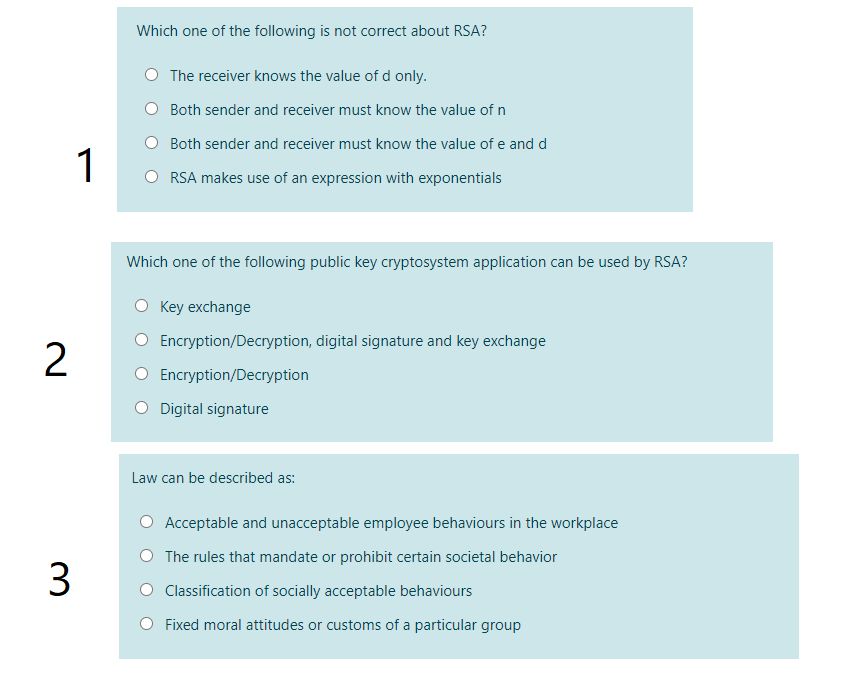
Which one of the following is not correct about RSA? O The receiver knows the value of d only. O Both sender and receiver must know the value of n Both sender and receiver must know the value of e and d RSA makes use of an expression with exponentials
Q: State by True/False: 3a EZ, VbEZ a+b=2 O True O False
A: Z is integer i.e negative number, 0 and positive number.
Q: g VRs: .00, 1.0
A: Step 1: Interpret the following VRs: .00, 1.00, .43.
Q: Which terms did not match the binary value of 11010? Choose three (3). Select one or more: O ABC DE…
A: A -> 1 A` -> 0 Complemented variable denotes 0 and normal variable denotes 1. Since the string…
Q: How many conditional and unconditional jump codes are there? 0 6 O 8 O5 0 7
A: Conditional and unconstitutional jump codes
Q: The message 11001001 is to be transmitted using the CRC polynomial x3 +1 to protect it from…
A: Question The message 11001001 is to be transmitted using the CRC polynomial x^3 +1 to protect it…
Q: 57- What are bitwise o
A: 57- What are bitwise operators?O. & O!O O . All above
Q: Sender wants to send “world” in ASCII. Verify using Parity check that is received uncorrupted and…
A: ISPs must be interconnected to form the Internet, which results in a network of networks. Rather…
Q: Read a 3 digit number N from keyboard and find individual digits in unit’s place (U), ten’s place…
A: Program code: #include <iostream>using namespace std; /* Function to get sum of digits */ //…
Q: Find the approximations Ln, R, Tụ and M, for n = 5, 10, and 20. Then compute the corresponding…
A: Question
Q: ¬[[p → ¬q) v s] = [p Aq A -s] -[[p → ¬q) → s] = [¬(p^q) A¬s] [(pA¬q) → s] = [¬s → (-p v q)] [¬s →…
A:
Q: Let s = sum of all the digits of your student ID, f = sum of first two digits of your student ID, =…
A: Given data, Let s = the sum of all the digits of your student ID f = the sum of the first two digits…
Q: Is it true that 132 ≡ 109 (mod 25)?
