Write a code to the following image using Console.Write
Q: What is the output equation (Y=_ Data select input S1 0 0 1 1 ) if both select inputs are 1? Data…
A: Given table is:S1S24 MUX00D001D110D211D3
Q: How does one acquire software applications? In a well-written response, you will provide examples to…
A: GivenHow does one acquire software applications? In a well-written response, you will provide…
Q: Can you explain how the structure of the software will be evaluated?
A: Software structure evaluation involves assessing a software system's organization, design, and…
Q: List the six most significant reasons why you began learning about compilers.
A: To begin with, a compelling reason for education about compilers is to know how high-level languages…
Q: In the following section, we will examine how cloud environments host network services and…
A: Cloud environment, or cloud computing platform, are a radical technology trend in central processing…
Q: How applicable are design patterns to software engineering, if at all? Choose one of the following…
A: Design patterns play a significant role in software engineering by providing reusable solutions to…
Q: What are the conditions for testing whether a linked list T is empty, if T is a (i) simple singly…
A: The requirements for determining if a linked list T is empty depend on the type of linked list. Here…
Q: What is the difference between a feeble entity set and a robust entity set?
A: In the field of entity relationship modeling, entity sets play a crucial role in representing…
Q: What exactly do you mean when you refer to "declaration statements"?
A: An declaration statement proclaims another neighborhood variable, nearby steady, or ref nearby…
Q: Design a sequence detector circuit using the mealy model to detect when a value is not BCD, for…
A: A sequence detector circuit is a digital circuit that detects the occurrence of a specific sequence…
Q: Consider the historical evolution of the internet and its present-day technological foundations.
A: The internet has undergone a remarkable historical evolution, transforming the way we communicate,…
Q: Explain in detail why my computer boots so slowly. We greatly value your assistance.
A: Computers can boot slowly for a variety of reasons. The most common among these include:Many startup…
Q: "Wifi access point" means what? What's the mechanism's purpose?
A: A Wi-Fi access point (AP) is a device that enables wireless communication between Wi-Fi-enabled…
Q: How and why did the term "spool" come to be used to designate printer output?
A: In this question we need to explain why and how spool come to be utilized in designate printer…
Q: In Java 8, I want the program to capture the current year and compare it to an input value.…
A: Step-1: StartStep-2: Declare variable currentYear and get current year with the help of Year…
Q: What else does the central processing unit do, exactly? I'm curious as to your thoughts on this. So,…
A: what else does the central processing unit do exactly this will answered in below step.
Q: Cost and performance discrepancies between main and secondary storage?
A: What is main and secondary storage: Main storage, often referred to as RAM (Random Access Memory),…
Q: I hardly know multi-factor authentication. How does it protect passwords?
A: In order to safeguard accounts and systems, multi-factor authentication (MFA) goes beyond the usual…
Q: Data mining's influence on privacy and safety?
A: Introduction:- Data mining refers to the process of extracting and analyzing large sets of data to…
Q: 2) Minimize the following DFAS: a 2 a b b b a 2 3 (3 a 3 a b a a a,b b a 5 5 a 6
A: DFA stands for Deterministic Finite Automaton, which is a type of automaton, or a mathematical model…
Q: This benefit makes pre-made software more convenient to use.
A: What is pre-made software:In the context of pre-made software, convenience refers to the ease of use…
Q: Create a programme REMOVE_DUPLICATES that removes sequentially occurring duplicate entries in a list…
A: Start with an input list L.Create an empty list called result to store the non-duplicate…
Q: What characteristics must a compiler possess to generate reliable and efficient code? Explain?
A: A compiler is a very important tool inside development, translating high-level programming languages…
Q: Conclusion: End your research with a conclusion that summarizes the importance of being computer…
A: Computer literacy has become an essential skill in today's digital age, and it holds immense…
Q: The hard drive, processor, memory, and graphics card on your computer have probably reached the end…
A: To verify the function of the diagnostic program, you would need to assess its accuracy,…
Q: Differentiate software engineering from other engineering disciplines.
A: Software engineering and additional engineering disciplines like civil, automatic, or Electrical…
Q: 3) Write a program to add your age and your father's age in the listbox. In addition to that check…
A: 1. Import the necessary modules: tkinter for GUI components.2. Define a function `add_ages()` that…
Q: n Java The last one I took it as a circulation queue or a queue with a limit. All depends on how…
A: A circular queue is a type of data structure that represents a queue in a circular manner. In a…
Q: What specific purpose does authentication serve? The advantages and disadvantages of various…
A: Authentication is the process of verifying the identity of a user or device. It is used to ensure…
Q: Which way of making a fence has become the usual way for businesses to do things in the present?…
A: In the rapidly evolving landscape of business practices, it is essential for companies to adapt and…
Q: Explain the importance of testability and provide an overview of the compiler; is this feasible?
