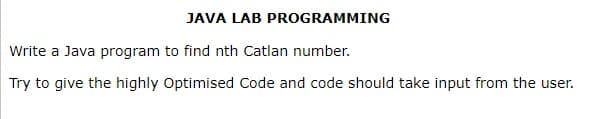
Write a Java program to find nth Catlan number. Try to give the highly Optimised Code and code should take input from the user.
Q: Watchdog timers are essential for embedded systems, correct?
A: Answer: Watchdog timers are usually found in implanted frameworks and other computer-controlled…
Q: 1.
A: Here from question , we have To print statement in php, echo is used To concatenate message use dot…
Q: What can you say about how important computer technology is to you?
A: Why will computer technology play a significant role in society? Here are a few of the explanations…
Q: Is it possible that data structures and algorithms may become outdated in this age of machine…
A: In this question we need to explain whether Data Structures can become outdated (obsolete) in the…
Q: Which protocol protects communications between browsers and web servers?
A: The Internet Protocol is a network layer communication protocol of the Internet Protocol Suite for…
Q: How is an operating system developed using a layered approach? What benefits and drawbacks does this…
A: Introduction: The hardware is at the bottom, while the user interface is at the top.The primary…
Q: Analyze the key parameters involved in this TCP transmission sequence to see how transmission round…
A: TCP stands for Transmission Control Protocol which is a Network layer protocol. Given graph…
Q: What is the DRAM cache's structure?
A: DRAM Cache Structure: To accommodate the growing diversity of memory components, DRAM reserves have…
Q: Let C={000000, 101110, 001010, 110111, 100100, 011001, 111101, 010011} be a binary code of length 6.…
A: A binary code represents text, computer processor instructions or any other data using a two-symbol…
Q: Two crucial concerns are what distributed data processing is, how it functions, and what resources…
A: The process of extracting the vast amount of data contained within a system from its various…
Q: Is it feasible that in the age of machine learning, data formats and algorithms will become…
A: Your answer is given below. Introduction :- The nature of an unsolved problem can be better…
Q: Watchdog timers are essential for embedded systems, correct?
A: Watchdog timers are crucial in embedded systems. The watchdog timer (WDT), which is a part of the…
Q: A GUI or a command line, which do you prefer? Why?
A: Introduction: A command-line interface (CLI) is a kind of user interface (UI) that requires the user…
Q: 17. Is it possible to express - 1024 in 11 bits if we use signed numbers? If so, then enter the…
A: Note: Due to company policies I am compelled to solve only one question and that is the first…
Q: Do algorithms and data structures become obsolete in the age of machine learning?
A: Data Structures: In order to store and arrange data in a manner that makes it useful, we employ data…
Q: ir chances of success
A: Page size describes the size of your publication's area. The size of the paper used for printing is…
Q: How can I integrate caches and
A: Introduction: Utilizing Cache: In-memory caches are layers that reduce the amount of time required…
Q: Imagine that you want a software developer to build a programme with features similar to those of…
A: Statement of objectives (SOO): It gives a general purpose as the foundation for the statement of…
Q: Why does a software not have to be completely error-free before being offered to its users?
A: Introduction: Because it is not always (99% of the time) feasible to give a defect-free product to…
Q: What are the different methods for getting application software? Use relevant examples to help prove…
A: Application Software: A computer software package known as an application, sometimes known as an…
Q: What separates the TPC's focus from that of the SPEC?
A: Introduction Transaction Procession Council TPC or Transaction Procession Council is an…
Q: What design problems exist in a secret cryptography method?
A: The process of concealing or encoding information through cryptography is designed to ensure that…
Q: What are the distinctions between two-tiered and three-tiered computer application architectures,…
A: It uses a client-server architecture. In a two-tier system, the application logic is either hidden…
Q: Why did our rdt protocols require timers in the first place?
A: In order to ensure that data is sent securely, sequence numbers indicate to the destination whether…
Q: How is this mapping carried out by the MMU utilising the page table?
A: The Paging Method: The MMU pulls relevant pages into frames placed in physical memory for speedier…
Q: What programme is used and how is IPsec configured between two computers?
