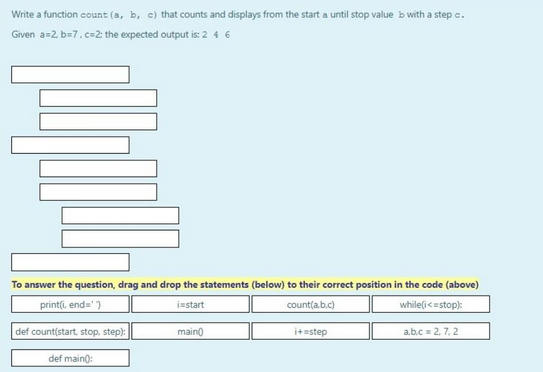
Write a function count (a, b, c) that counts and displays from the start a until stop value b with a step c. Given a=2 b=7, c=2: the expected output is: 2 4 6 To answer the question, drag and drop the statements (below) to their correct position in the code (above) print(i, end=') instart count(a.b.c) while(i <=stop):
Q: An organization has a class C network 196.10.10 and wants to for departments, which host as follows:
A: The answer is
Q: What risk management strategies work the best for moving to the cloud?
A: Introduction: Cloud computing is becoming more popular among businesses, but security precautions…
Q: What purpose does systems analysis serve? Is it really necessary? Why?
A: System analysis is the most common way of evaluating needs when deciding on a plan for new systems,…
Q: How are two separate connections between a field label and a control element possible? Please also…
A: There are actually two ways to link a field label to a control element: There are two ways to link a…
Q: Differentiate between control risk and inherent risk.
A: The answer of the question is given below
Q: Describe the main difference between the ways that symmetric encryption and asymmetric encryption…
A: The solution to the given question is: Symmetric encryption requires a single key known only to…
Q: How does quantum computing operate and what is it?
A: THE QUANTUM COMPUTER: Quantum computing is the practise of doing computations using an object's…
Q: What trade-offs do buffer trees have in comparison to LSM trees?
A: The buffer tree has the following trade-offs: The use of buffer trees is advised to lower the costs…
Q: What fundamental differences exist between cloud security solutions and on-premises data center…
A: Introduction: On-premises data is stored locally, eliminating the need for an internet connection…
Q: Can I apply data structure like Queue in creating a Java GUI like queue system?
A: The question has been answered in step2
Q: An example of an asymmetric encryption method is the usage of public key cryptography. Asymmetric…
A: Introduction: Asymmetric cryptography, sometimes called public key cryptography, encrypts and…
Q: One of the most popular methods of encrypting passwords has a security issue. The impact of each of…
A: Given: One of the most used methods of encrypting passwords is vulnerable. Common mitigation may be…
Q: Differentiate between control risk and inherent risk
A: The inherent risk arises from the nature of the business transaction or activity if internal…
Q: Explain why the concept of mutual exclusion (ME) is seen as a crucial mechanism for an operating…
A: Answer: Concept of mutual exclusion is seen as a crucial mechanism for an operating system's…
Q: The following code computes the sum of the first 10 numbers in revert order (10+9+...+1): 1-10…
A: Here is the explanation of the above output of the program. See below steps.
Q: How are two separate connections between a field label and a control element possible? Please also…
A: label Field: A string may be stored as the value of a label field, while another string can be…
Q: There are several ways that malicious traffic might be diverted into a network, including from one…
A: Advantages of the Symmetric encryption algorithm: Simple: The encryption is relatively…
Q: What TextAlign values are available?
A: TextAlign property values that may be used: If the text in the label is positioned at the top and…
Q: Write a function that recieves three integer values; option, dimension and dimension2. This function…
A: Note : As there is no programming language is mentioned in the question so I will solve this problem…
Q: What tools are available in Visual Studio to assist you rapidly correct syntax errors?
A: Visual Studio: It is a full-featured Integrated Development Environment that allows you to code,…
Q: There are several ways that malicious traffic might be diverted into a network, including from one…
A: Attacking the network resources of a virtual local area network (VLAN) by sending packets to a port…
Q: How does IP spoofing operate? What is it? Does IP spoofing pose a security threat?
A: IP spoofing is also known as: Spoofing an Internet Protocol address, often known as IP spoofing, is…
Q: For a small business with three full-time workers and two or three part-time employees, what core…
A: The organization's systems: Services, and data are protected against being used immorally or…
Q: Variable declaration is implicit in python true or false.