A: A ≡ B ( mod n ) simply, means A and B will give same remainder when they are divided by n . (…
Q: For any two integers n and m, ((n XOR m) XOR m) produces n. True False
A: For any two integers n and m, ((n XOR m) XOR m) produces n. True False
Q: Which of these jumps is used with unsigned integers? JL JLE JBE JG
A: Conditional jump is used to transfer control in assembly language. JL :- it is used with signed…
Q: Given that F(A,B,C) = A' B' + A C' Which of the following is a correct SoM expression for F?…
A: The function is F=(A'B'+AC') F=A'B'(C+C')+AC'(B+B') (Using x+x'=1 identity) =A'B'C+A'B'C'+AC'B+AC'B'…
Q: Find the approximations Ln, R, Tn, and M, for n = 5, 10, and 20. Then compute the corresponding…
A: Question:-
Q: We want to send the message 101000111 using a Cyclic Redundancy Check (CRC): Given the Generator…
A:
Q: an not use any control constructs such as if, do, while, for, switch, etc. /* * bitCount - returns…
A: We construct the methods tmax, minusTwo, bitCount and conditional as per the requirements of the…
Q: Which of the following sets of codewords can be Huffman codes? (a) [1, 01, 000, 001]; (b) [0,1); (c)…
A: Huffman coding is used for the file compression. In this Huffman coding, no code word must be the…
Q: 4. Which of the following is not correct about RSA? O a. The receiver knows the value of d only. O…
A: RSA is a public key encryption technique where both the sender and receiver is aware of their public…
Q: 3.(a) What is minimum hamming distance? Why are redundant bits added by the sender? Name two error…
A: Given: What is the shortest hammering distance? Why does the sender include superfluous bits? Name…
Q: A sender needs to send the four data items 0x1236, OXABCC, OX03BC, and 0XEEEE. To avoid confusion,…
A: The answer is
Q: 2. Which of the following is NOT logically equivalent to the rest: 1. wx~y + w~z + wxyz + w~yz 2. w…
A: To check which Boolean expression is not logically equivalent , you need to simplify the given…
Q: Q8/F(A,B,C,D)= Σm(0,2,5,8,10,13)+Σd(1,7,12,15) G(A,B,C,D)= [m(6,7,11,12)+[d(0,2,3,8,13,15) Chose the…
A:
Q: If a < 0 < b < c, then each of the following must be true EXCEPT (A) ac < ab (B) a2 < b2 < c2 (C)…
A: Given: a < 0 < b < cherea is negativeb,c are positive valuesnow(A) ac < abhere a is…
Q: (p q) v (p r) is logically equivalent to 2020 a.p- (q v r) b. p v (q A r) c.pA (q v r) d. p - (q Ar)
A: Here, we are going to check logically equivalent statement for the given logic statement. We can…
Q: How many bits are used by the following datatype? DOUBLEWORD which is same as DWORD O 32 O 128 0 1 0…
A: Note :- As per our guidelines we are supposed to answer only one question. Kindly repost other…
Q: Find the approximations Lnı Ra, Tn and M, for n = 5, 10, and 20. Then compute the corresponding…
A: Answer is given below .
Q: True or False? 3x (x € Z | a = 1 ( mod 2) A æ = 1( mod 3)) True O False
A: Given statement:
Q: Which of these equations is correct (chose one only) ? O 12=h21*11+h22*V2 O None of the other…
A: Every linear circuit having input and output terminals can be analyzed by four parameters called as…
Q: Determine the truth value of (p ∧ q) → r ↔ (p → r) ∧ (q → r) if p, q and r are all true
A:
Q: Even if f and f • g are one-to-one, it does not follow that g is one-to-one. O True O False
A: if f and f o g are one to one, does it follows that g is one to one.
