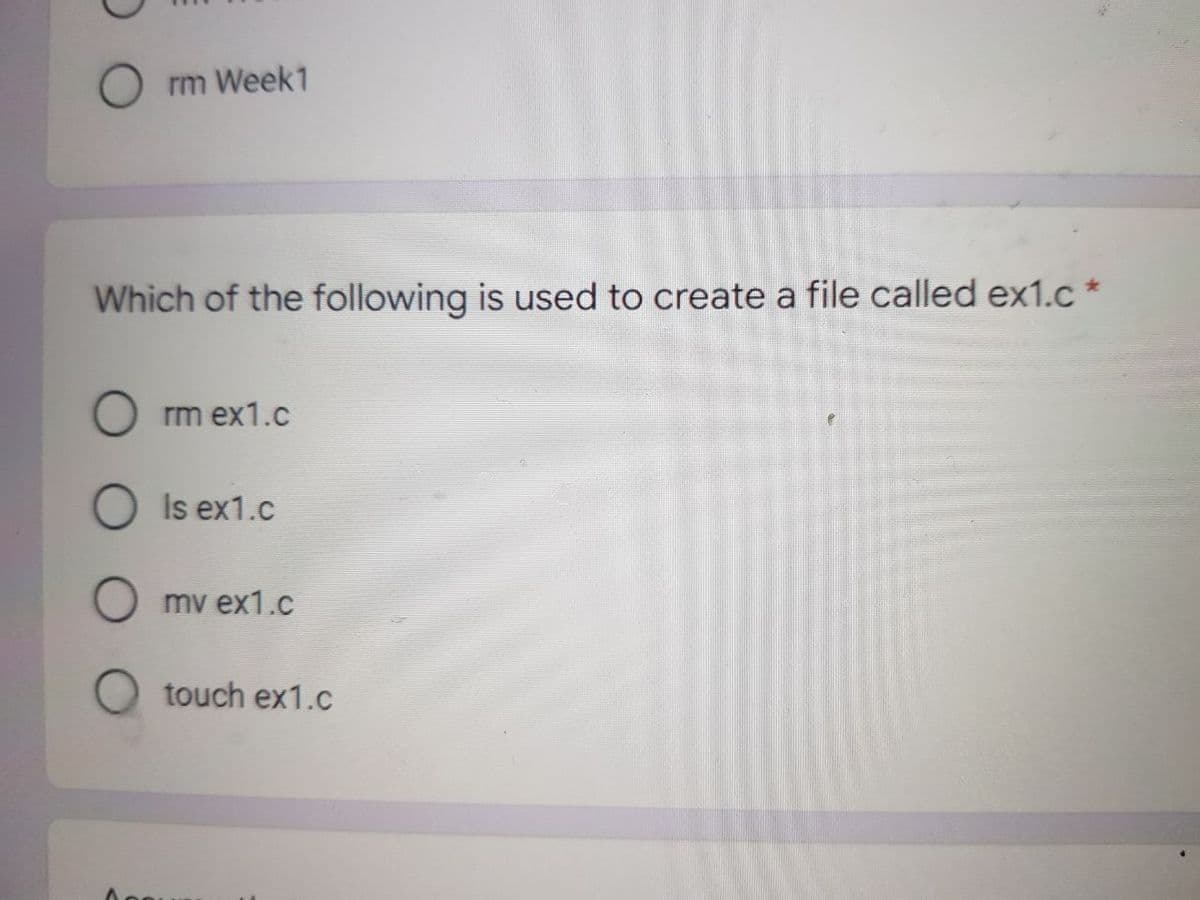
Which of the following is used to create a file called ex1.c O rm ex1.c O Is ex1.c mv ex1.c touch ex1.c
Q: VII.Let A = {2, 4, 6, 8}, B = {6, 9}, C = {4, 8}. Answer each of the following questions. Justify yo...
