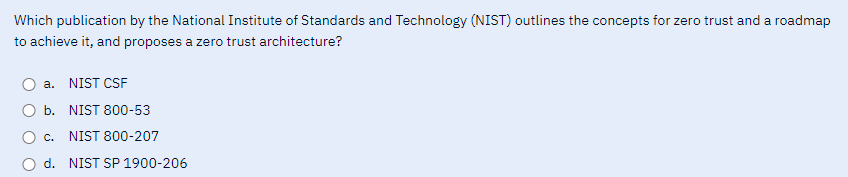
Which publication by the National Institute of Standards and Technology (NIST) outlines the concepts for zero trust and a roadmap to achieve it, and proposes a zero trust architecture? a. NIST CSF b. NIST 800-53 c. NIST 800-207 d. NIST SP 1900-206
Q: So, in the context of a multithreading system, what does "cooperative" multithreading entail? What…
A: Cooperative Multi Threading: This type of computer multi threading involves using one process to…
Q: The following is a list of the most important things that an OS does:
A: Operating System: An Operating System (OS) is a piece of software that serves as a mediator between…
Q: Java: For each of the following, write a single statement that performs the indicated task: (a)…
A: Q. a) Answer: int length = s3.length(); Explanation: In java, the string has a function length(). It…
Q: When is it appropriate to employ dynamic scoping, and how may its efficiency be improved?
A: Your answer is given below.
Q: How did we get to this point, and what are the root reasons of the many types of harmful software…
A: Malware Malware is only programming with malevolent reason. Coming up next are a portion of the…
Q: A. I. means what exactly?
A: Subdiscipline of computing science concerned with artificial intelligence is enormous. Creates…
Q: Question: 27 Assume the following: int a = 5, b = 3; float x = 9.0, y = 2.11 z = 3.0; Evaluate…
A: Here is your solution -
Q: What are some ways in which Service-Oriented Architecture differs from Web Services?
A: SOA design: It divides a large software programme into service components that interact over the…
Q: What are some of the most significant cybersecurity threats facing individuals and organizations…
A: Introduction: Cybersecurity is a critical issue in today's world, as businesses and individuals are…
Q: Please elaborate on the meanings of "computing organization" and "computing architecture" for me.
A: We have to give details about two terms: Computing organization and Computing architecture.
Q: With 8085 Write initialization instructions for the 8259A Interrupt Controller to meet the following…
A: The below code initializes the Interrupt Controller with the following specifications: Interrupt…
Q: Which platforms lend themselves to agile development?
A: Approaches to Agile Development: Using an agile strategy for project management is a frequent event.…
Q: Explain why, from a developer's perspective, deep access is preferable than shallow access, rather…
A: A programming method called deep access enables a programme to access variables outside the current…
Q: When talking about a computer system, what does it imply to say that it has a "RAID structure"? What…
A: IntroductionRAID (Redundant Array of Independent Disks) is a storage technology that combines…
Q: The concept of dynamic memory allocation is broken down for the layman
A: The act of assigning a process's physical or virtual memory address space on a computer's hard drive…
Q: Please Provide the stochiometric output as a matrix on Python. Thank you.
A: Based on the information provided, the question has two parts: Make an organized output of the…
Q: Shouldn't the hashed passwords be stored in their own encrypted file?
A: It is generally recommended to store hashed passwords in a separate encrypted file, rather than…
Q: The term "apriori pruning principle" seems interesting; please elaborate. Provide an example, if you…
A: Provide an explanation of the apriori pruning principle and an example of its application. Answer:…
Q: What is the CAP theorem and how does it work? So, what does this imply for NoSQL storage?
A: NoSQL storage: NoSQL storage refers to a type of database management system (DBMS) that is designed…
Q: The concept of dynamic memory allocation is broken down for the layman.
A: The act of assigning a process's physical or virtual memory address space on a computer's hard drive…
Q: How do the various types of databases vary, and what kinds of information may be kept in each?
A: Structured Query Language (SQL) is a standardised programming language for relational databases that…
Q: How do you distinguish between two computers sharing the same MAC address on a local network? That's…
A: Every network interface card (NIC) is assigned a unique MAC (Media Access Control) address by the…
Q: When several systems and applications use the same physical machine, how does it benefit the user?
A: Your answer is given below.