A: IPsec is a protocol and suite of algorithms used to secure the traffic between two hosts. The…
Q: Is it possible that data structures and algorithms may become outdated in this age of machine…
A: Algorithm and data structure usage: enables a deeper understanding of the nature of insoluble…
Q: What is the name of the SSH client file that a system administrator uses to set up an SSH server's…
A: A cryptographic protocol known as Secure Shell is used to operate business functions securely across…
Q: anything happen when a command that isn't an internal MS-DOS command is entered at the MS-DOS prompt
A: Answer:
Q: List and explain the commands that a command-line interface makes simpler to use than a graphical…
A: To begin, let's investigate the difference between the CLI and the GUI: Through the graphical icons…
Q: escribe the emergence and expansion of disruptive technologies and applications like Amazon as a…
A: Answer is in next step.
Q: How does the microprocessor differentiate between data and instruction?
A:
Q: In simple words, describe the final data pointer register.
A: Solution: Data pointer register: It is a 16-bit register that can hold a total of two bytes' worth…
Q: How do you calculate a prediction interval using a statistical programme like JMP?
A: The prediction timings indicate where in the sample you should be able to find the next datum.…
Q: Is it feasible to outline the responsibilities and qualifications for a help desk specialist?
A: To Do: Describe a support desk expert. Requirements include having at least X years of experience…
Q: Distinguish between system programming and application programming using examples, and then describe…
A: System software acts as the interface between the computer hardware and the application software.
Q: Give an example of data manipulation, forgeries, and website piracy.
A: Data diddling: Data diddling is the act of making unauthorised changes to data before its input into…
Q: What is it about virtual memory that inhibits its use in embedded systems more frequently?
A: Introduction: One of the reasons why some embedded systems don't use virtual memory is that the…
Q: Two crucial concerns are what distributed data processing is, how it functions, and what resources…
A: The process of extracting the vast amount of data contained within a system from its various…
Q: Is it feasible for an application to use the UDP transport protocol and yet have reliable data…
A: Introduction : The User Datagram Protocol is this simple protocol suddenly attracted…
Q: Can today's Mechanical Turks fool people? What distinguishes a Turk from the 18th century from one…
A: using an automated to dupe people: "No," you cannot deceive people using a method like Mechanical…
Q: What are the dangers of using the SSTF disc scheduling algorithm
A: Please find the answer below
Q: The capacity of embedded computers to carry out certain tasks sets them apart from general-purpose…
A: Introduction: Today, a wide variety of gadgets qualify as special-purpose computers, including Blade…
Q: Examine your place in the chain. What serves as the value chain? What do you then? How do you…
A: A sequence of actions that are utilised: To turn input into output in such a manner that the value…
Q: Explain in detail the meaning of the terms "aggregation" and "generalisation" as they relate to two…
A: The terms "aggregation" and "generalisation" refer to two different types of relationships that can…
Q: Information technology has had a major impact on our lives and society. Please provide reasons for…
A: Information technology Information technology (IT) is the utilization of PC frameworks or gadgets…
Q: How do you calculate a prediction interval using a statistical programme like JMF
A: It is defined as the program sequence is transferred to the memory location specified by the 16-bit…
Q: The most crucial fundamental elements of a computer
A: One must know about the basics and the fundamentals of the computer as nowadays this knowledge is…
Q: at four tasks does a router perform?
A: As we know A router is a networking device mainly that forwards data packets or information between…
Q: Only one-third of projects met their budget, timeline, and goal objectives, according to a recent…
A: When creating and deploying a mobile app under a constrained FIMC timeframe, the following possible…
Step by step
Solved in 4 steps with 4 images

- Java program Write a program in Java to take an double number and also take how much you round from user and round that numberProgramming language : Java Write an application that prints the initials "SP" in large block letters. Make each large letter out of the corresponding characters. Please use escape sequences to form the initials!Java I am beginner in java my program is to take 2 number from user and given that these number is of int type . i have to find remainder and print this
- (java programming language) Given f(x) = x+ x2/2+ x3/3+…… xn/n. Using do-while, write a program to compute f(x) for given x andn. The user should enter x and a positive integer n. Save your file as Q3.JavaJava Write an application that reads three nonzero values entered by the user and determines and prints whether they could represent the sides of a triangle.(java) Program to display the numbers which are divisible by 7; (between 1 and 100) Example: 7, 14, 21, 28,........ 98
- T/F 1. Only primitive forms may be returned by Java methods.Java Write a program that calculates the weight of number that should be taken from number. For ex : 123 = 6(Emirp) An emirp (prime spelled backward) is a nonpalindromic prime number whose reversal is also a prime. For example, 17 is a prime and 71 is a prime, so 17 and 71 are both emirps. Write a Java program that displays the first 100 emirps. Display 10 numbers per line with a spacing of 5; all numbers should be left-aligned.