A: Find the answer with explanation given as below :
Q: What is defensive programming, and what are some of the ways in which we, as programmers, can be def...
A: Introduction: A computer program is a set of instructions that are run on a computer to do certain t...
Q: Computer science What is the meaning of the abbreviation GSM? What exactly is the purpose of your s...
A: Introduction: A subscriber identity module, or SIM card, is a smart card that holds identification i...
Q: c++ Write a class named TestScores. The class constructor should accept an array of test scores as ...
A: Answer : Please Find the Code in C++ below In Step 2:
Q: In system development, a complete and clear software requirements specification might not always be ...
A: User will be having the option to add new items. It can be done by name, expiration date, quantity.
Q: In cryptograms, each character is encoded into another. If the text is long enough, one can, as a st...
A: Hi, Here we can write a java code for this and will give the output based on the text given in it. ...
Q: What is the benefit of utilising hyperlinks instead of keyboard shortcuts to move about your present...
A: Introduction: A hyperlink is an electronic connection that allows you to go from one location to ano...
Q: Please create an introduction and conclusion for your lap report regarding data transfer utilising e...
A: Introduction to External Memory Data TransferData is sent between the microprocessor and I/O devices...
Q: Write a PL/SQL script to display two outputs on the screen: 1) the most recent registration date and...
A: Answer 1) SELECT Registration_Date FROM STUDENT ORDER BY Registration_Date DESC LIMIT 1;
Q: 2. Write a single linux command to find the file(s) and line number(s) where the string: "using std:...
A: The command is
Q: Given a (general) tree below: a) Convert the given tree to a binary tree and draw your result, based...
A: Here are the steps to follow to convet general tree to binary First target all the leftmost node...
Q: Is it possible for a BGP router to always pick the loop-free, shortest ASpath route? Make an argumen...
A: Border Gateway of Protocol (BGP): BGP (Border Gateway Protocol) is an Inter-AS routing protocol that...
Q: What are the advantages of using cloud computing services? What are the risks and issues associated ...
A: Intro With cloud computing, you may have computer resources like servers and storage and databases ...
Q: What is the aim of the section General Declarations?
A: Introduction: The section of a form or standard module is devoted to general declarations. This port...
Q: What exactly is machine language, and how does it function?
A: Introduction: It's all in the code! It is possible for a computer to read, interpret, execute, and r...
Q: What is separable programming and how does it work?
A: Separable programming is a technique for addressing nonlinear problems that is approximate. It is a ...
Q: Write a C program that generates a sequence of random integers between -92 and 93, and find the maxi...
A: First we will generate two numbers and find min and max between them. If one of the numbers generate...
Q: When is it appropriate to build software in a weakly typed language rather than a strongly typed one...
A: Strongly typed languages : If once a type is assigned to a variable either at run time or compile ti...
Q: In the following instruction sequence, select the values of the Carry, Zero and Sign flags where ind...
A: (a) CF=0, ZF=0, SF=0(b) CF=1, ZF=0, SF=1
Q: Write the logic and a C program to input a number from user and print multiplication table of the gi...
A: Given :- Write the logic and a C program to input a number from user and print multiplication table ...
Q: The design commonly used in one residential community is of majestic doors and windows. In this comm...
A: It is defined as the rate of change of a quantity y with respect to another quantity x. A derivative...
Q: Computer science What are the advantages of utilising containers to replace virtual machines?
A: Introduction: Using a hypervisor, we can run many operating systems on a single computer via virtual...
Q: Would you be willing to utilise the internet today as a resource to help usher in a new era of inven...
A: Introduction: Would you use the Internet to bring in a new era of innovation
Q: Write a PL/SQL script to display two outputs on the screen: 1) the most recent registration date an...
A: Introduction: PL/SQL is a strong database programming language that is very simple to learn. It's si...
Q: choose the correct answer A PDA machine configuration (q.w.y) can be *trepresented as (unprocessed i...