Q: In the grand scheme of things, what role does MVC play in the creation of online applications? What…
A: MVC (Model-View-Controller) is a design pattern that is commonly used in the development of web…
Q: Summarize briefly the numerous benefits achieved by linking the worksheets included inside a…
A: Linking worksheets within a workbook offers several benefits that enhance productivity, data…
Q: The use of wireless networks is not without its challenges. Due to safety issues, should wireless…
A: The question is asking whether it is safe to rely only on wireless networks for communication in the…
Q: Challenges and Solutions for Android and Java Development in 2023" "Ensuring App Security in…
A: As we approach 2023, the world of Android and Java development faces several challenges that…
Q: When programmers refer to "common logic distributions," what exactly do they mean?
A: Logic distribution is also referred to as word distribution. The term of a proposal refers to the…
Q: All threads in a JVM have access to the same common method area. What give
A: Answer is
Q: Expense Modeling Algorithm What drawbacks does it have in comparison to other approaches?
A: The use of machine learning algorithms for expense modeling which can help organizations to make…
Q: Multithreading has replaced several separate background processes. Explain.
A: Introduction: Multi-threading is a programming technique that enables numerous pieces of code to…
Q: May I ask what you mean by the term "frequent item set"? Additionally, please elaborate on the…
A: What are common itemset: Let's first clarify what data mining is. Data mining is the process of…
Q: Does the JVM's method region serve any particular function, and if so, what is it used for? There…
A: Wireless data connections are used in a wireless network to connect network nodes. Mobile phone…
Q: The use of wireless networks in developing nations merits further scrutiny. For reasons that remain…
A: Introduction: Wi-Fi connects computers, tablets, smartphones, and other devices to the internet, as…
Q: How do computer engineers use principles of computer vision and image processing to develop advanced…
A: The answer is given in the below step
Q: Just what is Blazor, and how does it operate? What makes Razor stand out from other software…
A: Blazor leverages Mono WebAssembly runtime to construct single-page ".Net" apps. Blazor is a mix of…
Q: Packet switching is used in the world's oldest and most well-known (wired) communication network:…
A: Packet switching is a method of transmitting data over a network by dividing it into small packets…
Q: 1. Direct Mapped. 2. 2-way set associative. 3. Fully associative You need to fill the table and…
A: Cache mapping: Cache mapping is the process of determining how the main memory addresses are mapped…
Q: List the system bus subsets.
A: The system bus is a critical component of a computer system that allows different components to…
Q: any's network may connect as many as 70 individual workstations across three unique sites using a…
A: The question is asking about a scenario where a company has a network connecting 70 individual…
Q: More discussion of application layer protocols and network applications will be presented below.
A: Every programme that runs on a single host and is referred to be a network application use the…
Q: How do computer engineers apply principles of signal processing and communication theory to design…
A: A wireless communication system is a network that uses wireless signals to transmit information…
Q: Do you have any evidence to support your claim that many-to-many links are impossible in a…
A: I would like to clarify that the statement "many-to-many links are impossible in a relational…
Q: What level of trustworthiness do you need to have in the security of your private data? How can we…
A: Introduction: Data protection during use or transmission requires encryption. Data should always be…
Q: Describe the changes between a two- and three-tier application architecture. Which one works best…
A: Introduction: Compare two-tier and three-tier application design in this question. Definition and…
Q: The word "virtualization" is often used to describe cloud computing, but what does it really mean?
A: To define "virtualization" in cloud computing.
Q: Design asap the go to code .. Dedign.
A: To design signup form. I used HTML language.
Q: Think of a recent security incident involving authentication or authorization that made headlines.…
A: Introduction: Unauthorized data access for your benefit is a security breach. Due of…
Q: Provide an outline of the two-tier and three-tier architectures for applications. Which is…
A: The functionality of an application is divided into several functional sections, or tiers, in a…
Q: n nWhy is it advantageous to use a computer with both logical and subsystem divisions?
A: Logical partitions let you spread resources inside a system to make it work like several systems.…
Step by step
Solved in 2 steps

- A,B,C or D Which statement best describes zero trust? a. Zero trust is not a product that you can buy; it is a set of principles that promotes the elimination of implicit trust in security controls b. Zero trust can provide 100% protection against data breaches and ransomware c. Zero trust can be achieved by deploying a Zero Trust Network Access (ZTNA) solution d. Zero trust is a new security framework that requires you to abandon all of your existing security controls and start from scratch.What is the ISO 27000 series of standards? Which individual standards make up the series? Supplementary Materials Pfleeger, C.P., Pfleeger, S.L., & Margulies, J. (2015). Security in Computing 5 th Edition. Pearson Education. Stallings, W., & Brown, L. (2015). Computer security. Principles and Practice 3rd Edition. Pearson Education Schou, C., & Hernandez, S. (2014). Information Assurance Handbook: Effective Computer Security and Risk Management Strategies. McGraw Hill Professional. Agrawal, M., Campoe, A., & Pierce, E. (2014). Information security and IT risk management. Wiley Publishing.How can organizations implement Zero Trust security effectively?