A: Testability refers to the degree to which a system or component can be effectively tested to ensure…
Q: Design a Mealy machine to detect when a value is not BCD, for example when 1111 is generated it…
A: To design a Mealy machine that detects when a value is not in BCD (Binary Coded Decimal) format, we…
Q: Which symbol or key on the keyboard corresponds to the virtual Left Menu key?
A: What is virtual Left Menu key: The virtual Left Menu key is represented by the symbol of the Windows…
Q: A flowchart's selection structure icon is what?
A: Flowcharts are illustrative representations of algorithms or processes, illustrate the process as a…
Q: Is there a particular objective that authentication is intended to achieve? Compare and contrast the…
A: Authentication is a fundamental concept in information security and plays a crucial role in…
Q: hat advantages and disadvantages does manually walking through code have over print statements?…
A: Manually walking through code and using print statements are two different approaches to…
Q: Good afternoon, Assistance with this Discrete Math question would be greatly appriciated. Thank…
A: The problem of finding the maximum value in a list of numbers is directly related to discrete…
Q: Observe the stack's reaction when given some space.
A: When considering the behavior of a stack, it is interesting to observe its reaction when provided…
Q: Which architectures of back-end compilers require testing?
A: Testing is a fundamental activity in software development that involves evaluating the behavior,…
Q: What are some of the numerous characteristics of a compiler that rapidly generates high-quality…
A: A compiler is a software tool that translates source code written in a high-level programming…
Q: Again using the software.subscriptions table, pull all columns for premium_year subscriptions,…
A: If you have a table called software and want to pull all columns for premium_year subscriptions…
Q: Is there a particular architecture for a network that you think would perform best in this case?
A: What is neural network: A neural network is a computational model inspired by the structure and…
Q: Can the advantages and disadvantages of various
A: What is AUTHENTICATION: Authentication is the process of verifying the identity of a user or entity…
Q: Is a well-managed data protection system essential?
A: In today's data-driven world, a well-managed data protection system is essential for organizations…
Q: For instance, wireless networks are crucial in today's developing countries. Wireless networking has…
A: In today's rapidly evolving technological landscape, wireless networks have become indispensable,…
Q: If feasible, could you provide a more in-depth explanation of how metrics are utilised throughout…
A: Metrics play a crucial role in the software development process as they provide objective…
Q: Got stuck on this for my daily coding practice. I would like to understand it in Java. Given…
A: To complete the FoodItem class in Java, you need to implement the default constructor and the second…
Q: Given two int8 vectors called vec1 and vec2, select the line of code that sets the 3rd and 5th…
A: Option a). vec1.s24 = vec2.s03 is incorrect because it assigns the 0th element of vec2 to the 4th…
Q: e importance of testability and provide an overview of the compiler; is this feasible?
A: Testability refers to the ease with which software can be tested to ensure its correctness,…
Q: Determine the nature of an API and its relationship to system calls.
A: An Application Programming Interface (API) plays a crucial role in facilitating communication and…
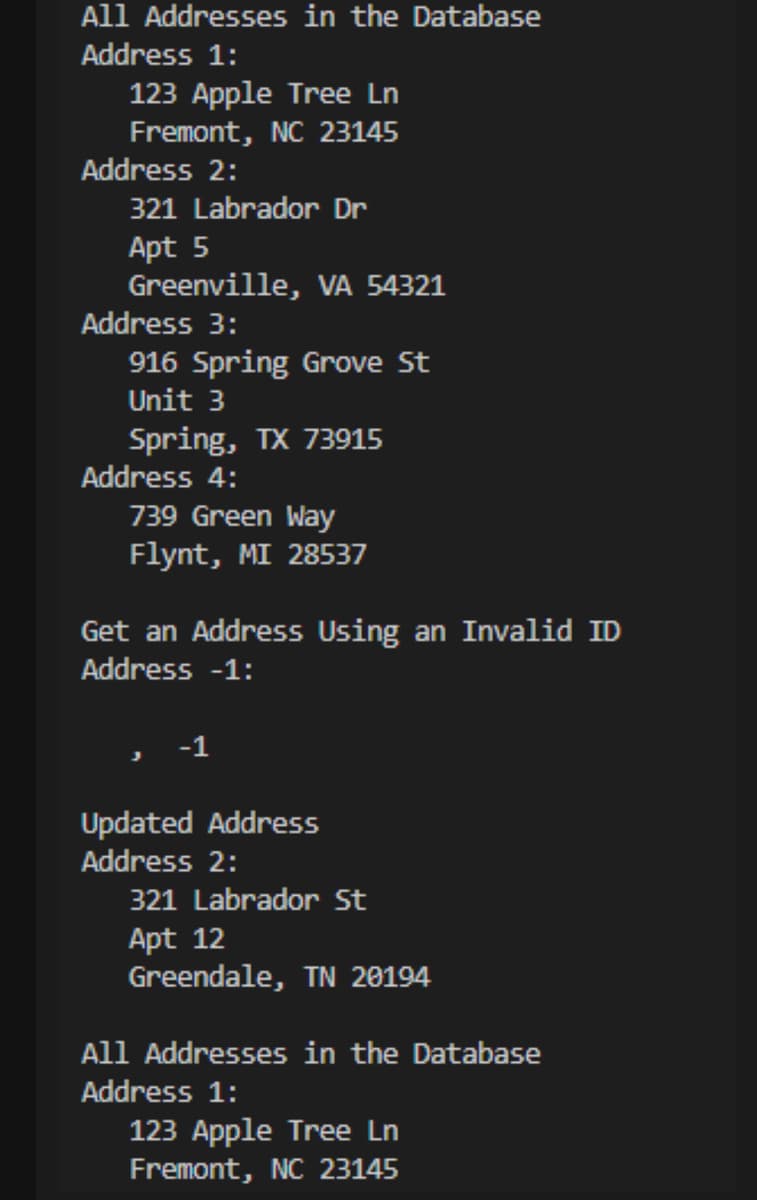
Step by step
Solved in 4 steps with 1 images

- main.java file import java.sql.*;public class Main { public static void main(String[] args) { try { // Connect to the library_db database, via the jdbc:mysql: channel on localhost (this PC) // Use username "otheruser", password "swordfish". Connection connection = DriverManager.getConnection( "jdbc:mysql://localhost:3306/library_db?useSSL=false", "otheruser", "swordfish" ); // Create a direct line to the database for running our queries Statement statement = connection.createStatement(); ResultSet results; int rowsAffected; // Set up finished, do some stuff: // executeQuery: runs a SELECT statement and returns the results. results = statement.executeQuery("SELECT title, qty FROM books"); // Loop over the results, printing them all. while (results.next()) {…Chapter 17 How to manage database security Exercises using the My Guitar Shop Database Use Microsoft SQL Server Write a script that creates a user-defined database role named OrderEntry in the MyGuitarShop database. Give INSERT and UPDATE permission to the new role for the Orders and OrderItems table. Give SELECT permission for all user tables. 2.Write a script that (1) creates a login ID named “RobertHalliday” with the password “HelloBob”; (2) sets the default database for the login to the MyGuitarShop database; (3) creates a user named “RobertHalliday” for the login; and (4) assigns the user to the OrderEntry role you created in exercise 1.A database has 4 transactions, shown below.TID Date items_boughtT100 10/15/04 {K, A, D, B}T200 10/15/04 {D, A, C, E, B}T300 10/19/04 {C, A, B, E}T400 10/22/04 {B, A, D}Assuming a minimum level of support min_sup = 60% and a minimum level ofconfidencemin_conf = 80%:(a) Find all frequent itemsets (not just the ones with the maximum width/length) using the Apriori algorithm. Show your work—just showing the final answer is not acceptable. For each iteration show the candidate and acceptable frequent itemsets. You should show your work similar to the way the example was done in thePowerPoint slides.(b)List all of the strong association rules, along with their support and confidence values, whichmatch the following metarule, where X is a variable representing customers and itemi denotes variables representing items (e.g., “A”, “B”, etc.).x transaction, buys(X, item1) buys(X, item2) buys(X, item3)Hint: don’t worry about the fact that the statement above uses relations. The point of the…
- blockchain is a collection ofrecords (called blocks), where each block links to the previous block using cryptography. Eachblock contains cryptographic hash, timestamp and data relevant to its application. Think ofit as a distributed ledger where instead of information being stored in a database it is storedon the blockchain. Some examples of solutions that use a blockchain at its core are:1. Cryptocurrencies (however, for this project you may NOT do a cryptocurrency)2. Smart contracts3. Trading4. Supply chain management5. Anti-counterfeiting6. Healthcare7. Domain names8. Proof of existence9. Voting10. and many others! Programming Language: Java The use of third-party libraries for primary functionally is strictly prohibited, however, third party libraries can be used for other functionality such as communications and visualisation (such as normal JavaFX, JFreeChart, GraphStream, JGraphT, Yworks, JUNG or JMonkey). The use of other data structures for auxiliary operations is…An objective of this task is to implement your own simple method of auditing the database activities.It is strongly recommended to connect to MySQL either through command line interface mysql or graphical user interface MySQL Workbench and process a script file dbdrop.sql and immediately after that the scripts dbcreate.sql and dbload.sql to refresh a sample database csit115.Download a file solution3.sql and insert into the file the implementations of the following actions.You must connect as a user root with a password csit115.Your implementation must directly follow a comment with a specification of a subtask.