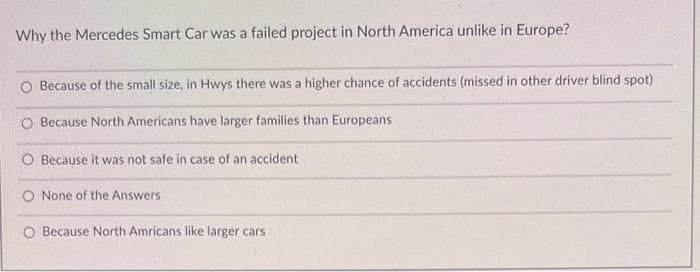
Why the Mercedes Smart Car was a failed project in North America unlike in Europe? O Because of the small size, in Hwys there was a higher chance of accidents (missed in other driver blind spot) Because North Americans have larger families than Europeans Because it was not safe in case of an accident O None of the Answers O Because North Amricans like larger cars
Q: The case graph below by using a predetermined solution approach Given adjacency matrix as follows: A…
A: branch and bound: The shortest tour that is going through all the vertices once and returning back…
Q: What is a memristor and how does it work as a data storage medium?
A: It is an electrical component which limits the flow of electric current in a circuit and store the…
Q: A LAN, or local area network, is a networking technology that connects computers and other devices…
A: Check below mentions step for solution
Q: If yes, then you should use this Microsoft Baseline Security Analyzer
A: A solid familiarity with Microsoft's Baseline Security Analyzer. With the Microsoft Baseline…
Q: Why are telecommunications and information networks unique from other types of networks?
A: Introduction: In order to link different devices in order to exchange data and use other services,…
Q: *) Derive Grammar for the following languages: Question 4 ( I. {b, abc, aabcc, ... . a^ bc¹} = {a^…
A: Context Free Grammar: A grammar contain a context free grammar then it must be a context free…
Q: which of the following would most likely be a self cancelling prediction
A: you can expect the speech you have to deliver at a work event to go terribly, so you won't be…
Q: A country has coins with k denominations 1 = d1 < d2 < ... < dk, and you want to make change for n…
A: The problem of making change refers to the task of finding the smallest number of coins needed to…
Q: Are the principles of a culture of security applicable to organizations that do not create…
A: The solution to the given question is: Yes , the principle of a culture of security are applicable…
Q: the set of values is a possible bootstrap sample
A: Given :- In the above given question, the statement is mention in the above given question Need to…
Q: We create a suffix trie out of the string AAAB$. The number of nodes in the trie is Please dont…
A: In this question, it is asked to calculate the total number of nodes in a suffix trie. In suffix…
Q: Question 15 pap Suppose we have a Monte Carlo algorithm, A, and a deterministic algorithm, B, for…
A: Dear Student, The answer to your question is given below -
Q: 1. How does exception handling work in Java? 2. What are exception handling keywords in Java? 3. How…
A: According to the policy we can only give the answer of first three questions, repost your remaining…
Q: When considering the overall structure of web applications, what role does the Model-View-Controller…
A: The process of creating a set of instructions that tells a computer how to perform a task is known…
Q: How does information security differ when viewed from a top-down vs a bottom-up perspective? The…
A: Top-down strategy: The top-down technique involves breaking down a system into smaller units in…
Q: Given a binary search tree and k integers stored in the tree, devise an O(n+h) time algorithm to…
A: According to the information given:- We have to define binary search tree and k integers stored in…
Q: Implement image segmentation method into biomedical image data (any data, for example cancer image)…
A: Introduction : Image segmentation is the process of dividing an image into multiple segments, or…
Q: Discuss a made-up scenario involving user logins and passwords. Note down the many different forms…
A: According to the information given:- We have to discuss a made-up scenario involving user logins and…
Q: How does the usage of a function improve your life?
A: FUNCTION: In the context that these functions are subsequently employed for the purpose of carrying…
Q: When talking about the cloud, what does the phrase "virtualization" relate to?
