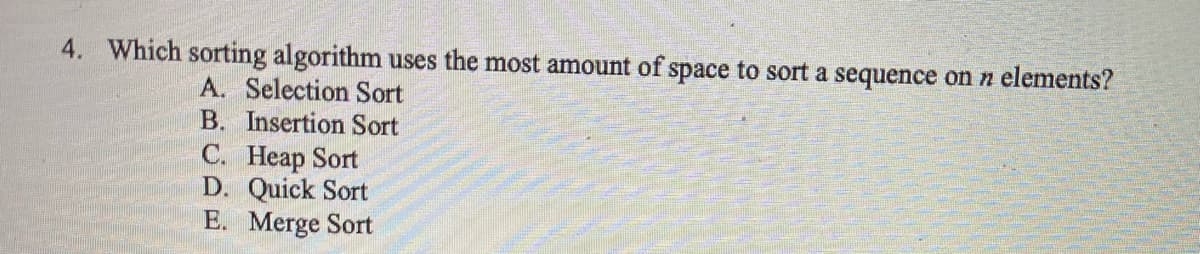
Which sorting algorithm uses the most amount of space to sort a sequence on n elements? A. Selection Sort B. Insertion Sort C. Heap Sort D. Quick Sort E. Merge Sort
Q: A new implementation may or may not have an adverse effect on the efficiency of your current system.…
A: Introduction: Even among operating systems in which reliability is a key priority, a broad range of…
Q: What is the significance and function of the central processing unit (CPU)? Explain your point of…
A: The CPU is the brain of a computer containing all the circuitry needed to process input store data,…
Q: 32/4 = 8 components (2-bit wide) I need the answer to part two, please If the size of each 4-bit…
A: The answer is
Q: Name at least six disciplines that are considered to be foundational to the subject of artificial…
A: Disciplines that spawned AI:…
Q: So, what exactly is Microsoft Office Excel (MS Office)? In what ways does Microsoft Excel differ…
A: answer is
Q: In your own words, sum up the lessons on Working with Data. To show your awareness of the…
A: According to the information given:- We have to describe differences between Microsoft Access…
Q: What adjustments may be made to the standard database development life cycle's data administration…
A: Given Data: What adjustments may be made to the standard database development life cycle's data…
Q: Assume you're employed by Xesoft as a software quality engineer. You've given the project title…
A: Assurance of Quality:Quality Assurance is the process of auditing quality criteria and the outcomes…
Q: Provide an example of a word processor or presentation software that is open source vs proprietary.…
A: A database management system (DBMS): Is software that enables you to store, modify, extract, and…
Q: What Makes SDLC Projects a Success?
A: SDLC is the process of planning, creating, testing and deploying. This life cycle is often a…
Q: explain why you choose time-sharing processing over batch processing.
A: Introduction: Time-sharing allows multiple individuals to utilise a computer system at the same time…
Q: Is it necessary to have a sound math foundation in order to use Microsoft Excel effectively? If yes,…
A: If someone practices every day and dedicates roughly 2-3 hours to learning the ideas, they can…
Q: List any five aspects of the Human Eye that allow it to collect pictures in the actual world.
A:
Q: Is there a typical amount of time before an interruption occurs? Is there any connection between…
A: Interrupts cause the operating system to change a CPU from its current task and to run a kernel…
Q: So why isn't it necessary to have a data model contain an object?
A: Introduction: So why isn't it necessary to have a data model contain an object?
Q: Give a brief description of the functions performed by each of the kernel's components in a typical…
A: The shell is a command interpreter : By requesting you for input, interpreting that input for the…
Q: Mpho has a spaza shop and he uses Microsoft applications to keep of his stock and to create posters…
A: A CIS (Computerized information system) is the analysis of data storage and processing, as well as…
Q: tal amount the user needs to pay according to the given conditions: The user has to pay…
A: add <- function(x, y) {return(x + y)}subtract <- function(x, y) {return(x - y)}multiply <-…
Q: To answer this question, why do HTTP, SMTP, and POP3 utilize TCP rather than UDP as the transport…
A:
Q: Why are TCP and UDP necessary for HTTP and DNS? Discuss.
