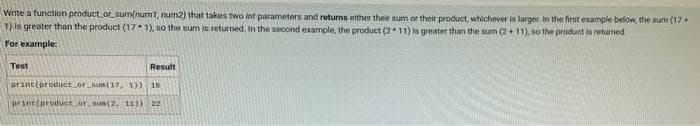
Write a function product or sum(num1, num2) that takes two int parameters and returns either their sum or their product, whichever is larger. In the first example below, the sum (17+ 1) is greater than the product (171), so the sum is returned. In the second example, the product (211) is greater than the sum (2+11), so the product is returned For example: Test Result print (product or sum(17, 1)) 18 print(product or sum(2, 11)) 22
Q: Provide some instances for each of the three primary categories of file management.
A: The process and demonstration of making a coordinated construction wherein you store data for…
Q: Make sure you know the difference between a PAN, LAN, MAN, and WAN
A: LAN represents neighborhood. A gathering of organization gadgets permit correspondence between…
Q: What do we use the second parameter of the open() call to indicate? a. How large we expect the file…
A: The above question is solved in step 2 :-
Q: What does it mean when we say that the data is fragmented?
A: When data becomes fragmented, it means it is stored in separate locations. Processes like data…
Q: Computer science a performance assessment utilising a performance optimization tool as an example.
A: Introduction: Computer science a performance assessment utilizing a performance optimization tool as…
Q: What are some of the reasons why people consider the internet to be the pinnacle of information and…
A: A quick overview: The internet is the most powerful tool accessible in the twenty-first century,…
Q: Let's assume, for the sake of simplicity, that the address 581132 on the disc is the location of a…
A: Start: In order to answer this issue, we must first comprehend how file blocks are identified and…
Q: Identify five (5) risks to present security architecture and design, as well as possible asset…
A: Introduction: The following are examples of dangers to the existing security architecture and…
Q: How is cooperation synchronisation given for Ada tasks?
A: Introduction: The cooperation synchronisation given for Ada tasks are :
Q: The end result that you have in mind when talking about the authentication process's objectives is…
A: The process of ascertaining whether someone or something is who or what they claim to be is known as…
Q: (d) Draw the final B+ tree when the key 34 is deleted from the following B+ tree of order M = 5 and…
A:
Q: number of flip a binary modul-
A:
Q: Disk requests are received by a disk drive for cylinder 20, 25, 45, 5, 10, 17, 60, 70, 35, 90.…
A: The Answer is
Q: Q. Can you tell me about the history of Windows operating systems?
A: Introduction: Microsoft Windows is a personal computer operating system (OS) developed by Microsoft…
Q: Do some research on authenticating users as a means of access control and write a report on it.
A: Definition: Security techniques impose system assurance levels. Operating systems use trust levels…
Q: In this section, you should provide a succinct summary of the two functions that are regarded the…
A: Introduction: The term "operating system" refers to the software that enables a computer to…
Q: Perhaps a concise explanation of the operating system's two most significant tasks should appear…
A: Input/output, memory management, and processing are just a few of the operations that an operating…
Q: Question 2 of 10 Which two features could be added to a game using an "if () then' block? A. A…
A: if() blockk can be adden when there is yes or no condition.
Q: tradeoff
A: A space-time off or time-space off in software engineering is a situation where a calculation or…
Q: Please explain to us the fundamentals of successful data entry fields. There may be occasions…
A: Intro while this may seem obvious, it is necessary to say. Many illustrations deceive the viewer by…
Q: Which idea of access control limits a user's access to the specific information that is required for…
A: Given: What are some of the objectives of the authentication process? Investigate both the positives…
Q: What precautions may be done to lessen the chance of a network failure?
A: Introduction: One of the most serious threats is network failure, which has a direct impact on…
Q: What is called data base
A: Database: A database is an organised collection of structured information or data typically stored…
Q: In a network, what functions are performed by the bridge, the router, the gateway, and the switch?
A: Gateway switch: A gateway is exactly what it sounds like: a device that operates as a crossing point…
Q: Walk me through the three most common approaches to managing my files, and show me how they work
A: File system in a the computer system, is the way or the method of naming the files and then to know…
Q: Q1: Use Input to print "==>" and stop the program until the user enters a value and Pressing the…
A: - We have to code for the vector input. - We are using python here.
Q: escribe the multifactor authentication technique and the phrase's meaning. What level of security…
A: Intro Describe the multifactor authentication procedure and the meaning of the phrase. What level of…
Q: What kind of connection does the field of telecommunications have with the realm of data…
A: Telecommunication: It refers to long-distance communication. Electronic signal transmission between…
Q: An authentication challenge–response system is a notion that you need to explain. Why is this more…
A: Challenge–response system can be explained as one of the Authentication process where in there are…
Q: What words would you use to characterise a challenge and answer authentication system, so that we…
A: Answer: In computer security, challenge-response authentication refers to a set of rules in which…
Q: In order to better understand the concept of a challenge-and-response authentication system, could…
A: Challenge-response authentication is a set of protocols used to secure digital assets and services…
Q: z+wx+wxy
A: --->As we know that we are given with above expression ,which can be expressed using truth…
Q: What's the difference between a controller and an adapter?