Q: Q8/F(A,B,C,D)= Em(0,2,5,8,10,13)+[d(1,7,12,15) G(A,B,C,D)= [m(6,7,11,12)+[d(0,2,3,8,13,15) Chose the…
A: Here in this question we have given two function with minterm. We have asked to find expression form…
Q: Which statement is true? O not deciable log, n = 0(fm) logą n 0(m)
A: Here the Correct answer for the question is "(d.)" i.e.. log2n>o(n) log2n>o(n) Explanation: It…
Q: Which one of the following error is not detectable by the CRC mechanism? All double-bit errors if…
A: Let's see the solution in the next steps
Q: GIVEN THE DATA STORED IN THE FOLLOWING REGIS TERS: A = 6CH B = D2H C = AAH Find the result of the…
A: Note : Answering the first three subparts as per the guidelines. Given Data : A = 6CH B = D2H C =…
Q: Which one of the following is not correct about RSA? a. RSA makes use of an expression with…
A: RSA scheme is developed by Rivest, Shamir and Adleman. In this it makes use of an expression with…
Q: Which of the following statement is not true about combinational circuits? O a. For n input…
A: logical design: All digital computers are based on a two-valued logic system—1/0, on/off, yes/no…
Q: Given prime numbers p=7, q=11. Use RSA to digital sign message m=9 where public key e=13, and…
A: Prime numbers are given p = 7 , q = 11, e = 13, d= 37.
Q: 6. Convert 14 to decimal? (8) T LO octal? Convert T40(10) 8. Convert 24CE16) to decimal?…
A: To change over a hexadecimal to a decimal physically, you should begin by increasing the hex number…
Q: Which of the following is true? E-o 4"-k5k (") = 87 -k=0 E, 5* () C) = 5" k=0 Eo 4*5n-k (") = 20"…
A: This question comes from Discrete Mathematics which is a paper of Computer Engineering. Let's…
Q: Using Huffman coding, calculate the number of bits required for encoding the following message: I A…
A: Given: Using Huffman coding, calculate the number of bits required for encoding the following…
Q: Which of the following represents "exponential" time? Note: ^ in the answers means power, so n^7…
A: The time complexity is here calculated by using Big O notations.
Q: which is transmitted over the channel. Let T(w) denote the word. (a) What is the probability that…
A: The answer is
Q: Which one of the following can be used to find text message in RSA decryption m =c (mod n) n=c (mod…
A: I have given an answer in step 2.
Q: Then which of the following is a path from a to d of length 5. Mark all correct answers O a.…
A: Directed graph belongs to graph and tree topic of data structure. We will use self loop count to…
Q: Which one of the following is not correct about RSA? O Both sender and receiver must know the value…
A: Answer is b) Both sender and receiver must know the value of e and d
Q: 2-Give the full term of the following: RST, INTA, INTR
A: The Answer for the given question in step-2.
Q: Given p = 47569 and q = 51413. What is N and the totient(N)? Choose a valid e. How do you know it's…
A:
Q: ind the approximations Ln, Ra. Tn and M, for n = 5, 10, and 20. Then compute the corresponding…
A: Answer : here we find the value of Ln,Rn,Tn and Mn : and make table also.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- a. Which of the following can be used for both encryption and digital signatures? 3DES AES RSA MD5 b. Digital Signatures provide which of the following? Confidentiality Authorization Integrity Authentication Availability c. The difference between a hash and a digital signature is: Hashes are used to verify message authenticity, digital signatures are used to verify message integrity. Hashes are used to verify message integrity and authenticity, digital signatures are used to verify message authenticity only. Hashes are used to verify the message integrity only, digital signatures are used to verify message authenticity and message integrity. There is no functional difference. d.Which asymmetric algorithm is used for establishing a shared key?A.Elliptic CurveB. PGPC. Diffie-HellmanD. RSA e.What is used to create a message digest that will be attached to data at rest or in transit? Asymmetric algorithm Symmetric algorithm Encryption Hashing Non-repudiation Authentication…Which of the following statements about cookies is true? a. Cookies were originally intended to facilitate advertising on web. b. Cookies allow websites to off load the storage of information about visitors. c. Cookies always contain encrypted data d. Cookies are text files and never contain encrypted data. e. None of the above is true.OBX Cart Rentals has created a website for customer access. They are trying todetermine a reasonably secure number of available passwords. They have decided toallow upper case letters, lower case letters, digits (0 – 9), and the three pecialcharacters: $, ! ?. Find the number of possible 6 character passwords given each of theconditions (Note: you MUST simplify completely.)a. The password must begin with a letter (either upper or lower case)i. repetitions permittedii. repetitions not permittedb. The password must begin with a letter and end with a special character ($, !, ?):i. repetitions permittedii. repetitions not permitted
