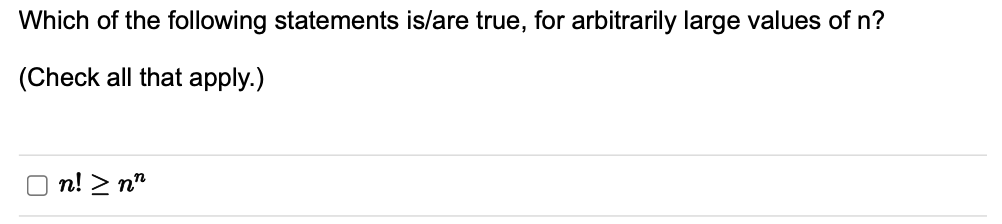
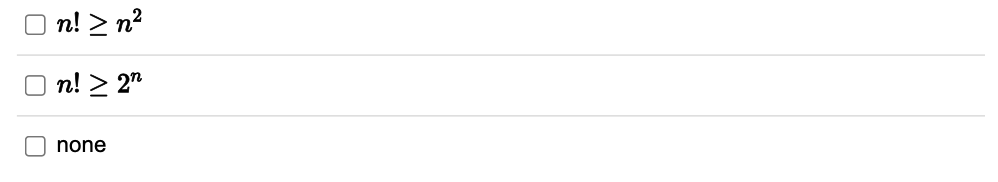
Which of the following statements is/are true, for arbitrarily large values of n? (Check all that apply.)
Q: 33. If the Telnet service has been configured on a network device, but a user still cannot realize…
A: Telnet User Telnet offers users a two-way interactive text-based communication system through an…
Q: Write Top down approach Algorithm in Unsupervised Learning Input: I = {I1, I2, … , In} Output: O
A: Top down approach Algorithm in Unsupervised Learning given data Input: I = {I1, I2, … , In}Output: O
Q: 31 Which of the following statements about the preference of static routes on a Huawei device are…
A: Static routing on Huawei devices:- The technology used here is Network Service. Provider: Huawei…
Q: Need to be in Python Given some components that have dependencies, find the order in which…
A: Here is the python code of the above problem. See below steps.
Q: How many elements (2, 3, 0, or Can't say - an error message was issued) are in the dictionary…
A: using python programming language the given dictionary code is someData = { } someData['cheese'] =…
Q: "Rabenstein code was used to send a message with 4 information bits, you receive 100110001, if you…
A: Rabenstein code:- Rabenstein codes are used to send a message by sending the same information two…
Q: reate a new StringBuilder Object using no-arg constructor. g. Using for loop append the array…
A: Please find the answer below :
Q: 1. State application of soft computing.
A:
Q: What are the constituents (or types) of Sof Computing techniques ? Explain each in brief.
A: Introduction In this question, we are asked about the constituents or types of Soft Computing…
Q: When a DHCP client applies for an IP address, only DHCP ACK messages are sent in unicast mode.
A: DHCP (Dynamic Host Configuration Protocol): A network management protocol called DHCP (Dynamic Host…
Q: wing functions can be executed by a convolutional neural network in deep learning? - ReLU, Max…
A: Introduction: The principal applications of a convolutional neural network (CNN), which comprises…
Q: 55. When an access port receives a frame whose VLAN ID is the same as the PVID of the access port,…
A: According to the information given:- We have to justify the mentioned statement weather it is…
Q: Use € Or € to indicate whether the given object 1s an element of the given set. 5 {1,2,3,4,5,6}
A: We need to use ∈ or ∉ to indicate if 1 is an element of the set {1, 2,3,4,5,6} or not.
Q: Observations about circular convolution in matlab. And what is the difference between circular…
A: Convolution:- It is a mathematical operation which is used to combine two signals and give a third…
Q: Define soft computing.
A:
Q: how do you reduce information risk
A: Threats and risks to information and data are a daily reality for most modern businesses. You…
Q: Use the file wordlist.txt for this problem. Find the following: (a) All words ending in ime (b) All…
A: QUESTION (a) time, slime, rhyme, prime, grime, dime, crime, mime QUESTION (b) save, cave, gave,…
Q: "Rabenstein code was used to send a message with 4 information bits, you receive 1001
A: The answer is
Q: Write java code for a calculator that calculates the Sum and Product of 2 numbers Program…
A: The required java program is provided below with explanatory comments. Methods and while loop are…
Q: 23. If a wireless client connects to the same SSID of two APs, which of the following methods can be…
A: The question has been answered in step2
Q: the following numbers expressed in their respective bases: 11001100112 52014378 93D46
A: Lets see the solution.
Q: Assume that a cryptographic checksum function computes hashes of 128 bits. Prove that the…
A: There are 2128 possible 128-bit hash values. After hashing 264 randomly selected messages, the…
Q: 1. A router receives a packet with destination address (222.186.114.16) Show how it finds the…
A: Introduction: A router receives a packet with a destination address (222.186.114.16) 0.0.0.0 to…
Q: Write code How to Dealing with Categorical Data in python
A: Vector or regression input data must be numeric for algorithm-like support. So, if you have…
Q: Which of the following statements is true about feature selection? A. Wrapper methods provide an…
A: Feature selection is a way of selecting the subset of the most relevant features from the original…
Q: Assume the following adjacency list for a graph. After you draw the graph, what is the path to reach…
A: In question one graph is missing that's why I am solving only second question. Kindly request you to…
Q: Describe, in your own words, the concept of "explicit parallelism" without repeating this book's…
A: In computer programming, explicit parallelism is the representation of concurrent computations using…
Q: Test assertions in your java code.