A: Virtualization: The given question asks for an illustration of the virtualization idea in cloud…
Q: Python: Given the following declarations, what is the value of each of the following boolean…
A: The Python code is given below with output and explanation
Q: Can you tell me about the most cutting-edge methods for defending your database against intrusion
A: A database is a readily accessible, controllable, and uneatable collection of information. It's also…
Q: Bob has sent his secret number m to Alice via secure RSA encryption. Break his ciphertext to find m.…
A: Solution:- RSA algorithm is an asymmetric cryptography algorithm. Asymmetric actually means that it…
Q: 1.4-6 Maximum end-end throughput (e). Consider the scenario below where 4 TCP senders are connected…
A: Below I have provided the solution of the given question;-
Q: If you are searching for a key in a binary search tree, explain how the shape of the tree affects…
A: The shape of a binary search tree can significantly affect the efficiency of finding a key within…
Q: Python: What is the output of the following code? list1 = list(range (1,10,2)) list2 = list1…
A: The statement list(range (1,10,2)) will initialize the list1 with a list with values as 1, 3, 5, 7,…
Q: Python: What is the result of each of the following expression? 。5+7*2 •(5 + 7)*2 • 3 ** 2 + 10 / 4…
A: Python Operators: 1) + Addition: It adds the values on either side of operator. Example: If a=10 and…
Q: The simplification of the Boolean expression (A’BC’)’ +(AB’C)’is
A: Let F = (A’BC’)’ +(AB’C)’ Apply demorgan's law. = (A+B'+C) (A'+B+C') Apply distribution law. =A.A'…
Q: Compared to wired networks, wireless ones provide faster throughput, but they still lag behind the…
A: Wireless networking serves as a connection between various equipment locations in residences,…
Q: Figure out the difference between file extensions and how you might benefit from them in your job.
A: A file extension, often known as a "extension," is a suffix that is applied to the end of a filename…
Q: A detachment of n soldiers must cross a wide and deep river with no bridge in sight. They notice two…
A: Algorithm: 1. Start 1. Initialize n to 10, boys to 2, boatSize to 1, and crossings to 0. 2. While n…
Q: Question 4 expain in brief What is the role of AWS in the field of Artificial intelligence?…
A: Introduction Artificial intelligence (AI) is indeed the area of computer science that focuses on…
Q: True or False: When law enforcement gets involved, intellectual property can be taken away from an…
A: Introduction The term "intellectual property" describes the accumulation of intangible assets that…
Q: Imagine Z9* a cyclic group. What is order of an element a=2 and show the elements? Show all your…
A: A cyclic graph is a graph containing at least one graph cycle. A graph that is not cyclic is said to…
Q: True or False: Object privileges allow you to add and drop users
A: There are two types of (grants) privileges that can be granted in a database: * System privileges *…
Q: and calculate the worst-case running time for the following algorithm, show the steps total = 5; for…
A: Dear Student, The answer to your question is given below -
Q: In terms of throughput speed, wireless networks are faster than wired networks; nevertheless, the…
A: Your answer is given below.
Q: Every running thread in a JVM has access to the same method area, which is shared by the JVM. What…
A: To do: All threads running in the virtual machine environment share a JVM's method area.
Q: When it comes to protecting sensitive data, what's the difference between a "top down" and a "bottom…
A: Information protection: Data security is referred to as information security, and it is one element…
Q: 1) What is ESP32 Camera? What is used for?
A: According to the policy we can only give the answer of first questions, repost your remaining…
Q: For this question, mark all answers that apply: Assume any float or int is stored in 32 bits and…
A: We will answer this question and tell which statements about floating point arithmetic are true or…
Q: Why does TCP predominate over UDP when it comes to data transfer?
A: TCP stands for Transmission Control Protocol and UDP stands for User Datagram Protocol. Both TCP and…
Q: Analyze the pros and cons of using agile approaches to system development.
A: Understand agile approach before presenting its benefits. Agile approaches promote a collaborative,…
Q: If you want to convince others of the benefits of dynamic programming, you should utilize real-world…
A: Introduction: After we have determined the appropriate response, we must next proceed to prepare…
Q: A _______ connects hardware devices such as computers, printers, and storage devices that are all in…
A: Hardware:Hardware refers to any physical components of a computer system, including the motherboard,…
Q: Write a regular expression in python that checks if a string in python has a length of exactly seven…
A: Your Python program is given below as you required with an output.
Q: If you were to look at a technical design, what font would you say is often used?
A: The text style that is chosen should provide the technological design an appealing look while also…
Q: .Give a DFA for the NFA in Figure 3.36 b on page 124. (Deterministic.?
