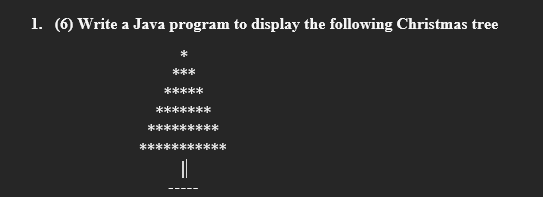
Write a Java program to display the following Christmas tree * *** ***** ******* ********* ***********
Q: 3. In the below PowerShell AD script why is ">>" used instead of "“>"? Get-ADForest >> ||dc1\shared\...
A: The answer as given below:
Q: What is the central processing unit in the power circuit in the mobile?
A: Below the central processing unit in the power circuit in the mobile
Q: Write a C program which creates a child processes using fork() system call. The parent process sh...
A: Write a C program which creates a child processes using fork() system call. The parent process s...
Q: Apply Horspool's algorithm to search for the pattern SORTING in the text SORTING ALGORITHM CAN _USE ...
A: The Answer is given below.
Q: Write a Python program to show the use of the isinstance() function to check whether the value 0.5 i...
A: Required:- Write a python program to show the use of the isinstance() function to check whether the ...
Q: Assume that Host C hosts a Web server that is accessible via port 80. Assume that A and B are the we...
A: Introduction: The source and destination IP addresses, as well as the source and destination port nu...
Q: Indicate whether or not the following is a valid Java statement. Whenever the statement is invalid, ...
A: double net profit = 5000.00; double is used to store float values ,it uses 64 bits to store a variab...
Q: What is the difference between implementing a one-to-many relationship and implementing a one-to-one...
A: Introduction: When a row in one table is associated with just one role in another table and vice ver...
Q: What role do you envision Artificial Intelligence playing in your life in the future? What artificia...
A: Introduction: Artificial intelligence, on a much greater scale, is expected to have a substantial in...
Q: Give the output of the following program segments. int a, b; a = 15; b-4+ --a; System.out.println(a ...
A: Let's see the solution
Q: In the event that a wireless signal comes into contact with a big obstruction, what occurs next?
A: Introduction; In response to the inquiry, Wireless networks are radio stations, not magic. Your wire...
Q: What exactly is cybercrime? Explain briefly three types of cybercrime and the security measures for...
A: Hey there, I am writing the required solution of the questin mentioned above. Please do find the sol...
Q: A My Home Programming Exercise 7 A Courses Tasks TypingGrades.cs + >- Terminal 1 using System; 2 usi...
A: Please refer below for your reference: The code above yours have a small bug inside the for loop:
Q: What are the differences between Big O, Ω and Θ notation? b. Provide examples for each notation
A: Here, we are going to discuss the Big O, Ω and Θ notations with examples.
Q: Add the numbers -0.4 and -0.156 in binary using the steps of floating point addition algorithm.(use ...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: Certain databases only utilise sectors in the outer tracks of magnetic discs, leaving sectors in the...
A: Introduction: A magnetic disc is a disc that is used to store vast amounts of data. It allows you i...
Q: a. Ifa new class Extend PartTime and FullTime class. What type of inheritance is used here for exten...
A: Multiple inheritance is used here for extending these classes. No, it is not possible to do it in JA...
Q: Create a GUI APPLICATION in JAVA PROGRAMMING LANGUAGE based on the following conditions :
A: This JDBC tutorial will show you how to use the JDBC (Java Database Connectivity) API to perform fun...
Q: EXERCISE 4.1.1: License plate combinations. help_outline In a particular state, the license plates h...
A: Introduction EXERCISE 4.1.1: License plate combinations. help_outline In a particular stat...
Q: What is the difference between raw data and an Excel table in an Excel spreadsheet?
A: Introduction: By default, a spreadsheet in Excel is a collection of rows and columns. Each box is re...
Q: Write Java statements (not necessarily complete programs) to achieve indicated task. To find the ave...
A: Introduction: It is a platform and a programming language. java is known as a high-level programmin...
Q: What are apps, and why are they important
A: What are apps, and why are they important?
Q: The velocity and variety of big data are two distinguishing characteristics. What are the specifics ...
A: Introduction: Variety and veracity might not be as necessary or as stressful when dealing with a Big...
Q: Matlab Create a 2D convolution that uses methods circular and nearest neighbor for border handling ...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: Question1: implement lab 3 by the two-dimensional array. ask the user to give you a number of rows a...
A: This given program will take a input as array elements and they define in two dimensional array the...
Q: If an encryption function er is identical to the decryption function dr, then the key K is said to b...
A: Hey there, I am writing the required solution of the questin mentioned above. Please do find the sol...
Q: m?Considering the following code sequence (a) determine at least four hazards for pendences and (b) ...
A: Section: HazardsFor all following questions we assume that:a) Pipeline contains stages: IF, IS (Issu...
Q: How Did Fibonacci Sequence Influence The Birth Of The Ceasar Cipher?
A: How Did Fibonacci Sequence Influence The Birth Of The Ceasar Cipher?
Q: Make a plot in matlab show code and output running in matlab
A: See below steps for code and output.
Q: the construction in Theorem 3.1 to find an nfa that accepts the language L ((aab)*ab).
A: Task : Given the language. The task is to find the NFA for the given expression.
Q: Write a C program executes the multiplication of two numbers entered by the user using only the addi...
A: Ans: Code: #include <stdio.h> int main(){ int a,b; int mul,loop=1; printf("Enter...
