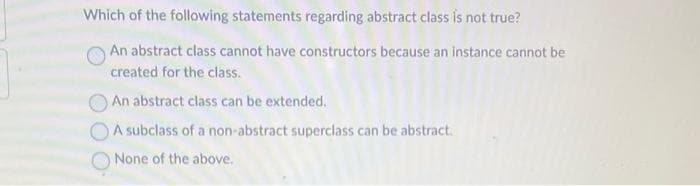
Which of the following statements regarding abstract class is not true? An abstract class cannot have constructors because an instance cannot be created for the class. An abstract class can be extended. A subclass of a non-abstract superclass can be abstract. None of the above.
Q: Web Vulnerabilities Assessment Instructions Protecting e-commerce, social media, and email…
A: Web application security is crucial for protecting sensitive information, maintaining user trust,…
Q: Provide an explanation of what a database management system is as well as the qualities that it has.
A: A Database Management System (DBMS) is a software application that enables users to create,…
Q: What are the key distinctions between an interpreter and a compiler?
A: Compiler: A compiler is a computer software that interprets a high-level programming language, such…
Q: Imagine that your database management system is broken. Describe the process of restoring a…
A: When a database management system is broken, restoring a database requires a set of steps that…
Q: What exactly is meant by the term "multifactor authentication," and how does the process work? In…
A: Multifactor authentication, also known as MFA, is an approach to protecting computer systems by…
Q: hitting time vector for the chain below for A = {1,3} (i.e. the expected time until you hit state 1…
A: To compute the expected hitting time vector, we need to set up a system of equations. Let h(i)…
Q: Devise an algorithm to scan an input array a of n elements, and output all prime numbers in the…
A: Answer: Algorithms Step1: Declared the array Step2: then find the size of the array Step3: then…
Q: Collaborative filtering—how does it work?
A: Collaborative filtering is a popular technique used in recommendation systems to suggest products,…
Q: When a web client requests access to a web server's protected resources, show how native…
A: Given: Show how a web client may utilise the web server's built-in authentication and authorization…
Q: Is this a case of cross-site scripting, often known as XSS?
A: Attack Using Cross-Site Scripting: Attacks of this type, also known as XSS or cross-site scripting,…
Q: What exactly is meant by the term "multifactor authentication," and how does the process work? In…
A: Multifactor Authentication
Q: Firewalls are crucial to keeping networks secure, therefore it's important to describe how they…
A: In today's interconnected world, the security of computer networks has become paramount for…
Q: What are the characteristics that are shared by a derived class and the base class from which it was…
A: The class that inherits from the base class is referred to as the derived class, while the class…
Q: When starting a new process to execute a command, how does the shell determine whether or not a file…
A: When starting a new process to execute a command, the shell determines whether a file is executable…
Q: . Dummy GUI Application by Codechum Admin A GUI Application is an application that has a user…
A: First, implement another class called Checkbox which implements the Clickable interface which has…
Q: Imagine an online banking software developer installed a hidden mechanism that sends him account…
A: Say the developer of online banking software incorporated a secret mechanism that sends him account…
Q: at precisely is meant by the abbreviation "RDBMS" (which stands for "relational database management…
A: RDBMS is an abbreviation commonly used in the field of computer science and database management. It…
Q: your explanation of the Domain Name System (DNS), be sure to include iterated and non-iterated…
A: The Domain Name System (DNS) is a hierarchical and distributed naming system that translates…
Q: Troubleshooting requires expertise and equipment for all technicians. To help technicians discover…
A: A toolkit is useful for providing technical support since it includes everything required to open up…
Q: Many newcomers struggle to understand the difference between how and Please provide an example to…
A: The touch command in the beginning language creates new files or changes file timestamps. It creates…
Q: What exactly do you mean when you talk about "inference rules"? Provide an explanation of the terms…
A: Inference rules are used in computer science to generate new information or conclusions from…
Q: What kind of mobile and wireless employee network would you suggest to others?
A: Required: How would you advise them to network while on the go? Devices connected to a wireless…
Q: In what kinds of situations would you find it more beneficial to make use of an abstract class as…
A: In object-oriented programming, both abstract classes and base classes serve as a foundation for…
Q: the program below is the program that is being referred to in the image, using namespace std;…
A: Start Define a struct for the employee with the necessary attributes. Initialize a head pointer to…
Q: Please provide two justifications for why data should be replicated across various data centers that…
A: Disaster Recovery: Replicating data across different data centers located in different parts of the…
Q: How does a business's information security incident response plan handle information sharing?
A: An incident response plan is a documented set of instructions or procedures to help organizations…
Q: Please provide a succinct explanation of the calling protocol.
A: In this question we have to understand explanation of the calling protocol. Let's understand and…
Q: In the context of the administration and monitoring of a network, what role does logging play?…
A: Introduction:- Here are some of the ways in which records contribute to the tracking and…
Q: What exactly is the name of a user interface control that is related to a data source
A: The name of a user interface control that is related to a data source is commonly referred to as a…
Q: Is there a specific data processing method I need to be aware of? If at all possible, provide…
A: Given: Is there a particular method of working with material of which I ought to be conscious and…
Q: What makes an infrared network unique in terms of the media that it uses?
A: Devices or systems that use infrared radiation (IR) to communicate information use infrared networks…
Q: Develop a hybrid merge-join technique for scenarios when both relations are not physically sorted…
A: Introduction: The merge join and the hybrid merge join are two distinct operations. We learned that…
Q: Show how web clients use native authentication and authorisation services to access web server…
A: Given: Explain in detail how a web client can use native identity and permission services to gain…
Q: What sets a hashtable distinct from a hashmap, and how are they both used?
A: The Hashtable and Hashmap. Both HashMap and HashTable are among the most used classes in Java's…
Q: There are various techniques to protect yourself against Man-in-the-middle (MITM) assaults. Please…
A: A man-in-the-middle (MITM) attack is a type of cyber attack where an unauthorized third party…
Q: Briefly
A: Introduction: The Agricultural Revolution was a significant period in human history that marked a…
Q: Explain how the ideas behind the RAID organization may be implemented in a setting involving…
A: Storage array interface for raid (Redundant Array Of Independent Disk) The RAID method utilises many…
Q: Analyze the differences and similarities between online and batch data entry processes. Included in…
A: A batch processing system handles large amounts of data which are processed on a routine schedule.…
Q: Walk me through the dangers of sending money online with a credit card.
A: A credit card is a payment method that allows customers to take funds on loan from banks. It is a…
Q: What does it mean precisely to have a fundamental algorithm?
A: Algorithm: An algorithm is a set of well-defined instructions or rules that specify how to solve a…
Q: What's an organization's information security limit? What are an organization's earliest and latest…
A: By using information security, organisations are able to protect both digital and analogue data…
Q: Be sure to detail how Personal Operating Solutions will disclose customer information to third…
A: Let's check out the answer. The following describes Personal Operating Solutions' privacy practises:…
Q: What were the usability and user experience objectives for the evaluation?
A: In the stages that follow, you will discover both the solution and an explanation in further depth.
Q: In a few phrases each, describe the five different techniques to risk management that may be used…
A: Introductory: In order to reduce exposure and threats, IT and InfoSec teams use risk control…
Q: Help write a C++ Program to do the following: This is to create a prototype for a Web browser.…
A: Given, When an anchor is displayed, it should appear as [n] where n is a number that is unique to…
Q: Why is using virtualization the best choice when it comes to simultaneously running several…
A: A virtual machine (VM) is a computer's representation in a virtual environment. It is a…
Q: microcontroller, could you please describe the memory addressing capabilities of the 20-bit address…
A: INTRODUCTION: An 8-bit byte-addressable computer with a 20-bit address bus (like the Intel 8086) can…
Q: Sort DNS entries based on the kind of records each one contains. Provide instances of each and a…
A: Adding a CNAME record with the CDN's address to the origin server that stores website content is a…
Q: Why is it important to differentiate between a logical division and a subsystem, and what are the…
A: 1) A logical division is a high-level conceptual grouping of related functionality within a system.…
Q: Research and cite the following problems. Computer science has six levels: Computer Science…
A: Level of the Algorithmic Foundations of Computer ScienceFoundations of Computer Science is a…
OOPs
In today's technology-driven world, computer programming skills are in high demand. The object-oriented programming (OOP) approach is very much useful while designing and maintaining software programs. Object-oriented programming (OOP) is a basic programming paradigm that almost every developer has used at some stage in their career.