A: Question 1: A PDA is defined as a finite machine that has additional stack storage. Its transitions...
Q: Write a C++ class to represent an Employee. Each employee is given a name, an age, a NIC number, an ...
A: Find the required code in C++ and output:
Q: Which instructions executes a branch based on the contents of ECX? JECX JMP LOOP
A: JECX instructions executes a branch based on the contents of ECX.
Q: Consider the int Array below and determine the values of A and B so that Array[0] has an integer in ...
A: The question is to find the values of A and B.
Q: I am trying to implement . I don't know what I should pass for the currPos and newPos when I call h...
A: handleDrag : If you want tags to be draggable, you need to provide this function. Function called wh...
Q: Derive 3 strings in the CFL given by the CFG G = (V, E, S, P) where P = {S → aSa | AB A → a B > bBb ...
A: Given language is, S→aSa|ABA→aB→bBb|b The variables presenat in the language are S, A and B. The ter...
Q: Apply the linear time operation to make a min heap to the following array: 10, 3, 12, 6, 2, 11, 1, 4...
A: def heapify(li, n, i): largest = i right = 2 * i + 2 left = 2 * i + 1 if righ...
Q: Implement a Python program that solves N-Queens problem that retrieves a natural number n as an inpu...
A: Python program to solve the given problem is below.
Q: Given 3 (disjoint) binary trees with total 28 nodes, what is their total number of edges? Оа. 25 оь....
A: We need to answer:
Q: the several types of cybercrime and the consequences of each Determine the most efficient cybercrim...
A: Introduction: a) Cybercrime may be divided into two categories.Type I is the most common. Advance Cy...
Q: What is the issue domain that the workflow management system is designed to solve?
A: INTRODUCTION: Workflow management system: Workflows are the fundamental components of business proce...
Q: What are the commercial implications of the cloud computing movement? Do you know how to work well w...
A: Intro Cloud computing might be a general term that involves delivering hosted services over the web...
Q: Which statement performs overwriting .2 ?assignment x=h+1 O h=e+1 0 e=h+2 X=x+1
A: According to the information given:- We have to choose the correct option to satisfy the statement. ...
Q: s it feasible to accomplish any of our goals with the aid of authentication? In this part, we'll loo...
A: Intro To-Do: Make a list of the advantages and disadvantages of different authentication techniques...
Q: Write the implementations of functions copy1 and copy2 for copying strings. copy1 uses array index n...
A: Algorithm: Start Implement a method named copy1() that takes two strings s1, s2 as arguments Inside...
Q: Describe what a hashing algorithm is in your own words. What is it, how is it used in digital forens...
A: An algorithm is set of instructions which is used to achieve a particular goal. Security is very imp...
Q: What is a virtual desktop, and how does it work?
A: Introduction: The virtual desktop is a technique for grouping accessible groups of Windows to execut...
Q: Describe the container of the active directory system in your own words. Any four elements of the co...
A: Introduction: Every network component is treated as an object in Active Directory. Objects may also ...
Q: If you enter an expression in the Command Window that does not contain an equal sign, MATLAB will ev...
A: Introduction True is the correct answer Explanation Because Matlab will store the result in a speci...
Q: Why are watchdog timers required in such a large number of embedded systems?
A: let us see the answer:- Introduction:- Watchdog timers are a way of informing a system or restarting...
Q: Which authentication method is used when you want a client to be authenticated for each session?
A: A. Session authentication
Q: Fc for F.
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 QUESTION. YOU CAN RESUBMIT THE QUESTION AGAIN ...
Q: What role does the internet play in the lives of people with impairments, both physical and mental? ...
A: Intro The internet has a positive impact on the lives of persons with disabilities. They may choose ...
Q: Write and Create a dictionary code in swift
A: Swift is just a programming language that is initially designed by the apple team for the IOS and ap...
Q: operation of combining two strings .4 . . called mixing merge adding concatenation
A: Find the answer given as below :
Step by step
Solved in 2 steps

- 372. To use information stored in a file, it must be a. Accessed into computer memory b. Read into computer memory c. Retrieved from computer memory d. Both a and bComputer Science Hello I have a Powershell question but my answer doesn't seem to work. The answer columns are where the blank contents are supposed to be filled Before you begin, create a new text file located in C:\MyTextFile.txt, add ten lines of text to it, and save the file. Complete the PowerShell script below by filling-in the missing information so that the script will satisfy the following requirements: Read the contents of the text file you created earlier. Using a while loop, display each line of text one line at a time in the console window. Solution Clear-Host Answer = Answer Answer = Answer Content -Path 'C:\MyTextFile.txt' Answer ( $lineNumber Answer le $fileContents.length ) { Answer line = $fileContents[ Answer ] Write-Host "Line $lineNumber Contents: Answer " $ Answer + } This is what I have so far for my answer Clear-Host $lineNumber = 0 $fileText = Get-Content -Path 'C:\MyTextFile.txt' while ( $lineNumber -le $fileContents.length) {…Python Question: Which statement correctly opens an existing file if you want to add lines to it? A. open('data.txt', 'a') B. f = open('data.txt', 'append') C. f = open('data.txt', 'a') D. data = open('data.txt', 'w')
- 111. Which of the following file types has the least life? a. Work File b. Master File c. Program File d. Transaction FileWhat is a file’s read position? Initially, where is the read position when an input file is opened?Answer the given question with a proper explanation and step-by-step solution. Write a function named file_sum that takes as a parameter the name of a text file that contains a list of numbers, one to a line, like this:```23.7711694-12.8014.999```The function should sum the values in the file and write the sum (just that number) to a text file named sum.txt.The file must be named: **file_sum.py**
- C++ Calculate the sum of one column from a txt file, Please do read the question carefully Below is some information in a txt file 249,V,R,5287,250,M,A,2941,251,M,R,7552,252,M,C,6723, How do I use c++ to read this text file and get the sum of the 4th column(last column) with follow #include #include <iostream>#include <iomanip>#include <string>#include <vector>#include <fstream>COMPLETE TO DO's (do not copy other responses to this question if you do ill downvote) recv.cpp #include <stdio.h>#include <stdlib.h>#include <string.h>#include <fcntl.h>#include <mqueue.h>#include <sys/stat.h>#include <sys/types.h>#include <sys/mman.h>#include <unistd.h>#include <signal.h> // The name of the shared memory segment#define MSQ_NAME "/cpsc351queue" // The name of the file where to save the received file#define RECV_FILE_NAME "file__recv" #define MQ_MSGSIZE 4096 /*** Receive the file from the message queue*/void recvFile(){ // TODO: Define a data structure // of type mq_attr to specify a // queue that can hold up to 10 // messages with the maximum message // size being 4096 bytes // The buffer used to store the message copied // copied from the shared memory char buff[MQ_MSGSIZE]; // The total number of bytes written int totalBytesWritten = 0; // The number of bytes written int…3. Write a function which reads an already existing file “File1.txt” and write digits (0-9) in to a new text file “mynumber.txt” and non digits into a file “Text.txt”.in c++
- Choose the correct answer after considering the following statements: I. A using namespace directive should never be in a .cpp file because that .cpp file could be included in another source file. II. A using namespace directive should always be used in a .h files. III. Namespaces help differentiate functions, variables, and types with the same name. Group of answer choices a. Only III are true b. Only II and III are true c. Only I is true d. Only I and III is true e. Only II is trueFind the error in each of the following program segments and explain how to correct it.a) The file referred to by fPtr ("payables.dat") has not been opened.printf(fPtr, "%d%s%d\n", account, company, amount);State which of the following are true and which are false. If false, explain why.d) If the file position pointer points to a location in a sequential file other than the beginningof the file, the file must be closed and reopened to read from the beginning of the file.