A: HTTP relies on the TCP( Transmisson Control Protocol) standard which is connection based. Before a…
Q: Name at least six disciplines that are considered to be foundational to the subject of artificial…
A: The solution to the given question is: Introduction - " Artificial Intelligence - AI is a branch of…
Q: Name two network layer firewalls.
A: Firewall:- Firewalls may be used to keep external sources out of network nodes, internal traffic, or…
Q: True or False: The expression 6!0! equals 0.
A: The complete answer is given below:
Q: a) Prove that: Vne N, Σ" i2¹ = (n−1)2¹+¹ +2. i=0 b) Consider the sequence (Si)ie Z+ defined by s₁=1…
A:
Q: You, as a computer manufacturer, have the difficult task of creating high-quality computers with…
A: Start: Cleaning the cache and cookies regularly is an excellent approach to increasing computer…
Q: When it comes to communication, why do HTTP, SMTP, and POP3 utilize TCP instead than UDP?
A: Introduction: It is necessary for the application data to be received without any gaps in the right…
Q: Find the Fourier transform of the rectangular pulse signal x(t) defined by x(t) = Pa(t) = {1 |t| a
A: Answer
Q: Assume you're employed by Xesoft as a software quality engineer. You've given the project title…
A: The process initiation group is responsible for developing the project charter during the project…
Q: Find (49.3) -(00110110.0010) 10 BCD = (?)p BCD , with BCD weight (8421)
A: The answer is
Q: Discuss how the information system is influenced by the organization.
A: Organisational Influences: Organisational influence refers to an organisation's qualities or…
Q: What challenges could develop with the external database model if one group makes a modification…
A: When the data is one-to-one, a single table is ideal: Multiple tables are preferable for reducing…
Q: Overlay: What is it? Why are huge computer systems no longer need overlays
A: What is Overlay? Why are huge computer systems no longer need overlays?
Q: OSI and TCP/IP are two different models. What do you mean by "specifically"?
A: OSI and TCP/IP are the two most popular computer network models OSI -It is a reference model that…
Q: Name two network layer firewalls.?
A: answer is
Q: Given an array A that contains a set of positive integer values n, where 4≤ n ≤ 100. Now, consider…
A: According to the information given:- We have to write a code on the basic of instruction mentioned.
Q: List and describe all the words related to the quantification of data, such as bit, byte, and…
A: There are many units of information. We will list down some of them units(step2) with It's binary…
Q: "Mpho is very excited about the new information system to be built for his spaza shop. In this…
A: - We have to talk to Mpho about a database and benefits of database for Mpho's shop.
Q: What is the difference between asymmetric and symmetric encryption approaches for network data…
A: Asymmetric Encryption: This is a cryptographic scheme that consists primarily of two keys, one…
Q: What does it mean to have data stolen? What was the catalyst for this event? Who are you talking…
A: Stolen data may involve sensitive, proprietary, or confidential information such as credit card…
Q: Write a brief summary of the Working with Data lessons. As an academic writing style, show your…
A: Answer
Q: Why is audio and video traffic often sent via TCP rather than UDP on today's Internet?
A: Introduction: Here we are required to explain why is audio and video traffic often sent via TCP…
Q: black tree might do with O(log n) time complexity? Choose one of the following: a) Insertion and…
A: In computer science, a red-dark tree is a sort of self-adjusting double pursuit tree. Every hub…
Q: What are the consequences of a data breach for cloud security? What are some of the things that may…
A: The consequences for businesses that experience data breaches are severe and increasing. This is…
Q: What does the function delay() do? What is its default setting?
A: The answer is discussed in the below steps with example
Q: In this context, what does the word "computer scalability" mean?
A: The capacity of a system to vary its performance and cost in response to changes in application and…
Q: When comparing ISS to databases, what are some of the parallels and differences you see? In what…
A: On the International Space Station, the flight systems include: Habitation; Crew Health Care System…
Q: What role does data modeling play in the analysis process, and how valuable is t? How can we figure…
A: There are different analysis process of data modeling which is valuable and it can provide…
Q: A comparison between DHCP and APIPA is made. Why would a network benefit from including both of…
A: 1. We have to list the differences between DHCP and APIPA. 2. List out the benefits it provides when…
Q: What does "The values of exponent term B are continuous rather than discrete" indicate in the…
A: The solution to the given question is: Value of the exponential term B are continuous rather than…
Q: What distinguishes the software development process from software modeling? Describe how one aids…
A: Methodology of Software Development: In software engineering, a software process divides development…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Which of the following sorting algorithm(s) is/are divide and conquer type? a. Selection sort b. Insertion sort c. Merge sort d. Bubble sortJava - Fill in the table – use Big O notation Worst Case Average Case Binary Search of Sorted Array Insertion Sort Merge Sort Quick Sort without “median of three” pivot selection Quick Sort WITH “median of three” pivot selection Selection Sort Heap SortComputer Science Trace the following sorting algorithms for the next list. 025, 001, 585, 162, 382, 500, 200, 367, 333, 568, 529 Insertion sort Bubble sort Shellsort Radix sort Merge sort Quicksort
- Which of the following sorting strategies follows the divide-and-conquer principle? a Bubble kind. insert sort with a B. C Rapid sort. Algorithm D.Quick Sort is another sorting algorithm that follows a divide-and-conquer approach. The algorithm can be summarized in 3 steps: A pivot element is chosen, usually the first element. All elements smaller than the pivot are placed to the left of the pivot. This creates 2 partitions, elements greater than the pivot and elements less than the pivot. The 2 partitions are sorted using Quick Sort. Sample code in python3: def quick_sort(arr): def quick_sort_r(arr, start, end): if end - start < 2: # single element base case return # choose a pivot pivot = start # you may choose other elements store = pivot+1 # index to store less than elements # for all elements after the pivot for i in range(pivot+1, end): if arr[i] < arr[pivot]: # if element is less than pivot arr[i], arr[store] = arr[store], arr[i] # swap store += 1 # increment store index # swap pivot with last element in less than…Which one of the below uses divide and conquer approach? * a) Insertion sort b) Merge sort c) Shell sort d) Heap sort
- Which of the following algorithms is better to sort a mostly sorted data sequence? A data sequence is mostly sorted if only a handful of integers don't appear in the longest sorted subsequence. For example, the following data sequence is almost sorted since there is only one integer (0) out of place in a sorted sequence of numbers: 1, 2, 3, 4, 0, 5, 6, 7, 8, 9 Question 28 options: merge sort selection sort insertion sort quick sortThe study of computers and their uses. How can I pinpoint the exact moment when the quick sort transforms into the insertion sort? a lot of websites assert that the answer is 10, but why is that the case?Suppose the keyword sequence to be sorted is {12, 2, 16, 30, 28, 10, 16, 20, 6, 18}, give the steps that need to be taken to sort this sequence with the following algorithms: (not code algorithm) Selection sort Bubble sort Insertion sort Merge sort
- Which trail uses the following search algorithms? Bubble Sort Selection Sort Insertion Sort Merge Sort Quick Sort Heap Sort Use the moves and comparisons columns to justify each trail's search algorithm.If the list has the following items 17 9 11 30 8 20 35 7 5 45 3 28 Apply the quick sort on the above list by using the pivot is always the left item and find the following The list after a first partition call 2-The split point in the second partition callQuestion) Which of the following is NOT an O(n2) sorting algorithm? Heap Sort Bubble Sort Insertion Sort Selection Sort