A: When reserving memory for variables, Python does not need explicit declaration. Anytime you give a…
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a…
A: N-tier architecture : An application is divided into logical layers and physical tiers using an…
Q: Write a program called p4.py that asks the user for two integers representing the month [1,..., 12]…
A: solution:- it is provide code:- python code:- print("Enter a month [1:12]")month =…
Q: Describe what the terms CRUD and RESTful imply.
A: CRUD and REST are two words. CRUD The phrase "CRUD" mainly refers to all set of activities that are…
Q: Give me an explanation of how a database works. 7. What kind of software are used during the data…
A: A database is data that is set up for simple access, the board and refreshing. PC data sets commonly…
Q: 3. Determine the running time of the following algorithm by analyzing each statement. Show work!…
A: In this question we need to find the running time of the given algorithm by analyzing the cost of…
Q: Why is studying information systems important to you? What do you want to get out of taking this…
A: Introduction: The IS programme is multidisciplinary in nature.
Q: The two-tier and three-tier application architectures should be defined. Which is more advantageous…
A: Applications: Application architectures include monoliths and N-tier design (tightly integrated),…
Q: Why is the stack of the x86 processor designated as a descending stack? List the steps involved in…
A: When a register is placed into the stack, it may be stored at either the highest or lowest address.…
Q: What are the advantages of deploying thin clients in a university computer lab rather than standard…
A: Advantages: For instance, a university computer lab needs several computers to do the same task.…
Q: Write List-scheduling algorithm for reconfigurable devices.
A: Here we have given list-scheduling algorithm for reconfigurable devices. You can find the solution…
Q: What trade-offs do buffer trees have in comparison to LSM trees?
A: A buffer tree's trade-offs: Buffer trees can be used in conjunction with any tree-structured index…
Q: Describe what integrity and authorization restrictions mean.
A: Integrity Restrictions: Primarily, it is used to preserve data consistency following the…
Q: An essential component of modern computers is cache memory. Describe the purpose of cache memory and…
A: Introduction In this question we have asked about the cache memory and Describe the purpose of cache…
Q: Why does hashing a password make more sense than encrypting one that has been saved in a file or on…
A: Introduction: Data may be decrypted so that it can once again be read since encryption is two-way.…
Q: Some magnetic disk-based databases only utilize the outside tracks of the disks, leaving the inside…
A: The information stored on a magnetic disc, a sort of secondary memory, is contained on a flat disc…
Q: What fundamental differences exist between the information technology security solutions used in a…
A: For almost every aspect of their IT services today, including software, servers, storage, backups,…
Q: What are the names of the three procedures in the subject of cryptography that are regarded as being…
A: Cryptography-: Cryptography studies secure exchanges that allow only the sender and intended…
Q: he two-tier and three-tier application architectures should be defined. Which is more advantageous…
A: Answer is in next step.
Q: How does IP spoofing operate? What is it? Does IP spoofing pose a security threat?
A: IP forgery: IP spoofing, also known as IP a address spoofing, is the act of sending Internet…
Q: Write The greatest common divisor sequential algorithm
A: The algorithm that is used to find the GCD of two numbers. The algorithm show below is one of the…
Q: 1. Consider the algorithm for the sorting problem that sorts an array by counting, for each of its…
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: If there are puzzle pieces on a table and you put them together so that you have a complete picture…
A: Hello student
Q: What three fundamental operations are there in cryptography?
A: Introduction: Cryptography is a data security method that protects personal data from attackers (or…
Q: How does IP spoofing operate? What is it? Does IP spoofing pose a security threat?
A: DNS spoofing: An Internet Protocol (IP) spoofing technique involves gaining unauthorised access to a…
Q: What businesses are developing their systems using splay tree?
A: Definition: The Splay tree is a binary searched tree that embodies self-adjustment. For the needed…
Q: Describe the distinctions between a decision support system's capabilities and a manager's ability…
A: Introduction: A management information system or MIS is a kind of information system that is by and…
Step by step
Solved in 2 steps with 1 images

- Write a function print_shampoo_instructions() with parameter num_cycles. If num_cycles is less than 1, print "Too few.". If more than 4, print "Too many.". Else, print "N : Lather and rinse." num_cycles times, where N is the cycle number, followed by "Done.".Sample output with input: 1: Lather and rinse. 2: Lather and rinse. Done. So far, this is what I have and it works except that it doesnt do 2 lather and rinse outputs: def print_shampoo_instructions(num_cycles): if num_cycles < 1: print('Too few') elif num_cycles > 4: print('Too many') else: print(str(num_cycles - 1) + ': Lather and rinse.') num_cycles += 1 user_cycles = int(input())print_shampoo_instructions(user_cycles) user_cycles = int(input())print_shampoo_instructions(user_cycles)Write a Paython program ,Please . Let f be the function from A to B where A={1, 2, 3, 4} and B = {a, b, c, d} with f(1)=d, f(2)=b, f(3)=c, and f(4)=a, then check all the condition for f whether f is:(i) One to one function(ii) Onto function(iii) One to one correspondence function Advance Many Many Thanks dear tutor .Write a function print_shampoo_instructions() with parameter num_cycles. If num_cycles is less than 1, print "Too few.". If more than 4, print "Too many.". Else, print "N : Lather and rinse." num_cycles times, where N is the cycle number, followed by "Done.".Sample output with input: 2 1: Lather and rinse. 2: Lather and rinse. Done. Hint: Define and use a loop variable. I am getting the correct output,but i can't get rid of the white space between the number and the ':' 1 : Lather and rinse. 2 : Lather and rinse. Done.