- Which one of the following statements is NOT correct about HTTP cookies? a. A cookies is a piece of code that has the potential to compromise the security of an Internet user b. A cookie gains entry to the user’s work area through an HTTP header c. A cookie has an expiry date and time d. Cookies can be used to track the browsing pattern of a user at a particular siteCan you provide some explanation and steps to do , i am using ubuntu20.04 on windows 10 VMware. also i could able to config VPN connection to the server what is next step also i would like to use python for programming. task description is below. Thanks A UDP service FlagServ is running at flagserv.cse543.rev.fish:13337. This UDP service receives a target IP address from the user, and if the user is authenticated, it will happily send a flag (a special string) via UDP to port 13337 of the target IP. Your job is to write a program that retrieves the flag. FlagServ employs THE BEST AUTHENTICATION METHOD IN THE WORLD: Source-IP-based authentication, which means it authenticates all users based on their source IP addresses. If a user's source IP address is trusted, FlagServ will send out the flag to the specified destination (repeat: via UDP). Otherwise, it will send an error message back to the untrusted user (via UDP, too). The only trusted IP is 10.2.4.10. Your task is to break or…Which of the following statements about the router command "service password- encryption" is true? a. The telnet password is encrypted using it. b. It is used to encrypt each and every password. c. The privilege exec mode password is encrypted using it. It's used to encrypt the console password.
- q5- Multi Factor Authentication uses which of the following combination ? a. User name and Passwords b. Certificate based authentication c. Captcha d. In addition to user name and password. It also uses, Something you have, and/or Something you areThis question is designed to gain more experience on symmetric encryption algorithms, encryption modes. The cryptographic library implemented by OpenSSL project will be used in this question. Using OpenSSL from the command line interface Create a new text file using a notepad or any other software, The text file contains your name(first 8 chars) and the file must be exactly 8 bytes in size only and name it “txt”. Print screen of your public ip address, repeat it twice and convert it to hexadecimal format then Create another text file and name it “key.txt” contains the doubled IP address in hexadecimal format. Encrypt the file “txt” using DES, using key.txt as a key and ECB mode of operation. The ciphertext should be in a file named “your_id.enc” and print screen your steps in details. [ Prove and explain by details that the avalanche effect is exist in DES algorithm. you don’t have check the existence of avalanche effect using different plaintext only you can use different keys to…Here is the header of another email obtained from Suni Munshani’s inbox. Compare the two headers and see if you can find any inconsistencies. Answer the following questions: Who are the senders and receivers of these emails? Construct the email paths and timelines of these two headers. What else can you compare?
- #find all IP addresses for invalid logins, then see which IPs are also used for scanning def compareInvalidIPs(): return True 3. The getinvalidLogins() method should find all IP addresses that are used for both invalid logins AND are blocked by the firewall. To get the invalid logins, you should use the log/auth.log file. For compareInvalidIPs, you should first extract all gzipped versions of auth.log* (meaning auth.log, auth.log.0, auth.log.1, etc.) using the extractLogFiles() method that you implement. Similarly, you will extract all gzipped versions of ufw.log* using the extractLogFiles() method for firewall logs. You will then compare the IPs found in each version. Here is the output for my solution code when executing the if __name__=="__main__" code branch. Your output should be similar.so i am tasked with creating 10 new local users on powershell with descriptions and no passwords. the script i cam up with is new-localuser -name "user01" -desription "contact info" -nopassword. my question is do i have to enter this script 10 seperate time or is there a way to include all 10 users using one script . if so how would I go about writing that scriptWhich encryption benchmark ensures data is not modified after it’s transmitted and before it’s received? Confidentiality Integrity Availability Symmetric Which remote file access protocol is an extension of SSH? SFTP TFTP FTPS HTTPS

