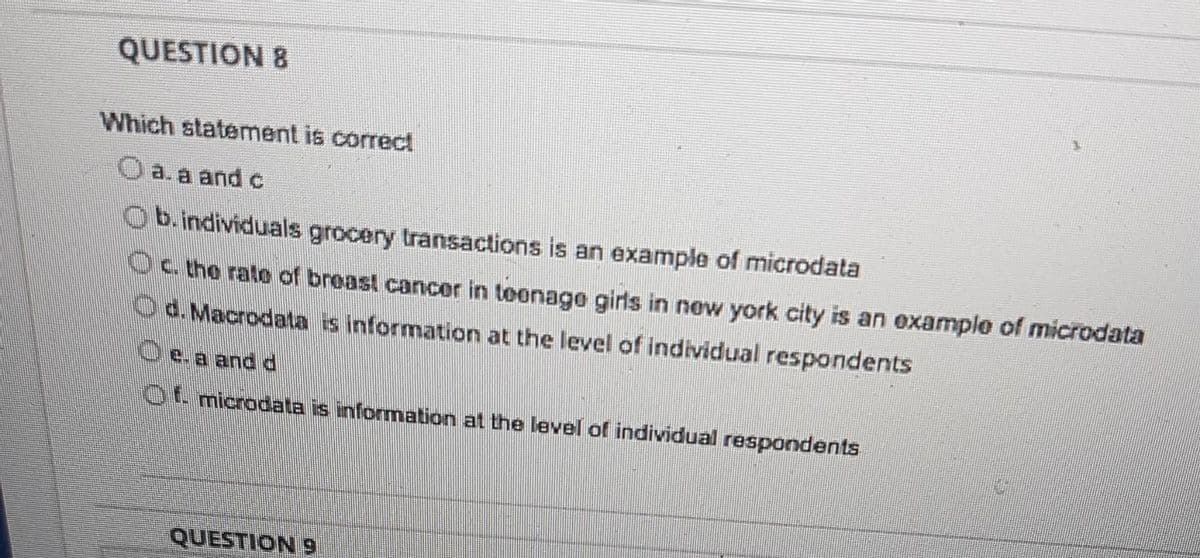
Which statement is correct a. a and c b.individuals grocery transactions is an example of microdata C. the rate of breast cancer in teenage girls in new york city is an example of microdata d. Macrodata is information at the level of individual respondents e. a and d Of microdata is information at the level of individual respondents OUECT
Q: What was Alan Turning known for? O Invented the Turning Machine. O Cracked the German Enigma code. O…
A: DISCLAIMER: “Since you have posted a question with multiple sub-parts, we will solve the first three…
Q: Question 2: Given the ending address and memory location address, determine the segment register…
A: Below I have solved the question on time .
Q: Dnetwork running at 1Mbps ignal speed in the cable is 2 would be
A:
Q: In the course of documenting the network, a network engineer uses the show cdp neighbor command on…
A: Solution: In privileged EXEC mode, you may use the show cdp neighbours command to display in-depth…
Q: Please answer in C++ Please Write a driver function definition called distance that takes as its…
A: Code in c++: #include <bits/stdc++.h> using namespace std; class PointType { public:…
Q: Find out whether any penetration testing is taking place on your network. Is data security a…
A: Penetration Testing: A penetration test, often called a pen test, ethical hacking, or simulated…
Q: Why is it more common to engage in multitasking, also known as multithreading, as opposed to having…
A: Having multiple processes means, each process having its own virtual memory. These are separate.…
Q: Why is authentication still an issue in today's digital age?
A: Authentication: Authentication is the process of verifying a user. This approach associates incoming…
Q: How does Model-View-Controller fit into the bigger picture of how web applications are structured?…
A: Answer: The most famous software architecture, by a wide margin, is the Model-View-Controller, or…
Q: What are the key distinctions between backward integration and forward integration, and how may they…
A: What are the key distinctions between backward integration and forward integration, and how may they…
Q: Draw a graph with the following conditions: a. 11 nodes total b. Directed, Acyclic c. Would have 5…
A: A directed graph is a graph in which a vertex can have both incoming as well as outgoing edges. An…
Q: SNORT is a intrusion detection system that create alerts (both true positive and false positives) .…
A: Answer: SNORT is a intrusion detection system that create alerts (both true positive and false…
Q: What exactly is fragmentation, and how does it effect your life? Provide examples to distinguish…
A: Fragmentation is a problem where the memory blocks cannot be allocated to the processes due to their…
Q: Given the runtime, (n) = n° + n +n+1 show that a. f(n) = 0(n*) b. f(n) = e(n³) c. f(n) = (n²)
A: The given Function f(n) = n3 + n2 + n + 1 The higest power in the given function is n3 So ,…
Q: If you were in charge of the administration of a network, in what kinds of scenarios would you…
A: Introduction: Static routing is appropriate for networks with just a few routes, such as a home…
Q: Explain in your own words what the point of looking at notes in page view is. Explain. Answer in 2-3…
A: NOTES PAGE VIEW: The notes page view is one of the ten available views for PowerPoint windows. This…
Q: in Object's data. For example, object hold 4/21/2022 as the date and if user of this object calls…
A: program is using calender method
Q: What are the key advantages and disadvantages of cloud-based data storage?
A: The advantages are as follows: 1) Access your data anywhere: As data is stored remotely in cloud so…
Q: SAMPLE DISPLAY OUTPUT: Arithmetic Operation Enter number 1: 10 Enter number 2: 5 [A] [+] Addition…
A: The elif allows us to check for multiple expressions.
Q: Write expression as sum of Minterms for Any One Neutral function F over 04 variables A, B, C, and…
A: Here we have given a solution as sum of minterms for one neutral F over 04 variables A,B,C and D.…
Q: Because of its defining qualities, wireless networks are inherently problematic, and this gives rise…
A: Institution: Wireless networks generate a slew of issues as a result of their essential features.…
Q: a) _____ is used to identify the devices and memory connected to the CPU. b) The number of tasks…
A: INTRODUCTION: Here we need to tell is used to identify the devices and memory connected to the CPU.
Q: Consider the importance of wireless networks in today's emerging nations. In a variety of…
A: WLAN is a wireless computer network that connects two or more devices using wireless communication…
Q: Create a Crow’s Foot ERD to include the following business rules for the EaonCo company: Each…
A: INTRODUCTION: The use of pictorial symbols to show the many sides of the connection is the most…
Q: Why is it necessary to rearrange the database structures?
A: Introduction: Database: It is a logically organized collection of data stored on a computer and…
Q: Defining the role of OLAP in descriptive analytics is essential.
A: OLAP:- The term "online transaction processing" (OLTP) refers to the complete process of refreshing,…
Q: Write a program that helps Poslaju customers in calculating postage fee. Poslaju National Courier…
A: Note :- You have not mention the language of the program so. i'm answering your question in C…
Q: The oldest and most well-known (wired) communication network in the world, the telephone network,…
A: The oldest and most well-known (wired) communication network in the world, the telephone network,…
Q: What are the possible consequences of cloud computing for our society? What is a synopsis of could…
A: Answer: Cloud computing: Cloud computing allows client devices to access data from remote servers,…
Q: how communication occurs a cross local ethernet network
A: Introduction: A local Area Network (LAN) is a data communication network that connects multiple…
Q: Suppose three algorithms A, B, and C, can be implemented to perform a task. The algorithms have the…
A: The answer is
Q: Under what circumstances do we prefer to use dynamic programming, and why? Exhibit your answer with…
A: What circumstances encourage dynamic programming, and why do we pick it?Use examples to demonstrate…
Q: Make sure you know what a file extension is and what it does in your work before you use it
A: answer is
Q: Oracle's ability to handle large objects is a great benefit to a developer. However, object-oriented…
A: LOB or large object use to hold a large amount of data. It can hold 8 terabytes to 128 terabytes…
Q: What are the many forms of malicious software that have a worldwide impact, and what are their…
A: Launch: Malware is malicious software. Malware can do the following things. tamper with computer…
Q: What are the consumer myths in software development, and what is the reality?
