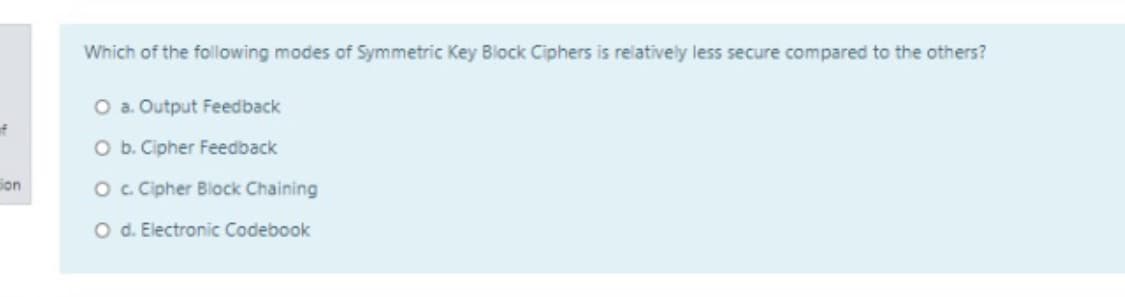
Which of the following modes of Symmetric Key Block Ciphers is relatively less secure compared to the others? O a. Output Feedback O b. Cipher Feedback Oc Cipher Block Chaining O d. Electronic Codebook
Q: The ciphertext OIKYWVHBX was produced by encrypting plaintext message using the Vigenère cipher with…
A:
Q: In the context of the EIGamal signature, the public key is (499, 185, x), where "x" is not known to…
A: Given:
Q: Your colleague sent to you a message which is encrypted using a Playfair cipher, with key…
A: Playfair cipher is a symmetric encryption technique which is also known as playfair square. Steps to…
Q: Which one of the following is an example of substitution cipher? a. Rail Fence cipher b. Caesar…
A: Here, Four examples are given.
Q: 1. Which of the following public key cryptosystem application can be used by RSA? O a. Key exchange…
A: RSA: It is a public key cryptosystem used for secure data transmission. It is asymmetric…
Q: Which of the following are requirements of secret-key cryptography? Select all that apply. O a)…
A: given data:- which of the following are requirements of security key cryptography? Select all that…
Q: Which is an advantage of symmetric key encryption? Strength Speed Error correction Key management…
A: As I have read the guidelines I can provide answers to only 3 parts of the questions in case of…
Q: Which of the following is NOTa characteristic of the Trusted Platform Module (TPM)? It includes a…
A: Introduction: Which of the following is NOT a characteristic of the Trusted Platform Module (TPM)?It…
Q: Which Cipher is used to resolve the issue with Mono alphabetic Cipher NOTE: Answer the above…
A: Monoalphabetic ciphers: Monoalphabetic cipher its is a substitution cipher and each plain alphabet…
Q: which of the following ciphers is more secure O a. DES cipher O b. 2DES O C. double Affine cipher O…
A: In cryptography, security is most important things otherwise data will no longer safe.
Q: Which of the following are a requirement for a secure One-Time Pad? Lütfen birini seçin: O A. The…
A: Requirements for the one time pad will be: The key must be truly random. The key must be at least as…
Q: Which mechanism most directly prevents a user from spending the same cryptocurrency more than once…
A: According to the information given:- Blockchain technology is something new in the past few years.…
Q: Which of the following mechanisms offers slowest performance compared to others? O a. Digitally…
A: All the processes are of same service, so they have equal performances.
Q: This is an older authentication protocol that uses UDP and does not encrypt the stream. Group of…
A: This is an older authentication protocol that uses UDP and does not encrypt the stream. TACACS + and…
Q: Kerberos uses which of the following for authentication? Select one: a. challenge mechanism…
A: Among many computer network security one is Kerberos. It is used to authenticate service requests…
Q: A) Encrypt the plaintext: "internet" using the Autokey cipher with the key "control". B) Encrypt the…
A: Given:
Q: Which of the following is used to determine encryption key material and security protection for use…
A: Encryption key:A random string-based key used to encrypt and decrypt data. These keys created by…
Q: I know how the Playfair cipher works. I would like to know how to find the keyword of the Playfair…
A:
Q: 5. Which of the following application is not one of the public key encryption categories? a. Digital…
A: Applications of public key encryption: ✓Encryption /decryption: The sender encrypts a message with…
Q: If each user in a group of 12 people wants to communicate secretly and bidirectionally with each…
A: Asymmetric Encryption consists of two cryptographic keys known as Public Key and Private Key. The…
Q: George is sending an email to Marsha. Which key is used to encrypt the email for confidentiality?…
A: To which key is used to encrypt the email for confidentiality.