- Write a function that makes the base conversion. It takes two integers n and b as input (n >= 0 andb > 1, both in base 10) and expresses n in base b. For example, the decimal expansion of 345 inbase 10 is 345 = 3 × 102 + 4 × 101 + 5 × 100.Sample input: n = 12, b =2. Sample output: 1100Explanation: (12)10 = (1100)2Write a Paython program , without using def function Please . Let f be the function from A to B where A={1, 2, 3, 4} and B = {a, b, c, d} with f(1)=d, f(2)=b, f(3)=c, and f(4)=a, then check all the condition for f whether f is:(i) One to one function(ii) Onto function(iii) One to one correspondence function Advance Many Many Thanks dear tutor .Write a program which will take marks of three quizzes as input, then call a function void ScaleUp(float q1, float q2, float q3) to check if the marks of any of the quiz ‘q’ is less than the average of rest of two quizzes ‘a’. If marks of any quiz is less than the average of the rest of two marks then add the difference between the average of the two quizzes and the quiz itself to q i.e., q = a - q, to scale up the quiz marks.For example, if q1 = 5, q2 = 8 and q3 = 9 then your function will change the marks of quiz 1 using the steps below:A = (q3 + q2 )/2 => (8+9)/2=> 8.5 Diff = A - q1 => 8.5 - 5 => 3.5 Q1 = Q1 + Diff => 5 + 3.5 => 8.5Note that the marks are input from the user, so there might be three cases I. if q1 < q2 + q3 orIi. if q2 < q1 + q3 orIii. if q3 < q1 + q2
- Write a function shampoo_instructions() with parameter num_cycles. If num_cycles is less than 1, print "Too few.". If more than 4, print "Too many.". Else, print "N : Lather and rinse." num_cycles times, where N is the cycle number, followed by "Done.". Sample output with input: 2 1 : Lather and rinse. 2 : Lather and rinse. Done. Hint: Define and use a loop variable.Given a boolean expression consisting of the symbols 0 (false), 1 (true), & (AND), I (OR), and /\ (XOR), and a desired boolean result value result, implement a function to count the number of ways of parenthesizing the expression such that it evaluates to result. The expression should be fully parenthesized (e.g., ( 0) A( 1)) but not extraneously (e.g., ( ( ( 0)) /\ ( 1)) ). EXAMPLE countEval("l/\01011", false) -> 2 countEval("0&0&0&1All0", true)-> 10Write a program such that the sequential input entered by the user is summed or counted, up until the end criteria is seen in the sequence. The end criteria is also defined by the user. No previous information about where the entered sequence is reached to the stop criteria. Both stop criteria and function type is defined by the user inputs in the main function and necessary information is passed to the proper function. As an example, if sum function is chosen with stop criteria 0, and user starts to enter one by one the values 1,2,3,0 in order, the program should stop receiving input immediately whenever the 0 (defined stop criteria) is entered and print out 6 as sum of inputs up to stop criteria. In another case, if -1 is chosen as stop criteria and the count function is chosen by the user, as an example, and the sequence one by one entered is the 3,2,5,1,-1, the program should print 4 to the screen as a number of inputs up to -1 entered. Don’t forget the sequence is entered one by…
- Define a function calc_total_inches, with parameters num_feet and num_inches, that returns the total number of inches. Note: There are 12 inches in a foot.Sample output with inputs: 5 8 Total inches: 68Write a function using C that has two integers and uses a loop to count from a lower value to a higher value and vice versa. Use each value of the loop counter as a length in miles and printing it with the corresponding length in KM, with three digits after the decimal point.Write a C program to determine whether a number is a prime number or not using a function.*The function prototype should look like int isPrime(int n) that prints 1 if n is prime and prints 0 if otherwise.*The use of Flag or bool is not allowed.

