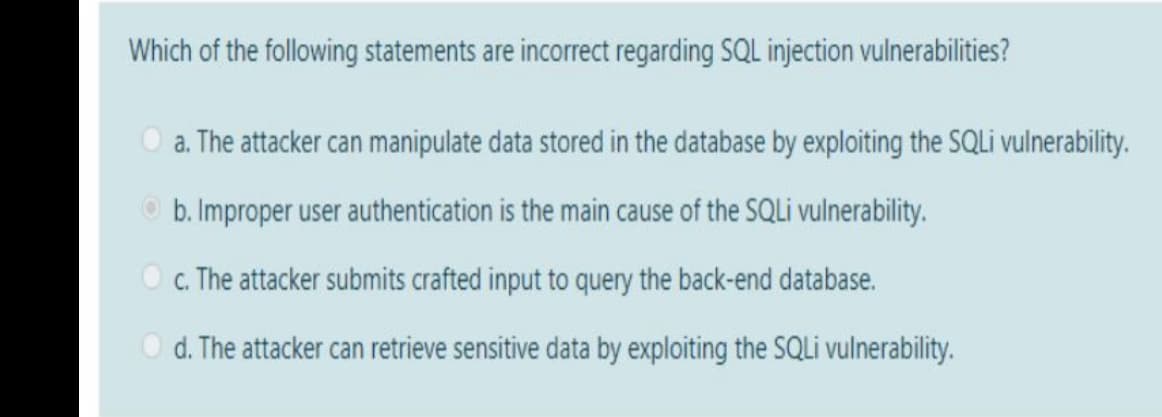
Which of the following statements are incorrect regarding SQL injection vulnerabilities? O a. The attacker can manipulate data stored in the database by exploiting the SQL vulnerability. O b. Improper user authentication is the main cause of the SQLI vulnerability. O . The attacker submits crafted input to query the back-end database. O d. The attacker can retrieve sensitive data by exploiting the SQLİ vulnerability.
Q: Which of the following statements best expresses your perspective on data security during transit…
A: Authentication: Data security when in use or in transit necessitates encryption. Encryption should…
Q: User.login = (credentials, result) { sql.query( *SELECT * ,(select…
A: Required : flowchart
Q: What is an SQL injection attack? Explain how it works and what precautions must be taken to prevent…
A: The Structured Query Language is the way to talk to database and fetch the desired results. SQL…
Q: 1- write a DBA command(s) that checks the database owner of the DBMS database , that exists in the…
A: 1- write a DBA command(s) that checks the database owner of the DBMS database , that exists in the…
Q: connect_error) { die ("Connection failed: ". $conn->connect_error); } $sql = "INSERT INTO MyGuests…
A: The question has been answered in step2
Q: Oracle Database 18c XE comes with a sample database user named HR. This user owns several database…
A: SQL*PLUS is an batch query tool .It is a command-line user interface, a Windows Graphical User…
Q: Which of the following is not a valid DBMS?
A: SQL server is short name for Microsoft SQL Server, and hence it is valid DBMS, and option(a) is…
Q: given a SQL command (s) to remove employee number 103 from the database and assign the…
A: The answer is given below:-
Q: ) Create a database called (heavy duty cars) that has these tables or write the SQL command to…
A: The SQL Queries for creating database, creating tables and the 4 queries are given below
Q: Which of the following database encryption techniques makes it difficult to perform database…
A: EXPLANATION: The disadvantage of Application-level Encryption is that it has a limited effect on the…
Q: in sql If you have not yet used the COMMIT command to store the changes permanently in the…
A: Answer: a. True
Q: In this exercise, you will create tablespaces and change their characteristics. 1. Connect to the…
A: 1. 2. 3.
Q: SQL is a type of database management system. True / False ??
