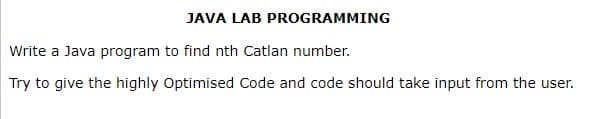
Write a Java program to find nth Catlan number. Try to give the highly Optimised Code and code should take input from the user.
Q: What benefits do constructed languages have over interpreted ones? What circumstances would you make…
A: Constructed languages: Proponents of a specific language believe that using it makes it simpler to…
Q: What design problems exist in a secret cryptography method?
A: To be determine: Where exactly are the weaknesses in the design of a top-secret cryptographic method…
Q: Is it feasible to outline the responsibilities and qualifications for a help desk specialist?
A: To Do: Describe a support desk expert.
Q: Give an example of data manipulation, forgeries, and website piracy.
A: Data tampering Data tampering refers to modifying data without a authorization before entering a…
Q: How are software and web engineering different from one another?
A: Following are some distinctions between web engineering and software engineering: Web Development:…
Q: Is there a distinction to be made between computer organisation and computer architecture? Do you…
A: A computer is an electronic device that accepts input, produces output, and does calculations. In…
Q: Blockers in compiler optimization Describe two obstacles to optimization. Describe them, the…
A: Introduction: Optimization is a method of modifying programs to enhance performance by decreasing…
Q: This essay investigates the effects of the switch from traditional to new media on societal values…
A: One of the cornerstones of our constitution is the media. It serves a vital function. Always have an…
Q: Why did our rdt protocols require timers in the first place?
A: Answer is in next step.
Q: List some of the difficulties in building the information system architecture of a new service.
A: Note: As per the question statement/assertion, only the difficulties are listed in this solution…
Q: Why should shared vs. private L2 caches be used for single-threaded, multi-threaded, and…
A: Cache Memory which refers to the chip-based computer component that makes retrieving data from the…
Q: Which protocol protects communications between browsers and web servers?
A: The Internet Protocol is a network layer communication protocol of the Internet Protocol Suite for…
Q: Does the current age of machine learning still have a place for data structures and algorithms? Do…
A: A data structure is a set of data items that have been organized in some way, for as by numbering…
Q: Why do we address computational geometry issues with MATLAB?
A: Introduction A great many engineers and researchers use MATLAB in industry and the scholarly world…
Q: A programming interface is sometimes known as an application programming interface (API). What does…
A: Application programming interface- (API): API is a type of computer interface that helps describe…
Q: Why did our rdt protocols require timers in the first place?
A: In order to ensure that data is sent securely, sequence numbers indicate to the destination whether…
Q: What stage of the data science process is the most important?
A: Given: Analysis and interpretation of the data is a crucial stage in the data science process. A…
Q: What are the two main advantages of software-defined networks versus hardware-defined networks, and…
A: There are many differences between software-defined networks versus hardware-defined networks and…
Q: Think about the following example: Your company's mail server sends you a message alerting you that…
A: Solution: Phishing attacks are a sort of virus that allow for the hacking of passwords. In these…
Q: What do computer applications and software programmes do?
A: The question has been answered in step2
Q: What are the distinctions between two-tiered and three-tiered computer application architectures,…
A: Generally speaking, there are several sorts of architectures in computer applications, including,…
Q: What are the operating system's microkernel design principles? What distinguishes this strategy from…
A: Introduction Is the microkernel of the operating system made in compliance with a specific set of…
Q: List three ways technology has enhanced productivity at the workplace
A:
Q: 5. aig in a in dispensing cash. Give your description in pseudocode. Analyse the following…
A: so the answers are given below 1) Pseudocode for ATM machine 2) analysis of algorithm
Q: Think about the following example: Your company's mail server sends you a message alerting you that…
A: Solution: Phishing attacks are a sort of virus that allow for the hacking of passwords. In these…
Q: Is it feasible for an application to use the UDP transport protocol and yet have reliable data…
A: Introduction It's certainly possible, but it's up to the application layer to handle it. However,…
Q: List three ways technology has enhanced productivity at the workplace
A: The workforce of today may quickly speak with one another from any location in the world and have…
Q: Two crucial concerns are what distributed data processing is, how it functions, and what resources…
A: The process of extracting the vast amount of data contained within a system from its various…
Q: What does "reduced," as it relates to a computer with a limited instruction set, mean?
