Why should we we generally use Exceptions rather than error codes? A. Error codes ensure the program crashes, while Exceptions give the user a chance to fix the exception B. Trick question: we should generally use error codes, not Exceptions. C. Error codes can be easily mistaken for legitimate output, whereas Exceptions cannot be D. Exceptions are easier to write than returning error codes
Why should we we generally use Exceptions rather than error codes? A. Error codes ensure the program crashes, while Exceptions give the user a chance to fix the exception B. Trick question: we should generally use error codes, not Exceptions. C. Error codes can be easily mistaken for legitimate output, whereas Exceptions cannot be D. Exceptions are easier to write than returning error codes
Chapter12: Exception Handling
Section: Chapter Questions
Problem 3RQ
Related questions
Question
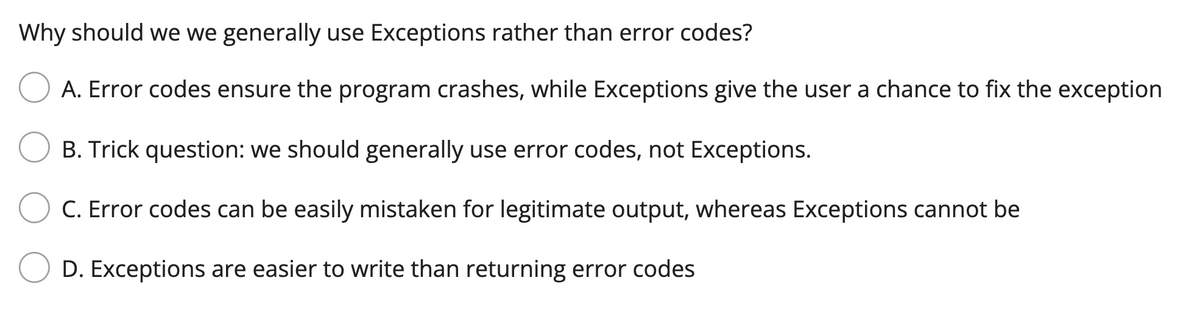
Transcribed Image Text:Why should we we generally use Exceptions rather than error codes?
A. Error codes ensure the program crashes, while Exceptions give the user a chance to fix the exception
B. Trick question: we should generally use error codes, not Exceptions.
C. Error codes can be easily mistaken for legitimate output, whereas Exceptions cannot be
D. Exceptions are easier to write than returning error codes
Expert Solution
Step 1
Answer:
We need to explain the what are the correct option regrading the error handling and exception . so we will see in the more details explanation.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning