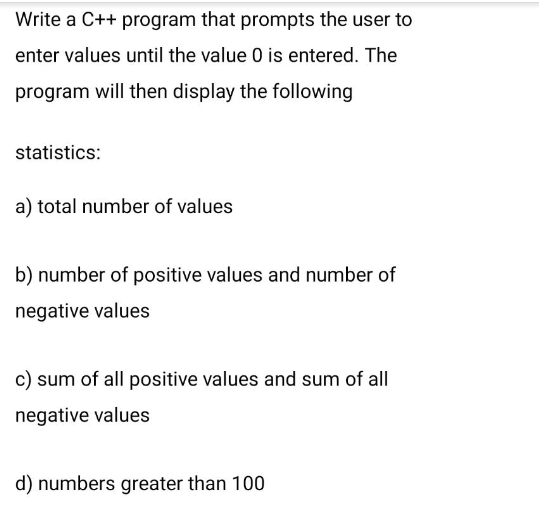
Write a C++ program that prompts the user to enter values until the value 0 is entered. The program will then display the following statistics: a) total number of values b) number of positive values and number of negative values c) sum of all positive values and sum of all negative values d) numbers greater than 100
Q: Could you maybe clarify what you mean particularly when you mention "principle of non-repudiation"?
A: The principle of non-repudiation often used in computing, information security and communication…
Q: What six instructions at the paper factory result in the creation of the design?
A: Given: Each processor the chain will have its own implementation for processing a command. Every…
Q: another is exposed. Teless
A: What is wireless Communication? Wireless Communication is the exchange of data between at least…
Q: In what way do morality matter in the age of information technology?
A: Information Technology: Information technology (IT) is the creation, processing, storage, secure…
Q: Your great-aunt and -uncle have given you a brand-new computer monitor out of thoughtfulness. You…
A: Instructions for connecting a monitor to a computer: Users must use caution when using a desktop…
Q: We believe that Flynn's taxonomy should be expanded by one level. What distinguishes a high-level…
A: In parallel computing, tasks are divided into independent components that may run simultaneously.…
Q: What are the similarities and differences between the waterfall model and the incremental and…
A: Waterfall Model: The waterfall model is one of the most popular and straightforward software…
Q: All partitions on a hard disk drive must utilize the same filesystem once it has been formatted.…
A: A hard drive needs to be partitioned and formatted before it can be utilised. Your final drive count…
Q: Could you maybe clarify what you mean particularly when you mention "principle of non-repudiation"?
A: Non-Repudiation Principle: A statement's non-repudiation ensures that you won't be able to challenge…
Q: For instance, personal firewalls and network firewalls, both of which are now offered for sale on…
A: In light of the query Devices linked to your network are shielded from online intruders by a home…
Q: Explain the figure below Satellite Uplink Antenna Earth station Terrestrial system جسم User Downlink…
A: A combined structure of Transmitter and Receiver is commonly known as Transceiver.
Q: $ ls -l foo --Wx-w---x 1 uli101 users 813 Sep 13 20:30 foo What command line using octal method sets…
A: chmod Command: It is possible to modify a file's permissions using the chmod command. Changes to a…
Q: Describe the advantages and disadvantages of the various Wi-Fi security strategies.
A: Given Wifi safety measures. and to be aware of these systems' benefits and drawbacks. Benefits of…
Q: se real-world examples to illustrate concepts like data manipula
A: Data Manipulation: *) The process of editing or changing information to make it better organized…
Q: the Spiral approach has at least three advantages over the Waterfall method. Put the two side by…
A: Waterfall Method: The Waterfall technique, often referred to as the Waterfall model, is a sequential…
Q: Purchase application development tools from the following suppliers: Please support your answer with…
A: By providing features like an integrated development environment (IDE), code-free development,…
Q: What further techniques exist in addition to message authentication?
A: Given: In cryptography, a message authentication code (MAC), often called a tag, is a brief piece of…
Q: How precisely can a Demilitarized Zone, often known as a DMZ, improve the security of a network as a…
A: let us see the answer:- INTRODUCTION:- DMZ OR DEMILITARIZED ZONE:- An organization's internal…
Q: What exactly does someone mean when they say they are talking about a "wifi access point"? What…
A:
Q: Initially, Linux developers chose a non-preemptible kernel because... How does a non-preemptible…
A: One is a DOS-based system with a cooperative, non-preemptive kernel. It was created in this way…
Q: How can functions reduce the amount of written code and make code easier to read/follow? Provide a…
A: A function is basically a "chunk" of code that you may reuse rather than writing it out repeatedly.…
Q: Purchase application development tools from the following suppliers: Please support your answer with…
A: App development software is a tool that facilitates the app development process by offering features…
Q: Watchdog timers are a need in many embedded systems for a variety of reasons
A: Watchdog timers in embedded systems are crucial: The simplest kind of embedded system has a watchdog…
Q: After receiving a message from your company's mail server, assume you have to confirm that your…
A: Introduction: The phishing attack, a sort of malware that involves password hacking, occurs when an…
Q: Why can the number of iterations only increase so far when utilizing the waterfall model?
A: Introduction There are a limited amount of iterations in the waterfall model. The waterfall model is…
Q: Both UDP and TCP use port numbers to identify the destination entity when delivering a message. Give…
A: 1-> An application process is assigned a process identifier number (process ID), which is likely…
Q: How may the SQL language be used to change a table's structure? Which of these significant changes…
A: Table's Structure: Rows and columns are represented by cells in a table's horizontal and vertical…
Q: o Find and fix the three errors in the given code. o Use the following sample input values to test…
A: 2. In the given code, there is only one error. The error is in the below statement:…
Q: How may a LAN's resiliency and availability be ensured most effectively?
A: The answer is:-
Q: A Boolean operator may be used to find information on two different subjects at the same time. Which…
A: Here's the solution:
Q: Why is the number of iterations in the waterfall approach capped at a certain amount? The reason why…
A: Introduction: The waterfall approach uses a linear strategy, sometimes known as a software…
Q: When it comes to sending and receiving email over the internet, what are the three protocols known…
A:
Q: Both UDP and TCP use port numbers to identify the destination entity when delivering a message. Give…
A: Answer. 1.An application method is allotted a method symbol variety (process ID), that is probably…
Q: In general, character devices are faster in transmitting data than block devices are. What do you…
A: What are Character and Block Devices? Block Devices Block storage devices can be used for both…
Q: Please provide examples for each of the three most popular file management techniques.
A: Give illustrations for each of the three main file management strategies. Ordinary files, usually…
Q: Assume the following: TLB Page Table Set # Way #0 Way #1 Way #2 Way #3 0: V=Y;Tag=0x2a…
A: The page size is 512 (= 29) bytes, so lowest 9 bits of virtual/physical address denote page/frame…
Q: The top five network topologies that are most often used should be included. According to your…
A: Network Topology Types: A bus topology Every node, or piece of equipment on the network, is…
Q: What is the primary difference between having a license to use software and holding the copyright to…
A: Here is the answer below:-
Q: Both UDP and TCP use port numbers to identify the destination entity when delivering a message. Give…
A: UDP(User Datagram Protocol): It is used for communication throughout the internet. It…
Q: Why can the number of iterations only increase so far when utilizing the waterfall model?
A: Answer : In waterfall model the no of iteration increase as per requirement of the project as if we…
Q: Where can I get a description of the Iterative Waterfall Model's steps? Another excellent choice is…
A: Definition: A traditional model used in the system a development life cycle to design a system with…
Q: How may discrete data be created from a still image? How precisely is the source code for a video…
A: Analog Digital to analogue conversion: Analog photographs resemble the images that people view.…
Q: List two ways in which the OSI reference model and the TCPAP reference model are the same. Now list…
A:
Q: What three requirements must a network meet in order to be successful and efficient? Please provide…
A: To be a successful and efficient network there are certain requirements which should meet. The three…
Q: What portions of the law permit the use of a work, such as an image, a diagram, a chart, or an…
A: The answer of the question is given below
Q: Are there some database management duties that are more vital than others?
A: A database management system (or DBMS) is basically just a modernized information keeping…
Q: Consider the following design problem concerning implementation of virtual-circuit service. If…
A: Here two implementations for virtual-circuit service are given. We need to identify which…
Q: What actions from the attacker are necessary for a sniffer attack to be deemed successful? How might…
A: Your answer is given below. Introduction :- Sniffing Attack: The act of intercepting or…
Q: Give three justifications for why the spiral model is superior than the waterfall strategy, and…
A: three justifications for why the spiral model is superior than the waterfall strategy, Risk…
Q: What was the rationale for the inclusion of timers in our rdt protocols?
