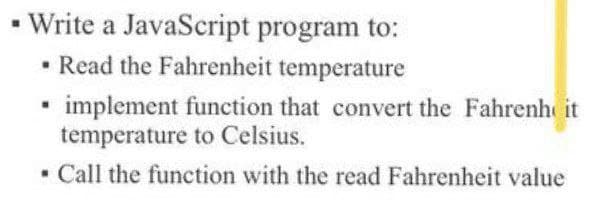
• Write a JavaScript program to: • Read the Fahrenheit temperature • implement function that convert the Fahrenh it temperature to Celsius. Call the function with the read Fahrenheit value
Q: What is the length of an IPv6 address in terms of bits?
A: Given Length of IPv6 in term of bits.
Q: In data mining, what exactly is meant by pattern evaluation?
A: - We need to talk about pattern evaluation.
Q: Are all of an organization's worries regarding its computer infrastructure eliminated as a result of...
A: Introduction: Cloud computing is a type that relies on sharing computing resources rather than appli...
Q: re this salary range per customer. The query should display the attributes as problem 1 but also inc...
A: Solution:-
Q: Consider the following program: Fib[n] if(n==0) then return 0 else if(n==1) then return 1 else retur...
A: Given program: Fib[n] If(n==0) then return 0 else if(n==1) then return 1 else return Fib[n-1]+Fib...
Q: PROBLEM: Write a program that computes the equivalent resistance of a purely series and purely paral...
A: Given: there is no programming language mentioned so I am answering in C++ programming language. ...
Q: Describe In a computer network, penetration testing is done.
A: Penetration Testing: Penetration test is nothing but a pen test that helps in cyber-attack for the v...
Q: 0,1 0,1
A:
Q: In terms of technology, what are some of the consequences of Moore's Law? What impact will it have o...
A: Introduction: Moore's Law's Economic Consequences One of the law's economic effects is that computer...
Q: Pete and Billy are great fans of even numbers, that's why they want to divide the watermelon in such...
A: Suppose, watermelon weighs 21 kg, then it can be divided as, 10 + 11 , in which one number is odd. O...
Q: Q1a) If a new application is built by a mobile platform, can it be created with web design? What's t...
A: Due to company policies I am compelled to solve only one question and that is the first question. Pl...
Q: When it comes to running their Internet of Things devices, IoT developers rely on Linux more than an...
A: Description In the Internet of Things, the operating system is critical. The operating system (OS) i...
Q: PROBLEM: Write a C++ program that will allow the user to input the First Name, Last name, Middle In...
A: 1)Read the input from the user first name, last name, middle initial and Grade 2)Display the first...
Q: ncircled one in a C++ language
A: We need to read in R1,R2 and R3 and compute Rs or Rp as per the given formula.
Q: pared to RISC machines
A: RISC: Reduce the cycles per instruction at the cost of the number of instructions per program. CIS...
Q: eate a program named SalesTaxDemo that declares an array of 10 Sale objects. Prompt the user for da...
A: Sale.cs : class Sale //C# class{ // class definition of Saleprivate string inventoryNumber;private d...
Q: Write an R program, using the corrgram library, to plot the Average_Daily_Traffic_Counts.csv dataset...
A: 5. answer import matplotlib.pyplot as plt import numpy as np import pandas as pd data = pd.read_c...
Q: Write the implementation of a static method, called evenElements, that takes one input parameter, ca...
A: In the file ListItem.java, write static methods that satisfy the following specifications. Remember ...
Q: Discuss the Performance Assessment of a computer processor particularly in terms of the Clock Speed ...
A: Clock Speed When comparing computers, the processor speed (CPU speed) is one of the most significan...
Q: Verify if the following statemen is true or false. Fully justify your answers. If f = log2 (n!) and...
A: f=log2(n!) and g=log2(nn) g=n log2 n f=log2(n!) =log2(1.2.3....n) upper bound log2(1)+log2(2)+........
Q: Lab Goal : This lab was designed to teach you more object oriented programming and start you down th...
A: public class DeckOfCards { private Card theCard; private int remainingCards = 52; DeckOfCards() ...
Q: Will there be less need for in-house systems analysts as more organisations outsource system develop...
A: The need for in-house systems analysts While you outsource, you are leveraging the services of outsi...
Q: When it comes to IT infrastructure and information systems in general, what is the job of the non-IT...
A: Introduction: Core telecommunications networks, databases and data warehouses, software and hardware...
Q: Ql: Give a result to the algorithm Start 2, 10, 2 Sum-0 Sum-Sum +1 Print Sum
A: Here we are using a for loop in the flowchart. The loop run from i=2 to 10 in increment of 2.
Q: Print specific number of the substrings use c# code
A: The answer is
Q: If i wanted to calculate how many times I need to send a message to a socket at a specified rate ove...
A: Please refer below for your reference: The formula to calculate is below:
Q: Assume register $t0 and $t1 contains 0×020A007E and 0×FFFFFFF0 respectively. The content of $t0 afte...
A: According to the information given:- We have to find after execute and $t0,$t0,$t1
Q: use c++ language This program should greet the user at start After that it should display Mcqs ques...
A: Have the question in first line and then first half of the options in second line and next half of o...
Q: interface designs will need to to be compatible with pre-defined, existing end products TRUE/FALSE
A: Answer is TRUE. Interface designs need to be compatible with pre-defined ,existing end products.
Q: PROBLEM: Write a program that prompts the user to input three (3) integers: MM, DD, and YYYY. For ex...
A: #include <iostream>using namespace std;// to check if year is leap year or notbool isLeap(int ...
Q: What is it about buses that makes them such a communication bottleneck?
A: What is it about buses that makes them such a communication bottleneck?
Q: What is the difference between clock cycles and clock frequency, and how do you explain it?
A: Introduction: When it comes to clocks, frequency is usually measured in clock pulses per second. A 1...
Q: Design the logic, using flowchart or pseudocode, for a program that calculates the projected cost of...
A: In the given Question, we need to provide a Flowchart and a Pseudocode that calculates the projected...
Q: Use c++ programming language: Write a program that prompts the user to input the amount of money th...
A: Find the required code given as below and output:
Q: for c++ A set is a collection of distinct elements of the same type. Design the class unorderedS...
A: Answer: Program #include <iostream>#include "unorderedSetType.h" using namespace std; int main...
Q: What role do frequent data backups have in protecting organisations against threats such as ransomwa...
A: Introduction: When someone gets Ransomware, their files are encrypted, and they can't open them. It ...
Q: In what sort of circuit is it possible to choose binary information from a large number of input lin...
A: Introduction: Typically, as humans, we represent numbers using the decimal system. 111, 222, 333, 44...
Q: The distinction between utilising direct and indirect addressing
A: Direct addressing mode means the operand address is contained in the instruction. In the 8085, an ex...
Q: If your computer's TCP/IP stack does not have a DNS server address and you need to access a website....
A: Basically we can access any website through either URL (DNS server) and IP addresses. DNS : The Doma...
Q: .Procedural languages such as employ this model to considerable success. C++ Java O Python
A: Ans: Procedural Language such As that employ this model to considerable success is : c) C
Q: ( What the deferent between Encoding and Encryption??
A: The reason for encoding is to change information with the goal that it tends to be appropriately (an...
Q: The requirement for flow control may be explained as follows: Explain the various ways to flow contr...
A: Controlling the Flow of Information Flow control not only monitors, but it also synchronises the dat...
Q: List five expenses or dangers connected with using a database to store information.
A: Introduction: The database method adds expenses and hazards that must be recognized and handled when...
Q: Polymorphism is a term that should be defined.
A: Polymorphism is the capacity to convey a message in several forms. A person may have many qualities ...
Q: Write a program that prompts the user to input three (3) integers: MM, DD, and YYYY. For example, 07...
A: For validations, check if date is positive, month is positive and year is non negative Also day must...
Q: What exactly is an opcode?
A: Step 1) instruction contains two parts operation code (opcode) Operand The first part of an instr...
Q: Define the term "memory."
A: Introduction: the power or process of reproducing or recalling what has been learned and retained es...
Q: , For each of the following expressions, show the value that will be shown in the Python interpreter...
A: a) On executing print("{:5.2f}".format(.67321)) in python interpreter, it displays 0.67 value. Pytho...