(1) First, the script makes a relational table that contains a general log empty.(2) Next, the script sets the appropriate values of the variables to save a general log in a relational table and to start recording a general log from now.(3) Next, the script makes a database csit115 a default database, it stops recording a report, it executes a script file updates.sql, and it…Assuming you have created already created a MySQL database named "database_name" with a table named "users" that has columns for "username", "password", and "email". And that you have also created a login system that sets the "username" session variable when a user logs in.Write a simple PHP code that makes use of sessions, mysql insert, update, and delete. The code should first start with a session using session_start(). It should then connect to a MySQL database using mysqli_connect(). It inserts a new record into the users table using mysqli_query() and an SQL INSERT statement. It updates an existing record in the users table using mysqli_query() and an SQL UPDATE statement. It deletes a record from the users table using mysqli_query() and an SQL DELETE statement. It sets a session variable using $_SESSION["username"] and displays it using echo. Finally, it closes the MySQL connection using mysqli_close()
- discuss the security vulnerability in this pseudocode. show one input that allows an attacker to delete table users. $user_id= $_GET["user"]; //Read username$pwd = $_GET["password"]; //Read password$query = "SELECT home_dir FROM users WHERE uid='".$user_id."' AND Password ='".$pwd."';$result= run_query($query) //If this query returns one row, the login is successfulCreate a MySQL Database called “CSC306Class”. Create three (3) tables in the database called “studentInf”, “IntructorInf”, and “LikedAndDisliked”. Each table should consist of five columns that are relatable to the table name. Insert at least five row of data in each table. The data can be any information as long as it is related to the table name.The system consists of a database and a servlet to access the database. The database is running on a server and can be accessed via a TCP/IP link. The main program is running on a different server as a Java Servlet. The database has a component to retrieve the query string and return the data and another component to insert data. The database is an “.exe” file. The server has a component to query the user for a search command and another component to submit the query. 1. How do I draw a deployment diagram for the system. 2. How do I draw a use case diagram for the system.
- This is why database-like access mechanisms are often used in corporate blockchains.Performing an Nmap scan from within Metasploit:We need something exciting to display when running the hosts command so run a quick nmap scan to collect some data. With msfconsole open and the databaseconnected.create Database CTU_YOURICASNOGOUSE CTU_YOURICASNO;GOCREATE TABLE Course( CourseID int PRIMARY KEY, CourseName varchar(255), CourseDesc varchar(255),);CREATE TABLE Students( ICASNo int Primary Key, StudentName varchar (255)NOT NULL, StudentSurname varchar (255)NOT NULL, StudentContact varchar (255)NOT NULL, StudentEmail varchar(255)NOT NULL, HighSchoolAttended varchar(255)NOT NULL, courseID int,);CREATE TABLE Semester( SemesterID int Primary Key, SemesterStartDate varchar(255)NOT NULL, SemesterEndDate varchar(255)NOT NULL, ICASNo varchar(255),);CREATE TABLE Facilitator( FacilitatorID int Primary Key, FacilitatorName varchar(255) Not Null, FacilitatorContact varchar(255)Not Null, FacilitatorEmail varchar(255)Not Null, ICASNo varchar(255)Not Null, ); CREATE TABLE Module( ModuleID int Primary Key, ModuelName varchar(255)Not Null, ModuleDuration varchar(255)Not Null, FacilitatorID varchar(255)Not Null,); Using the…