A: Answer of the given question: CUSTOMER'S MYTH Legend: An overall assertion of goals is adequate to…
Q: Give two real-life problems / scenarios where you can use a graph algorithm to solve it. Explain how…
A: Graph is a very important data structure that is used to solve various real-life problems.
Q: Q1:Write an algorithm for printing numbers less than a given number (n) that are divisible by 5.…
A: ALGORITHM:- 1. Take input for the value of n from user. 2. Traverse from 1 to n-1. 3. Check if the…
Q: Using eclipse, create a simple Java program that displays code snippets for creating a new project…
A: public class Tracker { private int deviceID; private String deviceName; private int accuracy; //…
Q: Write a code snippet of a function that returns the average of a set of marks for a given students.…
A: As there is no programming language is mentioned in the question, So I will answer this question…
Q: How can we check the history of ?commands used by only clicking the up direction button using the…
A: How can we check the history of ?commands used Here we use some commands like cd .. and d: and…
Q: hes are different. Two are different. What are the primary differences and similarities between the…
A: Developing applications would be unimaginable without databases. For our projects to work…
Q: What are routing metrics, and how can they be efficiently used?
A: What Is a Router? A router is a device that examines the contents of data packets that are…
Q: The oldest and most well-known (wired) communication network in the world, the telephone network,…
A: Interview: Telecommunications networks often use circuit switching as a networking strategy. Before…
Q: What three factors are taken into account when making hardware decisions?
A: Introduction: Hardware refers to the components of a computer system that are utilised for input,…
Q: b) Construct two leftmost derivations of the string aabb. c) Build the derivation trees for the…
A: Solution:-
Q: How much confidence should you have in the protection of your personal information? What is the best…
A: Personal information containing private data and financial related information is mainly desirable…
Q: What changes in computer processes have occurred as a result of the existence of resident monitors?
A: Given Question: What changes have occurred in computer operations as a result of the presence of…
Q: What are the consequences of the cloud computing revolution? Have you got Collaboration on your…
A: The goal of the research is to provide an overview of the advantages and dangers of cloud computing…
Q: What exactly is meant by the term "virtualization" in reference to cloud computing?
A: Given Ask for an illustration of the virtualization idea in Cloud Computing.
Step by step
Solved in 2 steps

- EMP(empno, ename, job@tle, managerno, hiredate, sal, comm, deptno) DEPT(deptno, dname, loc)a) Find Employees along with their Manager name.b) Find the Employees who are working in Smith's departmentc) Find the Employees who get salary more than Allen’s salary.d) Display employees who are geZng maximum salary in each department (without using aggregatefunc@on).I need to calculates and output the GPA of each students from the output from the code below. The txt file used in the code below is as follow: Tom IT 500 Business Analytics:94.6; IT 512 Project Management:88; IT 513 Information Security:91.2; ------------------------------------------- Tim MBA 503 Foundations of Business Statistics:85; IT 501 Fundamentals of Java Programming:70; IT 500 Business Analytics:64; IT 516 Social Media Analytics:77; IT 515 Organizational Behavior:50; ------------------------------------------- Smith MBA 503 Foundations of Business Statistics:20; IT 509 Data Management:89; IT 512 Project Management:90; ------------------------------------------- Davis MBA 503 Foundations of Business Statistics:77; IT 501 Fundamentals of Java Programming:89; IT 510 Information Technology Management:88; IT 517 Big Data Analytics:90; ------------------------------------------- Judge MBA 503 Foundations of Business Statistics:95; IT 501 Fundamentals of Java Programming:88;…Using a graphics program, develop an entity-relationship diagram for a database application for an Internet bookstore where students buy textbooks from a salesperson and receive invoices for their purchases. Use Figure 3.5 as a guide.