A: In the Given NFA the input alphabets are {a,b, A} starting state=1 final state={1} set of states={1,…
Q: What is the difference between Web Services and SOA, and how can it be explained?
A: SOA-architectureIt's a software design technique in which a large programme is separated into…
Question v
Step by step
Solved in 2 steps

- Molly is a promoter of XYZ Co. Ltd, which is expected to sell AI robots. Molly signeda contract with Ann before the company is incorporated to purchase AI software for theproposed XYZ Co. Ltd. After the efforts made by Molly, XYZ Co. Ltd is wellestablished later. However, after Ann provided the AI software to XYZ Co. Ltd, Annreceived no payment. Apply common law rules as well as Companies Ordinance (Cap.622) on analyzing this case and discuss if XYZ Co. Ltd or Molly should be liable tomake payment to Ann.Robots may be trained to do jobs that might be harmful to human health, insulting to sensitive audiences, or just too monotonous for human workers. If you think robots could eventually outperform humans in some jobs, provide an example. Provide justification for why you think it's preferable for this work to be performed by a computer rather than a human.The widespread availability of mobile phones now provides enormous convenience, but may its abuse lead to the loss of this benefit? Mobile phones are banned in many classrooms due to the distraction of constant texting and the use of the phone by dishonest students to cheat on exams; similarly, camera phones are now banned in many fitness centers, park restrooms, and other similar facilities because some people have used them inappropriately to take compromising photos. What do you think about these responses to cell phone abuse? Is universally prohibiting cell phone use the only solution, or are there alternative methods to assure responsible usage? Should individuals who exploit technology in a dishonest or immoral way face harsher penalties? .
- Nathan is playing an online video game. He discovers that all the avatars for the games are male. He doesn’t think that this is equitable, so he writes the gaming company and advocates for this to be corrected. What type of bias is Nathan advocating against? A)confirmation bias B)framing bias C)bandwagon effect D)gender biasDriverless cars have the ability to provide many benefits, from helping the elderly remain independent to reducing the number of road accidents. However, disasters can still happen and someone needs to be held accountable. Who should pay the damages – the car owner, the car producer, the government, some other entity? Discuss your thoughts on this technology, whether you find it useful, necessary, unnerving, interesting, etc. and who you think should be liable for accidents involving driverless cars.According to the findings of a research on patient travel times, trips to the doctor took more time for individuals of color and the unemployed. Another problem that people who live in rural locations face is having access to medical treatment that is of a sufficient standard. Is it feasible that the use of video telemedicine will make healthcare more accessible to populations who are currently underserved? Is there a way that the underprivileged may have access to more healthcare services with the use of this technology?
- In what ways may they be termed visible radiation? Pick the optimal option. t) Compile a record of your career highlights and hang it in the office hall of fame Using a digital whiteboard, important policies and procedures may be displayed for all employees to see. Keep your employees up-to-date on the latest happenings by posting information on digital displays or whiteboards. AboveSolutions built on the Internet of Things may benefit both vertical and horizontal sectors. When these methods are applicable in a broad variety of contexts, we have successfully implemented an industry-wide approach. Both humans and the Internet of Everything win out from this.Check out the illustrations provided. Pick two and classify them as either "horizontal" or "vertical" solutions for the market. Justify.Automated temperature regulation that responds to occupancy and external circumstancesWhen ingested, these microchips provide information to a doctor.You guys use AI tool to answer. Last time I found plagiarism and AI detection in my answer. Now If you will use these things I'll surely give multiple downvotes and will report ⚠️ sure.
- What do you consider to be one of the most significant uses of AI in the contemporary workplace? Start a discussion about it with someone. Please support your assertion with a concrete example of such a use of AI. Using AI, explain how your firm has benefited from this particular use of the technology and to what degree you believe it has been effective.Artificial Intelligence (For this scenario describe how you would develop an inteligent system to solve this problem) Every day we get dozens of email notifications and most of them are spam. Describe a tool which can classify the emails as spam or non-spam based on the content of the email alone.Charlie sat at his desk the morning after his nightmare. He had answered the most pressing e-mails in his inbox and had a piping hot cup of coffee at his elbow. He looked down at a blank legal pad, ready to make notes about what to do in case his nightmare became reality. Suppose Charlie encountered resistance to his plans to improve contingency planning. What appeals could he use to sway opinions toward improved business contingency planning?

