Which of the following regarding an absolute reference is NOT correct? It refers to the same cell, no matter where you copy it By default, a cell reference is an absolute reference To create an absolute reference, type dollar signs before the column letter and row number (e.g., $B$6) You can simply enter a cell address and press F4 once to get its absolute reference (e.g., $B$6). Alternatively, you can repeatedly press F4 to get the type of reference you need (e.g., $B$6, B$6, $B6, or B6).
Which of the following regarding an absolute reference is NOT correct? It refers to the same cell, no matter where you copy it By default, a cell reference is an absolute reference To create an absolute reference, type dollar signs before the column letter and row number (e.g., $B$6) You can simply enter a cell address and press F4 once to get its absolute reference (e.g., $B$6). Alternatively, you can repeatedly press F4 to get the type of reference you need (e.g., $B$6, B$6, $B6, or B6).
Chapter13: Handling Events
Section: Chapter Questions
Problem 4RQ
Related questions
Question
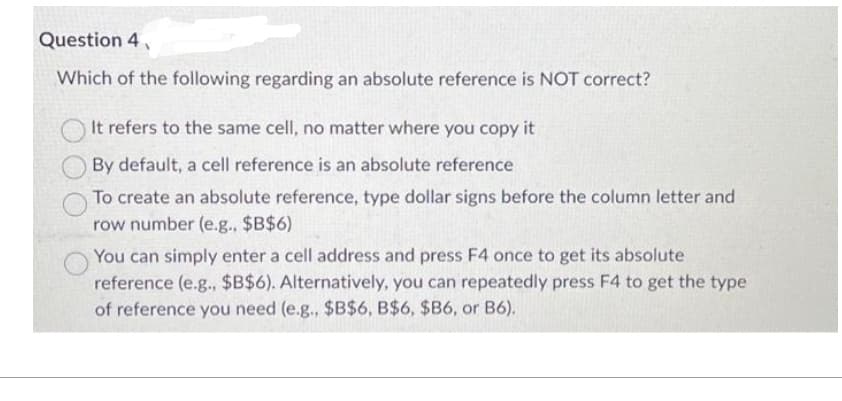
Transcribed Image Text:Question 4,
Which of the following regarding an absolute reference is NOT correct?
It refers to the same cell, no matter where you copy it
By default, a cell reference is an absolute reference
To create an absolute reference, type dollar signs before the column letter and
row number (e.g.. $B$6)
You can simply enter a cell address and press F4 once to get its absolute
reference (e.g., $B$6). Alternatively, you can repeatedly press F4 to get the type
of reference you need (e.g., $B$6, B$6, $B6, or B6).
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage