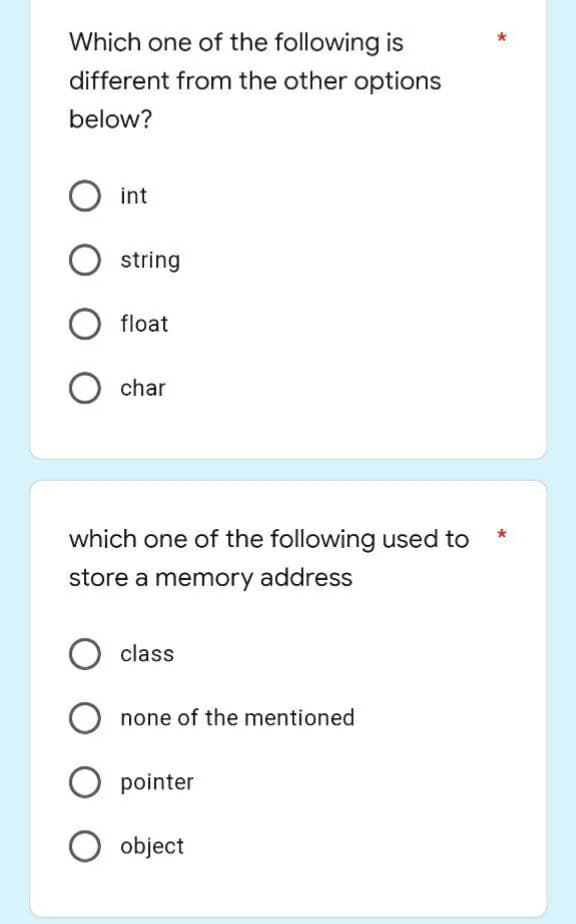
Which one of the following is different from the other options below? O int оооо string float char *
Q: Consider a significant privacy problem that makes it impossible for you to continue using a social…
A: Start: Privacy refers to a person's or group's ability to conceal oneself or information about…
Q: Identity theft is one of the most common online crimes.. There are several ways that identity…
A: Answer: An identity thief may hear you read your Visa number over the phone, buy it on the dark web…
Q: Is there a link between a computer's processor and the quality of its display?
A: Introduction: An output device on a computer is referred to as a display, and it is responsible for…
Q: Calculate the effective access time for a demand-paged memory given a memory access time of 100…
A: Paging: is a non-contiguous memory allocation technique.Page Table: is a table that maps a page…
Q: What are two examples of using menus in an application that are taken from the real world? What are…
A: INTERFACE DRIVEN BY MENU: This menu-driven interface is incredibly basic and straightforward. It is…
Q: It is essential, before moving on, to define the role of the firewall in terms of the safety and…
A: Introduction To effectively defend and secure a network, it is imperative to comprehend these…
Q: When developing software, one should think about the advantage sing a step-by-step method rather…
A: Introduction: Software is far too complex and unpredictable to design totally ahead of time, but…
Q: Please write a program that prints the woodchuck tongue twister when run with the given input…
A: This is very simple. I have written a simple code in python to perform the exact operations…
Q: Think about sending an email or other kind of message over the same route from one host to another…
A: End-to-end delay's delay components are: a lag in the processing a long wait in line The delay in…
Q: Send a packet to a host using the fixed route assuming that you are utilising it.
A: Introduction: Delays refer to the amount of time it takes to process a packet. Computer networks are…
Q: What kinds of ways does the interactive method vary from the waterfall model when it comes to…
A: Interactive method: In the waterfall approach, the objectives for each phase are determined by…
Q: When a project is concluded, it is important to determine what documentation the developer needs to…
A: Launch: Determine which documents the developer should get at the end of the project. When it comes…
Q: What feature should you include? 1. Text 2. card carousel 3. SuggestedAction card 4. Receipt card
A: Here user should be able to browse images, prices and description and made selection. In Text user…
Q: At each step of development, the inputs and outputs of a software system must be thoroughly…
A: Introduction: Input is raw data processed to generate output. Input design must consider PC, MICR,…
Q: I'm curious as to why making electronic transfers with credit card information might put your…
A: Because of the following reasons, using electronic transfers with credit card information may put…
Q: Create two (2) threads named by the user. Display their various states using getState(). In the main…
A: Java is the programming languages which can be executable on the different platforms. It can be used…
Q: Web page content can include O text O images audio & video all of the above
A: The answer is given below.
Q: Develop an estimated multiple regression equation with x=rarity rating and x2 as the two independent…
A:
Q: There are no privacy issues for those who purchase on Facebook since the social networking site…
A: Given that: We will learn about the security risks we may face while making purchases on social…
Q: If you had to select between the Traditional Waterfall Model and the Iterative Waterfall Model for…
A: Son Classical Waterfall Model Iterative Waterfall Model 1 Feasible for small projects…
Q: Greens in Reg. is the percentage of time a player is able to hit the green in regulation; Putting…
A:
Q: (a) Apply the (i) depth-first search and (ii) breadth-first search algorithms to the following…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: How can you tell the difference between information that is genuine and information that is fake…
A: What Actually is Fake News? Fake news is any article or video containing false data camouflaged as a…
Q: A binary code is a string of 0's and 1's. In particular, an n-bit binary code is a string of "n"…
A: lets start with 1-bit binary code: number of 1-bit binary codes: 0, 1 : 2 binary codes of 1 bit…
Q: When working with dynamic data, ensure that you have a solid understanding of how the heap operates.…
A: Inspection: Specific computer languages (including C++) allow for the generation of a "new" data…
Q: In the early days of computers, what kinds of precautions did people often take to protect their…
A: Start: Encryption is critical for securing data in use or in transit. When data travels via…
Q: Make an octave code to find the root of cos(x) - x * ex = 0 by using bisection method. The answer…
A:
Q: Two distinct processes are involved in the creation of software: the development of software and the…
A: Software: The Software Development Methodology is a set of guidelines that guides the development of…
Q: A palindrome is a sequence that is the same as its reverse. For example, the word "RACECAR" is a…
A: dp[i, j] — minimum number of operations to convert substring s[i..j] into palindrome. Below are the…
Q: The Linux and Windows netstat tool lists active network connections. Explain how to use this command…
A: Use the "netstat" command to: The phrase "network statistics" may be abbreviated to "netstat," which…
Q: a. Give another implementation where update takes O(n) time while isSorted takes O(1) time.
A: Please check the step 2 for solution
Q: Where would you start looking if you thought someone was trying to get into your computer?
A: By using the Windows Task Manager, you will be able to check to see if any applications have been…
Q: Hurry up
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT…
Q: When developing software, one should think about the advantages of using a step-by-step method…
A: Developing software: The product development process includes all of the stages that are required to…
Q: Contrast the following terms: a. supertype; subtype b. generalization; specialization c. disjoint…
A: Disclaimer: “Since you have posted a question with multiple sub-parts, we will solve the first three…
Q: The process of developing software and modelling software are not the same thing. The role that each…
A: Methodology for the Development of Software: In software engineering, the division of the…
Q: Write a function named average(num1, num2) that returns the average i.e. (num1+num2)/2, of the two…
A: In this question we have to write a python program for the function average(num1, num2) that…
Q: Discuss the ways in which individuals are being negatively affected by computers and other forms of…
A: Harmful effects: 1. Major Depressive Disorder and Other Problems Relating to Mental Health 2. Not…
Q: b. Describe how to use a balanced BST to implement both operations in O(log n) time. Discuss why…
A: Please check the step 2 for solution
Q: The field of computer science. In order to increase the security of your Windows system, you need do…
A: Start: Windows is a collection of Microsoft's proprietary graphical operating system families, all…
Q: Privacy is a hot-button topic in today's culture, but it's also a contentious one. What do you…
A: Introduction: Privacy implies avoiding dangers. Personal privacy is freedom. Information privacy…
Q: 2.26 LAB: Expression for calories burned during workout The following equation estimates the average…
A: I have provided JAVA CODE along with CODE SCREENSHOT and also provided 2 OUTPUT…
Q: The field of computer Describe the concept of a virtual machine in your own words.
A: Introduction: A Virtual Hardware (VM) is a computational resource that uses software to execute…
Q: b. Describe how to use a balanced BST to implement both operations in O(log n) time. Discuss why…
A: Please check the step 2 for solution
Q: When you need to identify yourself but don't want to use a credit card or an ATM, this might be a…
A: Explanation: When it comes to keeping you safe at the ATM, we take a number of measures. Here are…
Q: It's possible that you've read anything concerning the safety of credit cards.
A: Given: Account details, card numbers, and identifications are connected online, making cyber…
Q: Describe the role that firewalls play in ensuring the safety of your company. What are the benefits…
A: Introduction: The merits and downsides of hardware and software firewalls, software tools, and how…
Q: what is the core functions of logistics
A: Logistics is process of product distribution across various phases within and outside organisation.…
Q: Which PC ports are no longer available in today's computers?
A: Introduction: Port: Hardware to connect different peripherals Interface between CPU and other…
Q: 14. How many different ways can a structure var be declared:
A:
Step by step
Solved in 2 steps

- Which of the following commands can be used to display memory statistics? (Choose allthat apply.)a. freeb. sarc. vmstatd. iostatPlease answer properly with output screenshot must Where is the error in this code? from telethon.sync import TelegramClientfrom telethon.tl.functions.messages import GetDialogsRequestfrom telethon.tl.types import InputPeerEmptyimport os, sysimport configparserimport csvimport time re="\033[1;31m"gr="\033[1;32m"cy="\033[1;36m" def banner():os.system('clear')print("ok") cpass = configparser.RawConfigParser()cpass.read('config.data') try: api_id = cpass['cred']['id'] api_hash = cpass['cred']['hash'] phone = cpass['cred']['phone'] client = TelegramClient(phone, api_id, api_hash)except KeyError: os.system('clear') banner() print(re+"[!] run python3 setup.py first !!\n") sys.exit(1) client.connect()if not client.is_user_authorized(): client.send_code_request(phone) os.system('clear') banner() client.sign_in(phone, input(gr+'[+] Enter the code: '+re))os.system('clear')banner()chats = []last_date = Nonechunk_size = 200groups=[]result =…C++ Write a program that find out how many password meets the following criteria. Please use the random password file that I included, Please take a screenshot of the output. Thank you. Minimum length of twelve characters At least one UPPER CASE letter (A-Z) At least one lower case letter (a-z) At least one digit (0-9) At least one "special" character (printable, but not alphanumeric) No space characters Link to the FIle: "C:\Users\arnie\OneDrive\Desktop\passwords10k.txt"
- Can you see where I did wrong in this program ? They show in compiler : ar@osboxes:~ Documents/C++/Project/Projekt_alternativ/"try5/usr/bin/ld: /tmp/ccvECf7h.o: in function `add()':try5.cpp:(.text+0x502): undefined reference to `WriteToFile()'collect2: error: ld returned 1 exit status The program : #include<iostream>#include <fstream>#include<string>using namespace std;#define M 100int count=0;struct AddressBook{string FullName;int Birthday;string Address;string Email;int PhoneNumber;}Person [M];void WriteToFile();void add();void browse();void searchByName();void searchByBirthday();void removeContact();void order();int main(){fstream file;file.open("Contact'sBook.txt");int choice;do{cout << "Please Enter Your Choise: \n";cout << " 1-Add New Person\n 2-Browse\n 3- Search By Full Name \n 4- Search By Birthday 5- Remove a Person" << "\n6- Alphabetical Order \n7-Exit\n";cin >> choice;switch(choice){case 1: add();case 2: browse();break;case 3:…Which of the following reads an image from a file? Group of answer choices a) imshow b) imread c) image d) readmatrixThere might be two files in your account with the same name. Let's say you're at your home directory right now. To copy the file called florence into the user's Proposals folder, the user may use the following command.
- When I run this command I receive following error (see screenshot): size += os.stat(fp).st_size += SyntaxError: invalid syntaxWhich of the following is opening a file with a raw path? a. outs = open(“file.txt”,”w”) b. outs = open(r”c:\acc\file.txt”, “a”) c. None of the above d. ins = open(“newfile”, “r”)Which of the following lines of code will not create a file “abc.txt”? Choose an answer A cat >abc.txt B touch abc.txt C >abc.txt D echo abc.txt
- Which of the following opens the employ.txt file and allows the computer to write new data to the end of the file’s existing data? a. outFile = IO.File.AddText("employ.txt") b. outFile = IO.File.AppendText("employ.txt") c. outFile = IO.File.InsertText("employ.txt") d. outFile = IO.File.WriteText("employ.txt")Please identify the correct statement(s) for the following code snippet from the script: while inst_iter.hasNext() and not monitor.isCancelled(): ins = inst_iter.next() addr = ins.getAddress() pcodeList = ins.getPcode() for pcode in pcodeList: if pcode.getOpcode() == PcodeOp.FLOAT_DIV or pcode.getOpcode() == PcodeOp.INT_DIV: print("Address: {}, Inst: {}, Pcode: {}".format(addr, ins, pcode)) addrSet.add(addr) Question 1 options: It saves the address of the disassembled instruction that introduces division. This snippet uses refined/high p-code. This snippet uses raw p-code. It uses p-code opcode to identify the division operator. It uses the mnemonic string of a disassembled instruction to identify the division operator. It saves the sequence number of the p-code instruction that introduces division.-For external input, which of the following instructions is used? Aşayuakiieiuemangisi bir ueyişkeT upr ueyinui Osetlocale Ofor Ocout Oprintf Ocin -Aşayuakiieiuemangisi bir ueyişkeT -Which of the following does not represent a variable type? Ofloat vs Ochar Odouble Oint