A: Introduction: We must distinguish between an adapter and a controller.
Q: The sequential circuit below yields an output sequence of Z=11011111 when you apply the input…
A:
Q: Happy Shop sells different products to the customers. A customer could buy one or more products at a…
A: Ans: The primary key for the given table is customer ID. The 3 different update anomalies are as…
Q: In software development, what is the difference between V&V and V&V?They must be distinguished in…
A: Introduction: V&V stands for Verification and Validation in the context of software project…
Q: What other web-based technologies outside those already mentioned are used to help facilitate…
A: Google Docs (Gudoks): Other web-based tools that are used to facilitate project collaboration…
Q: Operating systems face certain challenges when they have an architecture that allows many threads.
A: Introduction: According to the facts provided, we must explore the key issues involved with the…
Q: Make up a hypothetical scenario to illustrate how the login process works. It's possible that you've…
A: Explanation: Scenario management is an effective way to handle several futures and create…
Q: What are some of the aims of the authentication procedure if any? Comparing and contrasting each of…
A: Authentication: Authentication is the process of determining if someone or something is who or what…
Q: What distinguishes NoSQL from other database systems currently on the market?
A: Intro In spite of other database systems, most NoSQL databases share a few qualities. As far as one…
Q: Design a Pushdown Automata. Please also include if its possible to design a machine within the state…
A: Given: L = {w = 0i1j0k and j=i+k for some i,k >=0} lets understand the language: strings in…
Q: Jobs Arrival Time Burst P1 0.0…
A: Lets understand each of the given algorithms: Shortest remaining time first : it is a pre-emptive…
Q: What exactly is the World Wide Web? Is it an additional network that operates similarly to the…
A: World wide web is one of the way which is used to access the documents which are spread over the…
Q: Is it possible to distinguish between a Trojan Horse, a computer virus, and a worm? Certain viruses…
A: Introduction: Blaster Worm. The worm's purpose is to burrow into your system and gain access to your…
Q: Please provide a description of the method used by the system that enables you to solve all of the…
A: Database : Database technique solves conventional file management system's shortcomings. Eliminating…
Q: Choose three separate smartphone apps that would be incredibly useful in your current or future…
A: Introduction: Three separate smartphone apps that might be highly useful in your current or future…
Q: Of the case that there is a breach in a company's security, what steps should be taken?
A: Encryption: It occurs when an organization's basic security mechanisms are breached, allowing…
Q: Matlab code if you knew to include marks as in the following: Write a program that ask about the…
A: I am writing a matlab script on calculating averages of 5 test scores of unknown number of students…
Q: What do you mean when you say that you comprehend the term "Data Modeling"?
A: Information demonstrating is the method involved with making a visual portrayal of either an entire…
Step by step
Solved in 3 steps with 2 images

- Write a program in Python with a function perfectcube(n), which returns True if n is a perfect cube and returns False otherwise. Notice that this function is not printing anything, but rather returning True or False. The function must use exhaustive enumeration to check if n is a perfect cube. Use the function in a program where you ask the user for n and you print a statement like "Yes, that is a perfect cube" or "No, that number is not a perfect cube".PYTHON!!! Write a function that receives 3 assignment grades, a1, a2, a3, and a final grade, f, for a student and returns the corresponding letter grade of the student. The weights for the assignments and the final are 0.2, 0.2, 0.2, and 0.4, respectively. You can use the following table for matching grades to letters: 95-100 -> A1 90-94 -> A2 85-89 -> A3 80-84 -> B1 75-79 -> B2 70-74 -> B3 65-69 -> C1 60-64 -> C2 55-59 -> C3 40-54 -> D 0-39 -> F For example, compute_letter(80, 60, 40, 70) returns "C2" because 80 * 0.2 + 50 * 0.2 + 40 * 0.2 + 70 * 0.4 = 62 and 62 corresponds to C2. Note that, you are expected to do rounding. For example, 39.4 is F, whereas 39.5 is D. You can use the builtin round() function for this. Please google this function and learn how to use it. """ def compute_letter(a1, a2, a3, f):Please answer it in Python Write a double_consonant function , It takes a word as a parameter and has two return values : A Boolean value equals True If the word contains a double consonant ( The same consonant twice in a row ), under these circumstances , The second value returned is the double consonant ; If there are no double consonants , Function should return False and None. relevant information : To simplify the exercise , We don't use words that contain multiple double consonants ( for example ,“successor”) Test your functionality on . Example : double_consonne('arrivee') vaut True, 'r'.double_consonne('bonbon') vaut False, Nonedouble_consonne('reussite') vaut True, 's'