Constructor
The easiest way to think of a constructor in object-oriented programming (OOP) languages is:
Step by step
Solved in 3 steps

- Which of these is not a correct statement about abstract class? Every class containing abstract method must be declared abstract. Abstract class define only the structure of the class not its implementation Abstract class can be initiated by new operator Abstract class can be inheritedWhich (if any) of the following conditions are necessary for using polymorphism? Select all correct answers. The classes involved are in the same hierarchy. None of the classes can be abstract. All of the subclasses involved override the same method. The object reference cannot be of an interface type. An object reference of the superclass is used to call any methods. A superclass object is referenced by a subclass reference. Which of the following (if any) are true of abstract methods? Select all correct answers. Abstract methods must have a method body. Abstract methods cannot be declared in a class that isn't abstract itself. Abstract methods cannot be private or static. Abstract methods can only be declared in an interface. Abstract methods cannot be called. Constructor methods can be abstract.Which (if any) of the following conditions are necessary for using polymorphism? Select all correct answers. The classes involved are in the same hierarchy. None of the classes can be abstract. All of the subclasses involved override the same method. The object reference cannot be of an interface type. An object reference of the superclass is used to call any methods. A superclass object is referenced by a subclass reference. Which of the following (if any) are true of abstract methods? Select all correct answers. Abstract methods must have a method body. Abstract methods cannot be declared in a class that isn't abstract itself. Abstract methods cannot be private or static. Abstract methods can only be declared in an interface. Abstract methods cannot be called.
- When would you be most likely to use an abstract class? when you need to derive a class from Object when every method in the class is concrete when you need a super class that should not be instantiated when you need a super class that can be instantiated alongside the derived classes =========== Which UML symbol represents aggregation? a filled triangle an unfilled diamond an unfilled triangle a filled diamondQuestion 30 Which of the following description is TRUE? Inheritance allows us to define a class based on another class. Child classes receive all the features from the parent class but can NOT have their own additional features. Abstraction means that a method in a parent class can have a number of different implementations in child classes. An interface is a completely abstract class, which contains abstract properties, methods, and variables. The private access modifier makes members accessible only from within the class and hides them from the outside.Which of the following statements about abstract base classes is true? a. abstract base classes may contain data. b. abstract base classes may not contain implementations of methods. c. abstract base classes must declare all methods as abstract. d. abstract base classes must declare all data members not given values as abstract
- Which of the following statements are true. a) An abstract method contains a signature but no code implementation. b) We cannot create an instance of an abstract class by using the new operator. c) We can derive classes from an abstract class, but we must provide code to implement all of the abstract methods. d) All of the above statements are true.A is a parent class whereas B and C are subclasses of A. Now, B and Cshare some common attributes and some common methods, but there are somemethods in B and C that have very different implementations. Explain with reason whatA is going to be - a concrete class or an abstract class or an interface.Which of the following is true about abstract classes? Note that if a class can be sub-classed, this simply means that it can be derived from. Abstract classes can only contain abstract methods. They cannot be sub-classed. Abstract classes cannot be instantiated, but they can be sub-classed. Abstract classes can only contain abstract methods. They can be sub-classed. Abstract classes can be instantiated, but they cannot be sub-classed. Can an interface ever contain method bodies (i.e. content between {})? Unknown Yes No Sometimes
- In Java, which of the following is true about an abstract base class? no constructors should be provided at least one member function should be abstract no objects of the class can be created exactly two of the above91. Which of the following is true concerning the following statement:class Manager extends Employee a. Manager is a concrete class and a superclass. b. Manager is a concrete class and a subclass. c. Manager is an abstract class and a superclass. d. Manager is an abstract class and a subclass.Write the abstract super class Transaction, and two of its subclasses, Payment and Sale (you do not need to supply any comments other than your name). I. Write an abstract superclass encapsulating a Transaction: The Transaction super class has an instance variable representing the customers name, and 3 methods: an overloaded constructor, a toString() method that returns a message including the name of the customer, and an abstract method called calculateAmount()which will be implemented in your subclasses. II. Write a non-abstract subclass that inherits from the Transaction class encapsulating a Payment: The Payment class has instance variable representing the payment amount received and 3 methods. It has an overloaded constructor, a toString() method that returns a message including customers name, the name of the class Payment, and the payment amount, an non-abstract class called calculateAmount() which returns the payment amount. III. Write a second…