Q: What type of key is used in symmetric cryptography, must be known by both parties, and is used for…
A: Symmetric cryptography (Symmetric-key encryption):It is an encryption technique in which a single…
Q: NOT correct?
A: Not correct about the AES cipher and about the block cipher operational modes
Q: Following the notation seen in class, we have a block cipher that is chained in this way: = Pe XOR…
A: MAC assist block chaining message authentication (CBC) residue. MAC also assists the continuous XOR…
Q: Signed by same ephimeral key Key ? long 1. How cam 2 Messages m.,m2 Mecoven the torm
A: Given question:-
Q: Moving to another question will save this response. Question 1 Explain why symmetric encryption…
A: Encryption is a technique which changes original text into scrambled text using some key. This way…
Q: Give detailed reasons to you friend why you think using vernam cipher encryption algorithm is the…
A: Here two friends are sending messages over internet and they decided to encrypt the messages. One of…
Q: Q1) Which encryption method is better: stream cipher or block cipher and why?
A: ANSWER:-
Q: Which of the following is an example of homophonic substitution ciphers? a. ROT-13 b. OTP c. None…
A: Homophonic Substitution Ciphers maps the plain text to various ciphertext symbols and this makes it…
Q: Which of the following is a true statement about the use of public key encryption in transmitting…
A: Correct option:D
Q: Which of the following is a problem in the Caesar cipher encryption mechanism Lütfen birini seçin: O…
A: A Caesar cipher is one of the least complex and most broadly known encryption methods. Algorithm:…
Q: One type of cryptographic algorithm splits the plaintext into equal sized parts before mixing in the…
A: Below is the simplified answer to the given MCQ problem:
Q: which one of the following is correct the Encrypt of "class is over felows" using Caesar cipher with…
A: In Caesar cipher technique, each letter is replaced by number of positions said in number of shifts.…
Q: Which encryption benchmark ensures data is not modified after it’s transmitted and before it’s…
A: Answer 2. Integrity is the right Option Explaination: Data integrity guarantees that the data…
Q: In which cryptography technique, sender and the receiver use different keys?.
A: Because asymmetric key cryptography is also known as public key cryptography in which it utilizes…
Q: Which of the following are symmetric key ciphers? Select all that apply. DES RSA Diffie-Hellman OAES…
A: According to question i give you all correct answer in step 2
Q: Which of the following symmetric key encryption ciphers provides the strongest protections O DES AES…
A: Given:
Q: Which of the following types of random number sequences are better for generating strong…
A: Explanation: The length of the sequence period and the seeds have no effect on the key strength.…
Q: 2. Which of the following is an example of substitution cipher? O a. AES O b. Rail Fence cipher O c.…
A: c) Caesar cipher The correct option is c)
Q: The theme of many of these questions reveals the key used in a Vigenere cipher to produce…
A: Vigenere Cipher is a technique for scrambling alphabetic text. It utilizes a basic type of…
Q: Write half a page on each of the following: 1. Classical Ciphers 2. Symmetric Ciphers 3.…
A: 1. Classical Ciphers: In cryptography, a classical cipher is a type of cipher that was used…
Q: Q The cipher text C=10 sent to user whose public key is e=7, n=91. What is the plaintext M? Back…
A: RSA Algorithm: Step1: Choose 2 prime numbers p and q Step2: Calculate n=p×q Step3: Select a public…
Q: What is the correct command to encrypt plain text passwords? O a. Ping O b. show running-config O c.…
A: The answer is given in step 2.