A: The Assert class provides several functions to help you test the state of your program as it runs:
Q: writing a Python program
A: Given :- In the above question, the statement is mention in the above given question Need to write…
Q: Create a vector (name it vecA) that has 14 elements of which the first is 49, the increment is -3,…
A: Matlab Code : - Command Window : -
Q: What is the Information Security Culture?
A: In order to build cybersecurity in businesses, employee conduct is crucial. Employees may…
Q: 9-14. Lottery: Using the list called series, write a function called get_winning_ticket_number that…
A: Coded using Python 3
Q: 150. Write a C# Sharp program to create a new list from a given list of integers removing those…
A: The C# code is given below with code and output screenshot Happy to help you ?
Q: In python language: What does csv reader() function do?
A: Python:-Python was created by Guido van Rossum and is an interpreted, object-oriented, high-level…
Q: C Program Pass-by-reference in Functions Using Pointers Write a function swap that swaps the values…
A: To swap three numbers in c programming language.
Q: What are the Cyber Attacks and Vulnerabilities?
A: a flaw in the planning, execution, internal control, or a computer's, hardware's, smart device's,…
Q: you have to choose more than one option
A: We need to find the correct options regarding Huawei device.
Q: Write shorts notes on: Bernoulli naive Bayes
A:
Q: Needham and Schroeder suggest the following variant of their protocol: 1. Alice → Bob : Alice 2.…
A: Stolen Session key:- In the field of computer science, session hijacking, also referred to as cookie…
Q: Using JAVA code: Please make a program that will show the step-by-step tablular procedure on how…
A: The programme was written in Java. Please study the source code and output before continuing.
Q: Suppose three algorithms A, B, and C, can be implemented to perform a task. The algorithms have the…
A: Introduction: Time complexity is the length of time it takes an algorithm to run as a function of…
Q: A signal with 60 milliwatts power passes through a device with an average noise of 6 microwatts.…
A: given, signal is 60 milliWatt passes through a device (1 device) with each average noise is 6…
Q: What are the constituents (or types) of Sof Computing techniques ? Explain each in brief. 1
A: Answer the above question are as follows
Q: The following query is intended to list the titles of all books that sold more than 3 copies. Fill…
A: Answers:- The data is the fetched after two tables have been joined The tables trans and book has…
Q: For example the client decides that all employees with a role of Scientist should no longer have…
A: The solution is an given below :
Q: Please help with this program. Need to write a program called did-stack.py in python that uses the…
A: Depth First Search (DFS) is a graph traversal algorithm in the data structure, it works the same as…
Q: 5. In the last chapter, we discussed deadlocks. Describe, in your own words, why mutual exclusion…
A: According to the information given:- We have to define mutual exclusion is necessary to proactively…
Q: Activity A B C D E F G H I J K L M Required Predecessor (None) (None) (None) A A, B C A D, E, F с D,…
A: ANSWER:-
Q: Q.7 Give advantages of fuzzy logic controllers.
A: In this question we need to explain the advantages of Fuzzy Logic Controller (FLC) is context of…
Q: Algorithm 2.3: Graph depth-first search with a stack. StackDFS (G, node) →visited Input: G=(V.E), a…
A: Stack An ordered, linear sequence of elements can be stored on a stack, an abstract data type.…
Step by step
Solved in 3 steps with 4 images

- Which of the following statements is not true if f(n) is O(g(n)): a)f(n) grows more c)f(n) and g(n) have the same growth b)g(n) grows more d)All of the statements mentioned hereIn C++ (Please type answer with correct detiles)Which of the following expressions correctly tests if x is even?a) x % 2 == 0 b) even(x) c) not odd(x) d) x % 2 == x
- Choose ALL correct statements if more than one are correct. Which of the following statements are true as (n gets large or n →∞)? A. n2 * 5n = O(5n) B. n5 * 2n + n2 * 5nn = O(n2 * 5n ) C. log(n5 + 7) +n2 + n = O(n) D. n0.5 + (0.5)n = O(n0.5) E. None of the above is correct.Tell if the statements are true or false. Let p: 3 + 5 = 6; q: 5 + 5 = 10. (a) (p ∧ ~q) ∧ p True False (b) p ∨ (p → q) True False (c) (p ∧ q) → p True FalseWhich of the following is false? * i need answer now
- Set up truth tables for the statementsP ⇒ (P ⇒ Q), (P ⇒ Q) ⇒ Q, P ∧ (∼ Q), (∼ P) ∨ (∼ Q)Are any of these statements equivalent?Choose True or False for all the followingTell if the statements are true or false. Let p: 2 + 1 = 3; q: 16 − 9 = 7. (a) ~p ∨ q TrueFalse (b) ~p ∧ ~q TrueFalse (c) ~(p ∧ q) TrueFalse