- a) What actions or steps in Excel will arrange the given spreadsheet in alphabetical and ascending order of Surname?b) What actions or steps in Excel will produce a list/display of those who had a sales revenue of £138,500 or more in the year?c) Write the Excel function to determine the number of salespersons who had a Sales Total above the given “Average Sales Total”?d) Which type of graph will be suitable for representing the above sales revenue by regions? e) In which column(s) might replication have been used? f) What formula was used to arrive at the Company Sales Total?What does this mean 2. The information below includes what was sent by the academic advisor (Program Checklist) (York U BSc Honours Computer Science) Foundational science: six credits from SC/BIOL 1000 3.00, SC/BIOL 1001 3.00, SC/CHEM 1000 3.00, SC/CHEM 1001 3.00, SC/PHYS 1011 3.00, SC/PHYS 1012 3.00, SC/PHYS 1010 6.00, SC/PHYS 1411 3.00, SC/PHYS 1412 3.00, SC/PHYS 1410 6.00, SC/PHYS 1421 3.00 General Education and/or Science Breadth See sections "A" and "C" A. General Education Requirement:non-science requirement: 12 credits from the approved list of courses and subject areas in your Academic Calendar;mathematics: satisfied within the core requirements;computer science: satisfied by the major requirements;science: satisfied by the BIOL, CHEM, or PHYS labs as stated on your degree checklist C. Science Breadth:24 credits in science disciplines outside the major, of which three credits must be at the 2000 level or above. 15 of these 24 credits are satisfied by the general…B. Please complete the following question. Make sure you are responding to all parts of the question and show all your work. As a tip let the marks assigned be a guide as to how much information is required to respond. The attached datafile awards_data.csv contains two variables: the type of program [prog] in which the student was enrolled (i.e., general, academic, or vocational) and the score on their final exam in math [math]. Use α = .05 for all analyses. 1. Use the information about the variables to develop a research question for a one-way ANOVA and conduct the analysis. Are the assumptions met? Please include the appropriate statistics or information to support your answer. What do you conclude? Present your answer in APA.
- 5. Give an example of how or when you have used information processing. Trite vour response below: 6. Fill in the blank. Information is processed usingCreate pro forma statements in your spreadsheet software. Each pro forma statement should have a different projection. At least one should include a revenue increase and at least one should include the receipt of capital funding. How do I do this? Formulas?Question 15 kk. subject: c# Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
- 1) Which of the following best explain why information should be complete in form? a. An incomplete information makes the information not up to date b. An incomplete information is costly since that would up to the cost of producing report c. An imcomplete information is more dangerous because the information has no logical coherence whatsoever with the problem d. An incomplete information leaves the decision makers hanging not knowing what to do next 2) Pedro developed would like to developed an application for the school. Pedro wants this application to be used by students whether they have internet connection or not. What type of mobile application would you suggest to Pedro to developed? a. Pedro should just stay put , study and go home. Pedro should not be a Jollibee b. Pedro should used hybrid application , Pedro needs to consider the cost of development and nowadays everyone has internet c. Pedro needs to developed a native…d. Retrieve the name and transcript of each senior student (Class = 5) majoring in CS. A transcript includes course name, course number, credit hours, semester, year, and grade for each course completed by the student. e. Retrieve the names and major departments of all straight-A students (students who have a grade of A in all their courses). f. Retrieve the names and major departments of all students who do not have a grade of A in any of their coursesSpecial Instructions: a. Refer Internet, Elibrary, Library Books & Handouts. (Wikipedia reference is not considered as a valid reference)b. Mention the Books and websites referred.c. Explanation should be neatly hand written (either in blue or black colour pen) with neat sketches in pencil. Name and ID should be mentioned on each sheet.d. Neatness and referencing- carry 1 mark eache. Assignments should be uploaded in PDF form.Academic Integrity & Plagiarism Policy: The student should be ready to prove the authenticity of the work done. If any forms of plagiarism/reproduction of answers are discovered, student will be asked to repeat the assignment, if first offence; otherwise will be awarded zero marks.To my Lecturer Mr. Darsan R S, I certify that all of this work is done by my self as in accordance with the Academic Integrity / Plagiarism policies.I am responsible for any violations with regard to this.