Q: Which one of the following cipher is an example for symmetric-key algorithm? O a. DSA Ob. RC4 O. RSA…
A: Answer: symmetric-key algorithm is the simplest kind of encryption that involves only one secret key…
Q: Which of the following is not true about cipher suites? O In a cipher suite negotiation, different…
A: The solution for the above given question is given below:
Step by step
Solved in 2 steps

- Which of the following operations do not achieve non-repudiation? a.Encryption using hybrid cryptosystems b.Digitally signing a message digest c.Digitally signing a complete message d.MACWhich of these encryption techniques does NOT rely on a key? a. Polyalphabetic substitution-based cipher b. Data Encryption Standard c. Monoalphabetic substitution-based cipher d. Transposition-based cipher No hand written and fast answer with explanationWhich of the following description regarding the RSA encryption are correct? Group of answer choices RSA Encryption is a symmetric key crypto In RSA Encryption, only the private key can be used to encrypted data. RSA Encryption is an asymmetric key crypto In RSA Encryption, both private key and public key can be used to encrypted data.
- a. Which of the following can be used for both encryption and digital signatures? 3DES AES RSA MD5 b. Digital Signatures provide which of the following? Confidentiality Authorization Integrity Authentication Availability c. The difference between a hash and a digital signature is: Hashes are used to verify message authenticity, digital signatures are used to verify message integrity. Hashes are used to verify message integrity and authenticity, digital signatures are used to verify message authenticity only. Hashes are used to verify the message integrity only, digital signatures are used to verify message authenticity and message integrity. There is no functional difference. d.Which asymmetric algorithm is used for establishing a shared key?A.Elliptic CurveB. PGPC. Diffie-HellmanD. RSA e.What is used to create a message digest that will be attached to data at rest or in transit? Asymmetric algorithm Symmetric algorithm Encryption Hashing Non-repudiation Authentication…Which of the following is an example of homophonic substitution ciphers? a.ROT-13 b.OTP c.None of the available options is correct d.ATBASHWhich encryption benchmark ensures data is not modified after it’s transmitted and before it’s received? Confidentiality Integrity Availability Symmetric Which remote file access protocol is an extension of SSH? SFTP TFTP FTPS HTTPS
- Vigenere Cipher By finding the key length in worksheet 7 .doc, you can use frequency analysis for each letter of the key in the cipher to find the particular shift and find the key word. Using the keyword you found, decrypt the following text. Enter your answer with no spaces. (Not case sensitive) ciphertext to decrypt: UHBRXATCBSZ UHFK PSUG NPPP UAOR UHJL HTPP FAMG AEBZ PUUR IEWG HEOC SEDG QESG TTIY UTIC TEDS SIUW DONC TDPU OTPI FEQG OGUF FKFW MEOE UHBQ FCSC U.IGR IELC ZLFL HTIA BNCC EEUC SMJL FDUF FNPL FITY CLFR PDPY GRFO VE OA ZAOY MYTG TOOR IEGG SSU.Q FCPL E,TIG SD,FR DLFR UESM GTIC LEZ.Z BBCY HEXY TACJ FTPZ SEBI WIHC OESC CYGG ODJL HGBN TOGY GIYC ELFL HTIZ FTXC FNDM NMPL QHSY TETM SWPP ES.PL DEIC IAEY OUNZ FRPD UHFQ F.HFI OEXR IELC ZLFL HTIK VSUZ FADM NMPL EIWG TOSM GAMJ PFUF FSFE BPT.D PRFV BMQJ FIGF FOCQ FRWC EGBN TOGD PRUW. UWFL UYGG WEBL EFJD UEFL, UHFL JTXY TLJI FLZR IELC ZHBB MEOE UHPD GIWC. XIUF UHJQ PBTC SVBR JOOR IETC DUSG UYPD UHJQ QASR JCVJ BRDP ZPUM TYTR FMXY TLPQ UFPP…Which of the following statements is FALSE regarding cryptography? a. Asymmetric ciphers use the sender’s public key to encrypt a message b. The difficulty of breaking RSA algorithm depends on prime number factorisation c. DES algorithm is an example of stream cipher d. Symmetric ciphers are faster than asymmetric ciphersWhich of the following assertions is false: There are two keys used for encryption and decryption in public-key cryptography. O Unencrypted data is the same as plain text. None of the above choices ring true. The terms encryption and cipher text are not interchangeable.
- Which one of the following is an example of substitution cipher? a. Rail Fence cipher b. Caesar Cipher c. AES d. Playfair cipheq5- Multi Factor Authentication uses which of the following combination ? a. User name and Passwords b. Certificate based authentication c. Captcha d. In addition to user name and password. It also uses, Something you have, and/or Something you areWhen sending a large file, which method uses less encryption operations, cypher block chaining or cypher feedback mode?And which one is much more effective?