Q: Develop a code for Gaussian -Filter
A: Here I have provided an python code for Gaussain-Filter. were you can put your known values.....
Q: To run multiple operating systems on a single machine at the same time, the most efficient method is...
A: Introduction: Virtualization is a computing technique that makes use of virtualized hardware and sof...
Q: You will be building a linked list. Make sure to keep track of both the heac (1) Create three files ...
A: #include "ContactNode.h"//#include "ContactNode.cpp" #include <iostream>#include <string>...
Q: What makes data security so important? After that, discuss how to respond to threats like this.
A: Introduction: Data security refers to securing data against illegal access and alteration throughout...
Q: Indicate whether or not the following is a valid Java statement. Whenever the statement is invalid, ...
A: Introduction: Here we are required to explain whether salary + 100 = salary; is a valid statement in...
Q: What database administration solutions are available for managing data integrity at the field level?
A: Introduction: The operations required to maintain and make a database accessible are referred to as ...
Q: What security measures are database managers using to secure personal information held in business d...
A: When it comes to protecting your information base worker, this means enforcing access rules and lock...
Q: This is referred to as if a wireless router is installed on your network without your knowledge
A: Wireless router:- A router is a device that communicates between the internet and the devices in ...
Q: given a file(use any text file) write MIPS instruction to count all words in that file. note: A si...
A: Creating a new variable to store the total number of words in the text file. And then open the text ...
Q: Using python - show-step-by-step with any needed fuctions that need to be added and show screenshots
A: This Program is written for calculating the cost of different different sets of the consumption of t...
Q: Linux system and network functions that will support a cyber analyst
A: Linux system and network functions that will support a cyber analyst. Network security monitoring to...
Q: 1. Write a function called removePunct() that takes a string and remove the punctuations from that s...
A: Kindly Note: As per our guidelines we are supposed to answer only first question. Kindly repost othe...
Q: Brief information about matlab software
A: Full form of MATLAB is Matrix Laboratory, It is nothing but a programming language or we can say it ...
Q: Disadvantages of using honeypots, honeynets, and padded cell systems are? NOTE - short answers and b...
A: NOTE :- Below i explain the answer in my own words by which you understand it well.
Q: DMA and cache memory are contrasted.
A: Introduction: DMA is a physical technique that allows data to be transferred from and to memory with...
Q: here's my code: #include int main(void) { int next_destination = 10; int *pointer_1, *poi...
A: Before, coming the output. We must understand all , 3 instructions to be followed. Assign the addres...
Q: Computer science What is the connection between an instance and an AMI?
A: Introduction: The information needed to launch an instance is included in an Amazon Machine Image (A...
Q: List and explain the primary tasks involved in the creation of a software system.
A: In the software development service, different software development models are used depending on the...
Q: Write a program that inputs the value 437 five times (use an array here) using each of the scanf con...
A: #include <stdio.h>#include <stdlib.h> int main(){int val[5]; //Reading valuesprintf("Ent...
in java eclipse ide
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Please read all directions carefully! Java Program Please1. Write a program that draws various figures, as shown in Figure (a). The user selects a figure from a radio button and uses a check box to specify whether it is filled. Using Java programmingJava: For each of the following, write a single statement that performs the indicated task: (a) Determine the length of the string in s3. (b) Compare the string in s2 to the string in s4 for equality of contents. (c) Append the string s1 to the string s2, using +=
- 4. Write a program in JAVA language to accept 10 integers from the user and print the maximum and minimum values in the output.Note: Use of any data structure is not allowed.c++ 1. Write a short program to compute the number of hours in a non-leap year. Compile and run, show me the source code and the output screen.10 - In an examination, 500 students appeared. Out of these students, 38 % got A+ grade, 45 % got B+ and the remaining just passed. Assuming that no student failed, find the number of students who got A+, B+ and the number of students who just passed.(Python code)
- 7.14 LAB: Remove all non-alpha characters Write a program that removes all non-alpha characters from the given input. Ex: If the input is: -Hello, 1 world$! the output is: Helloworld Use Python, please.0.O.9. Write a Java program to check if a given string is a palindrome or not. A palindrome is a word, phrase, number, or other sequence of characters that reads the same backward as forward, ignoring spaces, punctuation, and capitalization. For example, "racecar" and "Madam" are palindromes, while "hello" and "Java" are not. Your program should take a string as input and return true if it's a palindrome, and false otherwise.. Absolutely.2- Write a Python program that determines a student’s grade. The program will read three types of scores(quiz, midterm, final exam scores) and determine the grade based on the following rules : if the average score >=90% =>grade=A -if the average score >= 70% and <90% => grade=B -if the average score>=50% and <70% =>grade=C -if the average score<50% =>grade=F Example Input : Quiz score: 80 Mid-term score: 68 Final score: 90 Output: Your grade is B.
- 21.7 LAB: Login name (Use python) Write a program that creates a login name for a user, given the user's first name, last name, and a four-digit integer as input. Output the login name, which is made up of the first five letters of the last name, followed by the first letter of the first name, and then the last two digits of the number (use the % operator). If the last name has less than five letters, then use all letters of the last name. Ex: If the input is: Michael Jordan 1991 the output is: Your login name: JordaM91 Ex: If the input is: Kanye West 2024 the output is: Your login name: WestK24Exercise 1: (Algorithms and Flowcharts) To Converting feet into centimeters3. Find the error in the given code to print the message "Debugging Exercises." In the output. #include <stdio.h>int main(){ print "Debugging Exercises." return 0;}