A: A relational database contains multiple tables of data with rows and columns that relate to each…
Q: Make an Application called “ Student Management System ” that connect with database called…
A: BEGIN TRANSACTION;/* Create a student table */CREATE TABLE student(Id integer PRIMARY KEY, Name…
Q: In SQL, which command(s) is(are) used to enable/disable a database trigger? A MODIFY USER B CHANGE…
A: We need to find the correct option for the given statement. The statement given in the question is -…
Q: write a DBA command(s) that checks the database owner of the DBMS database , that exists in the…
A: Question 1- Write a DBA command(s) that checks the database owner of the DBMS database, that exists…
Q: when I do a scan to my website throw the ZAP tool it appears that I have SQL injection !! how can I…
A: Description: SQL injection is a type of online security flaw that allows an attacker to tamper with…
Q: ?The database must be organized in a logical manner True False O محو التحديد Advantages of a DBMS…
A: Please find the answers in the below step:
Q: write one SQL statement to display the three client types that have the most customers exactly as…
A: To print the top three CTOTAL customer, sort the record in descending order by CTOTAL then use…
Q: Lab Exercise Consider the following emp table given below and perform the given below operations.…
A: Create Table emp: CREATE TABLE emp ( EMPNO INTEGER primary key, ENAME varchar(20), JOB…
Q: The faculty and students (we refer to them in our system as clients) can electronically check out…
A: ANS 1. The ERD has 3 entity which are : book, client, author. -- The ERD and Relational is given…
Q: Which of the following commands can be used to eliminate the RECEPTIONIST role? (refer to the…
A: Option: D None of the above
Q: Which of the following statements is most accurate? (refer to the JustLee Books database).a.…
A: Authentication procedures may prevent or may not when data stored in database that is being stolen…
Q: Oracle Database with code and output on update,delete and insert code of trigger i need it on…
A: Here , CUSTOMERS table we had created : Select * from customers;…
Q: connect with database called university , the database contain 3 Tables o Student Table \ this…
A: STUDENT TABLE BEGIN TRANSACTION;/* Create a student table */CREATE TABLE student(Id integer PRIMARY…
Q: The InstantRide User Satisfaction team are looking forward to creating discounts for the users.…
A: This can be done with the help of a SQL query that can simply check for repeated user registrations…
Q: ) Create a database called cars that has these tables or write the SQL command to create the…
A: Create database: CREATE DATABASE cars; Create tables: Car: CREATE TABLE Car(car_ID int PRIMARY…
Q: What are Situations where default values will improve data integrity and situations where using them…
A: Answer: There are two situation as follows: 1.Situation where data integrity decreases: (a) There…
Q: Consider the information below and then answer the following questions. Database Name: DEdb Table…
A: 1. CREATE DATABASE DEdb; 2. CREATE TABLE Department(DepId int unsigned not null,DepName…
Q: pplications is so important. What might possibly go wrong if the application isn't secured? What…
A: Introduction A variety of techniques and procedures are used to secure web browsers and apps in web…
Q: An attacker has been successfully modifying the purchase price of items purchased on the company's…
A: An adversary exploits a weakness in the server's trust of client-side processing by modifying data…
Q: Modify the following code to perform simple password verification in PHP. if (___($password,…
A: We are only allowed to answer 1 question at a time, please repost the remaining questions…
Q: ith respect to relational databases, which of the following statement is true? O An insert anomaly…
A: Foreign key are primary key of a table and is present in some other table to establish the…
Q: Based on your understanding, what can be the main goal behind using try-catch block in most Web…
A: You should definitely use the try-catch syntax to catch any unexpected problem thrown by your…
Q: Which of the statements below is incorrect? A database system is a group of applications that allow…
A: GIVEN: Which of the statements below is incorrect? A database system is a group of applications…
Q: A SQL Data Manipulation command like UPDATE or INSERT immediately saves the result to disk without…
A: DML commands The commands like UPDATE or INSERT are called data manipulation commands which are used…
Q: 7. Which of the following shortcut is used to clear all bookmarks in SQL server Management studio?…
A: Question 7. Which of the following shortcut is used to clear all bookmarks in SQL server Management…
Q: You are providing a recommendation to use input validation on a web application. Answer the…
A: What is SQL Injection Attack? SQL injection, also known as SQLI, is a common attack vector that uses…
Q: Choose two of the following and for each describe how the attack function and how secure programming…
A: The solution is explained below with propper examples and resolution methods.