- Write a report which, if implemented, will address all the issues identified in the case study. Thereport must have the following structures:Q.2.1 Your report must be structured in the following approach.Q.2.1.1 Executive summary. (5)Q.2.1.2 Background (case study’s IT security issues only). (5)Q.2.1.3 Development of the proposed solution. (5)Q.2.1.4 The role of the IT risk manager in addressing physical and networkrisk.(5)Q.2.1.5 The best methods of combating the network-based attack. (5)Q.2.1.6 The impact of social engineering when combating network security. (5)Q.2.1.7 The most appropriate mechanism in implementing network accessauthentication and authorisation without compromising networksecurity.(5)Q.2.1.8 The implementation of the best strategy to fight against hacking,hijacking and maintain the online presence.(5)Q.2.1.9 The most appropriate location and strategy for the DMZ and firewallimplementation.(5)Q.2.1.10 Conclusion.here are several security frameworks and architectures available to use as templates for creating a secure environment. These include ISO, NIST, COBIT, ETSI, RFC, and ISA/IEC. Select three security frameworks/architectures and use the Internet to research each of them.1. How can a security framework assist in the design and implementation of a security Infrastructure? Supplementary Materials Pfleeger, C.P., Pfleeger, S.L., & Margulies, J. (2015). Security in Computing 5 th Edition. Pearson Education. Stallings, W., & Brown, L. (2015). Computer security. Principles and Practice 3rd Edition. Pearson Education Schou, C., & Hernandez, S. (2014). Information Assurance Handbook: Effective Computer Security and Risk Management Strategies. McGraw Hill Professional. Agrawal, M., Campoe, A., & Pierce, E. (2014). Information security and IT risk management. Wiley Publishing.
- Your company has acquired Joggers PLC, a smaller company. The integration of the information systems can take up to 6 months, and until then Joggers PLC workers will continue following their policies. You have been tasked with ensuring that their IT practices will be safe and lead to a secure system. What advice would you give your manager regarding information security policies?Similar to reviewing security policies, a CASP+ might need to review business documents such as disclosure agreements or service agreements. You might be asked to review such a document by the company lawyer or a senior executive familiar with the conditions of the document, but not necessarily have the technical expertise to assess its feasibility. 1. Does your company have or make use of an NDA? If no, an NDA should be created. 2. Is the existing or proposed NDA a one-way or a two-way NDA? A one-way NDA protects only the information of the company. Two-way NDAs are designed to protect the confidential information of both the client and the company. 3. Does the NDA clearly define confidential information? 4. Are controls put in place to protect confidential information? 5. What are the obligations of the receiving party? What level of protection must they apply to the information they have received? 6. What time period applies to the NDA? Most NDAs don’t last forever and have a time…List and define the factors that are likely to shift in an orginizations information security environment? need 12 point 1 page double spaced please
- Please define the security words "critical infrastructure challenge" and "attribution problem."How can a state player work together with other governments and business groups to deal with these two security issues?The most common frameworks for cybersecurity are from the National Institute of Standards and Technology (NIST), International Organization for Standardization (ISO). American Institute of Certified Public Accountants (AICPA)[Center for Internet Security (CIS), and Cloud Security Alliance (CSA). What exactly are these organizations, and what functions do they provide? And how helpful are their frameworks?The stakeholders of a software company have four new security requirements that they are considering including in the next release of their flagship product: Two-factor authentication (2FA), Captcha for Bot Detection (CBT), Password Expirations (PEX), and Role-base access control (RBA). Given the time constraints, they may not be able to include all, so they need to prioritize these requirements based on three criteria: Maintainability (MA), Ease of Use (EU), and Integration Support (IS). They have the following pairwise preferences of the criteria: Maintainability is three times as important as Ease of Use Ease of Use is two times as important as Integration Support Maintainability is five times as important as Integration Support Based on the above information, do the following: 1. Using the AHP calculations, calculate the criteria weights and rank the three