A: Introduction: When compared to complicated instruction set computers, this computer's instruction…
Q: What are the distinctions between two-tiered and three-tiered computer application architectures,…
A: Given: In the realm of computer applications, there are often many different kinds of architectures,…
Q: A programming interface is sometimes known as an application programming interface (API). What does…
A: An application programming interface is a means by which two or more computer programs communicate…
Q: One special contribution of Internet-based news is that it provides slower, more deliberative…
A: Internet-based news has revolutionised the entire communication industry as it is characterized as…
Q: th n, a total of M codewords, and minim of the major goals of coding theory is t strike a balance…
A: the answer is an below step :
Q: How is an operating system developed using a layered approach? What benefits and drawbacks does this…
A: Introduction: The hardware is at the bottom, while the user interface is at the top.The primary…
Q: List and explain the commands that a command-line interface makes simpler to use than a graphical…
A: Introduction: In GUI, we interface with software or devices via graphical icons. GUI is graphical.…
Q: Think about how the Windows API and POSIX API are different, and then quickly describe how you would…
A: Application Programming Interface: Application Programming Interface is referred to as - API. Any…
Q: Distinguish between system programming and application programming using examples, and then describe…
A: Provide instances of the distinctions between system programming and application programming.…
Q: Compilers for C and C++ are built in a certain method. Please give concrete examples.
A: Introduction: Compilers: A compiler is a computer program which helps you transform source code…
Q: What concrete examples would you use to describe data manipulation, forgeries, and internet jacking?
A: Meddling with data: Data diddling is the practises of making unauthorized changes to information…
Q: What reduced attacks are there, and how can you counter them?
A: Lower-level assault: The computer system or communication protocol is the target of a cryptographic…
Q: How is a skewed exponent useful?
A: Answer: The skewness of the exponential distribution doesn't depend upon the worth of the parameter…
Q: What are the different methods for getting application software? Use relevant examples to help prove…
A: Application software Programs are developed to execute a large variety of roles. The functions don't…
Q: Watchdog timers are essential for embedded systems, correct?
A: Answer: Watchdog timers are usually found in implanted frameworks and other computer-controlled…
Q: What performance advantages do vectors provide over arrays?
A: What benefits do vectors have over arrays?
Q: The most crucial fundamental elements of a computer must to be discussed and specified right away,…
A: The following are the four primary structural components of a computer: 1. Computer's main brains,…
Q: Why did our rdt protocols require timers in the first place?
A: Sequence numbers Sequence numbers illuminate the beneficiary whether new or old data is put away in…
Q: List some of the difficulties in building the information system architecture of a new service.
A: Please find the answer below :
Q: The capacity of embedded computers to carry out certain tasks sets them apart from general-purpose…
A: Embedded computers have the ability to carry out certain tasks that set them apart from…
Q: What does "reduced" imply in terms of the constrained set of instructions that a computer has?
A: In the given question Reduced Instruction Set Computer is a type of microprocessor architecture that…
Q: Why is packetizing required by the transport layer from the network layer? Why can't segments be…
A: System layer: In the OSI model, the network layer is the one utilised to give the host's ability to…
Step by step
Solved in 4 steps with 3 images

- Java program Write a program in Java to take an double number and also take how much you round from user and round that numberProgramming language : Java Write an application that prints the initials "SP" in large block letters. Make each large letter out of the corresponding characters. Please use escape sequences to form the initials!Java I am beginner in java my program is to take 2 number from user and given that these number is of int type . i have to find remainder and print this
- (java programming language) Given f(x) = x+ x2/2+ x3/3+…… xn/n. Using do-while, write a program to compute f(x) for given x andn. The user should enter x and a positive integer n. Save your file as Q3.JavaJava Write an application that reads three nonzero values entered by the user and determines and prints whether they could represent the sides of a triangle.(java) Program to display the numbers which are divisible by 7; (between 1 and 100) Example: 7, 14, 21, 28,........ 98
- T/F 1. Only primitive forms may be returned by Java methods.Java Write a program that calculates the weight of number that should be taken from number. For ex : 123 = 6(Emirp) An emirp (prime spelled backward) is a nonpalindromic prime number whose reversal is also a prime. For example, 17 is a prime and 71 is a prime, so 17 and 71 are both emirps. Write a Java program that displays the first 100 emirps. Display 10 numbers per line with a spacing of 5; all numbers should be left-aligned.