Q: Database question 2.You created a new user on the database by executing the following command:…
A: Question 2. You created a new user on the database by executing the following command: SQL>…
Q: Please help me as this is in regards to Oracle 12 database Question 7 IN SELECT statement you…
A: According to the question below the solution
Q: 1. If a user has only read authorization for the database, can he modify the data in the database?…
A: Authorisation is a privilege provided by the Database Administer. Different restrctions/privileges…
Q: Which keyword is used to query data from the database? O EXTRACT EXPORT SELECT O INSERT INTO QUERY…
A: In order to read data or query a data from database we need to used SELECT statement. Syntax of…
Q: Which of the following statements best describes how you feel about the safety of data while it is…
A: Authentication: Authentication refers to the process of determining whether or not someone or…
Q: 1. Which of the following is NOT an advantage of using a DBMS? efficient access in storing and…
A: Please give positive ratings for my efforts. Thanks. ANSWER 1. Application dependency is NOT…
Q: c) Suppose you want to move from one tablespace to another tablespace. How can you automatically…
A: In database recovery undo records are used to undo any uncommitted changes applied from the redo log…
Q: 1) Create a folder (directory) called "sqlite" (without the quotes) in your base drive (eg.…
A: In cmd 1. C:\>mkdir sqlite C:\sqlite> 2.sqlite>sqlite test.db 3. sqlite>create table…
Q: IN SQL Which of these examples of privileges are CREATE SESSION, CREATE TABLE, CREATE USER? Select…
A: Privilege is a right to execute a particular type of SQL statement. In SQL, Object privileges: It…
Q: choice "6" 2 if choice "5": 3 print(choice) 4 elif choice "6": 5- try: sql - "*"INSERT INTO…
A: ANSWER: Console Code:
Step by step
Solved in 2 steps

- Which of the following is a correct statement? a. A commit is issued implicitly when a user exits SQL Developer or SQLPlus. b. A commit is issued implicitly when a DDL command is executed. c. A commit is issued automatically when a DML command is executed. d. All of the above are correct. e. Both a and b are correct. f. Both a and c are correct.1. What are the three stages during the startup of an Oracle database? If a copy of the control file is corrupted, which stage of the startup would fail? Briefly explains why. 2. What are the SQL statements to perform the following tasks? Create a smallfile tablespace Hw2Tbs that contains a 32MB datafile in the directory C:\app\abc\oradata\csc544744\myData Add another 8MB to tablespace Hw2TbsGiven the following function Oracle user account: Jsmith Profile: Manager_prof Password verify function: Good_Pwd_Fun As a DBA, you will write SQL commands to accomplish the following tasks: a. Change Jsmith password to CatChasedog! b. Add the password verification function to the profile c. Add the profile to Jsmith d. Set smith password expire
- Choose two of the following and for each describe how the attack function and how secure programming techniques can be used to protect against the attack SQLcode injection cross sit scripting XXSWhat two SQL DCL statements are used to establish and remove database privileges?? Answer In short yet clear respose please!1. If a user has only read authorization for the database, can he modify the data in the database? 2. If a user has only read authorization for the database, can he retrieve data from the database?
- Write a PHP Program for authentication. 1) Create a table user’s 2) Apply SQL injection using Get and Post method. 3) Change code to make authentication mechanism secure. Use WAMP Server Software to write the PHP Program for authentication and to apply SQL injection using Get and Post Method. Provide answer all the questions and provide correct solution to all the questions mentioned above as soon as possibleMicrosoft Access performs an immediate update of the database when data is modified, added, or deleted, but Oracle will not actually physically update the database until a COMMIT command is explicitly or implicitly run. Question 38 options: 1) True 2) False73. Which of the following is a transaction isolation level as specified by SQL standard? a. Serializable b. Repeatable read c. Read committed d. All of the mentioned
- Answer the given question with a proper explanation and step-by-step solution. Exercise 1 Using oracle sql developer How to create a user? Write the following command in either your SQL Plus prompt or your SQL Developer. CREATE USER spy2000 IDENTIFIED BY 1234; Do you have errors as below? ORA-65096: invalid common user or role name Do this to fix the error: alter session set "_oracle_script" = true; Now you should be able to create a user without any error. Lets create a user with IDOracle Database 18c XE comes with a sample database user named HR. This user owns several database tables in a sample schema for a fictional Human Resources department. However, for security reasons, this user's account is locked. You need to unlock this account before you can view the HR objects or build any applications that use these objects. Assume that you are logged in as Systems Administrator, provide the SQL*plus commands for unlocking the HR account, making sure that the password reuse and life time is unlimited.You are in charge of creating a small database for a store that sells goods so that it can keep track of its customers and their orders. Write an SQL statement to create a customer table containing the following information: Every customer has a unique ID, that should not be empty and set as the primary key The customer's first and last name that shouldn't be empty The phone number that shouldn't be empty The email, which could be empty. The address, which could be empty. Write a SQL statement to create the table Orders, which will keep track of customer orders, using the following information: Each order has a unique ID, which shouldn't be empty and should be set as the primary key. The customer's ID and should not be empty and assign it as the foreign key of the customer ID in table customer. The Items purchased by the customer and shouldn't be left empty. The amount of each item, and should not be empty The price of the items, and should not be empty