A: Institution: For safe data transfer, sequence numbers inform the receiver whether fresh or old data…
Step by step
Solved in 4 steps with 2 images

- In C++, write a program that calculates and prints a monthly paycheck for an employee. The net pay is calculated after taking the following deductions from the employee's gross salary: Federal Income Tax: 17.5% State Tax: 9.1% Social Security Tax: 6.2% Medicare Tax: 1.45% Retirement Plan: 9.29% Health Insurance: $51.48 Life Insurance: $3.71 Your program will prompt the user to input the employee ID, the employee name, and the employee's monthly gross salary. The program will calculate the deductions listed above, along with the percentage of take home pay (defined as the net pay divided by the gross salary). After calculating each deduction and percentage, the output will be printed to the screen (see example output below). Requirements All decimal numbers must be formatted to 2 decimal places. Ask for the employee's ID first, then full name (can include spaces), then the salary. The prompt to enter the salary must include the employee name. The employee ID MUST be…C++ Programming: Write a program using inputs age (years), weight (pounds), heart rate (beats per minute), and time (minutes), respectively. Output the average calories burned for a person. Output each floating-point value with two digits after the decimal point, which can be achieved by executingcout << fixed << setprecision(2); once before all other cout statements.Write a code snippet in C that can arrange the alphabets of a name entered by user in alternate cases.Note: Ignore white spaces. Input String:Timothy Olyphant Output String :TiMoThY OLyPhAnT Input String: Olga Kurylenko Output string: OlGa KuRyLeNkO
- in c++ void check_palindrome() - to check whether the given number by user is palindrome or not. write a program using above function to check whether the number is palindrome or not. please add comments also.In C++, Write a program that asks the user to enter two numbers, obtains the two numbers from the user and prints the sum, product, difference, and quotient of the two numbers.In C Declare a variable of type double.Ask the user for a value and place it in the declared variable.Write code to check for and output statement stating whether the variable is zero, positive, ornegative.
- 5. Write a C program that keeps a number from the user and generates an integer between 1 and 7 and displays the name of the weekday. Test DataInput number: 3 Expected Output :WednesdayQuestion 2: Write a C Program A bank wants a program that determines the yearly interest earned on a guaranteed investment certificate (GIC), given a number of years. If the investment is for five years, the interest is 8.2% per year; if it is for one year, the interest is 5%. Print on the screen "Invalid data. Please try again later.", if the user enters any value other than 1 or 5 for the number of years of investment. Write a complete C program to determine the amount of interest earned per year Hint: Interest - amount * percentageQ13/ Write a program in c++ that asks the user to input two numbers. If the first number entered is greater than the second number, the program should print the message: "The first number is greater." Otherwise, it should print the message: "The first number is smaller." .By using functions
- *Correct all syntax errors so that the C++ program will compile correctly.* Procided C++ code: #include<iostream>#include<conio.h> Standard namespace declarationusing namespace std; Main Functionint main(){ double myMoney = 1000.50; //this should be printed out Standard Ouput Statement cout"Please be sure to correct all syntax errors in this program"<<endl; cout<<"I have corrected all errors for this program. <<endl; cout<<" The total amount of money available is = "<< <<endl; // Wait For Output Screen Main Function return Statement return 0;} Thank you for your helpWrite a program in C++ that should calculate the insurnace for a house. use questions below to write your programm. what is your first? what last name? how many people are living in the houes? how much did you bought the house for? how many bedrom does it have? what is the lenght in squre feet? - use Loop so everyone can repeat the programm. use function like "viod" and any other function. and finally use this formula: X/150*y/*50 x is the total price of the house y is the number of bedrooms s is the lenght in square feet.Q.1. Write a program in C++ which inputs a number from the user, and based on the numberentered display the week of the day as per the following table; [Use Switch Statement]1 - Sunday2 - Monday3 - Tuesday4 - Wednesday5 - Thursday6 - Friday7 – SaturdayDisplay appropriate error message if the number is not valid.