Q: There is an auto-complete feature in MATLAB. If a user starts to type a command and then presses the...
A: Given: There is an auto-complete feature in MATLAB. If a user starts to type a command and then pr...
Q: These are values or sets of values. O Data Object O Data O Data object
A: The data is information that has been translated into a form that is efficient for movement or proce...
Step by step
Solved in 3 steps with 2 images

- Help with understanding of what to use with this question in Javascript: /******************************************************************************* * Problem 2: mask the characters of a password. * * Sometimes we want to show a password, but replace some or all of the * letters with a character like *. This is called masking, and allows us to * hide information, while still displaying something. * * Write a function maskPassword() that takes two arguments: a password to mask, * and a number of characters to show at the start: * * maskPassword('super-secret', 3) * * would return the following string: * * "sup*********" * * Whereas maskPassword('super-secret') or maskPassword('super-secret', 0) * would both return: * * "************" * * @param {String} password - a password to be masked. * @param {Number} charsToShow - (optional) the number of characters to reveal. ******************************************************************************/ function…1. Implement function postal() that takes 6 inputs: a first name (as a string) a last name (as a string) an address (as a string) a city (as a string) a state (as a string) a zip code (as an integer)and then prints a mailing address in 3 lines as shown below.>>> postal('Ljubomir', 'Perkovic', '243 S Wabash Ave','Chicago', 'IL', 60304)Ljubomir Perkovic243 S Wabash AveChicago, IL 60304A java program where the system should use the following methods: .a) Lagrange interpolation for finding missing values of a function .b) A function implementing multiple application of the trapezoidal rule .c) A function implementing the composite Simpson's rule SHOULD ALLOW THE USER TO : Enter the known values of a function to be integrated or load them from a text file Enter a value of the parameter h and n (the number of intervals) .c) Choose a method to be used
- Please, help to write such a programm in Java! Build a program to work with the Date class. The program should provide the simplest functions: increase / decrease by 1 day, input values, output values.Create a Javascript function that takes a numeral (just digits without separators (e.g. 19093 instead of 19,093) and returns the standard way of reading a number, complete with punctuationCreate a program that takes two parameters called base and expo such that b ase is not zero and returns the value of baseexpo . Write a recursive function and call it power.
- write a program that simulates coin tossing. for each toss of the coin the program should print heads or tails. let the program toss the coin , and count the number of times each side of the coin appears. print the results. the program should call a separate function flip that takes no arguments and returns 0 for tails and 1 for heads.import random.java. Utilfunction myCompose(f,g){// TODO: return (f o g);// that is, a function that returns f(g(x)) when invoked on x.}Implement in C Programming 6.10.2: Pass by pointer. Write a function call to ConvertMoney() to store the number of quarters, nickels, and pennies within the integer variables numQuarters, numNickels, and numPennies, respectively. Ex: If the input is 133, then the output is: Quarters: 5 Nickels: 1 Pennies: 3 #include <stdio.h> void ConvertMoney(int totalPennies, int* numQuarters, int* numNickels, int* numPennies) { *numQuarters = totalPennies / 25; totalPennies = totalPennies % 25; *numNickels = totalPennies / 5; totalPennies = totalPennies % 5; *numPennies = totalPennies;} int main(void) { int totalPennies; int numQuarters; int numNickels; int numPennies; scanf("%d", &totalPennies); /* Your code goes here */ printf("Quarters: %d\n", numQuarters); printf("Nickels: %d\n", numNickels); printf("Pennies: %d\n", numPennies); return 0;}
- javascript 9. Return a Boolean if a number is divisible by 10 Here, you'll create a function that'll give you a "true" or "false" Boolean as its output. The inputted number should only return a "true" if it's divisible by 10. Otherwise, your program should return a "false" answer.Trace through (show all the steps as we did in class) for the following java code for the factorial function. Show all the steps (illustrate, do not code) that lead to the final answer when myFactorial(6) is called: int myFactorial( int integer) { if( integer == 1) return 1; else { return(integer*(myFactorial(integer-1); } }Write a Java program that will call a method (called f) to tabulate the following function. f(x) = x2 - 16