- Write a function called extractor() that takes a name as a parameter and counts every vowel present in it. The function should also identify and contact the consonants in another string. Finally, RETURN the total number of total vowels present in the name and the consonant string.Note: The name could be a mixture of uppercase & lowercase letters.Sample Input 1:MuhaiminulFunction call 1:extractor("Muhaiminul")Sample Output 1:(5, 'mhmnl')Explanation 1:Here, in the given name, we have 5 vowels (uaiiu). That's why 5 in the output. 'mhmnl' are the consonants present in the name.Sample Input 2:iLiyanaFunction call 2:extractor("iLiyana")Sample Output 2:(4, 'lyn')Explanation 2:Here, in the given name, we have 4 vowels (iiaa). That's why 4 in the output. 'lyn' are the consonants present in the name.Write a function that receives 3 assignment grades, a1, a2, a3, and a final grade, f, for a student and returns the corresponding letter grade of the student. The weights for the assignments and the final are 0.2, 0.2, 0.2, and 0.4, respectively. You can use the following table for matching grades to letters: 95-100 -> A1 90-94 -> A2 85-89 -> A3 80-84 -> B1 75-79 -> B2 70-74 -> B3 65-69 -> C1 60-64 -> C2 55-59 -> C3 40-54 -> D 0-39 -> F For example, compute_letter(80, 60, 40, 70) returns "C2" because 80 * 0.2 + 50 * 0.2 + 40 * 0.2 + 70 * 0.4 = 62 and 62 corresponds to C2. Note that, you are expected to do rounding. For example, 39.4 is F, whereas 39.5 is D. You can use the builtin round() function for this. Please google this function and learn how to use it. """Write a function MaxMagnitude() with two integer input parameters that returns the largest magnitude value. Use the function in a program that takes two integer inputs, and outputs the largest magnitude value. Ex: If the inputs are: 5 7 the function returns: 7 Ex: If the inputs are: -8 -2 the function returns: -8 Note: The function does not just return the largest value, which for -8 -2 would be -2. Though not necessary, you may use the absolute-value built-in math function. #include <iostream>using namespace std; void MaxMagnitude(int userVal1, int userVal2) {if (abs(userVal1) > abs(userVal2)) {return userVal1;}else if (abs(userVal2) > abs(userVal1)) {return userVal2;}}/* Define your function here */ int main() { int userVal1;int userVal2;cin >> userVal1 >> userVal2;/* Type your code here. Your code must call the function. */ cout << MaxMagnitude(userVal1, userVal2) << endl;/* Type your code here */ return 0;} Please help me with this problem using…
- ***python only*** Write a function votes_by_race() which takes a list of dicts as a parameter and returns a dict. For example, given the following list: votes = [{'for': 'A, 'age': 35, 'race': 'w'}, {'for': 'B', 'age': 40, 'race': 'b'}, {'for': 'B', 'age': 20, 'race': 'b'}, {'for': 'A', 'age': 30, 'race': 'a'}, {'for': 'A', 'age': 41, 'race': 'w'}, ] The call votes_by_race(votes) should return the following dict:{"White": 2, 'Black': 2, 'Asian': 1, "Hispanic': 0}Write a function convertQuartersToDollars that has the noOfQuarters, noOfDollars, and remainingCents as formal parameters of data type int. The noOfQuarters is the number of quarters to be used to calculate noOfDollars, the number of dollars that the total number of quarters can be converted to, and remainingCents , the remaining cents. The noOfDollars and remainingCents are returned from the function,Write a program in python with a function perfectcube(n), which returns True if n is a perfect cube and returns False otherwise. The function must use exhaustive enumeration to check if n is a perfect cube. Use the function in a program where you ask the user for n and you print a statement like "Yes, that is a perfect cube" or "No, that number is not a perfect cube", as appropriate.
- ‘Write a function has_unique_values() that takes a dict as a parameter and returns True if the keys have unique values (that is not two keys have the samevalues) Write several assertion to test this function.Write a function named sumDigits which takes three parameters: f, t and x. sumDigits, then, finds the smallest integer between f and t (both inclusive) whose sum of digits is x, and returns that integer.Write a program in c++ that calculates the area and perimeter of an upright rectangle.Create a struct Point that has two double values, x and y. Write a function that asks the user for a Point. Call that function twice, once to get the bottom left corner of a rectangle, and once to get the top right corner. Write another function that takes two Points and returns area and perimeter. Print out the area and perimeter. Given two points (x1,y1) and (x2,y2), the formulas to compute perimeter and area are as follows P erimeter = 2 ∗ (abs(x1 − x2) + abs(y1 − y2))Area = abs(x1 − x2) ∗ abs(y1 − y2)

